CCM —continuity check message. A multicast CFM frame that a MEP transmits periodically to ensure continuity across the maintenance
entities to which the transmitting MEP belongs, at the MA level on which the CCM is sent. No reply is sent in response to
receiving a CCM.
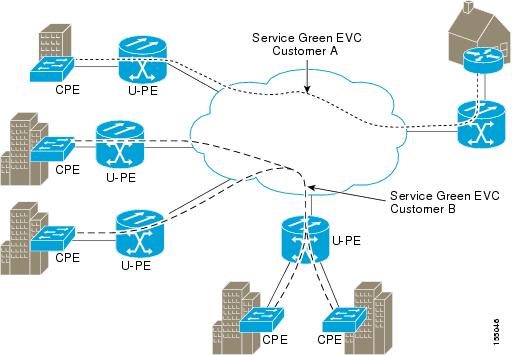
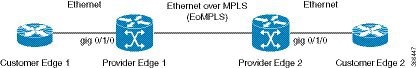
EVC —Ethernet virtual connection. An association of two or more user-network interfaces.
fault
alarm —An out-of-band signal, typically an SNMP notification, that notifies a system administrator of a connectivity failure.
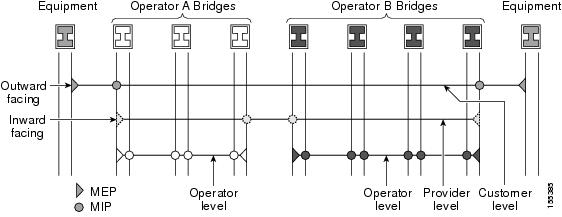
inward-facing
MEP —A MEP that resides in a bridge and transmits to and receives CFM messages from the direction of the bridge relay entity.
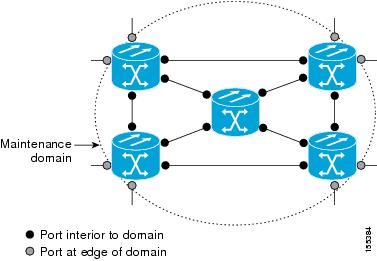
maintenance
domain —The network or part of the network belonging to a single administration for which faults in connectivity are to be managed.
The boundary of a maintenance domain is defined by a set of DSAPs, each of which may become a point of connectivity to a service
instance.
maintenance
domain
name —The unique identifier of a domain that CFM is to protect against accidental concatenation of service instances.
MEP —maintenance endpoint. An actively managed CFM entity associated with a specific DSAP of a service instance, which can generate
and receive CFM frames and track any responses. It is an endpoint of a single MA, and terminates a separate maintenance entity
for each of the other MEPs in the same MA.
MEP
CCDB —A database, maintained by every MEP, that maintains received information about other MEPs in the maintenance domain.
MIP —maintenance intermediate point. A CFM entity, associated with a specific pair of ISS SAPs or EISS Service Access Points,
which reacts and responds to CFM frames. It is associated with a single maintenance association and is an intermediate point
within one or more maintenance entities.
MIP
CCDB —A database of information about the MEPs in the maintenance domain. The MIP CCDB can be maintained by a MIP.
MP —maintenance point. Either a MEP or a MIP.
MPID —maintenance endpoint identifier. A small integer, unique over a given MA, that identifies a specific MEP.
OAM —operations, administration, and maintenance. A term used by several standards bodies to describe protocols and procedures
for operating, administrating, and maintaining networks. Examples are ATM OAM and IEEE Std. 802.3ah OAM.
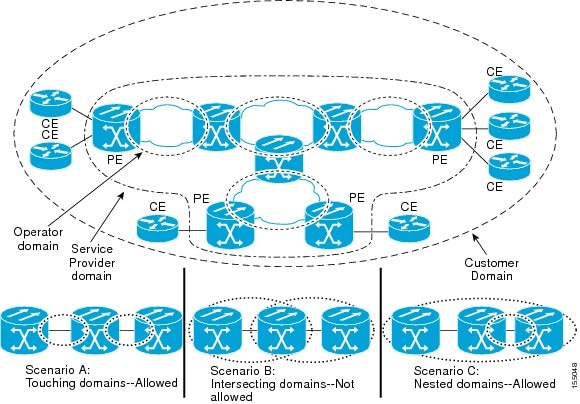
operator —Entity that provides a service provider a single network of provider bridges or a single Layer 2 or Layer 3 backbone network.
An operator may be identical to or a part of the same organization as the service provider. For purposes of IEEE P802.1ag,
Draft Standard for Local and Metropolitan Area Networks, the operator and service provider are presumed to be separate organizations.
Terms such as “customer,” “service provider,” and “operator” reflect common business relationships among organizations and
individuals that use equipment implemented in accordance with IEEE P802.1ag.
UNI —user-network interface. A common term for the connection point between an operator's bridge and customer equipment. A UNI
often includes a C-VLAN-aware bridge component. The term UNI is used broadly in the IEEE P802.1ag standard when the purpose
for various features of CFM are explained. UNI has no normative meaning.

 Feedback
Feedback