Introduction
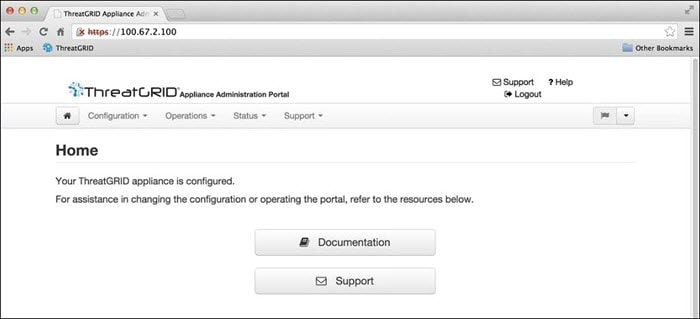
The OpAdmin Portal is the Threat Grid administrator's portal on the appliance and is the recommended tool for configuring your appliance. It is a Web user interface that can be used once an IP address has been configured on the Admin interface.
The configuration includes the following steps:
-
Change OpAdmin Admin Password
-
Review End User License Agreement
-
Review Network Configuration Settings (not configured using wizard)
-
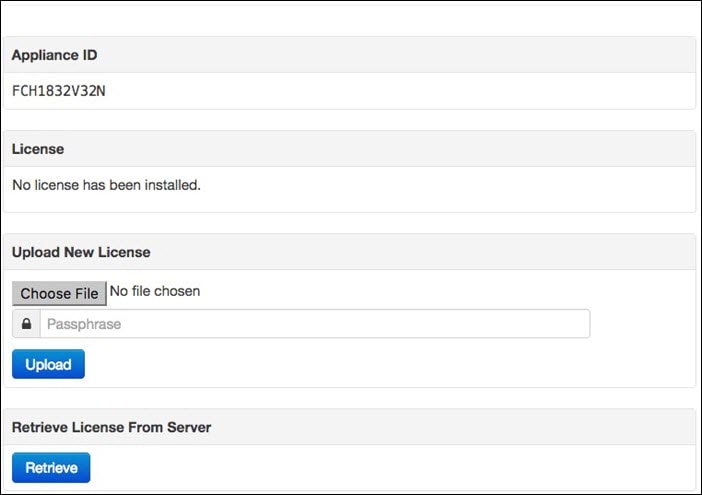
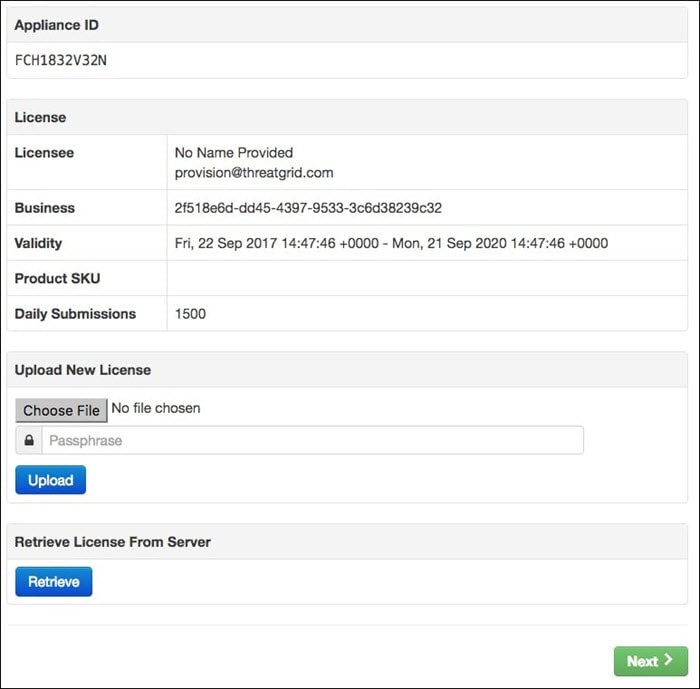
Install License
-
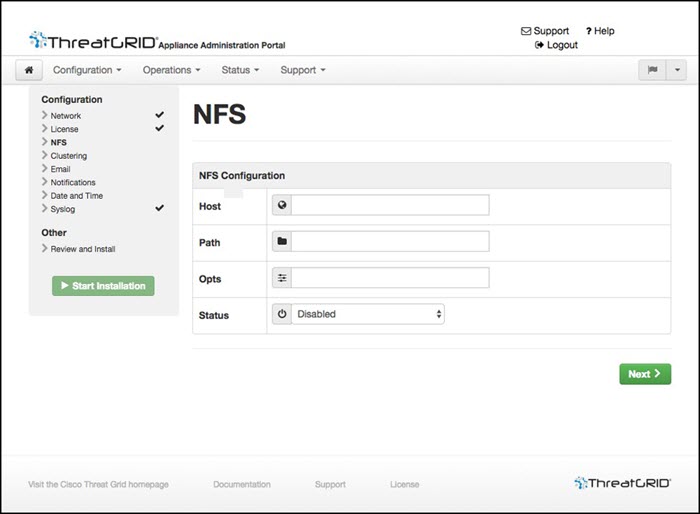
Configure NFS
-
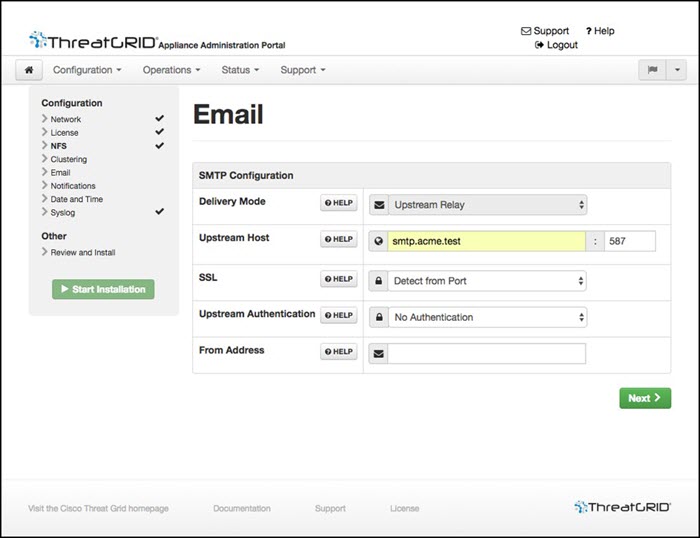
Configure Email Host
-
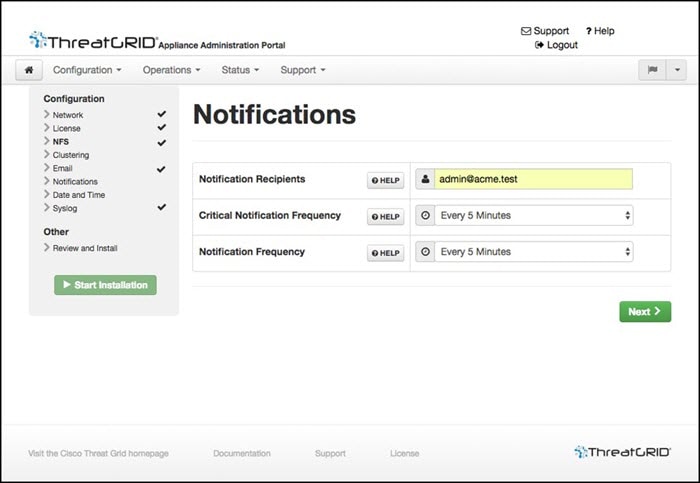
Configure Notifications
-
Configure Date and Time (NTP Server)
-
Configure SysLog
-
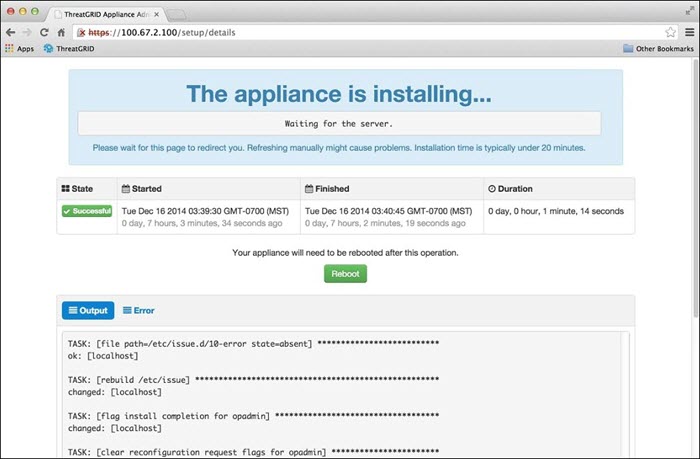
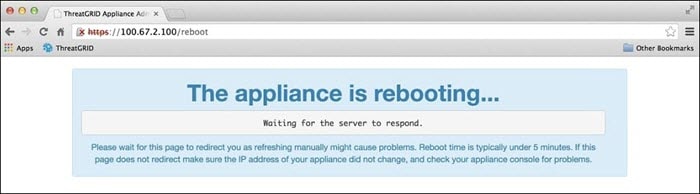
Review and Install Configuration Settings
 Note |
Not all configuration steps are completed using the configuration wizard. See the Cisco Threat Grid Appliance Administrator Guide for configuring settings not included in the wizard, such as SSL Certificates and Clustering. |
 Important |
The steps in the following sections should be completed in one session to reduce the chance of an interruption to the IP address during configuration. |
Log In to OpAdmin Portal
Perform the following steps to log in to the Threat Grid OpAdmin portal.
Procedure
| Step 1 |
In a browser, enter the URL for the OpAdmin portal (https://<adminIP>/ or https://<adminHostname>/) to open the Threat Grid OpAdmin login screen.
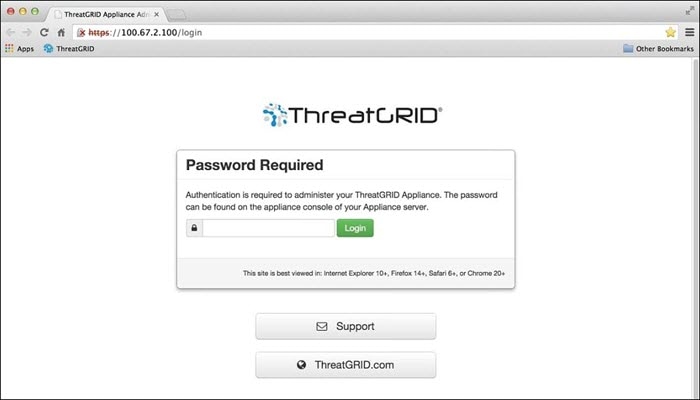
|
||
| Step 2 |
Enter the initial Admin Password that you copied from the TGSH Dialog and click Login. |
What to do next
Proceed to Change Admin Password.
Change Admin Password
The initial Admin password was generated randomly during the pre-ship Threat Grid installation, and is visible as plain text in the TGSH Dialog. You must change the initial Admin password before continuing with the configuration.
Procedure
| Step 1 |
Enter the password from the TGSH Dialog in the Old Password field. (You should have this saved in a text file.) |
||
| Step 2 |
Enter a New Password and re-enter it in the Confirm New Password field. |
||
| Step 3 |
Click Change Password. The password is updated.
|
What to do next
Proceed to Review End User License Agreement.
Review End User License Agreement
Review the license agreement and confirm that you agree to it.
Procedure
| Step 1 |
Review the End User License Agreement. |
||
| Step 2 |
Scroll to the end and click I HAVE READ AND AGREE.
|
What to do next
Proceed to Configure Network Settings.


 Feedback
Feedback