- About this Guide
-
- Configuring IPSec and ISAKMP
- Configuring L2TP over IPSec
- Setting General VPN Parameters
- Configuring Tunnel Groups, Group Policies, and Users
- Configuring IP Addresses for VPN
- Configuring Remote Access VPNs
- Configuring Network Admission Control
- Configuring Easy VPN on the ASA 5505
- Configuring the PPPoE Client
- Configuring LAN-to-LAN VPNs
- Configuring AnyConnect VPN Client Connections
- Configuring AnyConnect Host Scan
- Configuring an External Server for Authorization and Authentication
-
- Clientless SSL VPN Overview
- Basic Clientless SSL VPN Configuration
- Advanced Clientless SSL VPN Configuration
- Configuring Policy Groups
- Clientless SSL VPN Remote Users
- Configuring Clientless SSL VPN Users
- Using Clientless SSL VPN with Mobile Devices
- Customizing Clientless SSL VPN
- Clientless SSL VPN Troubleshooting
- Clientless SSL VPN Licensing
- Index
- Specifying the Client/Server Role of the Cisco ASA 5505
- Specifying the Primary and Secondary Servers
- Specifying the Mode
- Configuring Automatic Xauth Authentication
- Configuring IPsec Over TCP
- Comparing Tunneling Options
- Specifying the Tunnel Group or Trustpoint
- Configuring Split Tunneling
- Configuring Device Pass-Through
- Configuring Remote Management
- Guidelines for Configuring the Easy VPN Server
Configuring Easy VPN Services on the ASA 5505
This chapter describes how to configure the ASA 5505 as an Easy VPN hardware client. This chapter assumes you have configured the switch ports and VLAN interfaces of the ASA 5505 (see “Starting Interface Configuration (ASA 5505),” in the general operations configuration guide).

Note![]() The Easy VPN hardware client configuration specifies the IP address of its primary and secondary (backup) Easy VPN servers. Any ASA, including another ASA 5505 configured as a headend, a VPN 3000 Series Concentrator, an IOS-based router, or a firewall can act as an Easy VPN server. An ASA 5505 cannot, however function as both a client and a server simultaneously. To configure an ASA 5505 as a server, see the “Specifying the Client/Server Role of the Cisco ASA 5505” section. Then configure the ASA 5505 as you would any other ASA, beginning with the “Getting Started” section in the general operations configuration guide.
The Easy VPN hardware client configuration specifies the IP address of its primary and secondary (backup) Easy VPN servers. Any ASA, including another ASA 5505 configured as a headend, a VPN 3000 Series Concentrator, an IOS-based router, or a firewall can act as an Easy VPN server. An ASA 5505 cannot, however function as both a client and a server simultaneously. To configure an ASA 5505 as a server, see the “Specifying the Client/Server Role of the Cisco ASA 5505” section. Then configure the ASA 5505 as you would any other ASA, beginning with the “Getting Started” section in the general operations configuration guide.
This chapter includes the following sections:
- Specifying the Client/Server Role of the Cisco ASA 5505
- Specifying the Primary and Secondary Servers
- Specifying the Mode
- Configuring Automatic Xauth Authentication
- Configuring IPsec Over TCP
- Comparing Tunneling Options
- Specifying the Tunnel Group or Trustpoint
- Configuring Split Tunneling
- Configuring Device Pass-Through
- Configuring Remote Management
- Guidelines for Configuring the Easy VPN Server
Specifying the Client/Server Role of the Cisco ASA 5505
The Cisco ASA 5505 can function as a Cisco Easy VPN hardware client (also called “Easy VPN Remote”) or as a server (also called a “headend”), but not both at the same time. It does not have a default role. Use one of the following commands in global configuration mode to specify its role:
- vpnclient enable to specify the role of the ASA 5505 as an Easy VPN Remote
- no vpnclient enable to specify the role of the ASA 5505 as server
The following example shows how to specify the ASA 5505 as an Easy VPN hardware client:
ciscoasa(config)# vpnclient enable
ciscoasa(config)#
The CLI responds with an error message indicating that you must remove certain data elements if you switch from server to hardware client, depending on whether the elements are present in the configuration. Table 8-1 lists the data elements that are permitted in both client and server configurations, and not permitted in client configurations.
|
Configurations |
|
|---|---|
An ASA 5505 configured as an Easy VPN hardware client retains the commands listed in the first column within its configuration, however, some have no function in the client role.
The following example shows how to specify the ASA 5505 as an Easy VPN server:
ciscoasa(config)# no vpnclient enable
ciscoasa(config)#
After entering the no version of this command, configure the ASA 5505 as you would any other ASA, beginning with “Getting Started” section in the general operations configuration guide.
Specifying the Primary and Secondary Servers
Before establishing a connection with an Easy VPN hardware client, you must specify the IP address of an Easy VPN server to which it will connect. Any ASA can act as an Easy VPN server, including another ASA 5505 configured as a headend, a VPN 3000 Series Concentrator, an IOS-based router, or a firewall.
The ASA 5505 Client always tries to set up the tunnel to the headend primary VPN server. If unable to set up the tunnel to the primary server, it tries the connection to the secondary_1 VPN server, and then sequentially down the list of VPN servers at 8 second intervals. If the setup tunnel to the secondary_1 server fails, the primary comes online during this time, and the ASA proceeds to set up the tunnel to the secondary_2 VPN server.
Use the vpnclient server command in global configuration mode, as follows:
[ no ] vpnclient server ip_primary [ ip_secondary_1 … ip_secondary_10 ]
no removes the command from the running configuration.
ip_primary_address is the IP address or DNS name of the primary Easy VPN server.
ip_secondary_address_n (Optional) is a list of the IP addresses or DNS names of up to ten backup Easy VPN servers. Use a space to separate the items in the list.
For example, enter the following command to configure a VPN client to use Easy VPN Server 10.10.10.15 as the primary server, and 10.10.10.30 and 192.168.10.45 as alternate servers:
ciscoasa(config)# vpnclient server 10.10.10.15 10.10.10.30 192.168.10.10
ciscoasa(config)#
Specifying the Mode
The Easy VPN Client supports one of two modes of operation: Client Mode or Network Extension Mode (NEM). The mode of operation determines whether the inside hosts relative to the Easy VPN Client are accessible from the Enterprise network over the tunnel. Specifying a mode of operation is mandatory before making a connection because Easy VPN Client does not have a default mode.
Client mode, also called Port Address Translation (PAT) mode, isolates the IP addresses of all devices on the Easy VPN Client private network from those on the enterprise network. The Easy VPN Client performs PAT for all VPN traffic for its inside hosts. IP address management is neither required for the Easy VPN Client inside interface or the inside hosts.
NEM makes the inside interface and all inside hosts routeable across the enterprise network over the tunnel. Hosts on the inside network obtain their IP addresses from an accessible subnet (statically or via DHCP) pre-configured with static IP addresses. PAT does not apply to VPN traffic in NEM. This mode does not require a VPN configuration for each client. The Cisco ASA 5505 configured for NEM mode supports automatic tunnel initiation. The configuration must store the group name, user name, and password. Automatic tunnel initiation is disabled if secure unit authentication is enabled.

Note![]() If the Easy VPN hardware client is using NEM and has connections to secondary servers, use the crypto map set reverse-route command on each headend device to configure dynamic announcements of the remote network using Reverse Route Injection (RRI).
If the Easy VPN hardware client is using NEM and has connections to secondary servers, use the crypto map set reverse-route command on each headend device to configure dynamic announcements of the remote network using Reverse Route Injection (RRI).
To specify the mode for Easy VPN Clients, enter the following command in configuration mode:
[ no ] vpnclient mode { client-mode | network-extension-mode }
no removes the command from the running configuration.
NEM with Multiple Interfaces
If you have an ASA 5505 security appliance (version 7.2 (3) and higher) configured as an Easy VPN Client in Network Extension Mode with multiple interfaces configured, the security appliance builds a tunnel for locally encrypted traffic only from the interface with the highest security level.
For example, consider the following configuration:
In this scenario, the security appliance builds the tunnel only for vlan1, the interface with the highest security level. If you want to encrypt traffic from vlan12, you must change the security level of interface vlan1 to a lower value than that of vlan 12.
Configuring Automatic Xauth Authentication
The ASA 5505 configured as an Easy VPN hardware client automatically authenticates when it connects to the Easy VPN server if all of the following conditions are true:
- Secure unit authentication is disabled on the server.
- The server requests IKE Extended Authenticate (Xauth) credentials.
Xauth provides the capability of authenticating a user within IKE using TACACS+ or RADIUS. Xauth authenticates a user (in this case, the Easy VPN hardware client) using RADIUS or any of the other supported user authentication protocols.
Enter the following command in global configuration mode to configure the Xauth username and password:
vpnclient username xauth_username password xauth password
You can use up to 64 characters for each.
For example, enter the following command to configure the Easy VPN hardware client to use the XAUTH username testuser and password ppurkm1:
ciscoasa(config)# vpnclient username testuser password ppurkm1
ciscoasa(config)#
To remove the username and password from the running configuration, enter the following command:
ciscoasa(config)# no vpnclient username
ciscoasa(config)#
Configuring IPsec Over TCP
By default, the Easy VPN hardware client and server encapsulate IPsec in User Datagram Protocol (UDP) packets. Some environments, such as those with certain firewall rules, or NAT and PAT devices, prohibit UDP. To use standard Encapsulating Security Protocol (ESP, Protocol 50) or Internet Key Exchange (IKE, UDP 500) in such environments, you must configure the client and the server to encapsulate IPsec within TCP packets to enable secure tunneling. If your environment allows UDP, however, configuring IPsec over TCP adds unnecessary overhead.
To configure the Easy VPN hardware client to use TCP-encapsulated IPsec, enter the following command in global configuration mode:
vpnclient ipsec-over-tcp [ port tcp_port ]
The Easy VPN hardware client uses port 10000 if the command does not specify a port number.
If you configure an ASA 5505 to use TCP-encapsulated IPsec, enter the following command to let it send large packets over the outside interface:
This command clears the Don't Fragment (DF) bit from the encapsulated header. A DF bit is a bit within the IP header that determines whether the packet can be fragmented. This command lets the Easy VPN hardware client send packets that are larger than the MTU size.
The following example shows how to configure the Easy VPN hardware client to use TCP-encapsulated IPsec, using the default port 10000, and to let it send large packets over the outside interface:
ciscoasa(config)# vpnclient ipsec-over-tcp
ciscoasa(config)#
The next example shows how to configure the Easy VPN hardware client to use TCP-encapsulated IPsec, using the port 10501, and to let it send large packets over the outside interface:
ciscoasa(config)# vpnclient ipsec-over-tcp port 10501
ciscoasa(config)#
To remove the attribute from the running configuration, use the no form of this command, as follows:
ciscoasa(config)# no vpnclient ipsec-over-tcp
ciscoasa(config)#
Comparing Tunneling Options
The tunnel types the Cisco ASA 5505 configured as an Easy VPN hardware client sets up depends on a combination of the following factors:
- Use of the split-tunnel-network-list and the split-tunnel-policy commands on the headend to permit, restrict, or prohibit split tunneling. (See the Specify a Network List for Split-Tunneling and “Set the Split-Tunneling Policy” section, respectively.)
Split tunneling determines the networks for which the remote-access client encrypts and sends data through the secured VPN tunnel, and determines which traffic it sends to the Internet in the clear.
- Use of the vpnclient management command to specify one of the following automatic tunnel initiation options:
–![]() tunnel to limit administrative access to the client side by specific hosts or networks on the corporate side and use IPsec to add a layer of encryption to the management sessions over the HTTPS or SSH encryption that is already present.
tunnel to limit administrative access to the client side by specific hosts or networks on the corporate side and use IPsec to add a layer of encryption to the management sessions over the HTTPS or SSH encryption that is already present.
–![]() clear to permit administrative access using the HTTPS or SSH encryption used by the management session.
clear to permit administrative access using the HTTPS or SSH encryption used by the management session.
–![]() no to prohibit management access
no to prohibit management access

- Use of the vpnclient mode command to specify one of the following modes of operation:
–![]() client to use Port Address Translation (PAT) mode to isolate the addresses of the inside hosts, relative to the client, from the enterprise network.
client to use Port Address Translation (PAT) mode to isolate the addresses of the inside hosts, relative to the client, from the enterprise network.
–![]() network-extension-mode to make those addresses accessible from the enterprise network.
network-extension-mode to make those addresses accessible from the enterprise network.
Figure 8-1 shows the types of tunnels that the Easy VPN client initiates, based on the combination of the commands you enter.
Figure 8-1 Easy VPN Hardware Client Tunneling Options for the Cisco ASA 5505
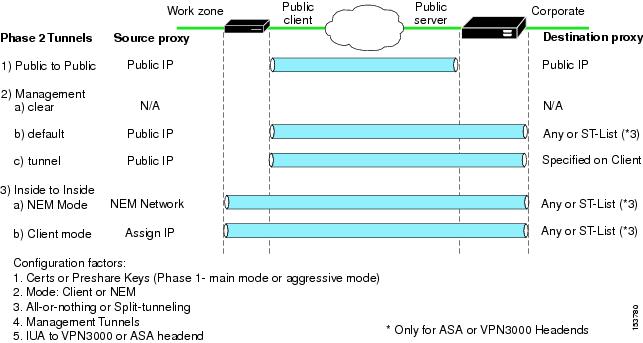
The term “All-Or-Nothing” refers to the presence or absence of an ACL for split tunneling. The ACL (“ST-list”) distinguishes networks that require tunneling from those that do not.
Specifying the Tunnel Group or Trustpoint
When configuring the Cisco ASA 5505 as an Easy VPN hardware client, you can specify a tunnel group or trustpoint configured on the Easy VPN server, depending on the Easy VPN server configuration. See the section that names the option you want to use:
Specifying the Tunnel Group
Enter the following command in global configuration mode to specify the name of the VPN tunnel group and password for the Easy VPN client connection to the server:
vpnclient vpngroup group_name password preshared_key
group_name is the name of the VPN tunnel group configured on the Easy VPN server. You must configure this tunnel group on the server before establishing a connection.
preshared_key is the IKE pre-shared key used for authentication on the Easy VPN server.
For example, enter the following command to identify the VPN tunnel group named TestGroup1 and the IKE preshared key my_key123.
ciscoasa(config)# vpnclient vpngroup TestGroup1 password my_key123
ciscoasa(config)#
To remove the attribute from the running configuration, enter the following command:
If the configuration of the ASA 5505 running as an Easy VPN client does not specify a tunnel group, the client attempts to use an RSA certificate.
ciscoasa(config)# no vpnclient vpngroup
ciscoasa(config)#
Specifying the Trustpoint
A trustpoint represents a CA identity, and possibly a device identity, based on a certificate the CA issues. These parameters specify how the ASA obtains its certificate from the CA and define the authentication policies for user certificates issued by the CA.
First define the trustpoint using the crypto ca trustpoint command, as described in the general operations configuration guide. Then enter the following command in global configuration mode to name the trustpoint identifying the RSA certificate to use for authentication:
vpnclient trustpoint trustpoint_name [ chain ]
trustpoint_name names the trustpoint identifying the RSA certificate to use for authentication.
(Optional) chain sends the entire certificate chain.
For example, enter the following command to specify the identity certificate named central and send the entire certificate chain:
ciscoasa(config)# vpnclient trustpoint central chain
ciscoasa(config)#
To remove the attribute from the running configuration, enter the following command:
ciscoasa(config)# no vpnclient trustpoint
ciscoasa(config)#
Configuring Split Tunneling
Split tunneling lets a remote-access IPsec client conditionally direct packets over an IPsec tunnel in encrypted form or to a network interface in clear text form.
The Easy VPN server pushes the split tunneling attributes from the group policy to the Easy VPN Client for use only in the work zone. See Configuring Split-Tunneling for AnyConnect Traffic to configure split tunneling on the Cisco ASA 5505.
Enter the following command in global configuration mode to enable the automatic initiation of IPsec tunnels when NEM and split tunneling are configured:
[ no ] vpnclient nem-st-autoconnect
no removes the command from the running configuration.
ciscoasa(config)# vpnclient nem-st-autoconnect
ciscoasa(config)#
Configuring Device Pass-Through
Devices such as Cisco IP phones, wireless access points, and printers are incapable of performing authentication. Enter the following command in global configuration mode to exempt such devices from authentication, thereby providing network access to them, if individual user authentication is enabled:
[ no ] vpnclient mac-exempt mac_addr_1 mac_mask_1 [ mac_addr_2 mac_mask_2...mac_addr_n mac_mask_n ]
no removes the command from the running configuration.
mac_addr is the MAC address, in dotted hexadecimal notation, of the device to bypass individual user authentication.
mac_mask is the network mask for the corresponding MAC address. A MAC mask of ffff.ff00.0000 matches all devices made by the same manufacturer. A MAC mask of ffff.ffff.ffff matches a single device.

Note![]() The mac-exempt list cannot exceed 15.
The mac-exempt list cannot exceed 15.
Only the first six characters of the specific MAC address are required if you use the MAC mask ffff.ff00.0000 to specify all devices by the same manufacturer. For example, Cisco IP phones have the Manufacturer ID 00036b, so the following command exempts any Cisco IP phone, including Cisco IP phones, you might add in the future:
ciscoasa(config)# vpnclient mac-exempt 0003.6b00.0000 ffff.ff00.0000
ciscoasa(config)#
The next example provides greater security but less flexibility because it exempts one specific Cisco IP phone:
ciscoasa(config)# vpnclient mac-exempt 0003.6b54.b213 ffff.ffff.ffff
ciscoasa(config)#

Note![]() Make sure you have Individual User Authentiction and User Bypass configured on the headend device. For example, if you have the ASA as the headend, configure the following under group policy:
Make sure you have Individual User Authentiction and User Bypass configured on the headend device. For example, if you have the ASA as the headend, configure the following under group policy:
hostname(config-group-policy)#user-authentication enable
hostname(config-group-policy)#ip-phone-bypass enable
Configuring Remote Management
The Cisco ASA 5505, operating as an Easy VPN hardware client, supports management access using SSH or HTTPS, with or without a second layer of additional encryption. You can configure the Cisco ASA 5505 to require IPsec encryption within the SSH or HTTPS encryption.
Use the vpnclient management clear command in global configuration mode to use normal routing to provide management access from the corporate network to the outside interface of the ASA 5505 (no tunneling management packets).

Use the vpnclient management tunnel command in global configuration mode if you want to automate the creation of IPsec tunnels to provide management access from the corporate network to the outside interface of the ASA 5505. The Easy VPN hardware client and server create the tunnels automatically after the execution of the vpnclient server command. The syntax of the vpnclient management tunnel command follows:
vpnclient management tunnel ip_addr_1 ip_mask_1 [ip_addr_2 ip_mask_2...ip_addr_n ip_mask_n]

Note![]() Regardless of your configuration, DHCP requests (including renew messages) should not flow over IPsec tunnels. Even with a vpnclient management tunnel, DHCP traffic is prohibited.
Regardless of your configuration, DHCP requests (including renew messages) should not flow over IPsec tunnels. Even with a vpnclient management tunnel, DHCP traffic is prohibited.
For example, enter the following command to automate the creation of an IPsec tunnel to provide management access to the host with IP address 192.168.10.10:
ciscoasa(config)# vpnclient management tunnel 192.198.10.10 255.255.255.0
ciscoasa(config)#
The no form of this command sets up IPsec for management tunnels in accordance with the split-tunnel-policy and split-tunnel-network-list commands.
ciscoasa(config)# no vpnclient management
ciscoasa(config)#
Guidelines for Configuring the Easy VPN Server
The following sections address the Easy VPN hardware client considerations that apply to the Easy VPN server:
Group Policy and User Attributes Pushed to the Client
Upon tunnel establishment, the Easy VPN server pushes the values of the group policy or user attributes stored in its configuration to the Easy VPN hardware client. Therefore, to change certain attributes pushed to the Easy VPN hardware client, you must modify them on the ASAs configured as the primary and secondary Easy VPN servers. This section identifies the group policy and user attributes pushed to the Easy VPN hardware client.

Note![]() This section serves only as a reference. For complete instructions on configuring group policies and users, see Configuring Connection Profiles, Group Policies, and Users.
This section serves only as a reference. For complete instructions on configuring group policies and users, see Configuring Connection Profiles, Group Policies, and Users.
Use Table 8-2 as a guide for determining which commands to enter to modify the group policy or user attributes.

Note![]() IPsec NAT-T connections are the only IPsec connection types supported on the home VLAN of a Cisco ASA 5505. IPsec over TCP and native IPsec connections are not supported.
IPsec NAT-T connections are the only IPsec connection types supported on the home VLAN of a Cisco ASA 5505. IPsec over TCP and native IPsec connections are not supported.
Authentication Options
The ASA 5505 supports the following authentication mechanisms, which it obtains from the group policy stored on the Easy VPN Server. The following list identifies the authentication options supported by the Easy VPN hardware client, however, you must configure them on the Easy VPN server:
Ignores the vpnclient username Xauth command (described in “Configuring Automatic Xauth Authentication” section) and requires the user to authenticate the ASA 5505 by entering a password. By default, SUA is disabled. You can use the secure-unit-authentication enable command in group-policy configuration mode to enable SUA. See Configuring Secure Unit Authentication.
Requires users behind the ASA 5505 to authenticate before granting them access to the enterprise VPN network. By default, IUA is disabled. To enable the IUA, use the user-authentication enable command in group-policy configuration mode. See Configuring User Authentication.
The security appliance works correctly from behind a NAT device, and if the ASA5505 is configured in NAT mode, the provisioned IP (to which the clients all PAT) is injected into the routing table on the central-site device.

Use the user-authentication-idle-timeout command to set or remove the idle timeout period after which the Easy VPN Server terminates the client’s access. See Configuring an Idle Timeout.
The Cisco Easy VPN server intercepts HTTP traffic and redirects the user to a login page if one of the following is true:
–![]() SUA or the username and password are not configured on the Easy VPN hardware client.
SUA or the username and password are not configured on the Easy VPN hardware client.
HTTP redirection is automatic and does not require configuration on the Easy VPN Server.
The ASA 5505 supports preshared keys, token-based (e.g., SDI one-time passwords), and “no user authentication” for user authentication. NOTE : The Cisco Easy VPN server can use the digital certificate as part of user authorization. See Chapter 1, “Configuring IPsec and ISAKMP” for instructions.
 Feedback
Feedback