Release Notes for IoT Field Network Director, Release 4.7.x
These release notes contain the latest information about using the user interface for IoT Field Network Director (FND), Release 4.7 to configure and manage IPv6 mesh endpoints, Cisco 1000 Series Connected Grid Routers (CGR1120 or CGR1240), Cisco 800 Series Integrated Services Routers (C800), Cisco LoRaWAN IXM Gateway, Cisco 500 WPAN Industrial Routers (IR500), Cisco 5921 (ESR5921) Embedded Service Routers, and Cisco 800 Series Industrial Integrated Services Routers (IR807, IR809, and IR829), Cisco Industrial Compute Gateway IC3000, and Cisco 1101 Integrated Services Router.
IoT FND is a software platform that helps to enable a clear separation between communications network management and operational applications such as distribution management systems, outage management systems, and meter data management in utilities. Use the software to manage a multi-service network of routers or a combination of routers and endpoint devices deployed with end-to-end security for your specific use case.
IoT FND is highly secure, scalable, and modular. Its pluggable architecture can enable network connectivity to a multi-vendor ecosystem of legacy and next-generation IoT devices.
 Note |
The documentation set for this product strives to use bias-free language. For purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. |
Cisco IoT FND Documentation
Listed below are the documents that support this release:
-
Cisco IoT FND Deployment on an Open Virtual Appliance, VMware ESXi 5.5/6.0/6.5
-
Cisco IoT Field Network Director Installation Guide-Oracle Deployment, Releases 4.3.x and Later
Please refer to the Cisco IoT Field Network Director data sheet for an extensive list of the product capabilities and the required licenses to support specific platforms management by the FND application.
 Note |
IoT FND was previously named Connected Grid Network Management System (CG-NMS) for releases 2.x and 1.x. |
 Note |
IoT FND Release 4.7.2 is a bug fix release only. There are no new features. |
Conventions
This document uses the following conventions.
| Conventions | Indication |
|---|---|
| bold font |
Commands and keywords and user-entered text appear in bold font. |
|
italic font |
Document titles, new or emphasized terms, and arguments for which you supply values are in italic font. |
|
[ ] |
Elements in square brackets are optional. |
|
{x | y | z } |
Required alternative keywords are grouped in braces and separated by vertical bars. |
|
[ x | y | z ] |
Optional alternative keywords are grouped in brackets and separated by vertical bars. |
|
string |
A nonquoted set of characters. Do not use quotation marks around the string or the string will include the quotation marks. |
|
courier font |
Terminal sessions and information the system displays appear in courier font. |
|
< > |
Nonprinting characters such as passwords are in angle brackets. |
|
[ ] |
Default responses to system prompts are in square brackets. |
|
!, # |
An exclamation point (!) or a pound sign (#) at the beginning of a line of code indicates a comment line. |
 Note |
Means reader take note . Notes contain helpful suggestions or references to material not covered in the manual. |
 Caution |
Means reader be careful. In this situation, you might perform an action that could result in equipment damage or loss of data. |
 Warning |
IMPORTANT SAFETY INSTRUCTIONS Means danger. You are in a situation that could cause bodily injury. Before you work on any equipment, be aware of the hazards involved with electrical circuitry and be familiar with standard practices for preventing accidents. Use the statement number provided at the end of each warning to locate its transaltion in the translated safety warnings that accompanied this device. SAVE THESE INSTRUCTIONS. |
About Cisco IoT FND
The IoT Field Network Director (IoT FND) is a software platform that helps to enable a clear separation between communications network management and operational applications such as distribution management systems, outage management systems, and meter data management in utilities.
Through the browser-based interface, use the software to manage a multi-service network of routers or a combination of routers and endpoint devices such as:
-
Cisco 1101 Series Integrated Services Routers (ISRs) with Cisco IOS XE Software combine Internet access, comprehensive security, and wireless services (LTE Advanced 3.0 wireless WAN and 802.11ac wireless LAN) in a single, high-performance device. The Cisco 1101 Series ISRs are well-suited for deployment as Customer Premises Equipment (CPE) in enterprise branch offices, in service provider managed environments as well as smaller form factor and M2M use cases.
-
Cisco 800 Series Industrial Integrated Services Routers (IR800s) are ruggedized small-form factor cellular routers for mobile/vehicle applications. IR829 includes Wi-Fi providing connectivity in non-carpeted IT spaces, industrials, utilities, transportation, infrastructure, industrial M2M application, asset monitoring, Smart Grid, and utility applications. These devices are referred to as FARs in this document and identified by product ID (for example, IR800) on the Field Devices page. You can use IoT FND to manage the following IR800 models: IR809 and IR829.
-
Cisco 800 Series Integrated Services Routers (C800s) are used in most networks as edge routers or gateways to provide WAN connectivity (cellular, satellite over Ethernet, and Wi-Fi) to an end device (energy-distribution automation devices, other verticals such as ATMs, and mobile deployments). These devices are referred to as FARs in this document and identified by product ID (for example, C800 or C819) on the Field Devices page.
-
Cisco 500 Series Wireless Personal Area Network (WPAN) Industrial Routers (IR500) supply RF mesh connectivity to IPv6 and serial Internet of Things (IoT) devices (for example, recloser control, cap bank control, voltage regulator controls, and other remote terminal units).
-
The Cisco Wireless Gateway for LoRaWAN (IXM-LPWA-800, IXM-LPWA-900) can be a standalone product that connects to Ethernet switches or routers or connects to LAN ports of the Cisco 800 Series Industrial Integrated Services Routers. This gateway can be configured as a radio interface of the Cisco Industrial Routers 809 and 829. One or multiple gateways are connected to the LAN port(s) of the IR809 or IR829 via Ethernet or VLANs with encrypted links. Through this configuration, it provides LoRaWAN radio access while the IR809 or IR829 offer backhaul support for Gigabit Ethernet (electrical or fiber), 4G/LTE, or Wi-Fi.
-
Cisco Interface Module for LoRaWAN is an extension module for the industrial routers, Cisco IR809 and IR829, and serves as a carrier-grade gateway for outdoor deployments. The module provides unlicensed low-power wide area (LPWA) wireless connectivity for a range of Internet of Things (IoT) use cases such as asset tracking, water and gas metering, street lighting, smart parking/building/agriculture, and environment monitoring. There are two models supported, which are differentiated by their band support (863-870 MHz ISM or 902-928 MHz ISM). The module is identified by product ID (for example, IXM-LORA-800-H-V2).
-
Cisco 800 Series Access Points are integrated with C800 and IR829 platforms. These access points are referred to as FARs in this document and identified by product ID (for example, AP800).
-
Cisco ASR 1000 Series Aggregation Services Routers (ASRs) and Cisco 4000 Series Integrated Service Routers (ISRs) are referred to as head-end routers or HERs in this document.
-
Cisco IPv6 RF mesh endpoints (smart meters and range extenders).
 Note |
CGRs, C800, IR800s, IR500s, and other types of mesh endpoint devices can coexist on a network, but cannot be in the same device group or firmware management group. Refer to the following sections in the IoT Field Network Director User Guide for more information: Creating Device Groups, Working with Resilient Mesh Endpoint Firmware Images, and Configuring Firmware Group Settings. |
The software features enterprise-class fault, configuration, accounting, performance, and security (FCAPS) functionality, as defined in the OSI Network Management reference model.
Cisco IoT FND Features and Capabilities
-
Configuration Management– Cisco IoT FND facilitates configuration of large numbers of Cisco FAR, HER, gateways, and endpoints. Use Cisco IoT FND to bulk-configure devices by placing them into configuration groups, editing settings in a configuration template, and then pushing the configuration to all devices in the group.
-
Device Management– Cisco IoT FND displays easy-to-read tabular views of extensive information generated by devices, allowing you to monitor your network for errors. Cisco IoT FND provides integrated Geographic Information System (GIS) map-based visualization of FAN devices such as routers and smart meters.
-
Firmware Management – Cisco IoT FND serves as a repository for Cisco CGR, Cisco C800s, Cisco IR800, IR500, and mesh endpoint firmware images. Use Cisco IoT FND to upgrade the firmware on groups of similar devices by loading the firmware image file onto the Cisco IoT FND server, and then uploading the image to the devices in the group. Once uploaded, use IoT FND to install the firmware image directly on the devices.
-
Zero Touch Deployment – Ease of deployment at scale with Zero-Touch Deployment (ZTD) of gateways and routers.
-
Tunnel Provisioning– Protects data exchanged between Cisco ASRs and Cisco CGRs and C800s, and prevents unauthorized access to Cisco CGRs to provide secure communication between devices. Cisco IoT FND can execute CLI commands to provision secure tunnels between Cisco CGRs, Cisco C800s, Cisco IR800s and Cisco ASRs. Use Cisco IoT FND to bulk-configure tunnel provisioning using groups.
-
IPv6 RPL Tree Polling – The IPv6 Routing Protocol for Low-power and Lossy Networks (RPL) finds neighbors and establishes routes using ICMPv6 message exchanges. RPL manages routes based on the relative position of the endpoint to the CGR that is the root of the routing tree. RPL tree polling is available through the mesh nodes and CGR periodic updates. The RPL tree represents the mesh topology, which is useful for troubleshooting. IoT FND maintains a periodically updated snapshot of the RPL tree.
-
Dynamic Multipoint VPN and Flex VPN– For Cisco C800 devices and Cisco IR800 devices, DMVPN and Flex VPN do not require IoT FND to apply device-specific tunnel configuration to the HER during tunnel provisioning. HER tunnel provisioning is only required for site-to-site VPN tunnels.
-
Dual PHY Support – IoT FND can communicate with devices that support Dual PHY (RF and PLC) traffic. IoT FND identifies CGRs running Dual PHY, enables configuration to masters and slaves, and collects metrics from masters. IoT FND also manages security keys for Dual PHY CGRs. On the mesh side, IoT FND identifies Dual PHY nodes using unique hardware IDs, enables configuration pushes and firmware updates, and collects metrics, including RF and PLC traffic ratios.
-
Device Location Tracking – IoT FND displays real-time location and device location history for CGR1000, C800, IR1101, IR8100, and IR800 devices.
-
Diagnostics and Troubleshooting – The IoT FND rule engine infrastructure provides effective monitoring of triage-based troubleshooting. Device troubleshooting runs on-demand device path trace and ping on any CGR, Cisco C800, Cisco IR800, range extender, or meter (mesh endpoints).
-
High Availability – To ensure uninterrupted network management and monitoring, you can deploy the Cisco IoT FND solution in a High Availability (HA) configuration. By using clusters of load-balanced IoT FND servers and primary and standby IoT FND databases, Cisco IoT FND constantly monitors the health of the system, including connectivity within clusters and server resource usage. If a server cluster member or database becomes unavailable or a tunnel fails, another takes its place seamlessly. Additionally, you can add reliability to your IoT FND solution by configuring redundant tunnels between a Cisco CGR and multiple Cisco ASRs.
-
Power Outage Notifications – Cisco Resilient Mesh Endpoints (RMEs) implement a power outage notification service to support timely and efficient reporting of power outages. In the event of a power outage, CGEs perform the necessary functions to conserve energy and notify neighboring nodes of the outage. FARs relay the power outage notification to IoT FND, which then issues push notifications to customers to relate information on the outage.
-
Audit Logging – Logs access information for user activity for audit, regulatory compliance, and Security Event and Incident Management (SEIM) integration. This simplifies management and enhances compliance by integrated monitoring, reporting, and troubleshooting capabilities.
-
North Bound APIs – Eases integration of existing utility applications such as outage management system (OMS), meter data management (MDM), trouble-ticketing systems, and manager-of-managers.
-
Role-Based Access Controls– Integrates with enterprise security policies and role-based access control for AMI network devices.
-
Event and Issue Management– Fault event collection, filtering, and correlation for communication network monitoring. IoT FND supports a variety of fault-event mechanisms for threshold-based rule processing, custom alarm generation, and alarm event processing. Faults display on a color-coded GIS-map view for various endpoints in the utility network. This allows operator-level custom, fault-event generation, processing, and forwarding to various utility applications such as an outage management system. Automatic issue tracking is based on the events collected.
New Features
 Note |
Do not use an underscore (_) in the FND hostname or OVA template name. |
 Note |
For optimal performance, ensure that the network ping latency between the FND Application Server and Database Server is < 1ms. |
The following table lists new platforms and features that are managed in IoT FND 4.7.x.
| Feature | Description | First IoT FND Release Support | Related Documentation | ||||||
|---|---|---|---|---|---|---|---|---|---|
|
Enhanced Tunnel Reprovisioning and DHCP Addresses |
The Tunnel Provisioning workflow has been modified so that DHCP addresses are released during decommissioning of the Field Area Router (FAR) device rather than during Tunnel Provisioning. To improve Tunnel Provisioning, we have introduced a new property: optimizeTunnelProv By default, tunnel creation and deletion will lock the Head-end Router (HER). However, if the optimizeTunnelProv property is set to ‘true’ either through CSV or cgms.properties, then tunnel creation and deletion will not lock the HER during the operation
This change applies to the management of the followingCisco IOS and Cisco IOS XE Routers:
This change applies to the management of the followingCisco IOS XE Routers:
|
4.7.2-8 |
|||||||
|
Support Expired Cisco SUDI Certificate |
The expiration date for a limited number of Cisco Secure Unique Device Identifier (SUDI) certificates for a limited number of Internet of Things (IoT) products will expire on: Date of Manufacture plus 10 years or 2029-05-14, whichever is earlier. The following Cisco devices are affected by this change:
Note: A previously enrolled device will not be affected by an expired Cisco SUDI certificate. Devices with expired SUDI certificate will not have any authentication issues with FND from now on. |
4.7.1-60 |
|||||||
|
Improved Usability for File Management |
You can modify the width of the Open Issues column that displays for a Field Device when two or more open issues exist by selecting the column and moving the cursor to the left to minimize the size of the column. Additionally, this feature reduces the Open Issues display to a single line of content versus multiple lines and displays three periods (...) to indicate that additional content is available to view by expanding the column to the right. DEVICES > FIELD DEVICES > Browse Devices > Inventory |
4.7.1-60 |
|||||||
|
Device Search Field added to the Device File Management page to Search for a Specific Router |
You can perform partial or full search for a router on the Upload File to Routers page using a router name such as: CGR1120/K9+JAF1641648BBCT CONFIG > DEVICE FILE MANAGEMENT > Actions |
4.7.1-60 |
|||||||
|
Number of Devices that Display on the Upload File to Routers Page Increased to 200 |
By default, a minimum of ten routers display. You can select up to 200 devices to display. CONFIG > DEVICE FILE MANAGEMENT > Actions |
4.7.1-60 |
|||||||
|
Set Time Range and Page Preferences for Events |
On the Events tab for a device, you can define values for Time Range and Page View settings for a device type and apply those same settings to a device of the same type. DEVICES > FIELD DEVICES > {Router | Switch | Endpoint | Gateway] |
4.7.1-60 |
|||||||
|
New Browser Support for FND 4.7.1 |
Microsoft Edge browser Microsoft EdgeHTML: 88.0.705.68 |
4.7.1-60 |
— |
||||||
|
Troubleshooting Page for On Demand Statistics |
A new Troubleshooting tab is available for CG-MESH and IR500 endpoint ‘s on the Device Details page. This new page, allows you to generate the following predefined system reports for the CG-MESH and IR500 endpoints:- All TLVs, Connectivity, General, Registration, and Routing. DEVICES > FIELD DEVICES > ENDPOINT > Troubleshoot tab |
4.7.0-100 |
|||||||
|
Itron Bridge Meter, ITRON30 Support and Management |
An Endpoint Operator can now manage Itron Bridge Meters (such as ITRON30) using IoT FND as a cg-mesh device type (METER-CGMESH). This meter was previously run in RFLAN mode. Only Root and Endpoint operators can see and perform the endpoint operations and scheduling for the channel notch feature. To manage an Itron Bridge Meter in cg-mesh node, an Endpoint Operator (RBAC) must convert the RFLAN meter to a cg-mesh device type and upgrade all CG-mesh firmware to CG-mesh 5.6.x. After successful registration, the channel notch settings (in the bootstrap config.bin file) should be pushed to all nodes by the Endpoint operator. Two new properties: channelNotchMaxAttempts = 20: The maximum attempts to try to send the configuration and schedule info to all the endpoints. channelNotchSettingEnabled=true. Allows you to enable or disable the channel notch feature. |
4.7.0-100 |
|||||||
|
Channel Notch Settings |
You can define up to four pairs of Notch Range Start and End Channels in the Channel Notch Settings page: CONFIG > CHANNEL NOTCH SETTINGS The above page only appears when the cgmesh.properties has the following setting: channelNotchSettingEnabled=true |
4.7.0-100 |
|||||||
|
Channel Notch Configuration page |
You can push and schedule the Channel Notch Configuration Settings in the following new page: CONFIG > CHANNEL NOTCH CONFIG You can initiate the following two actions for those routers whose endpoints have been successfully updated with the channel notch configuration: + button on the router group displays the router name and the corresponding cg-mesh endpoints.
|
4.7.0-100 |
|||||||
|
ITRON30, IR500 and CG-Mesh Device Configuration |
On the ENDPOINT > Default-cgmesh page, you can now perform the additional actions at the Push Configuration tab page found in the right-pane: Select the ‘Push ENDPOINT Re-Enrollment’ option in the drop-down menu on the page, along with the Certificate Re-enrollment Type. Supported certificate re-enrollment options are:
Messages are sent in unicast form. CONFIG > DEVICE CONFIGURATION > Groups > ENDPOINT > Desired Group (Default-ir500 or Meter) > Push CONFIG Select ‘Push Endpoint Re-enrollment’ |
4.7.0-100 |
|||||||
|
Endpoint Re-Enrollment Option for ITRON30 and IR500 Endpoints |
You can now re-enroll a certificate for cg-mesh endpoints by selecting the Re-Enrollment tab on the Device info page of the CGMESH and IR500 endpoints. When you click the Re-enrollment button on the cgmesh or IR500 device details page, it will open a popup window with three options. Select one of the certificates and click Submit. DEVICES > FIELD DEVICES > Browse Devices > ENDPOINT > METER-CGMESH (left pane) Newly added endpoint appears on the Device Config page |
4.7.0-100 |
|||||||
|
DTLS Relay and Certificate Auto Renew Settings for ITRON30 and IR500 Endpoints |
New options are available on the Edit Configuration Template page.
CONFIG > DEVICE CONFIGURATION > Groups > ENDPOINT > Default-CGMesh > Edit Configuration Template CONFIG > DEVICE CONFIGURATION > Groups > ENDPOINT > Default-ir500 > Edit Configuration Template |
4.7.0-100 |
|||||||
|
Certificate Information page for Gateway IR500 Endpoints |
The following certificate information is reported for IR500 endpoints managed by IoT FND on the Certificate Info page (right-pane):
DEVICE > FIELD DEVICES > ENDPOINT > GATEWAY-IR500 Certificate Info |
4.7.0-100 |
|||||||
|
New Device Events for Gateway IR500 Endpoints |
Name of new events supported: MAJOR: Authentication Failure INFO: Authentication Success, CAcert Request, CAcert Response, Email Success, Enroll Request, Enroll Success, SSL Error DEVICE > FIELD DEVICES > Browse Devices > GATEWAY-IR500 > Events |
4.7.0-100 |
|||||||
|
Audit Trail for Re-Enrollment for Gateway-IR500 Endpoints |
The following new Operation will be recorded for Re-Enrollment of the Group: Operation: Re-Enrollment (Get NMS Cert and NPS/AAA Cert) Status: Initiated Details: Group default-cg-mesh, Device category: endpoint ADMIN > SYSTEM MANAGEMENT > AUDIT TRAIL |
4.7.0-100 |
|||||||
|
WiSUN Configuration for IR500 and Itron30 |
|
4.7.0-100 |
|||||||
|
TLS Version Settings for Default-cgmesh Endpoints |
The available settings for the TLS version are:
CONFIG > DEVICE CONFIGURATION > Groups > Endpoint > default-ir500 > Edit Configuration Template |
4.7.0-100 |
|||||||
|
Mesh WiSUN 1.x Power Outage Notifications (PON) and Power Restoration Notifications (PRN) for IR510 |
This feature is supported on IR510 from Mesh Release 6.2 and onward. IR510 can send the WiSUN Outage and Restoration notification when running in WiSUN mode.
OPERATIONS > EVENTS OPERATIONS > ISSUES |
4.7.0-100 |
|||||||
|
Mesh 6.3: Configure Rate Limits for LoWPAN interfaces and IR5xx Ethernet Interfaces and meters (ITRON30, CGREF3) to Defend Against Denial of Service (DoS) Attacks |
You can define a Default Access Control List (ACL) Profile for each protocol (UDP, TCP, ICMP) to control the rate of the traffic sent or received. The rate limit is set in kbits/unit. A configuration push will fail if the rate exceeds the configured limit. CONFIG > DEVICE CONFIGURATION> Config Profiles > ACL Profile > Default ACL Profile |
4.7.0-100 |
|||||||
|
Interface ACL Settings for Lowpan in the Config Push Template |
You can now define an ACL rule in the configuration profile for Lowpan interfaces as well as define rate limits for lowpan interfaces. CONFIG > DEVICE CONFIGURATION> Config Profiles > ACL Profile > Interface ACL Settings |
4.7.0-100 |
|||||||
|
ACL Deny Messages |
A new section on the Device Details page for IR510, IR529 and IR530, shows ITRON30 and CGREF3 meters, displays ACL Deny Message Detail for LoWPAN Interfaces. DEVICES > FIELD DEVICES > ENDPOINT > GATEWAY-IR500 |
4.7.0-100 |
|||||||
|
Bandwidth Efficient Software Transfer (BEST) |
When updating an existing installed software base for IR510, IR530, IR509, IR529 and CGMESH (Itron, CGEREF2, CGEREF3) devices, you have the option to upload only the new FND 4.7 software updates, rather than the full image, by using bspatch and bsdiff version 4.3. The platform image on IR510, IR509, IR530, IR529 and CGMESH (ITRON, CGEREF2, CGEREF3) must be running Mesh 6.3 or greater for this feature to work. To make use of this feature in the FND 4.7 user interface at the CONFIG > FIRMWARE UPDATE > Firmware Management > Upload Image page of your system, you must enable the feature by checking the Install Patch option on that page before you select the Upload Image button. CONFIG > FIRMWARE UPDATE |
4.7.0-100 |
|||||||
|
Enforcing Wi-SUN Firmware Upgrade Rules |
All endpoints in the subnet that are moved to WiSUN mode must have a mesh firmware software version of Mesh 6.3 or greater. IoT FND 4.7 will not allow a software upgrade to proceed if the mesh firmware software version requirement is not met. Additionally, you will not be able to downgrade endpoints from a WiSUN firmware version to a non-WiSUN version. Pop-up messages will appear when an invalid firmware upload or scheduled firmware upload is detected.
|
4.7.0-100 |
|||||||
|
Management of Cisco Wireless Gateway for LoRAWAN (IXM), Release 2.1.0.1 |
IoT FND now manages the following IXM components:
Prerequisite to managing the IXM: Add the following property to cgms.properties and set it to ‘true’ and restart the FND service: trust-ixm-server-cert=true
See Gateway Bootstrap Configuration Template in these release notes. |
4.7.0-100 |
|||||||
|
Oracle 19C Support |
FND 4.7.0 Oracle OVA will have Oracle19C installed in the virtual machine. |
4.7.0-100 |
|||||||
|
Update LDevID for Greenfield and Brownfield deployment |
FND now has tcl scripts, autorenewal_update.tcl, which activates the CLIs, and LDevID-update.tcl, which does file manipulation to update the new certificate information in the before-* config files whenever the LDevID certificate is renewed.
Formerly, when a FAR device renewed its LDevID certificate, the before-* config files were not updated with the new certificate information. As a result, if FND rolled back a FAR device because of a new tunnel or device config push, then the FAR device would reload with its previous certificate information which might have been expired at that time and break any communication with FND.
|
4.7.1-60 |
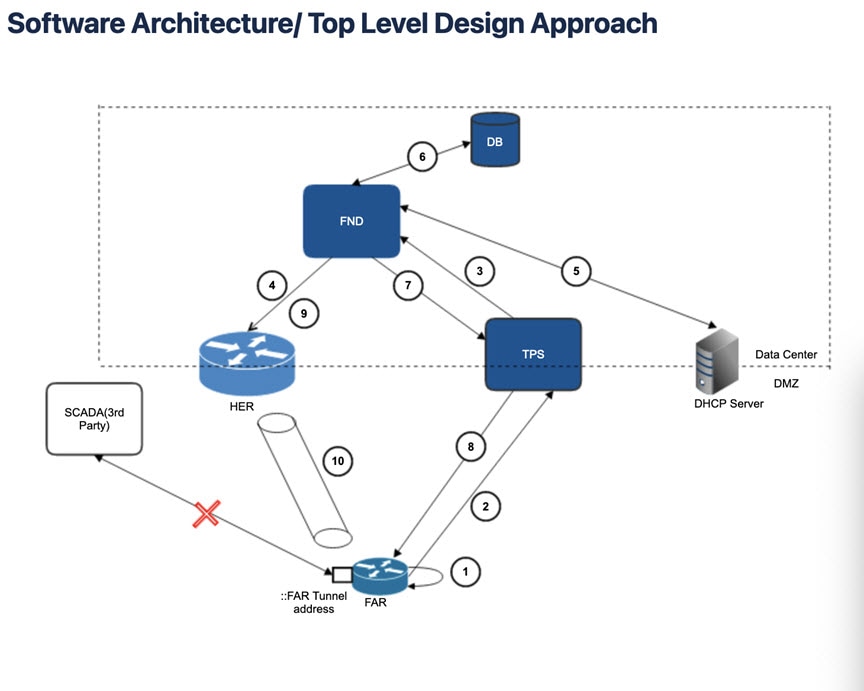
| Step | Activity |
|---|---|
|
1 |
When the Field Area Router (FAR) reboots, it executes the tunnel-provision-template profile. |
|
2 |
FAR connects to the Tunnel Provisioning Server (TPS). |
|
3 |
TPS forwards the request to FND. |
|
4 |
FND initiates the Tunnel Provisioning workflow including removing any older Head-end Router (HER) tunnel configuration. |
|
5 |
FND initiates the Tunnel Addition Template and checks if the IP address is in the Database (DB). If the address is not in the DB, FND will contact the DHCP server to get the address which the FAR will use as the FAR endpoint address while creating the Tunnel. |
|
6 |
The DHCP address is stored on the FND Database. |
|
7 |
FND will then push the processed Tunnel template to the TPS as config commands. |
|
8 |
The Tunnel config commands are then pushed to the FAR. |
|
9 |
FND then pushes the Tunnel Addition template to the Head-end Router (HER) |
|
10 |
A tunnel is then formed between ASR and the FAR with the IP address generated by the DHCP at the FAR side. Note: With release of the DHCP leases for every tunnel reprovisioning, the address which was bound to the FAR Tunnel gets replaced with a new one. This results in the communication to break between the third-party services such as SCADA and FAR since these services might be using the older IP address to connect to the FAR. |
System Requirements
The following table lists the hardware and software versions associated with this release.
 Note |
| Component | Minimum Hardware Requirement | Software Release Requirements | ||||||
|---|---|---|---|---|---|---|---|---|
|
Cisco IoT FND application server (or comparable system that meets the hardware and software requirements) |
|
|
||||||
|
Cisco IoT FND TPS proxy |
|
|
||||||
|
Database server for IoT FND Scalable to 25 routers/10,000 endpoints with minimum hardware requirement. See Resource Management Guidelines for additional scale sizes. |
|
|
||||||
|
Cisco IoT FND Client |
The client must meet the following minimum requirements to connect to the IoT FND application server and view IoT FND. It displays:
|
Supported browsers:
|
||||||
|
Cisco Prime Network Registrar (used as a DHCP server) |
Server must have the following minimum requirements:
|
The following software environment must exist before installing Prime Network Registrar:
|
||||||
|
Hardware Security Module (HSM) |
Luna SA appliance, with client software installed on the IoT FND application servers |
Luna SA appliance:
Luna SA client software:
|
||||||
|
Software Security Module (SSM) |
|
|
 Note |
If deploying a IoT FND server cluster, all nodes in the cluster should run on similar hardware. Additionally, all nodes must run the same version of IoT FND. |
Supported Device Types in IoT FND
| Device Types | Software Release Requirements | ||
|---|---|---|---|
|
FAR |
|||
|
1. Cisco 1101 Series Industrial Integrated Services Routers (IR1101) |
Cisco IOS-XE 17.4.1 |
||
|
2. Cisco CGR1000 Series Connected Grid Router (CGR1120 or CGR1240) |
Cisco IOS Release 15.9(3)M3b |
||
|
3. Cisco 5921 (ESR5921) Embedded Service Routers |
Cisco IOS Release 15.8(3)M2 |
||
|
4. Cisco 800 Series Industrial Integrated Services Router (IR800) |
Cisco IOS Release 15.9(3)M3 |
||
|
5. Cisco 800 Series Integrated Services Router (C800) |
Cisco IOS Release 15.8(3)M2 |
||
|
6. Cisco 800 Series Access Points (AP800) are integrated with C800 and IR829 platforms. |
|
||
| HER | |||
|
1. Cisco ASR 1001 or 1002 Aggregation Services Router (ASR) serving as a head-end router |
Cisco IOS XE Release 16.9.3 for Flex tunnels (IOS) |
||
|
2. Cisco 4000 Series Integrated Service Router (ISR) |
|
||
|
|||
| Compute Gateway | |||
|
Cisco IC3000 Industrial Compute Gateway |
Firmware version —1.4.1 |
||
|
Cisco Resilient Mesh Module and supported endpoints |
|
||
|
Cisco RF Mesh endpoints |
|
||
|
Cisco 500 Series Wireless Personal Area Network (WPAN) Industrial Routers (IR500) |
|
||
| LoRaWAN | |||
|
Long Range Wide Area Network (LoRaWAN) Interface Module for Cisco 800 Series Industrial Integrated Services Routers (IR800) |
LoRa/IXM-LPWA—Firmware version is 2.0.32 |
||
Resource Management Guidelines
Virtual machine (VM) configuration workload characterization is important. When using multiple VMs on the same physical host, allocate resources so that individual VMs do not impact the performance of other VMs. For example, to allocate 4 VMs on a 8-CPU host, do not allocate all 8 CPUs to ensure that one (or more) VM does not use all resources.
The following table lists example Oracle database server usage profiles for important resource parameters such as CPU, memory, and disk space.
| Nodes (Routers/Endpoints) | CPU(Virtual Cores) | Memory(RAM GB) | Disk Space (GB) |
|---|---|---|---|
|
25/10,000 |
2 |
16 |
100 |
|
50/50,000 |
4 |
16 |
200 |
|
500/500,000 |
8 |
32 |
500 |
|
1,000/1,000,000 |
12 |
48 |
1000 |
|
2,000/2,000,000 |
16 |
64 |
1000 |
|
6,000/6,000,000 |
20 |
96 |
1000 |
The following table lists example IoT FND Application server usage profiles for important resource parameters such as CPU, memory, and disk space.
| Nodes(Routers/Endpoints) | CPU(Virtual Cores) | Memory(RAM GB) | Disk Space (GB) |
|---|---|---|---|
|
25/10,000 |
2 |
16 |
100 |
|
50/50,000 |
4 |
16 |
200 |
|
500/500,000 |
4 |
16 |
250 |
|
1,000/1,000,000 |
8 |
16 |
250 |
|
2,000/2,000,000 1 |
8 |
16 |
500 |
|
5,000/5,000,000 1 |
8 |
16 |
500 |
|
6,000/6,000,000 |
8 |
16 |
500 |
-
Clustered installations.
 Note |
RAID 10 is mandatory for deployments of 2 million endpoints and above. |
For Router Only Deployments
Information in the following tables is relevant to Router Only deployments.
| Nodes(IR800/LoRa modules) | CPU(Virtual Cores) | Memory (RAM GB) | Disk Space (GB) |
|---|---|---|---|
|
10,000/30,000 |
4 |
24 |
100 |
| Nodes(IR800/LoRa modules) | CPU(Virtual Cores) | Memory(RAM GB) | Disk Space (GB) |
|---|---|---|---|
|
10,000/30,000 |
6 |
32 |
500 |
OpenSSH Version
Since IoT FND is supported on a variety of Red Hat Enterprise Linux (RHEL) 5 Update releases, the OpenSSH version that comes with a given release might be an older version with known security holes. Consequently, we recommend ensuring that OpenSSH on the RHEL IoT FND server is up to date. On initial installation, upgrade the OpenSSH package in the IoT FND server to version (7.7).
IoT FND Release 4.x Upgrade Matrix Table
This section provides IoT FND upgrade information based on the current and target releases.
| Target Release | You Can Upgrade to the Target Release (Left column) from the Following Releases (Right Column) | |
|---|---|---|
|
4.7.2-xx |
4.7.1-60 4.7.0-100 |
4.6.1-61 |
|
4.7.1-60 |
4.7.0-100 |
4.6.1-61 |
|
4.7.0-100 |
4.6.1-61 |
4.5.1-11 |
|
4.6.1-61 |
4.5.1-11 |
4.4.4-9 4.4.3-4 4.4.2-11 4.4.1-10 4.4.0-79 |
|
4.5.1-11 |
4.4.2-11 4.4.1-10 4.4.0-79 |
4.3.2-7 4.3.1-7 4.3.0-133 |
|
4.4.x |
4.3.1-7 4.3.0-133 |
4.2.0-123 |
|
4.3.x |
4.2.0-123 |
4.1.1-64.1.0-257 |
|
4.2.0-123 |
4.1.0-257 |
4.0.0-299 |
 Note |
Target Release versions allow upgrades from the two prior major releases and its maintenance releases unless the maintenance release was released after the Target version. |
If the current version is not within the two prior versions of the target release, then multiple upgrade hops will be required to get to the target release. Use the table above to plan the upgrade paths.
The system must be upgraded to each intermediate version(s) followed by starting the FND application and allowing it to stabilize. This allows the FND application to perform necessary modifications of databases during startup. The ability to log on to FND is the best indication of completion of these startup modifications.
EXAMPLE:
If your network is running FND 4.4.0-79 and your Target Release is 4.7.0-100, then your best upgrade path would be:
-
Upgrade 4.4.0-79 to 4.6.1-61 and then upgrade to 4.7.0-100
Recommended steps for the multi-hop upgrade noted above are:
-
Backup FND 4.4.0-79 database.
-
Perform an upgrade to FND 4.6.1-61 using the upgrade instructions in the Install Guide.
-
Start FND 4.6.1-61 and login to the FND user interface and perform a quick sanity check.
-
Stop FND 4.6.1-61 services.
-
Backup FND 4.6.1-61 database.
-
Upgrade to FND 4.7.0-100 using the upgrade instructions in the Install Guide.
-
Start FND 4.7.0-100 and login to the GUI.
Hardware Security Module (HSM) Upgrade Table
For IoT-FND Release 4.6.2 and greater, within the IoT-FND image bundle, there are new sub-folders for the jar and API files: /opt/cgms/safenet/LunaX, so, there is no need to backup the software.
 Note |
LunaProvider.jar and libLunaAPI files contain the HSM library patch for the defect CSCvs83557. |
The table below lists the HSM client versions that are tested and recommended for the corresponding Cisco IoT FND software versions. However, FND application software is backward compatible with HSM client versions. For example, FND version 4.7.1 is compatible with older versions of HSM client such as 5.4, 6.3.
| FND Software Release | HSM Client | HSM Hardware |
|---|---|---|
|
4.7.1 |
10.2 |
7.4 |
|
4.6 |
7.3 with software patch |
7.4 |
|
4.5 |
7.3 with software patch |
7.3 |
|
4.4 |
7.3 with software patch |
7.0 |
Gateway Bootstrap Configuration Template
Add the following Gateway Bootstrap Configuration template to LoRAWAN in Tunnel Provisioning Page before triggering PNP on the device.
Enter the following commands:
hostname <hostname>
!crypto ipsec profile primary
ipaddr <ipaddr> iketime 86000 keytime 86000 aes 256
subnet <subnet> ip>/24
exit
ip domain lookup
ip domain name cisco.com
ip host fnd.iot.cisco.com <fnd ip address>
!
interface Fast Ethernet 0/1
ipaddress dhcp
exit
!
ip default-gateway <default gateway ip>
!
username <username> password <password>
!
ip ssh authenticaton-retires 3
radio off
ip ssh admin-access
ip ssh port 22
!
ntp server ip <ntp server ip>
ipsec isakmp admin <password> group 19 <password>
ipsec enable
!
igma secure enable
!
igms event destination <FND IP> 5683
!
igma profile iot-fnd-register
active
add-command show fpga
add-command show inventory
add-command show ip interface FastEthernet 0/1
add-command show ipsec status info
add-command show platform status
add-command show radio
add-command show version
interval 2
url https://fnd.iot.cisco.com:9121/igma/register
exit
!
igma local-trustpoint sudiInstall Sudi Certificate with 2099 expiry in FND and TPS keystore
Sudi 2099 has to be installed in FND and TPS for compatibility with newer versions of images for devices.
Limitations and Restrictions
Cisco recommends that you review this section before you begin working with IoT FND. These are known limitations, and there is not always a workaround for these issues. Some features might not work as documented, and some features might be affected by recent changes to the software.
|
Feature |
IoT FND Releases |
Upgrade Impact |
|---|---|---|
|
Firmware Upgrade during PnP |
4.4 onwards |
The PnP work flow supports device upgrade only if the target image version is higher than the running (current) image version. If the target image runs the same or lower version, then the device upgrade is skipped during the PnP work flow. |
|
External DHCP support for tunnel provisioning |
Applicable to all IoT FND releases |
External DHCP is not supported for tunnel provisioning in the Postgres-OVA deployment. |
|
IPv6 address swap between FND container and FogD container |
Applicable to all releases of IoT FND Postgres-OVA deployments |
The IPv6 address is swapped between FND container and FogD container whenever there is a reboot. The IPv6 address swap restricts the tunnel provisioning operations to complete (pushing tunnel configuration to the router). Workaround: FND container IPv6 address should be static. Configure the field "outbound-proxy-allowed-addresses" in the tunnel provisioning server with FND-container IP for the tunnel operations to run consistently. |
Caveats
This section presents open and resolved caveats in this release and information on using the Bug Search Tool to view details on those caveats. Section topics are:
Open Caveats
There are no known Open Caveats.
Resolved Caveats
|
Caveat Number |
Description |
|---|---|
|
CSCvt38501 |
FND CGMS setup script corrupts RAC setup (SF# 889732) |
|
CSCvv02183 |
Need to revisit tunnel repro and DHCP addresses release workflows (enhancement) (Resolved in FND 4.7.2) |
|
CSCvv44554 |
Upgrade status stuck as 35% for a few IR829 during bulk IOS installation with FND instance in GMM |
|
CSCvx41566 |
FND keeps sending the same outage and restore events repeatedly to outage event subscribes |
|
CSCvx41677 |
Data import of devices causing CPU and Memory spikes |
|
CSCvw07363 |
Unable to move devices within domain’s firmware groups |
|
CSCvw27421 |
FND: Push status shows “ERROR” when [you] do re-enrollment on Itron30 |
|
CSCvw27368 |
ZTD provisioning settings - no verification and cgnms.propoerties check |
|
CSCvw28528 |
Nullpointer exception when processing IR500 periodic |
|
CSCvy55237 |
[Fw_upload] FW upgrade for IR1101 failing in 4.7.1 postgres ova (Resolved in FND 4.7.2) |
|
CSCvz18999 |
Endpoints States Over Time and Router States Over Time Dashboard UI error for non-root users (Resolved in FND 4.7.2) |
Accessing the Bug Search Tool
You can use the Bug Search Tool to find information about caveats for this release, including a description of the problems and available workarounds. The Bug Search Tool lists both open and resolved caveats.
To access the Bug Search Tool, you need the following items:
-
Internet connection
-
Web browser
-
Cisco.com user ID and password
To access the Bug Search Tool, use the following URL: https://bst.cloudapps.cisco.com/bugsearch
End of Life Bulletins for FND Releases
The following IoT FND releases are End of Life (EOL):
End of Sale and End of Life Bulletin for IoT Device Manager
Related Products
In addition to Cisco IoT FND, you can use the following tools to manage the Cisco 1000 Series Connected Grid Routers (CGR1000), the Cisco 800 Series Industrial Integrated Routers (IR800), and the Cisco 500 Series WPAN Industrial Routers (IR500):
Command Line Interface
Use the command line interface (CLI) to configure, manage, and monitor the routers noted above.
Cisco IoT Device Manager
The Cisco IoT Device Manager (IoT-DM or Device Manager) is a Windows-based application for field management of a single router at a time. IoT-DM uses a local Ethernet or WiFi link to connect to the routers noted above.
Related Documentation
Find Cisco 1000 Series Connected Grid Routers documentation at:
For information on additional devices or applications referenced in this release note, see the following documentation on Cisco.com:
 Feedback
Feedback