- Overview: Secure Connectivity
-
- Implementing and Managing PKI Features Roadmap
- Cisco IOS PKI Overview: Understanding and Planning a PKI
- Deploying RSA Keys Within a PKI
- Configuring Authorization and Revocation of Certificates in a PKI
- Configuring Certificate Enrollment for a PKI
- Configuring and Managing a Cisco IOS Certificate Server for PKI Deployment
- Storing PKI Credentials
- Source Interface Selection for Outgoing Traffic with Certificate Authority (CA)
Cisco IOS Security Configuration Guide: Secure Connectivity, Release 12.2SR
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- June 4, 2010
Chapter: Easy VPN Server
- Finding Feature Information
- Contents
- Restrictions for Easy VPN Server
- Information About Easy VPN Server
- How It Works
- RADIUS Support for Group Profiles
- RADIUS Support for User Profiles
- Supported Protocols
- Functions Supported by Easy VPN Server
- Mode Configuration Version 6 Support
- Xauth Version 6 Support
- IKE DPD
- Split Tunneling Control
- Initial Contact
- Group-Based Policy Control
- User-Based Policy Control
- Session Monitoring for VPN Group Access
- Virtual IPsec Interface Support on a Server
- Virtual Tunnel Interface Per-User Attribute Support
- Banner, Auto-Update, and Browser Proxy
- Configuration Management Enhancements
- Per User AAA Policy Download with PKI
- Per-User Attribute Support for Easy VPN Servers
- Syslog Message Enhancements
- Network Admission Control Support for Easy VPN
- Central Policy Push Firewall Policy Push
- Password Aging
- Split DNS
- cTCP
- VRF Assignment by a AAA Server
- Enabling Policy Lookup via AAA
- Defining Group Policy Information for Mode Configuration Push
- Enabling VPN Session Monitoring
- Verifying a VPN Session
- Applying Mode Configuration and Xauth
- Enabling Reverse Route Injection for the Client
- Enabling IKE Dead Peer Detection
- Configuring RADIUS Server Support
- Verifying Easy VPN Server
- Configuring a Banner
- Configuring Auto Upgrade
- Configuring Browser Proxy
- Configuring the Pushing of a Configuration URL Through a
Mode-Configuration Exchange - Configuring Per User AAA Download with PKI—Configuring the Crypto PKI Trustpoint
- Configuring the Actual Per User AAA Download with PKI
- Configuring Per-User Attributes on a Local Easy VPN AAA Server
- Enabling Easy VPN Syslog Messages
- Defining a CPP Firewall Policy Push Using a Local AAA Server
- Applying a CPP Firewall Policy Push to the Configuration Group
- Defining a CPP Firewall Policy Push Using a Remote AAA Server
- Adding the VSA CPP-Policy Under the Group Definition
- Verifying CPP Firewall Policy Push
- Configuring Password Aging
- Configuring Split DNS
- Verifying Split DNS
- Monitoring and Maintaining Split DNS
- Configuring an Easy VPN Server to Obtain an IP Address from a DHCP Server
- Verifying DHCP Client Proxy
- Monitoring and Maintaining DHCP Client Proxy
- Configuring cTCP
- Verifying cTCP
- Monitoring and Maintaining a cTCP Configuration
- Troubleshooting a cTCP Configuration
- Configuring Cisco IOS for Easy VPN Server: Example
- RADIUS Group Profile with IPsec AV Pairs: Example
- RADIUS User Profile with IPsec AV Pairs: Example
- Backup Gateway with Maximum Logins and Maximum Users: Example
- Easy VPN with an IPsec Virtual Tunnel Interface: Example
- Pushing a Configuration URL Through a Mode-Configuration
Exchange: Examples - Per User AAA Policy Download with PKI: Example
- Per-User Attributes on an Easy VPN Server: Example
- Network Admission Control: Example
- Configuring Password Aging: Example
- Split DNS: Examples
- DHCP Client Proxy: Examples
- cTCP Session: Example
- VRF Assignment by a AAA Server: Example
Easy VPN Server
The Easy VPN Server feature allows a remote end user to communicate using IP Security (IPsec) with any Cisco IOS Virtual Private Network (VPN) gateway. Centrally managed IPsec policies are "pushed" to the client device by the server, minimizing configuration by the end user.
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest feature information and caveats, see the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the "Feature Information for Easy VPN Server" section.
Use Cisco Feature Navigator to find information about platform support and Cisco IOS and Catalyst OS software image support. To access Cisco Feature Navigator, go to http://tools.cisco.com/ITDIT/CFN/jsp/index.jsp. An account on Cisco.com is not required.
Contents
•![]() Restrictions for Easy VPN Server
Restrictions for Easy VPN Server
•![]() Information About Easy VPN Server
Information About Easy VPN Server
•![]() How to Configure Easy VPN Server
How to Configure Easy VPN Server
•![]() Configuration Examples for Easy VPN Server
Configuration Examples for Easy VPN Server
•![]() Feature Information for Easy VPN Server
Feature Information for Easy VPN Server
Restrictions for Easy VPN Server
Nonsupported Protocols
Table 1 outlines IPsec protocol options and attributes that are not supported by Cisco VPN clients, so these options and attributes should not be configured on the router for these clients.
Cisco Secure VPN Client 1.x Restrictions
When used with this feature, the Cisco Secure VPN Client 1.x has the following restrictions:
•![]() It does not support dead peer detection (DPD) or any other keepalive scheme.
It does not support dead peer detection (DPD) or any other keepalive scheme.
•![]() It does not support initial contact.
It does not support initial contact.
This feature cannot use per-group attribute policy profiles such as IP addresses, and Domain Name Service (DNS). Thus, customers must continue to use existing, globally defined parameters for IP address assignment, Windows Internet Naming Service (WINS) and DNS, and preshared keys.
Multicast and Static NAT
Multicast and static NAT are supported only for Easy VPN servers using dynamic virtual tunnel interfaces (DVTIs).
Virtual IPsec Interface Restrictions
The Virtual IPsec Interface Support feature works only with a Cisco software VPN Client that is version 4.x or later, and an Easy VPN remote device that is configured to use a virtual interface.
cTCP Restrictions
•![]() If a port is being used for Cisco Tunnel Control Protocol (cTCP), it cannot be used for other applications.
If a port is being used for Cisco Tunnel Control Protocol (cTCP), it cannot be used for other applications.
•![]() cTCP can be used on only ten ports at a time.
cTCP can be used on only ten ports at a time.
•![]() cTCP is supported on only Cisco IOS Easy VPN servers.
cTCP is supported on only Cisco IOS Easy VPN servers.
•![]() If a cTCP connection is set up on a port, cTCP cannot be disabled on that port because doing so causes the existing connection to stop receiving traffic.
If a cTCP connection is set up on a port, cTCP cannot be disabled on that port because doing so causes the existing connection to stop receiving traffic.
•![]() High Availability of cTCP is not currently supported on the Easy VPN server.
High Availability of cTCP is not currently supported on the Easy VPN server.
Universal Client Mode Using DHCP
•![]() The Easy VPN Server feature does not support universal client mode using DHCP.
The Easy VPN Server feature does not support universal client mode using DHCP.
Information About Easy VPN Server
•![]() RADIUS Support for Group Profiles
RADIUS Support for Group Profiles
•![]() RADIUS Support for User Profiles
RADIUS Support for User Profiles
•![]() Functions Supported by Easy VPN Server
Functions Supported by Easy VPN Server
How It Works
When the client initiates a connection with a Cisco IOS VPN device, the "conversation" that occurs between the peers consists of device authentication via Internet Key Exchange (IKE), followed by user authentication using IKE Extended Authentication (Xauth), VPN policy push (using Mode Configuration), and IPsec security association (SA) creation. An overview of this process is as follows:
•![]() The client initiates IKE Phase 1 via aggressive mode (AM) if a preshared key is to be used for authentication; the client initiates main mode (MM) if digital certificates are used. If the client identifies itself with a preshared key, the accompanying group name entered in the configuration GUI (ID_KEY_ID) is used to identify the group profile associated with this client. If digital certificates are used, the organizational unit (OU) field of a distinguished name (DN) is used to identify the group profile.
The client initiates IKE Phase 1 via aggressive mode (AM) if a preshared key is to be used for authentication; the client initiates main mode (MM) if digital certificates are used. If the client identifies itself with a preshared key, the accompanying group name entered in the configuration GUI (ID_KEY_ID) is used to identify the group profile associated with this client. If digital certificates are used, the organizational unit (OU) field of a distinguished name (DN) is used to identify the group profile.

Note ![]() Because the client may be configured for preshared key authentication, which initiates IKE AM, it is recommended that the administrator change the identity of the Cisco IOS VPN device via the crypto isakmp identity hostname command. This will not affect certificate authentication via IKE MM.
Because the client may be configured for preshared key authentication, which initiates IKE AM, it is recommended that the administrator change the identity of the Cisco IOS VPN device via the crypto isakmp identity hostname command. This will not affect certificate authentication via IKE MM.
•![]() The client attempts to establish an IKE SA between its public IP address and the public IP address of the Cisco IOS VPN device. To reduce the amount of manual configuration on the client, every combination of encryption and hash algorithms, in addition to authentication methods and D-H group sizes, is proposed.
The client attempts to establish an IKE SA between its public IP address and the public IP address of the Cisco IOS VPN device. To reduce the amount of manual configuration on the client, every combination of encryption and hash algorithms, in addition to authentication methods and D-H group sizes, is proposed.
•![]() Depending on its IKE policy configuration, the Cisco IOS VPN device will determine which proposal is acceptable to continue negotiating Phase 1.
Depending on its IKE policy configuration, the Cisco IOS VPN device will determine which proposal is acceptable to continue negotiating Phase 1.

Tip ![]() IKE policy is global for the Cisco IOS VPN device and can consist of several proposals. In the case of multiple proposals, the Cisco IOS VPN device will use the first match, so you should always list your most secure policies first.
IKE policy is global for the Cisco IOS VPN device and can consist of several proposals. In the case of multiple proposals, the Cisco IOS VPN device will use the first match, so you should always list your most secure policies first.

Note ![]() Device authentication ends and user authentication begins at this point.
Device authentication ends and user authentication begins at this point.
•![]() After the IKE SA is successfully established, and if the Cisco IOS VPN device is configured for Xauth, the client waits for a "username/password" challenge and then responds to the challenge of the peer. The information that is entered is checked against authentication entities using authentication, authorization, and accounting (AAA) protocols such as RADIUS and TACACS+. Token cards may also be used via AAA proxy. During Xauth, it is also possible for a user-specific attribute to be retrieved if the credentials of that user are validated via RADIUS.
After the IKE SA is successfully established, and if the Cisco IOS VPN device is configured for Xauth, the client waits for a "username/password" challenge and then responds to the challenge of the peer. The information that is entered is checked against authentication entities using authentication, authorization, and accounting (AAA) protocols such as RADIUS and TACACS+. Token cards may also be used via AAA proxy. During Xauth, it is also possible for a user-specific attribute to be retrieved if the credentials of that user are validated via RADIUS.

Note ![]() VPN devices that are configured to handle remote clients should always be configured to enforce user authentication.
VPN devices that are configured to handle remote clients should always be configured to enforce user authentication.
•![]() If the Cisco IOS VPN device indicates that authentication was successful, the client requests further configuration parameters from the peer. The remaining system parameters (for example, IP address, DNS, and split tunnel attributes) are pushed to the client at this time using Mode Configuration.
If the Cisco IOS VPN device indicates that authentication was successful, the client requests further configuration parameters from the peer. The remaining system parameters (for example, IP address, DNS, and split tunnel attributes) are pushed to the client at this time using Mode Configuration.

Note ![]() The IP address pool and group preshared key (if Rivest, Shamir, and Adelman [RSA] signatures are not being used) are the only required parameter in a group profile, all other parameters are optional.
The IP address pool and group preshared key (if Rivest, Shamir, and Adelman [RSA] signatures are not being used) are the only required parameter in a group profile, all other parameters are optional.
•![]() After each client is assigned an internal IP address via Mode Configuration, it is important that the Cisco IOS VPN device knows how to route packets through the appropriate VPN tunnel. Reverse route injection (RRI) will ensure that a static route is created on the Cisco IOS VPN device for each client internal IP address.
After each client is assigned an internal IP address via Mode Configuration, it is important that the Cisco IOS VPN device knows how to route packets through the appropriate VPN tunnel. Reverse route injection (RRI) will ensure that a static route is created on the Cisco IOS VPN device for each client internal IP address.

Note ![]() It is recommended that you enable RRI on the crypto map (static or dynamic) for the support of VPN clients unless the crypto map is being applied to a Generic Routing Encapsulation (GRE) tunnel that is already being used to distribute routing information.
It is recommended that you enable RRI on the crypto map (static or dynamic) for the support of VPN clients unless the crypto map is being applied to a Generic Routing Encapsulation (GRE) tunnel that is already being used to distribute routing information.
•![]() After the configuration parameters have been successfully received by the client, IKE quick mode is initiated to negotiate IPsec SA establishment.
After the configuration parameters have been successfully received by the client, IKE quick mode is initiated to negotiate IPsec SA establishment.
•![]() After IPsec SAs are created, the connection is complete.
After IPsec SAs are created, the connection is complete.
RADIUS Support for Group Profiles
Group policy information is stored in a profile that can be defined locally in the router configuration or on a RADIUS server that is accessible by the Cisco IOS VPN device. If RADIUS is used, you must configure access to the server and allow the Cisco IOS VPN device to send requests to the server.
To define group policy attributes for RADIUS, you must do the following task on your RADIUS server:
•![]() Define a user that has a name equal to the group name as defined in the client graphical user interface (GUI). For example, if users will be connecting to the Cisco IOS VPN device using the group name "sales," you will need a user whose name is "sales." The password for this user is "cisco," which is a special identifier that is used by the router for RADIUS purposes. The username must then be made a member of a group in which the correct policy is defined. For simplicity, it is recommended that the group name be the same as the username.
Define a user that has a name equal to the group name as defined in the client graphical user interface (GUI). For example, if users will be connecting to the Cisco IOS VPN device using the group name "sales," you will need a user whose name is "sales." The password for this user is "cisco," which is a special identifier that is used by the router for RADIUS purposes. The username must then be made a member of a group in which the correct policy is defined. For simplicity, it is recommended that the group name be the same as the username.
For a Cisco Secure Access Control Server
If you are using a Cisco Secure access control server (ACS), you may configure your remote access VPN group profiles on this server. To perform this task, you must ensure that Internet Engineering Task Force (IETF) RADIUS attributes are selected for group configuration as shown in Figure 1. (This figure also shows the compulsory attributes required for a remote access VPN group.) All values must be entered except the Tunnel-Password attribute, which is actually the preshared key for IKE purposes; if digital certificates are preferred, this attribute may be omitted.
Figure 1 IETF RADIUS Attributes Selection for Group Configuration
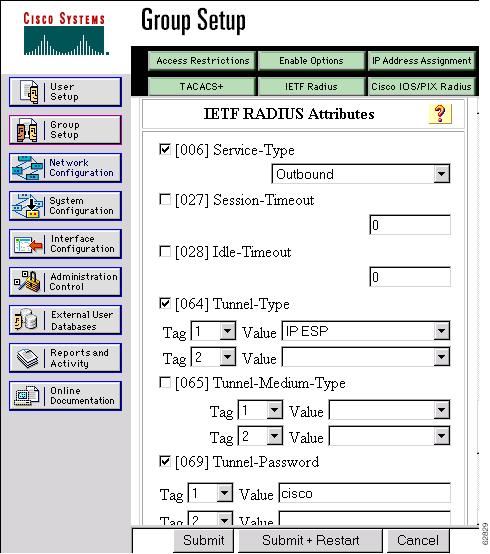
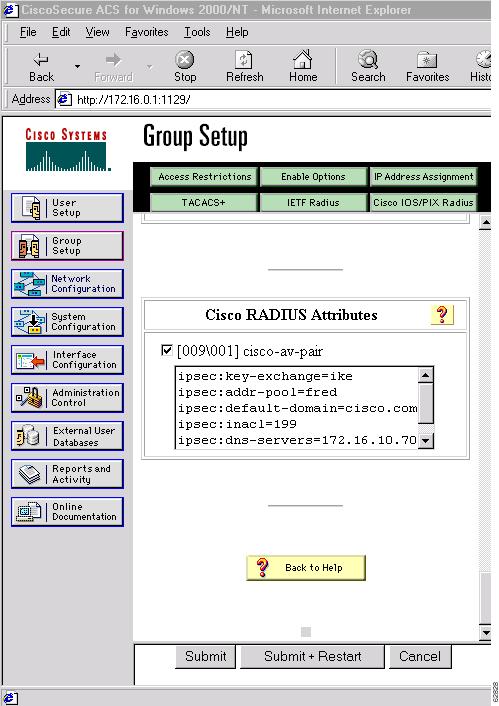
In addition to the compulsory attributes shown in Figure 1, other values can be entered that represent the group policy that is pushed to the remote client via Mode Configuration. Figure 2 shows an example of a group policy. All attributes are optional except the addr-pool, key-exchange=preshared-key, and key-exchange=ike attributes. The values of the attributes are the same as the setting that is used if the policy is defined locally on the router rather than in a RADIUS server. (These values are explained in the "Defining Group Policy Information for Mode Configuration Push" section.)
Figure 2 CiscoSecure ACS Group Policy Setup
After the group profile is created, a user who is a member of the group should be added. (Remember that the username that is defined maps to the group name as defined on the remote client, and the password defined for the username in the RADIUS database must be "cisco.") If digital certificates are the preferred method of IKE authentication, the username should reflect the OU field in the certificate presented by the remote client.
For All Other RADIUS Servers
Ensure that your RADIUS server allows you to define attribute-value (AV) pairs. (For an example, see the "Configuring Cisco IOS for Easy VPN Server: Example" section).

Note ![]() If digital certificates are used, the username defined in RADIUS must be equal to the OU field of the DN of the certificate of the client.
If digital certificates are used, the username defined in RADIUS must be equal to the OU field of the DN of the certificate of the client.
RADIUS Support for User Profiles
Attributes may also be applied on a per-user basis. If you apply attributes on a per-user basis, you can override a group attribute value with an individual user attribute. The attributes are retrieved at the time that user authentication via Xauth occurs. The attributes are then combined with group attributes and applied during Mode Configuration.
User-based attributes are available only if RADIUS is being used for user authentication.
To define user policy attributes for RADIUS, you must do the following task on your RADIUS server:
•![]() Define a user or add attributes to the existing profile of a user in your RADIUS database. The password for the user will be used during Xauth user authentication, or you may proxy to a third-party server, such as a token card server.
Define a user or add attributes to the existing profile of a user in your RADIUS database. The password for the user will be used during Xauth user authentication, or you may proxy to a third-party server, such as a token card server.
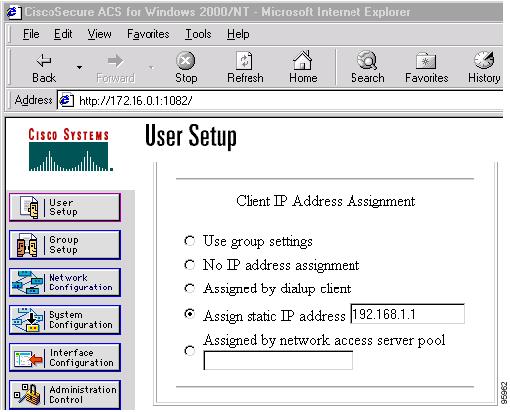
Figure 3 shows how CiscoSecure ACS may be used for user authentication and for the assignment of a Framed-IP-Address attribute that may be pushed to the client. The presence of this attribute means that the local address pool defined for the group to which that user belongs will be overridden.
Figure 3 CiscoSecure ACS User Profile Setup
For All Other RADIUS Servers
Ensure that your RADIUS server allows you to define AV pairs. (For an example, see Configuring Cisco IOS for Easy VPN Server: Example.)
Supported Protocols
Table 2 outlines supported IPsec protocol options and attributes that can be configured for this feature. (See Table 1 for nonsupported options and attributes.)
Functions Supported by Easy VPN Server
•![]() Mode Configuration Version 6 Support
Mode Configuration Version 6 Support
•![]() Session Monitoring for VPN Group Access
Session Monitoring for VPN Group Access
•![]() Virtual IPsec Interface Support on a Server
Virtual IPsec Interface Support on a Server
•![]() Virtual Tunnel Interface Per-User Attribute Support
Virtual Tunnel Interface Per-User Attribute Support
•![]() Banner, Auto-Update, and Browser Proxy
Banner, Auto-Update, and Browser Proxy
•![]() Configuration Management Enhancements
Configuration Management Enhancements
•![]() Per User AAA Policy Download with PKI
Per User AAA Policy Download with PKI
•![]() Per-User Attribute Support for Easy VPN Servers
Per-User Attribute Support for Easy VPN Servers
•![]() Network Admission Control Support for Easy VPN
Network Admission Control Support for Easy VPN
•![]() Central Policy Push Firewall Policy Push
Central Policy Push Firewall Policy Push
•![]() cTCP
cTCP
•![]() VRF Assignment by a AAA Server
VRF Assignment by a AAA Server
Mode Configuration Version 6 Support
Mode Configuration version 6 is now supported for more attributes (as described in an IETF draft submission).
Xauth Version 6 Support
Cisco IOS has been enhanced to support version 6 of Xauth. Xauth for user authentication is based on an IETF draft submission.
IKE DPD
The client implements a new keepalives scheme—IKE DPD.
DPD allows two IPsec peers to determine whether the other is still "alive" during the lifetime of a VPN connection. DPD is useful because a host may reboot, or the dialup link of a remote user may disconnect without notifying the peer that the VPN connection has gone away. When an IPsec host determines that a VPN connection no longer exists, the host can notify a user, attempt to switch to another IPsec host, or clean up valuable resources that were allocated for the peer that no longer exists.
A Cisco IOS VPN device can be configured to send and reply to DPD messages. DPD messages are sent if no other traffic is being passed through the VPN tunnel. If a configured amount of time has lapsed since the last inbound data was received, DPD will send a message ("DPD R-U-THERE") the next time it sends outbound IPsec data to the peer. DPD messages are unidirectional and are automatically sent by Cisco VPN clients. DPD must be configured on the router only if the router wishes to send DPD messages to the VPN client to determine the health of the client.
Split Tunneling Control
Remote clients can support split tunneling, which enables a client to have intranet and Internet access at the same time. If split tunneling is not configured, the client will direct all traffic through the tunnel, even traffic destined for the Internet.
Initial Contact
If a client is suddenly disconnected, the gateway may not be notified. Consequently, removal of connection information (IKE and IPsec SAs) for that client will not immediately occur. Thus, if the client attempts to reconnect to the gateway again, the gateway will refuse the connection because the previous connection information is still valid.
To avoid such a scenario, a new capability called initial contact has been introduced; it is supported by all Cisco VPN products. If a client or router is connecting to another Cisco gateway for the first time, an initial contact message is sent that tells the receiver to ignore and delete any old connection information that has been maintained for that newly connecting peer. Initial contact ensures that connection attempts are not refused because of SA synchronization problems, which are often identified via invalid security parameter index (SPI) messages and which require devices to have their connections cleared.
Group-Based Policy Control
Policy attributes such as IP addresses, DNS, and split tunnel access can be provided on a per-group or per-user basis.
User-Based Policy Control
Attributes may also be applied on a per-user basis. You can override a group attribute value with an individual user attribute. The attributes are retrieved at the time that user authentication via Xauth occurs. They are then combined with group attributes and applied during Mode Configuration.
From Cisco IOS Release 12.3(4)T forward, attributes can be applied on a per-user basis after the user has been authenticated. These attributes can override any similar group attributes. User-based attributes are available only if RADIUS is used as the database.
Framed-IP-Address
To select the Framed-IP-Address attribute for CiscoSecure for NT, do the following: Under the user profile, choose the "use this IP address" option under addressing and manually enter the address. (You should check the method of configuring a framed IP address with your own RADIUS server because this procedure will vary.)

Note ![]() If a framed IP address is present, and there is also a local pool address configured for the group that the user belongs to, the framed IP address will override the local pool setting.
If a framed IP address is present, and there is also a local pool address configured for the group that the user belongs to, the framed IP address will override the local pool setting.
DHCP Client Proxy
Easy VPN servers currently assign an IP address to a remote device using either a local pool that is configured on the router or the framed IP address attribute that is defined in RADIUS. Effective with Cisco IOS Release 12.4(9)T, the DHCP Client Proxy feature provides the option of configuring an Easy VPN server to obtain an IP address from a DHCP server. The IP address is pushed to the remote device using mode configuration.

Note ![]() This feature does not include functionality for the DHCP server to push the DNS, WINS server, or domain name to the remote client.
This feature does not include functionality for the DHCP server to push the DNS, WINS server, or domain name to the remote client.
To configure DHCP Client Proxy, see the "Configuring an Easy VPN Server to Obtain an IP Address from a DHCP Server" section.
Benefits of DHCP Client Proxy
•![]() The functionality provided with this feature helps in the creation of DDNS (dynamic Domain Name System) entries when a DNS server exists in conjunction with the DHCP server.
The functionality provided with this feature helps in the creation of DDNS (dynamic Domain Name System) entries when a DNS server exists in conjunction with the DHCP server.
•![]() The user is not restricted to IP address pools.
The user is not restricted to IP address pools.
User-Save-Password
As per the group description, the User-Save-Password attribute can be received in addition to the group variant (Save-Password), but if it is received, it will override the value asserted by the group.
The following is an output example of a RADIUS AV pair for the User-Save-Password attribute:
ipsec:user-save-password=1
User-Include-Local-LAN
As per the group description, the User-Include-Local-LAN attribute can be received in addition to the group variant (Include-Local-LAN), but if it is received, it will override the value asserted by the group.
The following is an output example of a RADIUS AV pair for the User-Include-Local LAN attribute:
ipsec:user-include-local-lan=1
User-VPN-Group
The User-VPN-Group attribute is a replacement for the Group-Lock attribute. It allows support for both preshared key and RSA signature authentication mechanisms such as certificates.
If you need to check that the group a user is attempting to connect to is indeed the group the user belongs to, use the User-VPN-Group attribute. The administrator sets this attribute to a string, which is the group that the user belongs to. The group the user belongs to is matched against the VPN group as defined by group name (ID_KEY_ID) for preshared keys or by the OU field of a certificate. If the groups do not match, the client connection is terminated.
This feature works only with AAA RADIUS. Local Xauth authentication must still use the Group-Lock attribute.
The following is an output example of a RADIUS AV pair for the Use-VPN-Group attribute:
ipsec:user-vpn-group=cisco
Group-Lock
If you are using preshared keys (no certificates or other RSA signature authentication mechanisms) with RADIUS or local AAA, you can continue to use the Group-Lock attribute. If you are using preshared keys (no certificates or other RSA signature authentication mechanisms) with RADIUS only, you can either continue to use the Group-Lock attribute or you can use the new User-VPN-Group attribute.
How It works
The group lock feature, introduced in Cisco IOS 12.2(13)T, allows you to perform an extra authentication check during Xauth. With this feature enabled, the user must enter a username, group name, and user password during Xauth to authenticate. The username and group name can be entered in any of the following formats: "username/group name," "username\group name," "username%group name," or "username group name." The group name entered during Xauth is compared by the Server with the group name sent for preshared key device authentication. If they do not match, the server denies the connection. To enable this feature, use the group-lock command for the group.
Cisco IOS software does not strip the @group from the Xauth username, so the username user@group must exist in the local or external AAA database pointed to by the ISAKMP profile selected at Phase 1 (machine group authentication).

Session Monitoring for VPN Group Access
It is possible to mimic the functionality provided by some RADIUS servers for limiting the maximum number of connections to a specific server group and also for limiting the number of simultaneous logins for users in that group. After user-defined thresholds are defined in each VPN group, connections will be denied until counts drop below these thresholds.
If you use a RADIUS server, such as CiscoSecure ACS, it is recommended that you enable this session control on the RADIUS server if the functionality is provided. In this way, usage can be controlled across a number of servers by one central repository. When enabling this feature on the router itself, only connections to groups on that specific device are monitored. Load-sharing scenarios are not accurately accounted for.
To configure session monitoring using command-line interface (CLI), use the crypto isakmp client configuration group command and the max-users and max-logins subcommands.
The following is an output example of RADIUS AV pairs that have been added to the relevant group:
ipsec:max-users=1000
ipsec:max-logins=1
Virtual IPsec Interface Support on a Server
Virtual IPsec Interface Support on a Server allows you to selectively send traffic to different Easy VPN concentrators (servers) as well as to the Internet.
Before Cisco IOS Release 12.4(4)T, at the tunnel-up/tunnel-down transition, attributes that were pushed during the mode configuration had to be parsed and applied. When such attributes resulted in the configurations being applied on the interface, the existing configuration had to be overridden.
With the Virtual IPsec Interface Support feature, the tunnel-up configuration can be applied to separate interfaces, making it easier to support separate features at tunnel-up. Features that are applied to the traffic going into the tunnel can be separate from the features that are applied to traffic that is not going through the tunnel (for example, split-tunnel traffic and traffic leaving the device when the tunnel is not up). When the Easy VPN negotiation is successful, the line protocol state of the virtual-access interface gets changed to up. When the Easy VPN tunnel goes down because the SA expires or is deleted, the line protocol state of the virtual-access interfaces changes to down.

Note ![]() This feature does not support multicast.
This feature does not support multicast.
For more information about this feature, see the "Cisco Easy VPN Remote" module in the Cisco IOS Security Configuration Guide: Secure Connectivity. (This feature is configured on the Easy VPN remote device.)
For information about the IPsec Virtual Tunnel Interface feature, see the "IPsec Virtual Tunnel Interface" module in the Cisco IOS Security Configuration Guide: Secure Connectivity.
Virtual Tunnel Interface Per-User Attribute Support
Effective with Cisco IOS Release 12.4(9)T, Virtual Tunnel Interface provides per-user attribute support for Easy VPN servers.
For more information about this feature, see the "IPsec Virtual Tunnel Interface" module in the Cisco IOS Security Configuration Guide: Secure Connectivity.
Banner, Auto-Update, and Browser Proxy
The following features provide support for attributes that aid in the management of the Cisco Easy VPN remote device.
Banner
An Easy VPN server can be configured to push the banner to the Easy VPN remote device. A banner is needed for the web-based activation feature. The banner is displayed when the Easy VPN tunnel is up on the Easy VPN remote console or as a HTML page in the case of web-based activation.
Auto-Update
An Easy VPN server can be configured to provide an automated mechanism for software and firmware upgrades on an Easy VPN remote device.
Browser Proxy
An Easy VPN server can be configured so that an Easy VPN remote device can access resources on the corporate network. Using this feature, the user does not have to manually modify the proxy settings of his or her web browser when connecting to the corporate network using Cisco IOS VPN Client or manually revert the proxy settings upon disconnecting.
Configuration Management Enhancements
Pushing a Configuration URL Through a Mode-Configuration Exchange
When remote devices connect to a corporate gateway for creating an IPsec VPN tunnel, some policy and configuration information has to be applied to the remote device when the VPN tunnel is active to allow the remote device to become a part of the corporate VPN.
The Pushing a Configuration URL Through a Mode-Configuration Exchange feature provides for a mode-configuration attribute that "pushes" a URL from the concentrator (server) to the Cisco IOS Easy VPN remote device. The URL contains the configuration information that the remote device has to download and apply to the running configuration, and it contains the Cisco IOS CLI listing. (For more information about a Cisco IOS CLI listing, see Cisco IOS documentation for the configuration url command.) The CLI for this feature is configured on the concentrator.
The configuration that is pushed to the remote device is persistent by default. That is, the configuration is applied when the IPsec tunnel is "up," but it is not withdrawn when the IPsec tunnel goes "down." However, it is possible to write a section of configuration that is transient in nature, in which case the configuration of the section is reverted when the tunnel is disconnected.
There are no restrictions on where the configuration distribution server is physically located. However, it is recommended that a secure protocol such as HTTPS (Secure HTTP) be used to retrieve the configuration. The configuration server can be located in the corporate network, so because the transfer happens through the IPsec tunnel, insecure access protocols (HTTP) can be used.
Regarding backward compatibility: the remote device asks for the CONFIGURATION-URL and CONFIGURATION-VERSION attributes. Because the CONFIGURATION-URL and CONFIGURATION-VERSION attributes are not mandatory attributes, the server sends them only if it has them configured for the group. There is no built-in restriction to push the configuration, but bootstrap configurations (such as for the IP address) cannot be sent because those configurations are required to set up the Easy VPN tunnel, and the CONFIGURATION-URL comes into effect only after the Easy VPN tunnel comes up.
After the Configuration Has Been Acquired by the Easy VPN Remote Device
After the configuration has been acquired by the Easy VPN remote device, the remote device sends a new ISAKMP notification to the Easy VPN server. The notification contains several manageability information messages about the client (remote device). The Easy VPN server takes two actions when this information is received:
•![]() The Easy VPN server caches the information in its peer database. The information can be displayed by using the show crypto isakmp peer config command. This command output displays all manageability information that is sent by the client (remote device).
The Easy VPN server caches the information in its peer database. The information can be displayed by using the show crypto isakmp peer config command. This command output displays all manageability information that is sent by the client (remote device).
•![]() If accounting is enabled, the Easy VPN server sends an accounting update record that contains the manageability information messages about the remote device to the accounting RADIUS server. This accounting update is later available in the accounting log of the RADIUS server.
If accounting is enabled, the Easy VPN server sends an accounting update record that contains the manageability information messages about the remote device to the accounting RADIUS server. This accounting update is later available in the accounting log of the RADIUS server.
How to Configure This Feature
The commands that are used to configure this feature and the attributes CONFIGURATION-URL and CONFIGURATION-VERSION are described in the crypto isakmp client configuration group command documentation.
Per User AAA Policy Download with PKI
With the Support of Per User AAA Policy Download with PKI feature, user attributes are obtained from the AAA server and pushed to the remote device through mode configuration. The username that is used to get the attributes is retrieved from the remote device certificate.
Per-User Attribute Support for Easy VPN Servers
The Per-User Attribute Support for Easy VPN Servers feature provides users with the ability to support per-user attributes on Easy VPN servers. These attributes are applied on the virtual access interface.
Local Easy VPN AAA Server
For a local Easy VPN AAA server, the per-user attributes can be applied at the group level or at the user level using the command-line interface (CLI).
To configure per-user attributes for a local Easy VPN server, see "Configuring Per-User Attributes on a Local Easy VPN AAA Server" section.
Remote Easy VPN AAA Server
Attribute value (AV) pairs can be defined on a remote Easy VPN AAA server as shown in this example:
cisco-avpair = "ip:outacl#101=permit tcp any any established
Per-User Attributes
The following per-user attributes are currently defined in the AAA server and are applicable to IPsec:
•![]() inacl
inacl
•![]() interface-config
interface-config
•![]() outacl
outacl
•![]() route
route
•![]() rte-fltr-in
rte-fltr-in
•![]() rte-fltr-out
rte-fltr-out
•![]() sub-policy-In
sub-policy-In
•![]() sub-policy-Out
sub-policy-Out
•![]() policy-route
policy-route
•![]() prefix
prefix
Syslog Message Enhancements
Some new syslog messages have been added for Easy VPN in Cisco IOS Release 12.4(4)T. The syslog messages can be enabled on your server by using the command-line interface (CLI). The format of the syslog messages is as follows:
timestamp: %CRYPTO-6-VPN_TUNNEL_STATUS: (Server) <event message> User=<username> Group=<groupname> Client_public_addr=<ip_addr> Server_public_addr=<ip addr>
For an authentication-passed event, the syslog message looks like the following:
Jul 25 23:33:06.847: %CRYPTO-6-VPN_TUNNEL_STATUS: (Server) Authentication PASS ED User=blue Group=Cisco1760group Client_public_addr=10.20.20.1 Server_public_addr=10.20.20.2
Three of the messages (Max users, Max logins, and Group does not exist) are authorization issues and are printed only with the group name in the format. The reason for only the group name being printed is that authorization check happens much before mode configuration happens. Therefore, the peer information is not yet present and cannot be printed. The following is an example of a "Group does not exit" message.
*Jun 30 18:02:58.107: %CRYPTO-6-VPN_TUNNEL_STATUS: Group: group_1 does not exist
Easy VPN Syslog Messages That Are Supported
Both ezvpn_connection_up and ezvpn_connection_down were already supported in a previous release of syslog messages. The enhancements in Cisco IOS Release 12.4(4)T follow the same format, but new syslogs are introduced. The added syslogs are as follows:
•![]() Authentication Passed
Authentication Passed
•![]() Authentication Rejected
Authentication Rejected
–![]() Group Lock Enabled
Group Lock Enabled
–![]() Incorrect Username or Password
Incorrect Username or Password
–![]() Max Users exceeded/Max Logins exceeded
Max Users exceeded/Max Logins exceeded
–![]() No. of Retries exceeded
No. of Retries exceeded
•![]() Authentication Failed (AAA Not Contactable)
Authentication Failed (AAA Not Contactable)
•![]() IP Pool Not present/No Free IP Address available in the pool
IP Pool Not present/No Free IP Address available in the pool
•![]() ACL associated with Ezvpn policy but NOT defined (hence, no split tunneling possible)
ACL associated with Ezvpn policy but NOT defined (hence, no split tunneling possible)
•![]() Save password Turned ON
Save password Turned ON
•![]() Incorrect firewall record being sent by Client (incorrect vendor | product | capability)
Incorrect firewall record being sent by Client (incorrect vendor | product | capability)
•![]() Authentication Rejected
Authentication Rejected
–![]() Access restricted via incoming interface
Access restricted via incoming interface
–![]() Group does not exist
Group does not exist
Network Admission Control Support for Easy VPN
Network Admission Control was introduced in Cisco IOS Release 12.3(8)T as a way to determine whether a PC client should be allowed to connect to the LAN. Network Admission Control uses Extensible Authentication Protocol over UDP (EAPoUDP) to query the Cisco trust agent on the PC and allows a PC to access the network if the client status is healthy. Different policies can be applied on the server to deny or limit access of PCs that are infected.
Effective with Cisco IOS Release 12.4(4)T, Network Admission Control can now be used to monitor the status of remote PC clients as well. After the Easy VPN tunnel comes up and the PC starts to send traffic, the traffic is intercepted at the Easy VPN server, and the posture validation process starts. The posture validation process consists of sending an EAPoUDP request over the Easy VPN tunnel and querying the Cisco trust agent. The authentication server is configured inside the trusted network, behind the IPsec aggregator.
The configuration of an Easy VPN server that has Network Admission Control enabled is shown in the output in Network Admission Control: Example.
Central Policy Push Firewall Policy Push
The Easy VPN server supports Central Policy Push (CPP) Firewall Policy Push. This feature allows administrators to push policies that enforce security to the Cisco Easy VPN (software) Client and related firewall software.
A split tunnel enables access to corporate networks, but it also allows a remote device to be exposed to attacks from the Internet. This feature enables the server to determine whether to allow or deny a tunnel if the remote device does not have a required firewall, thereby reducing exposure to attacks.
The following firewall types are supported:
•![]() Cisco-Integrated-firewall (central-policy-push)
Cisco-Integrated-firewall (central-policy-push)
•![]() Cisco-Security-Agent (check-presence)
Cisco-Security-Agent (check-presence)
•![]() Zonelabs-Zonealarm (both)
Zonelabs-Zonealarm (both)
•![]() Zonelabs-ZonealarmPro (both)
Zonelabs-ZonealarmPro (both)
The server can be used either to check the presence of a firewall on the client (remote device) using the check-presence option or to specify the specifics of the firewall policies that must be applied by the client using the central-policy-push.

Note ![]() The policy check-presence command and keyword, which are used with this feature, replace the firewall are-u-there command functionality that was supported before Cisco IOS Release 12.4(6)T. The firewall are-u-there command will continue to be supported for backward compatibility.
The policy check-presence command and keyword, which are used with this feature, replace the firewall are-u-there command functionality that was supported before Cisco IOS Release 12.4(6)T. The firewall are-u-there command will continue to be supported for backward compatibility.
To enable this feature, see the "Defining a CPP Firewall Policy Push Using a Local AAA Server" section and "Applying a CPP Firewall Policy Push to the Configuration Group" section.
Syslog Support for CPP Firewall Policy Push
Syslog support can be enabled using the crypto logging ezvpn command on your router. CPP syslog messages will be printed for the following error conditions:
•![]() If policy is configured on a group configuration (using the firewall policy command), but a global policy with the same name is not defined (using the crypto isakmp client firewall command). The syslog message is as follows:
If policy is configured on a group configuration (using the firewall policy command), but a global policy with the same name is not defined (using the crypto isakmp client firewall command). The syslog message is as follows:
Policy enabled on group configuration but not defined
Tunnel setup proceeds as normal (with the firewall).
•![]() If an incorrect firewall request (vendor/product/cap incorrect order) is received, the syslog message is as follows:
If an incorrect firewall request (vendor/product/cap incorrect order) is received, the syslog message is as follows:
Incorrect firewall record received from client
•![]() If a policy mismatch occurs between the Cisco VPN Client and the server, the syslog is as follows:
If a policy mismatch occurs between the Cisco VPN Client and the server, the syslog is as follows:
CPP policy mismatch between client and headend
Password Aging
Prior to Cisco IOS Release 12.4(6)T, EasyVPN remote devices (clients) sent username and password values to the Easy VPN server, which in turn sent them to the AAA subsystem. The AAA subsystem generated an authentication request to the RADIUS server. If the password had expired, the RADIUS server replied with an authentication failure. The reason for the failure was not passed back to the AAA subsystem. The user was denied access due to authentication failure, but he or she did not know that the failure was due to password expiration.
Effective with Cisco IOS Release 12.4(6)T, if you have configured the Password Aging feature, the EasyVPN client is notified when a password has expired, and you are prompted to enter a new password. To configure the Password Aging feature, see the section Configuring Password Aging.
For more information about Password Aging, see the reference for "Password Aging" in the section Additional References (subsection "Related Documents).
Split DNS
Effective with Cisco IOS Release 12.4(9)T, split DNS functionality is available on Easy VPN servers. This feature enables the Easy VPN hardware client to use primary and secondary DNS values to resolve DNS queries. These values are pushed by the Easy VPN server to the Easy VPN remote device. To configure this feature on your server, use the split-dns command (see the "Defining Group Policy Information for Mode Configuration Push" section). Configuring this command adds the split-dns attribute to the policy group. The attribute will include the list of domain names that you configured. All other names will be resolved using the public DNS server.
For more information about configuring split DNS, see "Configuring Split and Dynamic DNS on the Cisco VPN 3000" at the following URL: http://www.cisco.com/warp/public/471/dns_split_dynam.pdf.
cTCP
The Cisco Tunneling Control Protocol (cTCP) feature can be used for situations in which an Easy VPN remote device is operating in an environment in which standard IPsec does not function or in which it does not function transparently without modification to existing firewall rules. These situations include the following:
•![]() Small or home office router performing Network Address Translation (NAT) or Port Address Translation (PAT)
Small or home office router performing Network Address Translation (NAT) or Port Address Translation (PAT)
•![]() PAT-provided IP address behind a larger router (for example, in a corporation)
PAT-provided IP address behind a larger router (for example, in a corporation)
•![]() Non-NAT firewall (packet filtering or stateful)
Non-NAT firewall (packet filtering or stateful)
•![]() Proxy server
Proxy server
The firewall should be configured to allow the headend to accept cTCP connections on the configured cTCP port. This configuration is enabled on the Easy VPN server. If the firewall is not configured, it will not allow the cTCP traffic.

Note ![]() cTCP traffic is actually Transmission Control Protocol (TCP) traffic. cTCP packets are IKE or Encapsulating Security Payload (ESP) packets that are being transmitted over TCP.
cTCP traffic is actually Transmission Control Protocol (TCP) traffic. cTCP packets are IKE or Encapsulating Security Payload (ESP) packets that are being transmitted over TCP.
The cTCP server sends a gratuitous ACK message to the client whenever the data received from the client over the cTCP session established reaches 3 kilobytes (KB). A similar procedure is followed by the client. By default, this gratuitous ACK message is sent to keep the NAT or firewall sessions between the cTCP server and cTCP client alive. The data size at which gratuitous ACK messages are sent is not configurable.
Keepalives that are sent by a client or server do not keep the sessions alive when the server or client sends data at a high speed.
The cTCP server sending ACK message ensures that NAT or firewall sessions do not drop packets when there is one-way traffic and the data is large. It also ensures that an acknowledgement is provided from the device receiving the data.
VRF Assignment by a AAA Server
To assign VRF to Easy VPN users, the following attributes should be enabled on a AAA server:
Cisco-avpair "ip:interface-config=ip vrf forwarding example1"
Cisco-avpair "ip:interface-config=ip unnumbered loopback10"
How to Configure Easy VPN Server
This section includes the following procedures:
•![]() Enabling Policy Lookup via AAA (required)
Enabling Policy Lookup via AAA (required)
•![]() Defining Group Policy Information for Mode Configuration Push (required)
Defining Group Policy Information for Mode Configuration Push (required)
•![]() Enabling VPN Session Monitoring (optional)
Enabling VPN Session Monitoring (optional)
•![]() Verifying a VPN Session (optional)
Verifying a VPN Session (optional)
•![]() Applying Mode Configuration and Xauth (required)
Applying Mode Configuration and Xauth (required)
•![]() Enabling Reverse Route Injection for the Client (optional)
Enabling Reverse Route Injection for the Client (optional)
•![]() Enabling IKE Dead Peer Detection (optional)
Enabling IKE Dead Peer Detection (optional)
•![]() Configuring RADIUS Server Support (optional)
Configuring RADIUS Server Support (optional)
•![]() Verifying Easy VPN Server (optional)
Verifying Easy VPN Server (optional)
•![]() Configuring a Banner (optional)
Configuring a Banner (optional)
•![]() Configuring Auto Upgrade (optional)
Configuring Auto Upgrade (optional)
•![]() Configuring Browser Proxy (optional)
Configuring Browser Proxy (optional)
•![]() Configuring the Pushing of a Configuration URL Through a Mode-Configuration Exchange (optional)
Configuring the Pushing of a Configuration URL Through a Mode-Configuration Exchange (optional)
•![]() Configuring Per User AAA Download with PKI—Configuring the Crypto PKI Trustpoint (optional)
Configuring Per User AAA Download with PKI—Configuring the Crypto PKI Trustpoint (optional)
•![]() Configuring the Actual Per User AAA Download with PKI (optional)
Configuring the Actual Per User AAA Download with PKI (optional)
•![]() Configuring Per-User Attributes on a Local Easy VPN AAA Server
Configuring Per-User Attributes on a Local Easy VPN AAA Server
•![]() Configuring Per-User Attributes on a Local Easy VPN AAA Server (optional)
Configuring Per-User Attributes on a Local Easy VPN AAA Server (optional)
•![]() Defining a CPP Firewall Policy Push Using a Local AAA Server (optional)
Defining a CPP Firewall Policy Push Using a Local AAA Server (optional)
•![]() Applying a CPP Firewall Policy Push to the Configuration Group (optional)
Applying a CPP Firewall Policy Push to the Configuration Group (optional)
•![]() Defining a CPP Firewall Policy Push Using a Remote AAA Server (optional)
Defining a CPP Firewall Policy Push Using a Remote AAA Server (optional)
•![]() Adding the VSA CPP-Policy Under the Group Definition (optional)
Adding the VSA CPP-Policy Under the Group Definition (optional)
•![]() Verifying CPP Firewall Policy Push (optional)
Verifying CPP Firewall Policy Push (optional)
•![]() Configuring Password Aging (optional)
Configuring Password Aging (optional)
•![]() Configuring Split DNS (optional)
Configuring Split DNS (optional)
•![]() Verifying Split DNS (optional)
Verifying Split DNS (optional)
•![]() Monitoring and Maintaining Split DNS (optional)
Monitoring and Maintaining Split DNS (optional)
•![]() Configuring an Easy VPN Server to Obtain an IP Address from a DHCP Server (optional)
Configuring an Easy VPN Server to Obtain an IP Address from a DHCP Server (optional)
•![]() Verifying DHCP Client Proxy (optional)
Verifying DHCP Client Proxy (optional)
•![]() Monitoring and Maintaining DHCP Client Proxy (optional)
Monitoring and Maintaining DHCP Client Proxy (optional)
•![]() Configuring cTCP (optional)
Configuring cTCP (optional)
•![]() Verifying cTCP (optional)
Verifying cTCP (optional)
•![]() Monitoring and Maintaining a cTCP Configuration (optional)
Monitoring and Maintaining a cTCP Configuration (optional)
•![]() Troubleshooting a cTCP Configuration (optional)
Troubleshooting a cTCP Configuration (optional)
Enabling Policy Lookup via AAA
To enable policy lookup via AAA, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() aaa new-model
aaa new-model
4. ![]() aaa authentication password-prompt text-string
aaa authentication password-prompt text-string
5. ![]() aaa authentication username prompt text-string
aaa authentication username prompt text-string
6. ![]() aaa authentication login [list-name method1] [method2...]
aaa authentication login [list-name method1] [method2...]
7. ![]() aaa authorization network list-name local group radius
aaa authorization network list-name local group radius
8. ![]() username name password encryption-type encrypted-password
username name password encryption-type encrypted-password
DETAILED STEPS
Defining Group Policy Information for Mode Configuration Push
Although users can belong to only one group per connection, they may belong to specific groups with different policy requirements. Thus, users may decide to connect to the client using a different group ID by changing their client profile on the VPN device. To define the policy attributes that are pushed to the client via Mode Configuration, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto isakmp client configuration group {group-name | default}
crypto isakmp client configuration group {group-name | default}
4. ![]() key name
key name
5. ![]() dns primary-server secondary-server
dns primary-server secondary-server
6. ![]() wins primary-server secondary-server
wins primary-server secondary-server
7. ![]() domain name
domain name
8. ![]() pool name
pool name
9. ![]() netmask name
netmask name
10. ![]() acl number
acl number
11. ![]() access-restrict {interface-name}
access-restrict {interface-name}
12. ![]() policy check-presence
policy check-presence
or
firewall are-u-there
13. ![]() group-lock
group-lock
14. ![]() include-local-lan
include-local-lan
15. ![]() save-password
save-password
16. ![]() backup-gateway
backup-gateway
17. ![]() pfs
pfs
DETAILED STEPS
Enabling VPN Session Monitoring
If you wish to set restrictions on the maximum number of connections to the router per VPN group and the maximum number of simultaneous logins per user, add the following attributes to the VPN group.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto isakmp client configuration group group-name
crypto isakmp client configuration group group-name
4. ![]() exit
exit
5. ![]() max-logins number-of-logins
max-logins number-of-logins
6. ![]() max-users number-of-users
max-users number-of-users
DETAILED STEPS
Verifying a VPN Session
To verify a VPN session, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() show crypto session group
show crypto session group
3. ![]() show crypto session summary
show crypto session summary
DETAILED STEPS
Applying Mode Configuration and Xauth
Mode Configuration and Xauth must be applied to a crypto map to be enforced. To apply Mode Configuration and Xauth to a crypto map, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto map tag client configuration address [initiate | respond]
crypto map tag client configuration address [initiate | respond]
4. ![]() crypto map map-name isakmp authorization list list-name
crypto map map-name isakmp authorization list list-name
5. ![]() crypto map map-name client authentication list list-name
crypto map map-name client authentication list list-name
DETAILED STEPS
Enabling Reverse Route Injection for the Client
To enable RRI on the crypto map (static or dynamic) for VPN client support, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto dynamic map-name seq-num
crypto dynamic map-name seq-num
or
crypto map map-name seq-num ipsec-isakmp
4. ![]() set peer ip-address
set peer ip-address
5. ![]() set transform-set transform-set-name
set transform-set transform-set-name
6. ![]() reverse-route
reverse-route
7. ![]() match-address
match-address
DETAILED STEPS
Enabling IKE Dead Peer Detection
To enable a Cisco IOS VPN gateway (instead of the client) to send IKE DPD messages, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto isakmp keepalive secs retries
crypto isakmp keepalive secs retries
DETAILED STEPS
Configuring RADIUS Server Support
To configure access to the server and allow the Cisco IOS VPN device to send requests to the server, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() radius server host ip-address [auth-port port-number] [acct-port port-number] [key string]
radius server host ip-address [auth-port port-number] [acct-port port-number] [key string]
DETAILED STEPS
Verifying Easy VPN Server
To verify your configurations for this feature, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() show crypto map [interface interface | tag map-name]
show crypto map [interface interface | tag map-name]
DETAILED STEPS
Configuring a Banner
To configure an Easy VPN server to push a banner to an Easy VPN remote device, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto isakmp client configuration group {group-name}
crypto isakmp client configuration group {group-name}
4. ![]() banner c {banner-text} c
banner c {banner-text} c
DETAILED STEPS
Configuring Auto Upgrade
To configure an Easy VPN server to provide an automated mechanism to make software and firmware upgrades automatically available to an Easy VPN remote device, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto isakmp client configuration group {group-name}
crypto isakmp client configuration group {group-name}
4. ![]() auto-update client {type-of-system} {url url} {rev review-version}
auto-update client {type-of-system} {url url} {rev review-version}
DETAILED STEPS
Configuring Browser Proxy
To configure an EasyVPN server so that the Easy VPN remote device can access resources on the corporate network when using Cisco IOS VPN Client software, perform the following steps. With this configuration, the user does not have to manually modify the proxy settings of his or her web browser when connecting and does not have to manually revert the proxy settings when disconnecting.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto isakmp client configuration browser-proxy {browser-proxy-name}
crypto isakmp client configuration browser-proxy {browser-proxy-name}
4. ![]() proxy {proxy-parameter}
proxy {proxy-parameter}
DETAILED STEPS
Configuring the Pushing of a Configuration URL Through a
Mode-Configuration Exchange
To configure an Easy VPN server to push a configuration URL through a Mode-Configuration Exchange, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto isakmp client configuration group {group-name}
crypto isakmp client configuration group {group-name}
4. ![]() configuration url {url}
configuration url {url}
5. ![]() configuration version {version-number}
configuration version {version-number}
DETAILED STEPS
Configuring Per User AAA Download with PKI—Configuring the Crypto PKI Trustpoint
To configure a AAA server to push user attributes to a remote device, perform the following steps.
Prerequisites
Before configuring a AAA server to push user attributes to a remote device, you must have configured AAA. The crypto PKI trustpoint must also be configured (see the first configuration task below). It is preferable that the trustpoint configuration contain the authorization username command.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto pki trustpoint name
crypto pki trustpoint name
4. ![]() enrollment url url
enrollment url url
5. ![]() revocation-check none
revocation-check none
6. ![]() rsakeypair key-label
rsakeypair key-label
7. ![]() authorization username {subjectname subjectname}
authorization username {subjectname subjectname}
8. ![]() exit
exit
DETAILED STEPS
Configuring the Actual Per User AAA Download with PKI
To configure the actual per-user download with PKI, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto isakmp policy priority
crypto isakmp policy priority
4. ![]() group {1 | 2}
group {1 | 2}
5. ![]() exit
exit
6. ![]() crypto isakmp profile profile-name
crypto isakmp profile profile-name
7. ![]() match certificate certificate-map
match certificate certificate-map
8. ![]() client pki authorization list listname
client pki authorization list listname
9. ![]() client configuration address {initiate | respond}
client configuration address {initiate | respond}
10. ![]() virtual-template template-number
virtual-template template-number
11. ![]() exit
exit
12. ![]() crypto ipsec transform-set [transform-set-name transform1] [transform2] [transform3] [transform4]
crypto ipsec transform-set [transform-set-name transform1] [transform2] [transform3] [transform4]
13. ![]() crypto ipsec profile name
crypto ipsec profile name
14. ![]() set transform-set transform-set-name
set transform-set transform-set-name
DETAILED STEPS
Configuring Per-User Attributes on a Local Easy VPN AAA Server
To configure per-user attributes on a local Easy VPN AAA server, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() aaa attribute list list-name
aaa attribute list list-name
4. ![]() attribute type name value [service service] [protocol protocol]
attribute type name value [service service] [protocol protocol]
5. ![]() exit
exit
6. ![]() crypto isakmp client configuration group group-name
crypto isakmp client configuration group group-name
7. ![]() crypto aaa attribute list list-name
crypto aaa attribute list list-name
DETAILED STEPS
Enabling Easy VPN Syslog Messages
To enable Easy VPN syslog messages on a server, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto logging ezvpn group group-name
crypto logging ezvpn group group-name
DETAILED STEPS
Defining a CPP Firewall Policy Push Using a Local AAA Server
To define a CPP firewall policy push on a server to allow or deny a tunnel on the basis of whether a remote device has a required firewall for a local AAA server, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto isakmp client firewall {policy-name} {required | optional} {firewall-type}
crypto isakmp client firewall {policy-name} {required | optional} {firewall-type}
4. ![]() policy {check-presence | central-policy-push {access-list {in | out} access-list-name | access-list-number}}
policy {check-presence | central-policy-push {access-list {in | out} access-list-name | access-list-number}}
DETAILED STEPS
What to Do Next
Apply the CPP firewall policy push to the configured group.
Applying a CPP Firewall Policy Push to the Configuration Group
Now that the CPP firewall policy push has been defined, it must be applied to the configuration group by performing the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto isakmp client configuration group group-name
crypto isakmp client configuration group group-name
4. ![]() firewall policy policy-name
firewall policy policy-name
DETAILED STEPS
Defining a CPP Firewall Policy Push Using a Remote AAA Server
To define a CPP firewall policy push using a remote AAA server, see the section "Defining a CPP Firewall Policy Push Using a Local AAA Server." The steps are the same for this configuration.
What to Do Next
After defining the CPP firewall policy push, you should add the VSA cpp-policy under the group definition.
Adding the VSA CPP-Policy Under the Group Definition
To add the the VSA cpp-policy under the group definition that is defined in RADIUS, perform the following step.
SUMMARY STEPS
1. ![]() Add the VSA cpp-policy under the group definition that is defined in RADIUS.
Add the VSA cpp-policy under the group definition that is defined in RADIUS.
DETAILED STEPS
Verifying CPP Firewall Policy Push
To verify the CPP firewall push policy on a local or remote AAA server, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() debug crypto isakmp
debug crypto isakmp
DETAILED STEPS
Configuring Password Aging
To configure Password Aging so that the Easy VPN client is notified if the password has expired, perform the following steps.
Restrictions
The following restrictions apply to the Password Aging feature:
•![]() It works only with VPN software clients. It does not work with VPN client hardware.
It works only with VPN software clients. It does not work with VPN client hardware.
•![]() It works only with RADIUS servers.
It works only with RADIUS servers.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() aaa new-model
aaa new-model
4. ![]() aaa authentication login {list-name} password-expiry method1 [method2...]
aaa authentication login {list-name} password-expiry method1 [method2...]
5. ![]() radius-server host {ip-address} auth-port port-number acct-port port-number key string}
radius-server host {ip-address} auth-port port-number acct-port port-number key string}
6. ![]() Configure the ISAKMP profile
Configure the ISAKMP profile
7. ![]() client authentication list {list-name}
client authentication list {list-name}
DETAILED STEPS
|
|
|
|
|---|---|---|
Step 1 |
enable Router> enable |
Enables privileged EXEC mode. • |
Step 2 |
configure terminal Router# configure terminal |
Enters global configuration mode. |
Step 3 |
aaa new-model Router(config)# aaa new-model |
Enables AAA. |
Step 4 |
aaa authentication login {list-name}
password-expiry method1 [method2...]
Router(config)# aaa authentication login userauth paswd-expiry group radius |
Configures the authentication list so that the Password Aging feature is enabled. |
Step 5 |
radius-server host {ip-address} auth-port
port-number acct-port port-number key string
Router(config)# radius-server host 172.19.217.96 255.255.255.0 auth-port 1645 acct-port 1646 key cisco radius-server vsa send authentication |
Configures the RADIUS server. |
Step 6 |
Configure the ISAKMP profile. see the section "Configuring Password Aging: Example" |
Configures the ISAKMP profile and enters ISAKMP profile configuration mode (see the section "Configuring Password Aging: Example"). |
Step 7 |
client authentication list {list-name}
Router(config-isakmp-profile)# client authentication list userauth |
Configures IKE extended authentication (Xauth) in an ISAKMP profile and includes the authentication list that was defined above. |
Configuring Split DNS
To configure Split DNS, perform the following steps.
Prerequisites
Before the Split DNS feature can work, the following commands should have been configured on the Easy VPN remote:
•![]() ip dns server
ip dns server
•![]() ip domain-lookup
ip domain-lookup
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto isakmp client configuration group group-name
crypto isakmp client configuration group group-name
4. ![]() dns primary-server secondary-server
dns primary-server secondary-server
5. ![]() split-dns domain-name
split-dns domain-name
DETAILED STEPS
Verifying Split DNS
To verify a split DNS configuration, perform the following steps (the show commands can be used one at a time or together).
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() show ip dns name-list [name-list-number]
show ip dns name-list [name-list-number]
3. ![]() show ip dns view [vrf vrf-name] [default | view-name]
show ip dns view [vrf vrf-name] [default | view-name]
4. ![]() show ip dns view-list [view-list-name]
show ip dns view-list [view-list-name]
DETAILED STEPS
Monitoring and Maintaining Split DNS
To monitor and maintain the split DNS configuration on Easy VPN remote devices, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() debug ip dns name-list
debug ip dns name-list
3. ![]() debug ip dns view
debug ip dns view
4. ![]() debug ip dns view-list
debug ip dns view-list
DETAILED STEPS
Configuring an Easy VPN Server to Obtain an IP Address from a DHCP Server
When the Easy VPN server selects the method for address assignment, it does so in the following order of precedence:
1. ![]() Selects the Framed IP address
Selects the Framed IP address
2. ![]() Uses the IP address from the authentication server (group/user)
Uses the IP address from the authentication server (group/user)
3. ![]() Uses the global IKE address pools
Uses the global IKE address pools
4. ![]() Uses DHCP
Uses DHCP

Note ![]() To enable the Easy VPN server to obtain an IP address from a DHCP server, remove other address assignments.
To enable the Easy VPN server to obtain an IP address from a DHCP server, remove other address assignments.
To configure an Easy VPN server to obtain an IP address from a DHCP server, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto isakmp client configuration group group-name
crypto isakmp client configuration group group-name
4. ![]() dhcp server {ip-address | hostname}
dhcp server {ip-address | hostname}
5. ![]() dhcp timeout time
dhcp timeout time
6. ![]() dhcp giaddr scope
dhcp giaddr scope
DETAILED STEPS
Verifying DHCP Client Proxy
To verify your DHCP client proxy configuration, perform the following steps (use the show commands one at a time or together).
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() show dhcp lease
show dhcp lease
3. ![]() show ip dhcp pool
show ip dhcp pool
4. ![]() show ip dhcp binding
show ip dhcp binding
DETAILED STEPS
Monitoring and Maintaining DHCP Client Proxy
To monitor and maintain your DHCP client proxy configuration, perform the following steps (use the debug commands one at a time or together).
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() debug crypto isakmp
debug crypto isakmp
3. ![]() debug dhcp
debug dhcp
4. ![]() debug dhcp detail
debug dhcp detail
5. ![]() debug ip dhcp server events
debug ip dhcp server events
DETAILED STEPS
Configuring cTCP
To enable cTCP, perform the following steps on your Easy VPN server.
Prerequisites
Before configuring cTCP, you should have configured crypto IPsec.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() crypto ctcp port [port-number]
crypto ctcp port [port-number]
DETAILED STEPS
Verifying cTCP
To verify your cTCP configuration, perform the following steps (the show commands can be used one at a time or together).
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() show crypto ctcp [peer ip-address]
show crypto ctcp [peer ip-address]
DETAILED STEPS
Monitoring and Maintaining a cTCP Configuration
To monitor and maintain your cTCP configuration, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() debug crypto ctcp
debug crypto ctcp
DETAILED STEPS
Clearing a cTCP Configuration
To clear a cTCP configuration, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() clear crypto ctcp [peer ip-address]
clear crypto ctcp [peer ip-address]
DETAILED STEPS
Troubleshooting a cTCP Configuration
To troubleshoot a cTCP configuration, perform the following steps.
SUMMARY STEPS
1. ![]() Ensure that the cTCP session is in the CTCP_ACK_RECEIVED state.
Ensure that the cTCP session is in the CTCP_ACK_RECEIVED state.
2. ![]() If the cTCP session is not in the CTCP_ACK_RECEIVED state, enable the debug crypto ctcp command.
If the cTCP session is not in the CTCP_ACK_RECEIVED state, enable the debug crypto ctcp command.
3. ![]() If no cTCP bugs are seen, ensure that the firewall is allowing the cTCP packets to get to the server.
If no cTCP bugs are seen, ensure that the firewall is allowing the cTCP packets to get to the server.
4. ![]() If the firewall configuration is correct, debugging is enabled, and you do not see any cTCP debugs on your console, you must find out why the cTCP port on the router is not receiving packets.
If the firewall configuration is correct, debugging is enabled, and you do not see any cTCP debugs on your console, you must find out why the cTCP port on the router is not receiving packets.
DETAILED STEPS
Step 1 ![]() To ensure that the cTCP session is in the CTCP_ACK_RECEIVED state, use the show crypto ctcp command.
To ensure that the cTCP session is in the CTCP_ACK_RECEIVED state, use the show crypto ctcp command.
Step 2 ![]() If the cTCP session is not in the CTCP_ACK_RECEIVED state, enable the debug crypto ctcp command and then try using the show crypto ctcp command again.
If the cTCP session is not in the CTCP_ACK_RECEIVED state, enable the debug crypto ctcp command and then try using the show crypto ctcp command again.
Step 3 ![]() If no cTCP bugs are seen, ensure that the firewall is allowing the cTCP packets to get to the server (check the firewall configuration).
If no cTCP bugs are seen, ensure that the firewall is allowing the cTCP packets to get to the server (check the firewall configuration).
Step 4 ![]() If the firewall configuration is correct, debugging is enabled, and you do not see any cTCP debugs on your console, you must find out why the cTCP port on the router is not receiving packets. If you do not see any cTCP debugs and a cTCP session has not been set up, there is a possibility that cTCP packets that are actually TCP packets could have been delivered to a TCP stack instead of to the cTCP port. By enabling the debug ip packet and debug ip tcp packet commands, you may be able to determine whether the packet is being given to the TCP stack.
If the firewall configuration is correct, debugging is enabled, and you do not see any cTCP debugs on your console, you must find out why the cTCP port on the router is not receiving packets. If you do not see any cTCP debugs and a cTCP session has not been set up, there is a possibility that cTCP packets that are actually TCP packets could have been delivered to a TCP stack instead of to the cTCP port. By enabling the debug ip packet and debug ip tcp packet commands, you may be able to determine whether the packet is being given to the TCP stack.
Configuration Examples for Easy VPN Server
This section provides the following configuration examples:
•![]() Configuring Cisco IOS for Easy VPN Server: Example
Configuring Cisco IOS for Easy VPN Server: Example
•![]() RADIUS Group Profile with IPsec AV Pairs: Example
RADIUS Group Profile with IPsec AV Pairs: Example
•![]() RADIUS User Profile with IPsec AV Pairs: Example
RADIUS User Profile with IPsec AV Pairs: Example
•![]() Backup Gateway with Maximum Logins and Maximum Users: Example
Backup Gateway with Maximum Logins and Maximum Users: Example
•![]() Easy VPN with an IPsec Virtual Tunnel Interface: Example
Easy VPN with an IPsec Virtual Tunnel Interface: Example
•![]() Pushing a Configuration URL Through a Mode-Configuration Exchange: Examples
Pushing a Configuration URL Through a Mode-Configuration Exchange: Examples
•![]() Per User AAA Policy Download with PKI: Example
Per User AAA Policy Download with PKI: Example
•![]() Per-User Attributes on an Easy VPN Server: Example
Per-User Attributes on an Easy VPN Server: Example
•![]() Network Admission Control: Example
Network Admission Control: Example
•![]() Configuring Password Aging: Example
Configuring Password Aging: Example
•![]() VRF Assignment by a AAA Server: Example
VRF Assignment by a AAA Server: Example
Configuring Cisco IOS for Easy VPN Server: Example
The following example shows how to define group policy information locally for mode configuration. In this example, a group name is named "cisco" and another group name is named "default." The policy is enforced for all users who do not offer a group name that matches "cisco."
! Enable policy look-up via AAA. For authentication and authorization, send requests to
! RADIUS first, then try local policy.
aaa new-model
aaa authentication login userlist group radius local
aaa authorization network grouplist group radius local
enable password XXXX
!
username cisco password 0 cisco
clock timezone PST -8
ip subnet-zero
! Configure IKE policies, which are assessed in order so that the first policy that
matches the proposal of the client will be used.
crypto isakmp policy 1
group 2
!
crypto isakmp policy 3
hash md5
authentication pre-share
group 2
crypto isakmp identity hostname
!
! Define "cisco" group policy information for mode config push.
crypto isakmp client configuration group cisco
key cisco
dns 10.2.2.2 10.2.2.3
wins 10.6.6.6
domain cisco.com
pool green
acl 199
! Define default group policy for mode config push.
crypto isakmp client configuration group default
key cisco
dns 10.2.2.2 10.3.2.3
pool green
acl 199
!
!
crypto ipsec transform-set dessha esp-des esp-sha-hmac
!
crypto dynamic-map mode 1
set transform-set dessha
!
! Apply mode config and xauth to crypto map "mode." The list names that are defined here
! must match the list names that are defined in the AAA section of the config.
crypto map mode client authentication list userlist
crypto map mode isakmp authorization list grouplist
crypto map mode client configuration address respond
crypto map mode 1 ipsec-isakmp dynamic mode
!
!
controller ISA 1/1
!
!
interface FastEthernet0/0
ip address 10.6.1.8 255.255.0.0
ip route-cache
ip mroute-cache
duplex auto
speed auto
crypto map mode
!
interface FastEthernet0/1
ip address 192.168.1.28 255.255.255.0
no ip route-cache
no ip mroute-cache
duplex auto
speed auto
! Specify IP address pools for internal IP address allocation to clients.
ip local pool green 192.168.2.1 192.168.2.10
ip classless
ip route 0.0.0.0 0.0.0.0 10.6.0.1
!
! Define access lists for each subnet that should be protected.
access-list 199 permit ip 192.168.1.0 0.0.0.255 any
access-list 199 permit ip 192.168.3.0 0.0.0.255 any
!
! Specify a RADIUS server host and configure access to the server.
radius-server host 192.168.1.1 auth-port 1645 acct-port 1646 key XXXXX
radius-server retransmit 3
!
!
line con 0
exec-timeout 0 0
length 25
transport input none
line aux 0
line vty 5 15
!
RADIUS Group Profile with IPsec AV Pairs: Example
The following is an example of a standard RADIUS group profile that includes RADIUS IPsec AV pairs. To get the group authorization attributes, "cisco" must be used as the password.
client_r Password = "cisco"
Service-Type = Outbound
cisco-avpair = "ipsec:tunnel-type*ESP"
cisco-avpair = "ipsec:key-exchange=ike"
cisco-avpair = "ipsec:tunnel-password=lab"
cisco-avpair = "ipsec:addr-pool=pool1"
cisco-avpair = "ipsec:default-domain=cisco"
cisco-avpair = "ipsec:inacl=101"
cisco-avpair = "ipsec:access-restrict=fastethernet 0/0"
cisco-avpair = "ipsec:group-lock=1"
cisco-avpair = "ipsec:dns-servers=10.1.1.1 10.2.2.2"
cisco-avpair = "ipsec:firewall=1"
cisco-avpair = "ipsec:include-local-lan=1"
cisco-avpair = "ipsec:save-password=1"
cisco-avpair = "ipsec:wins-servers=10.3.3.3 10.4.4.4"
cisco-avpair = "ipsec:split-dns=green.com"
cisco-avpair = "ipsec:ipsec-backup-gateway=10.1.1.1"
cisco-avpair = "ipsec:ipsec-backup-gateway=10.1.1.2"
cisco-avpair = "ipsec:pfs=1"
cisco-avpair = "ipsec:cpp-policy="Enterprise Firewall"
cisco-avpair = "ipsec:auto-update="Win http://www.example.com 4.0.1"
cisco-avpair = "ipsec:browser-proxy=bproxy_profile_A"
cisco-avpair = "ipsec:banner=Xauth banner text here"
The following is an example of a RADIUS user profile that is set up for group that has group-lock configured. The user name is entered in the same format as the user@domain format.
abc@example.com Password = "abcll1111"
cisco-avpair = "ipsec:user-include-local-lan=1"
cisco-avpair = "ipsec:user-save-password=1"
Framed-IP-Address = 10.10.10.10
RADIUS User Profile with IPsec AV Pairs: Example
The following is an example of a standard RADIUS user profile that includes RADIUS IPsec AV pairs. These user attributes will be obtained during Xauth.
ualluall Password = "uall1234"
cisco-avpair = "ipsec:user-vpn-group=unity"
cisco-avpair = "ipsec:user-include-local-lan=1"
cisco-avpair = "ipsec:user-save-password=1"
Framed-IP-Address = 10.10.10.10
Backup Gateway with Maximum Logins and Maximum Users: Example
The following example shows that five backup gateways have been configured, that the maximum users have been set to 250, and that maximum logins have been set to 2:
crypto isakmp client configuration group sdm
key 6 RMZPPMRQMSdiZNJg`EBbCWTKSTi\d[
pool POOL1
acl 150
backup-gateway 172.16.12.12
backup-gateway 172.16.12.13
backup-gateway 172.16.12.14
backup-gateway 172.16.12.130
backup-gateway 172.16.12.131
max-users 250
max-logins 2
Easy VPN with an IPsec Virtual Tunnel Interface: Example
The following output shows that Easy VPN has been configured with an IPsec virtual tunnel interface.
!
version 12.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname Router
!
boot-start-marker
boot-end-marker
!
!
aaa new-model
!
!
aaa authentication login default local
aaa authorization network default local
!
aaa session-id common
!
resource policy
!
clock timezone IST 0
ip subnet-zero
ip cef
no ip domain lookup
no ip dhcp use vrf connected
!
username lab password 0 lab
!
crypto isakmp policy 3
authentication pre-share
group 2
crypto isakmp xauth timeout 90
!
crypto isakmp client configuration group easy
key cisco
domain foo.com
pool dpool
acl 101
crypto isakmp profile vi
match identity group easy
isakmp authorization list default
client configuration address respond
client configuration group easy
virtual-template 1
!
!
crypto ipsec transform-set set esp-3des esp-sha-hmac
!
crypto ipsec profile vi
set transform-set set
set isakmp-profile vi
!
!
interface Loopback0
ip address 10.4.0.1 255.255.255.0
!
interface Ethernet0/0
ip address 10.3.0.2 255.255.255.0
no keepalive
no cdp enable
interface Ethernet1/0
no ip address
no keepalive
no cdp enable
!
interface Virtual-Template1 type tunnel
ip unnumbered Ethernet0/0
tunnel mode ipsec ipv4
tunnel protection ipsec profile vi
!
ip local pool dpool 10.5.0.1 10.5.0.10
!
ip classless
ip route 10.2.0.0 255.255.255.0 10.3.0.1
no ip http server
no ip http secure-server
!
!
access-list 101 permit ip 10.4.0.0 0.0.0.255 any
no cdp run
!
!
line con 0
line aux 0
line vty 0 4
!
end
Pushing a Configuration URL Through a Mode-Configuration
Exchange: Examples
The following show crypto ipsec client ezvpn command output displays the mode configuration URL location and version:
Router# show crypto ipsec client ezvpn
Easy VPN Remote Phase: 5
Tunnel name : branch
Inside interface list: Vlan1
Outside interface: FastEthernet0
Current State: IPSEC_ACTIVE
Last Event: SOCKET_UP
Address: 172.16.1.209
Mask: 255.255.255.255
Default Domain: cisco.com
Save Password: Allowed
Configuration URL [version]: tftp://172.16.30.2/branch.cfg [11]
Config status: applied, Last successfully applied version: 11
Current EzVPN Peer: 192.168.10.1
The following show crypto isakmp peers config command output displays all manageability information that is sent by the remote device.
Router# show crypto isakmp peers config
Client-Public-Addr=192.168.10.2:500; Client-Assigned-Addr=172.16.1.209; Client-Group=branch; Client-User=branch; Client-Hostname=branch.; Client-Platform=Cisco 1711; Client-Serial=FOC080210E2 (412454448); Client-Config-Version=11; Client-Flash=33292284; Client-Available-Flash=10202680; Client-Memory=95969280; Client-Free-Memory=14992140; Client-Image=flash:c1700-advipservicesk9-mz.ef90241;
Client-Public-Addr=192.168.10.3:500; Client-Assigned-Addr=172.16.1.121; Client-Group=store; Client-User=store; Client-Hostname=831-storerouter.; Client-Platform=Cisco C831; Client-Serial=FOC08472UXR (1908379618); Client-Config-Version=2; Client-Flash=24903676; Client-Available-Flash=5875028; Client-Memory=45298688; Client-Free-Memory=6295596; Client-Image=flash:c831-k9o3y6-mz.ef90241
Per User AAA Policy Download with PKI: Example
The following output shows that the Per User AAA Policy Download with PKI feature has been configured on the Easy VPN server.
Router# show running-config
Building configuration...
Current configuration : 7040 bytes
!
! Last configuration change at 21:06:51 UTC Tue Jun 28 2005
!
version 12.4
no service pad
service timestamps debug uptime
service timestamps log uptime
no service password-encryption
!
hostname GEN
!
boot-start-marker
boot-end-marker
!
!
aaa new-model
!
!
aaa group server radius usrgrppki
server 10.76.248.201 auth-port 1645 acct-port 1646
!
aaa authentication login xauth group usrgrppki
aaa authentication login usrgrp group usrgrppki
aaa authorization network usrgrp group usrgrppki
!
aaa session-id common
!
resource policy
!
ip subnet-zero
!
!
ip cef
!
!
ip address-pool local
!
!
crypto pki trustpoint ca-server
enrollment url http://10.7.7.2:80
revocation-check none
rsakeypair rsa-pair
! Specify the field within the certificate that will be used as a username to do a per-user AAA lookup into the RADIUS database. In this example, the contents of the commonname will be used to do a AAA lookup. In the absence of this statement, by default the contents of the "unstructured name" field in the certificate is used for AAA lookup.
authorization username subjectname commonname
!
!
crypto pki certificate map CERT-MAP 1
subject-name co yourname
name co yourname
!
crypto pki certificate chain ca-server
certificate 02
308201EE 30820157 A0030201 02020102 300D0609 2A864886 F70D0101 04050030
14311230 10060355 04031309 63612D73 65727665 72301E17 0D303530 36323832
30303731 345A170D 30363036 32383230 30373134 5A301531 13301106 092A8648
86F70D01 09021604 47454E2E 30819F30 0D06092A 864886F7 0D010101 05000381
8D003081 89028181 00ABF8F0 FDFFDF8D F22098D6 A48EE0C3 F505DD96 C0022EA4
EAB95EE8 1F97F450 990BB0E6 F2B7151F C5C79391 93822FE4 DEE5B00C A03412BB
9B715AAD D6C31F93 D8802658 AF9A8866 63811942 913D0C02 C3E328CC 1C046E94
F73B7C1A 4497F86E 74A627BC B809A3ED 293C15F2 8DCFA217 5160F9A4 09D52044
350F85AF 08B357F5 D7020301 0001A34F 304D300B 0603551D 0F040403 0205A030
1F060355 1D230418 30168014 F9BC4498 3DA4D51D 451EFEFD 5B1F5F73 8D7B1C9B
301D0603 551D0E04 1604146B F6B2DFD1 1FE237FF 23294129 E55D9C48 CCB04630
0D06092A 864886F7 0D010104 05000381 81004AFF 2BE300C1 15D0B191 C20D06E0
260305A6 9DF610BB 24211516 5AE73B62 78E01FE4 0785776D 3ADFA3E2 CE064432
1C93E82D 93B5F2AB 9661EDD3 499C49A8 F87CA553 9132F239 1D50187D 21CC3148
681F5043 2F2685BC F544F4FF 8DF535CB E55B5F36 31FFF025 8969D9F8 418C8AB7
C569B022 46C3C63A 22DD6516 C503D6C8 3D81
quit
certificate ca 01
30820201 3082016A A0030201 02020101 300D0609 2A864886 F70D0101 04050030
14311230 10060355 04031309 63612D73 65727665 72301E17 0D303530 36323832
30303535 375A170D 30383036 32373230 30353537 5A301431 12301006 03550403
13096361 2D736572 76657230 819F300D 06092A86 4886F70D 01010105 0003818D
00308189 02818100 BA1A4413 96339C6B D36BD720 D25C9A44 E0627A29 97E06F2A
69B268ED 08C7144E 7058948D BEA512D4 40588B87 322C5D79 689427CA 5C54B3BA
82FAEC53 F6AC0B5C 615D032C 910CA203 AC6AB681 290D9EED D31EB185 8D98E1E7
FF73613C 32290FD6 A0CBDC40 6E4D6B39 DE1D86BA DE77A55E F15299FF 97D7C185
919F81C1 30027E0F 02030100 01A36330 61300F06 03551D13 0101FF04 05300301
01FF300E 0603551D 0F0101FF 04040302 0186301F 0603551D 23041830 168014F9
BC44983D A4D51D45 1EFEFD5B 1F5F738D 7B1C9B30 1D060355 1D0E0416 0414F9BC
44983DA4 D51D451E FEFD5B1F 5F738D7B 1C9B300D 06092A86 4886F70D 01010405
00038181 003EF397 F4D98BDE A4322FAF 4737800F 1671F77E BD6C45AE FB91B28C
F04C98F0 135A40C6 635FDC29 63C73373 5D5BBC9A F1BBD235 F66CE1AD 6B4BFC7A
AB18C8CC 1AB93AF3 7AC67436 930E9C81 F43F7570 A8FE09AE 3DEA01D1 DA6BD0CB
83F9A77F 1DFAFE5E 2F1F206B F1FDD8BE 6BB57A3C 8D03115D B1F64A3F 7A7557C1
09B0A34A DB
quit
!
!
crypto isakmp policy 10
group 2
crypto isakmp keepalive 10
crypto isakmp profile ISA-PROF
match certificate CERT-MAP
isakmp authorization list usrgrp
client pki authorization list usrgrp
client configuration address respond
client configuration group pkiuser
virtual-template 2
!
!
crypto ipsec transform-set trans2 esp-3des esp-sha-hmac
!
crypto ipsec profile IPSEC_PROF
set transform-set trans2
!
crypto ipsec profile ISC_IPSEC_PROFILE_1
set transform-set trans2
!
!
crypto call admission limit ike sa 40
!
!
interface Loopback0
ip address 10.3.0.1 255.255.255.255
no ip route-cache cef
no ip route-cache
!
interface Loopback1
ip address 10.76.0.1 255.255.255.255
no ip route-cache cef
no ip route-cache
!
interface Ethernet3/0
ip address 10.76.248.209 255.255.255.255
no ip route-cache cef
no ip route-cache
duplex half
!
!
interface Ethernet3/2
ip address 10.2.0.1 255.255.255.0
no ip route-cache cef
no ip route-cache
duplex half
!
!
interface Serial4/0
no ip address
no ip route-cache cef
no ip route-cache
shutdown
serial restart-delay 0
!
interface Serial4/1
no ip address
no ip route-cache cef
no ip route-cache
shutdown
serial restart-delay 0
!
interface Serial4/2
no ip address
no ip route-cache cef
no ip route-cache
shutdown
serial restart-delay 0
!
interface Serial4/3
no ip address
no ip route-cache cef
no ip route-cache
shutdown
serial restart-delay 0
!
interface FastEthernet5/0
ip address 10.9.4.77 255.255.255.255
no ip route-cache cef
no ip route-cache
duplex half
!
interface FastEthernet6/0
ip address 10.7.7.1 255.255.255.0
no ip route-cache cef
no ip route-cache
duplex full
!
interface Virtual-Template1
no ip address
!
interface Virtual-Template2 type tunnel
ip unnumbered Loopback0
tunnel source Ethernet3/2
tunnel mode ipsec ipv4
tunnel protection ipsec profile IPSEC_PROF
!
router eigrp 20
network 172.16.0.0
auto-summary
!
ip local pool ourpool 10.6.6.6
ip default-gateway 10.9.4.1
ip classless
ip route 10.1.0.1 255.255.255.255 10.0.0.2
ip route 10.2.3.0 255.255.0.0 10.2.4.4
ip route 10.9.1.0 255.255.0.0 10.4.0.1
ip route 10.76.0.0 255.255.0.0 10.76.248.129
ip route 10.11.1.1 255.255.255.0 10.7.7.2
!
no ip http server
no ip http secure-server
!
!
logging alarm informational
arp 10.9.4.1 0011.bcb4.d40a ARPA
!
!
radius-server host 10.76.248.201 auth-port 1645 acct-port 1646 key cisco
!
control-plane
!
!
gatekeeper
shutdown
!
!
line con 0
stopbits 1
line aux 0
stopbits 1
line vty 0 4
!
!
end
Per-User Attributes on an Easy VPN Server: Example
The following example shows that per-user attributes have been configured on an Easy VPN server.
!
aaa new-model
!
!
aaa authentication login default local
aaa authentication login noAAA none
aaa authorization network default local
!
aaa attribute list per-group
attribute type inacl "per-group-acl" service ike protocol ip mandatory
!
aaa session-id common
!
resource policy
!
ip subnet-zero
!
!
ip cef
!
!
username example password 0 example
!
!
crypto isakmp policy 3
authentication pre-share
group 2
crypto isakmp xauth timeout 90
!
crypto isakmp client configuration group PerUserAAA
key cisco
pool dpool
crypto aaa attribute list per-group
!
crypto isakmp profile vi
match identity group PerUserAAA
isakmp authorization list default
client configuration address respond
client configuration group PerUserAAA
virtual-template 1
!
!
crypto ipsec transform-set set esp-3des esp-sha-hmac
!
crypto ipsec profile vi
set transform-set set
set isakmp-profile vi
!
!
interface GigabitEthernet0/0
description 'EzVPN Peer'
ip address 192.168.1.1 255.255.255.128
duplex full
speed 100
media-type rj45
no negotiation auto
!
interface GigabitEthernet0/1
no ip address
shutdown
duplex auto
speed auto
media-type rj45
no negotiation auto
interface Virtual-Template1 type tunnel
ip unnumbered GigabitEthernet0/0
tunnel mode ipsec ipv4
tunnel protection ipsec profile vi
!
ip local pool dpool 10.5.0.1 10.5.0.10
ip classless
!
no ip http server
no ip http secure-server
!
!
ip access-list extended per-group-acl
permit tcp any any
deny icmp any any
logging alarm informational
logging trap debugging
!
control-plane
!
gatekeeper
shutdown
!
line con 0
line aux 0
stopbits 1
line vty 0 4
!
!
end
Network Admission Control: Example
The following is output for an Easy VPN server that has been enabled with Network Admission Control.

Note ![]() Network Admission Control is supported on an Easy VPN server only when the server uses IPsec virtual interfaces. Network Admission Control is enabled on the virtual template interface and applies to all PC clients that use this virtual template interface.
Network Admission Control is supported on an Easy VPN server only when the server uses IPsec virtual interfaces. Network Admission Control is enabled on the virtual template interface and applies to all PC clients that use this virtual template interface.
Router# show running-config
Building configuration...
Current configuration : 5091 bytes
!
version 12.4
!
hostname Router
!
aaa new-model
!
!
aaa authentication login userlist local
!
aaa authentication eou default group radius
aaa authorization network hw-client-groupname local
aaa accounting update newinfo
aaa accounting network acclist start-stop broadcast group radius
aaa session-id common
!
!
! Note 1: EAPoUDP packets will use the IP address of the loopback interface when sending the EAPoUDP hello to the Easy VPN client. Using the IP address ensures that the returning EAPoUDP packets come back encrypted and are associated with the correct virtual access interface. The ip admission (ip admission source-interface Loopback10) command is optional. Instead of using this command, you can specify the IP address of the virtual template to be an address in the inside network space as shown in the configuration of the virtual template below in Note 2.
ip admission source-interface Loopback10
ip admission name test eapoudp inactivity-time 60
!
!
eou clientless username cisco
eou clientless password cisco
eou allow ip-station-id
eou logging
!
username lab password 0 lab
username lab@easy password 0 lab
!
!
crypto isakmp policy 3
encr 3des
authentication pre-share
group 2
!
!
crypto isakmp key 0 cisco address 10.53.0.1
crypto isakmp client configuration group easy
key cisco
domain cisco.com
pool dynpool
acl split-acl
group-lock
configuration url tftp://10.13.0.9/Config-URL_TFTP.cfg
configuration version 111
!
crypto isakmp profile vi
match identity group easy
client authentication list userlist
isakmp authorization list hw-client-groupname
client configuration address respond
client configuration group easy
accounting acclist
virtual-template 2
!
crypto ipsec security-association lifetime seconds 120
crypto ipsec transform-set set esp-3des esp-sha-hmac
crypto ipsec transform-set aes-trans esp-aes esp-sha-hmac
crypto ipsec transform-set transform-1 esp-des esp-sha-hmac
crypto ipsec profile vi
set security-association lifetime seconds 3600
set transform-set set aes-trans transform-1
set isakmp-profile vi
!
!
crypto dynamic-map dynmap 1
set transform-set aes-trans transform-1
reverse-route
!
interface Loopback10
ip address 10.61.0.1 255.255.255.255
!
interface FastEthernet0/0
ip address 10.13.11.173 255.255.255.255
duplex auto
speed auto
!
interface FastEthernet0/1
ip address 10.55.0.1 255.255.255.255
duplex auto
speed auto
!
!
interface Virtual-Template2 type tunnel
! Note2: Use the IP address of the loopback10. This ensures that the EAPoUDP packets that are attached to virtual-access interfaces that are cloned from this virtual template carry the source address of the loopback address and that response packets from the VPN client come back encrypted.
!
ip unnumbered Loopback10
! Enable Network Admission Control for remote VPN clients.
ip admission test
tunnel mode ipsec ipv4
tunnel protection ipsec profile vi
!
!
ip local pool dynpool 172.16.2.65 172.16.2.70
ip classless
ip access-list extended ClientException
permit ip any host 10.61.0.1
ip access-list extended split-acl
permit ip host 10.13.11.185 any
permit ip 10.61.0.0 255.255.255.255 any
permit ip 10.71.0.0 255.255.255.255 any
permit ip 10.71.0.0 255.255.255.255 10.52.0.0 0.255.255.255
permit ip 10.55.0.0 255.255.255.255 any
!
ip radius source-interface FastEthernet0/0
access-list 102 permit esp any any
access-list 102 permit ahp any any
access-list 102 permit udp any any eq 21862
access-list 102 permit ospf any any
access-list 102 deny ip any any
access-list 195 deny ospf any any
access-list 195 permit ip 10.61.0.0 255.255.255.255 10.51.0.0 255.255.255.255
!
!
radius-server attribute 6 on-for-login-auth
radius-server attribute 8 include-in-access-req
radius-server host 10.13.11.185 auth-port 1645 acct-port 1646 key cisco
radius-server vsa send accounting
radius-server vsa send authentication
!
end
Configuring Password Aging: Example
The following example shows that password aging has been configured so that if the password expires, the Easy VPN client is notified.
Current configuration : 4455 bytes
!
version 12.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname xinl-gateway
!
boot-start-marker
boot system flash c2800nm-advsecurityk9-mz.124-7.9.T
boot-end-marker
!
!
aaa new-model
!
!
aaa authentication login USERAUTH passwd-expiry group radius aaa authorization network branch local !
aaa session-id common
!
ip cef
username cisco privilege 15 secret 5 $1$A3HU$bCWjlkrEztDJx6JJzSnMV1 !
!
crypto isakmp policy 1
encr 3des
authentication pre-share
group 2
crypto isakmp client configuration address-pool local dynpool !
crypto isakmp client configuration group branch
key cisco
domain cisco.com
pool dynpool
!
!
crypto ipsec transform-set transform-1 esp-3des esp-sha-hmac !
crypto isakmp profile profile2
client authentication list USERAUTH
match identity group branch
isakmp authorization list branch
client configuration address respond
virtual-template 1
crypto ipsec profile vi
set transform-set transform-1
interface GigabitEthernet0/0
description $ETH-LAN$$ETH-SW-LAUNCH$$INTF-INFO-GE 0/0$
ip address 192.168.1.100 255.255.255.0
duplex auto
speed auto
crypto map dynmap
!
interface GigabitEthernet0/1
description $ES_LAN$
ip address 172.19.217.96 255.255.255.0
duplex auto
speed auto
!
!interface Virtual-Template1 type tunnel
ip unnumbered Ethernet0/0
no clns route-cache
tunnel mode ipsec ipv4
tunnel protection ipsec profile vi
!
ip local pool dpool 10.0.0.1 10.0.0.3
!
radius-server host 172.19.220.149 auth-port 1645 acct-port 1646 key cisco radius-server vsa send authentication !
control-plane
!
!
end
Split DNS: Examples
In the following example, the split tunnel list named "101" contains the 10.168.0.0/16 network. It is necessary to include this network information so that the DNS requests to the internal DNS server of 10.168.1.1 are encrypted.
crypto isakmp client configuration group home
key abcd
acl 101
dns 10.168.1.1. 10.168.1.2
show Output
The following show command output example shows that www.ciscoexample1.com and www.ciscoexample2.com have been added to the policy group:
Router# show running-config | security group
crypto isakmp client configuration group 831server
key abcd
dns 10.104.128.248
split-dns www.ciscoexample1.com
split-dns www.ciscoexample2.com
group home2 key abcd
The following show command output example displays currently configured DNS views:
Router# show ip dns view
DNS View default parameters:
Logging is off
DNS Resolver settings:
Domain lookup is enabled
Default domain name: cisco.com
Domain search list:
Lookup timeout: 3 seconds
Lookup retries: 2
Domain name-servers:
172.16.168.183
DNS Server settings:
Forwarding of queries is enabled
Forwarder addresses:
DNS View ezvpn-internal-view parameters:
Logging is off
DNS Resolver settings:
Domain lookup is enabled
Default domain name:
Domain search list:
Lookup timeout: 3 seconds
Lookup retries: 2
Domain name-servers:
10.104.128.248
DNS Server settings:
Forwarding of queries is enabled
Forwarder addresses:
The following show command output example displays currently configured DNS view lists.
Router# show ip dns view-list
View-list ezvpn-internal-viewlist:
View ezvpn-internal-view:
Evaluation order: 10
Restrict to ip dns name-list: 1
View default:
Evaluation order: 20
The following show command output displays DNS name lists.
Router# show ip dns name-list
ip dns name-list 1
permit www.ciscoexample1.com
permit www.ciscoexample2.com
DHCP Client Proxy: Examples
The following examples display DHCP client proxy output information using show and debug commands.
show Output

Note ![]() To use the show ip dhcp command, the DHCP server must be a Cisco IOS server.
To use the show ip dhcp command, the DHCP server must be a Cisco IOS server.
The following show ip dhcp pool command output provides information about the DHCP parameters:
Router# show ip dhcp pool
Pool dynpool :
Utilization mark (high/low) : 100 / 0
Subnet size (first/next) : 0 / 0
Total addresses : 254
Leased addresses : 1
Pending event : none
1 subnet is currently in the pool:
Current index IP address range Leased addresses
10.3.3.1 - 10.3.3.254 1
No relay targets associated with class aclass
The following show ip dhcp command output provides information about the DHCP bindings:
Router# show ip dhcp binding
Bindings from all pools not associated with VRF:
IP address Client-ID/ Lease expiration Type
Hardware address/User name
10.3.3.5 0065.7a76.706e.2d63. Apr 04 2006 06:01 AM Automatic 6c69.656e.74
debug Output
The following example shows how the debug crypto isakmp and debug ip dhcp server events commands can be used to troubleshoot your DHCP client proxy support configuration:
*Apr 3 06:01:32.047: ISAKMP: Config payload REQUEST *Apr 3 06:01:32.047: ISAKMP:(1002):checking request:
*Apr 3 06:01:32.047: ISAKMP: IP4_ADDRESS
*Apr 3 06:01:32.047: ISAKMP: IP4_NETMASK
*Apr 3 06:01:32.047: ISAKMP: MODECFG_CONFIG_URL
*Apr 3 06:01:32.047: ISAKMP: MODECFG_CONFIG_VERSION
*Apr 3 06:01:32.047: ISAKMP: IP4_DNS
*Apr 3 06:01:32.047: ISAKMP: IP4_DNS
*Apr 3 06:01:32.047: ISAKMP: IP4_NBNS
*Apr 3 06:01:32.047: ISAKMP: IP4_NBNS
*Apr 3 06:01:32.047: ISAKMP: SPLIT_INCLUDE
*Apr 3 06:01:32.047: ISAKMP: SPLIT_DNS
*Apr 3 06:01:32.047: ISAKMP: DEFAULT_DOMAIN
*Apr 3 06:01:32.047: ISAKMP: MODECFG_SAVEPWD
*Apr 3 06:01:32.047: ISAKMP: INCLUDE_LOCAL_LAN
*Apr 3 06:01:32.047: ISAKMP: PFS
*Apr 3 06:01:32.047: ISAKMP: BACKUP_SERVER
*Apr 3 06:01:32.047: ISAKMP: APPLICATION_VERSION
*Apr 3 06:01:32.047: ISAKMP: MODECFG_BANNER
*Apr 3 06:01:32.047: ISAKMP: MODECFG_IPSEC_INT_CONF
*Apr 3 06:01:32.047: ISAKMP: MODECFG_HOSTNAME
*Apr 3 06:01:32.047: ISAKMP/author: Author request for group homesuccessfully sent to AAA *Apr 3 06:01:32.047: ISAKMP:(1002):Input = IKE_MESG_FROM_PEER, IKE_CFG_REQUEST
*Apr 3 06:01:32.047: ISAKMP:(1002):Old State = IKE_P1_COMPLETE New State = IKE_CONFIG_AUTHOR_AAA_AWAIT
*Apr 3 06:01:32.047: ISAKMP:(1002):attributes sent in message:
*Apr 3 06:01:32.047: Address: 10.2.0.0
*Apr 3 06:01:32.047: Requesting DHCP Server0 address 10.3.3.3 *Apr 3 06:01:32.047: DHCPD: Sending notification of DISCOVER:
*Apr 3 06:01:32.047: DHCPD: htype 1 chaddr aabb.cc00.6600
*Apr 3 06:01:32.047: DHCPD: circuit id 00000000
*Apr 3 06:01:32.047: DHCPD: Seeing if there is an internally specified pool class:
*Apr 3 06:01:32.047: DHCPD: htype 1 chaddr aabb.cc00.6600
*Apr 3 06:01:32.047: DHCPD: circuit id 00000000
*Apr 3 06:01:34.063: DHCPD: Adding binding to radix tree (10.3.3.5) *Apr 3 06:01:34.063: DHCPD: Adding binding to hash tree *Apr 3 06:01:34.063: DHCPD: assigned IP address 10.3.3.5 to client 0065.7a76.706e.2d63.6c69.656e.74.
*Apr 3 06:01:34.071: DHCPD: Sending notification of ASSIGNMENT:
*Apr 3 06:01:34.071: DHCPD: address 10.3.3.5 mask 255.255.255.0
*Apr 3 06:01:34.071: DHCPD: htype 1 chaddr aabb.cc00.6600
*Apr 3 06:01:34.071: DHCPD: lease time remaining (secs) = 86400
*Apr 3 06:01:34.183: Obtained DHCP address 10.3.3.5 *Apr 3 06:01:34.183: ISAKMP:(1002):allocating address 10.3.3.5 *Apr 3 06:01:34.183: ISAKMP: Sending private address: 10.3.3.5 *Apr 3 06:01:34.183: ISAKMP: Sending subnet mask: 255.255.255.0
cTCP Session: Example
The following debug crypto ctcp command output displays information about a cTCP session, and it includes comments about the output:
Router# debug crypto ctcp
! In the following two lines, a cTCP SYN packet is received from the client, and the cTCP connection is created.
*Sep 26 11:14:37.135: cTCP: Connection[648B50C0] 10.76.235.21:3519 10.76.248.239:10000: created
*Sep 26 11:14:37.135: cTCP: SYN from 10.76.235.21:3519
! In the following line, the SYN acknowledgement is sent to the client.
*Sep 26 11:14:37.135: cTCP: Sending SYN(680723B2)ACK(100C637) to 10.76.235.21:3519
! In the following two lines, an acknowledgement is received, and connection setup is complete. IKE packets should now be received on this newly created cTCP session.
*Sep 26 11:14:37.135: cTCP: Connection[648B50C0] 10.76.235.21:3519 10.76.248.239:10000: found
*Sep 26 11:14:37.135: cTCP: ACK from 10.76.235.21:3519
*Sep 26 11:14:37.727: cTCP: Connection[648B50C0] 10.76.235.21:3519 10.76.248.239:10000: found
*Sep 26 11:14:37.731: cTCP: updating PEER Seq number to 16828803l
*Sep 26 11:14:37.731: cTCP: Pak with contiguous buffer
*Sep 26 11:14:37.731: cTCP: mangling IKE packet from peer: 10.76.235.21:500->3519 10.76.248.239:500->500
*Sep 26 11:14:37.731: cTCP: Connection[648B50C0] 10.76.235.21:3519 10.76.248.239:10000: found
*Sep 26 11:14:37.799: cTCP: demangling outbound IKE packet: 10.76.248.239:500->500 10.76.235.21:3519->500
*Sep 26 11:14:37.799: cTCP: encapsulating IKE packet
*Sep 26 11:14:37.799: cTCP: updating LOCAL Seq number to 1745298727l
! The above lines show that after the required number of IKE packets are exchanged, IKE and IPsec SAs are created.
*Sep 26 11:14:40.335: cTCP: updating PEER Seq number to 16830431l
*Sep 26 11:14:40.335: cTCP: Pak with particles
*Sep 26 11:14:40.335: cTCP: encapsulating pak
*Sep 26 11:14:40.339: cTCP: datagramstart 0xF2036D8, network_start 0xF2036D8, size 112
*Sep 26 11:14:40.339: cTCP: Pak with contiguous buffer
*Sep 26 11:14:40.339: cTCP: allocated new buffer
*Sep 26 11:14:40.339: cTCP: updating LOCAL Seq number to 1745299535l
*Sep 26 11:14:40.339: IP: s=10.76.248.239 (local), d=10.76.235.21 (FastEthernet1/1), len 148, cTCP
! The above lines show that Encapsulating Security Payload (ESP) packets are now being sent and received.
VRF Assignment by a AAA Server: Example
The following output example shows that neither a VRF nor an IP address has been defined:
aaa new-model
aaa authentication login VPN group radius
aaa authorization network VPN group radius
!
ip vrf example1
rd 1:1
!
crypto isakmp profile example1
match identity group example1group
client authentication list VPN
isakmp authorization list VPN
client configuration address respond
virtual-template 10
!
crypto ipsec transform-set TS esp-3des esp-sha-hmac
!
crypto ipsec profile example1
set transform-set TS
set isakmp-profile example1
!
interface Virtual-Template10 type tunnel
! The next line shows that neither VRF nor an IP address has been defined.
no ip address
tunnel mode ipsec ipv4
tunnel protection ipsec profile example1
Additional References
The following sections provide references related to the EasyVPN Server feature.
Related Documents
|
|
|
|---|---|
Configuring and Assigning the Easy VPN Remote Configuration |
"Cisco Easy VPN Remote" module in the Cisco IOS Security Configuration Guide: Secure Connectivity |
General information on IPsec and VPN |
• • • |
IPsec Protocol options and attributes |
"Configuring Internet Key Exchange for IPsec VPNs" module in the Cisco IOS Security Configuration Guide: Secure Connectivity |
IPsec virtual tunnels |
"IPsec Virtual Tunnel Interface" module in the Cisco IOS Security Configuration Guide: Secure Connectivity |
Network Admission Control |
"Network Admission Control" module in the Cisco IOS Security Configuration Guide: Securing User Services |
RRI |
"IPSec VPN High Availability Enhancements" module in the Cisco IOS Security Configuration Guide: Secure Connectivity |
Standards
|
|
|
|---|---|
None |
- |
MIBs
|
|
|
|---|---|
None |
To locate and download MIBs for selected platforms, Cisco IOS software releases, and feature sets, use Cisco MIB Locator found at the following URL: |
RFCs
|
|
|
|---|---|
Technical Assistance
Feature Information for Easy VPN Server
Table 3 lists the release history for this feature.
Not all commands may be available in your Cisco IOS software release. For release information about a specific command, see the command reference documentation.
Use Cisco Feature Navigator to find information about platform support and software image support. Cisco Feature Navigator enables you to determine which Cisco IOS and Catalyst OS software images support a specific software release, feature set, or platform. To access Cisco Feature Navigator, go to http://tools.cisco.com/ITDIT/CFN/jsp/index.jsp. An account on Cisco.com is not required.

Note ![]() Table 3 lists only the Cisco IOS software release that introduced support for a given feature in a given Cisco IOS software release train. Unless noted otherwise, subsequent releases of that Cisco IOS software release train also support that feature.
Table 3 lists only the Cisco IOS software release that introduced support for a given feature in a given Cisco IOS software release train. Unless noted otherwise, subsequent releases of that Cisco IOS software release train also support that feature.
|
|
|
|
|---|---|---|
Easy VPN Server |
12.2(8)T |
The Easy VPN Server feature introduces server support for the Cisco VPN Client Release 3.x and later software clients and Cisco VPN hardware clients (such as the Cisco 800, Cisco 900, Cisco 1700, VPN 3002, and PIX 501 devices). This feature allows a remote end user to communicate using IP Security (IPsec) with any Cisco IOS Virtual Private Network (VPN) gateway. Centrally managed IPsec policies are "pushed" to the client device by the server, minimizing configuration by the end user. |
12.3(2)T |
The following commands were introduced or modified: RADIUS support for user profiles, user-based policy control, session monitoring for VPN group access, backup-gateway list, and PFS. |
|
12.3(7)T |
The netmask command was integrated for use on the Easy VPN server. For information about configuring this command, see the following section: • |
|
12.4(2)T |
The following feature was added in this release: • |
|
12.4(6)T |
The Central Policy Push Firewall Policy Push feature was added. |
|
12.2(33)SRA |
This feature was integrated into Cisco IOS |
|
12.4(9)T |
The following features were added in this release: • The following section provides information about this feature: • – • The following section provides information about this feature: • The following sections provide information about this feature: – • The following sections provide information about this feature: – – – • The following sections provide information about this feature: – – The following new commands were introduced: crypto aaa attribute list, debug ip dns, dhcp-server (isakmp), dhcp-timeout, show ip dns name-list, show ip dns view, and show ip dns view-list The following commands were modified: crypto isakmp client configuration group |
|
12.4(11)T |
The DHCP Client Proxy feature was updated to include manageability enhancements for remote access VPNs. The following commands were modified: clear crypto session, crypto isakmp client configuration group, debug crypto condition, show crypto debug-condition, show crypto isakmp peers, show crypto isakmp profile, show crypto isakmp sa, show crypto session |
|
EasyVPN Server Enhancements |
Cisco IOS XE Release 2.1 |
This feature was introduced on Cisco ASR 1000 Series Routers. |
Glossary
AAA—authentication, authorization, and accounting. Framework of security services that provides the method for identifying users (authentication), for remote access control (authorization), and for collecting and sending security server information used for billing, auditing, and reporting (accounting).
aggressive mode (AM)—Mode during Internet Key Exchange negotiation. Compared to main mode (MM), AM eliminates several steps, which makes it faster but less secure than MM. Cisco IOS software will respond in aggressive mode to an Internet Key Exchange (IKE) peer that initiates aggressive mode.
AV pair—attribute-value pair. Additional authentication and authorization information in the following format: Cisco:AVPair="protocol:attribute=value".
IKE—Internet Key Exchange. Hybrid protocol that implements Oakley key exchange and Skeme key exchange inside the ISAKMP framework. Although IKE can be used with other protocols, its initial implementation is with IPsec. IKE provides authentication of the IPsec peers, negotiates IPsec keys, and negotiates IPsec security associations.
IPsec—IP Security Protocol. Framework of open standards that provides data confidentiality, data integrity, and data authentication between participating peers. IPsec provides these security services at the IP layer. IPsec uses IKE to handle negotiation of protocols and algorithms based on local policy and to generate the encryption and authentication keys to be used by IPsec. IPsec can be used to protect one or more data flows between a pair of hosts, between a pair of security gateways, or between a security gateway and a host.
ISAKMP—Internet Security Association Key Management Protocol. Protocol framework that defines payload formats, the mechanics of implementing a key exchange protocol, and the negotiation of a security association.
MM—main mode. Mode that is slower than aggressive mode but more secure and more flexible than aggressive mode because it can offer an IKE peer more security proposals. The default action for IKE authentication (Rivest, Shamir, and Adelman signature (rsa-sig), RSA encryption (rsa-encr), or preshared) is to initiate main mode.
policy push—Allows administrators to push policies that enforce security to the Cisco Easy VPN (software) Client and related firewall software.
reverse route injection (RRI)—Simplified network design for VPNs on which there is a requirement for redundancy or load balancing. RRI works with both dynamic and static crypto maps.
In the dynamic case, as remote peers establish IPsec security associations with an RRI enabled router, a static route is created for each subnet or host protected by that remote peer. For static crypto maps, a static route is created for each destination of an extended access-list rule.
SA—security association. Description of how two or more entities will utilize security services to communicate securely. For example, an IPsec SA defines the encryption algorithm (if used), the authentication algorithm, and the shared session key to be used during the IPsec connection.
Both IPsec and IKE require and use SAs to identify the parameters of their connections. IKE can negotiate and establish its own SA. The IPsec SA is established either by IKE or by manual user configuration.
VPN—Virtual Private Network. Framework that consists of multiple peers transmitting private data securely to one another over an otherwise public infrastructure. In this framework, inbound and outbound network traffic is protected using protocols that tunnel and encrypt all data. This framework permits networks to extend beyond their local topology, while remote users are provided with the appearance and functionality of a direct network connection.
 Feedback
Feedback