- Contents
- Prerequisites for Writing EEM Policies Using the Cisco IOS CLI
- Information About Writing EEM Policies Using the Cisco IOS CLI
- How to Write EEM Policies Using the Cisco IOS CLI
- Registering and Defining an Embedded Event Manager Applet
- Registering and Defining an Embedded Event Manager Policy to Run Manually
- Unregistering Embedded Event Manager Policies
- Suspending All Embedded Event Manager Policy Execution
- Configuring and Tracking a Stub Object Using Embedded Event Manager
- Displaying Embedded Event Manager History Data
- Displaying Embedded Event Manager Registered Policies
- Configuring Event SNMP Notification
- Configuring Multiple Event Support
- Configuring EEM Class-Based Scheduling
- Prerequisites
- Holding a Scheduled EEM Policy Event or Event Queue
- Resuming Execution of EEM Policy Events or Event Queues
- Clearing Pending EEM Policy Events or Event Queues
- Modifying the Scheduling Parameters of EEM Policy Events or Event Queues
- Verifying Class-Based Scheduled Activities of EEM Policies
- Verifying Class-Based Active EEM Policies
- Verifying Pending EEM Policies
- Configring EEM Applet (Interactive CLI) Support
- Configuring SNMP Library Extensions
- Configuring Variable Logic for EEM Applets
- Configuring Event SNMP Object
- Disabling AAA Authorization
- Configuring Description of an Embedded Event Manager Applet
- Configuration Examples for Writing EEM Policies Using the Cisco IOS CLI
- Embedded Event Manager Applet Configuration: Examples
- Embedded Event Manager Manual Policy Execution: Examples
- Configuring and Tracking a Stub Object Using Embedded Event Manager: Example
- Embedded Event Manager Watchdog System Monitor (Cisco IOS) Event Detector Configuration: Example
- Configuration SNMP Library Extensions: Examples
- Configuring Variable Logic for EEM Applets: Examples
- Configuring Event SNMP-Object: Examples
- Configuring Description of an EEM Applet: Examples
- Where to Go Next
- Additional References
- Feature Information for Writing EEM Policies Using the Cisco IOS CLI
Writing Embedded Event Manager Policies Using the Cisco IOS CLI
This module describes how to write Embedded Event Manager (EEM) policies using Cisco IOS command-line interface (CLI) applets to handle Cisco IOS software faults and events. EEM is a distributed and customized approach to event detection and recovery offered directly in a Cisco IOS device. EEM offers the ability to monitor events and take informational, corrective, or any desired action when the monitored events occur or when a threshold is reached. The EEM policy engine receives notifications when faults and other events occur. EEM policies implement recovery on the basis of the current state of the system and the actions specified in the policy for a given event. Recovery actions are triggered when the policy is run.
Finding Feature Information in This Module
Your Cisco IOS software release may not support all of the features documented in this module. To reach links to specific feature documentation in this module and to see a list of the releases in which each feature is supported, use the "Feature Information for Writing EEM Policies Using the Cisco IOS CLI" section.
Finding Support Information for Platforms and Cisco IOS and Catalyst OS Software Images
Use Cisco Feature Navigator to find information about platform support and Cisco IOS and Catalyst OS software image support. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Contents
•![]() Prerequisites for Writing EEM Policies Using the Cisco IOS CLI
Prerequisites for Writing EEM Policies Using the Cisco IOS CLI
•![]() Information About Writing EEM Policies Using the Cisco IOS CLI
Information About Writing EEM Policies Using the Cisco IOS CLI
•![]() How to Write EEM Policies Using the Cisco IOS CLI
How to Write EEM Policies Using the Cisco IOS CLI
•![]() Configuration Examples for Writing EEM Policies Using the Cisco IOS CLI
Configuration Examples for Writing EEM Policies Using the Cisco IOS CLI
•![]() Feature Information for Writing EEM Policies Using the Cisco IOS CLI
Feature Information for Writing EEM Policies Using the Cisco IOS CLI
Prerequisites for Writing EEM Policies Using the Cisco IOS CLI
•![]() Before writing EEM policies, you should be familiar with the concepts explained in the "Embedded Event Manager Overview" module.
Before writing EEM policies, you should be familiar with the concepts explained in the "Embedded Event Manager Overview" module.
•![]() If the action cns-event command is used, access to a Cisco Networking Services (CNS) Event gateway must be configured.
If the action cns-event command is used, access to a Cisco Networking Services (CNS) Event gateway must be configured.
•![]() If the action force-switchover command is used, a secondary processor must be configured on the device.
If the action force-switchover command is used, a secondary processor must be configured on the device.
•![]() If the action snmp-trap command is used, the snmp-server enable traps event-manager command must be enabled to permit SNMP traps to be sent from the Cisco IOS device to the SNMP server. Other relevant snmp-server commands must also be configured; for details see the action snmp-trap command page.
If the action snmp-trap command is used, the snmp-server enable traps event-manager command must be enabled to permit SNMP traps to be sent from the Cisco IOS device to the SNMP server. Other relevant snmp-server commands must also be configured; for details see the action snmp-trap command page.
Information About Writing EEM Policies Using the Cisco IOS CLI
To write EEM policies using the Cisco IOS CLI, you should understand the following concepts:
•![]() Embedded Event Manager Policies
Embedded Event Manager Policies
•![]() Embedded Event Manager Built-In Environment Variables Used in EEM Applets
Embedded Event Manager Built-In Environment Variables Used in EEM Applets
Embedded Event Manager Policies
EEM offers the ability to monitor events and take informational or corrective action when the monitored events occur or a threshold is reached. An EEM policy is an entity that defines an event and the actions to be taken when that event occurs. There are two types of EEM policies: an applet or a script. An applet is a simple form of policy that is defined within the CLI configuration. A script is a form of policy that is written in Tool Command Language (Tcl).
EEM Applet
An EEM applet is a concise method for defining event screening criteria and the actions to be taken when that event occurs. In applet configuration mode, three types of configuration statements are supported. The event commands are used to specify the event criteria to trigger the applet to run, the action commands are used to specify an action to perform when the EEM applet is triggered, and the set command is used to set the value of an EEM applet variable. Currently only the _exit_status variable is supported for the set command.
Only one event configuration command is allowed within an applet configuration. When applet configuration mode is exited and no event command is present, a warning is displayed stating that no event is associated with this applet. If no event is specified, this applet is not considered registered. When no action is associated with this applet, events are still triggered but no actions are performed. Multiple action configuration commands are allowed within an applet configuration. Use the show event manager policy registered command to display a list of registered applets.
Before modifying an EEM applet, be aware that the existing applet is not replaced until you exit applet configuration mode. While you are in applet configuration mode modifying the applet, the existing applet may be executing. It is safe to modify the applet without unregistering it. When you exit applet configuration mode, the old applet is unregistered and the new version is registered.
The action configuration commands are uniquely identified using the label argument, which can be any string value. Actions are sorted in ascending alphanumeric key sequence using the label argument as the sort key, and they are run using this sequence.
The Embedded Event Manager schedules and runs policies on the basis of an event specification that is contained within the policy itself. When applet configuration mode is exited, EEM examines the event and action commands that are entered and registers the applet to be run when a specified event occurs.
EEM Script
Scripts are defined off the networking device using an ASCII editor. The script is then copied to the networking device and registered with EEM. Tcl scripts are supported by EEM.
EEM allows you to write and implement your own policies using Tcl. Writing an EEM policy involves:
•![]() Selecting the event for which the policy is run.
Selecting the event for which the policy is run.
•![]() Defining the event detector options associated with logging and responding to the event.
Defining the event detector options associated with logging and responding to the event.
•![]() Choosing the actions to be followed when the event occurs.
Choosing the actions to be followed when the event occurs.
Cisco provides enhancements to Tcl in the form of keyword extensions that facilitate the development of EEM policies. The main categories of keywords identify the detected event, the subsequent action, utility information, counter values, and system information. For more details about writing EEM policies using Tcl, see the "Writing Embedded Event Manager Policies Using Tcl" module.
Embedded Event Manager Built-In Environment Variables Used in EEM Applets
EEM built-in environment variables are a subset of the Cisco-defined environment variables and the built-in variables are available to EEM applets only. The built-in variables can be read-only or can be read and write and these variables may apply to one specific event detector or to all event detectors. Table 1 lists the Cisco built-in environment variables that are read-only alphabetically by event detector and subevent.
How to Write EEM Policies Using the Cisco IOS CLI
This section contains the following tasks:
•![]() Registering and Defining an Embedded Event Manager Applet
Registering and Defining an Embedded Event Manager Applet
•![]() Registering and Defining an Embedded Event Manager Policy to Run Manually
Registering and Defining an Embedded Event Manager Policy to Run Manually
•![]() Unregistering Embedded Event Manager Policies
Unregistering Embedded Event Manager Policies
•![]() Suspending All Embedded Event Manager Policy Execution
Suspending All Embedded Event Manager Policy Execution
•![]() Configuring and Tracking a Stub Object Using Embedded Event Manager
Configuring and Tracking a Stub Object Using Embedded Event Manager
•![]() Displaying Embedded Event Manager History Data
Displaying Embedded Event Manager History Data
•![]() Displaying Embedded Event Manager Registered Policies
Displaying Embedded Event Manager Registered Policies
•![]() Configuring Event SNMP Notification
Configuring Event SNMP Notification
•![]() Configuring Multiple Event Support
Configuring Multiple Event Support
•![]() Configuring EEM Class-Based Scheduling
Configuring EEM Class-Based Scheduling
•![]() Configring EEM Applet (Interactive CLI) Support
Configring EEM Applet (Interactive CLI) Support
•![]() Configuring SNMP Library Extensions
Configuring SNMP Library Extensions
•![]() Configuring Variable Logic for EEM Applets
Configuring Variable Logic for EEM Applets
•![]() Configuring Event SNMP Object
Configuring Event SNMP Object
•![]() Configuring Description of an Embedded Event Manager Applet
Configuring Description of an Embedded Event Manager Applet
Registering and Defining an Embedded Event Manager Applet
Perform this task to register an applet with Embedded Event Manager and to define the EEM applet using the Cisco IOS CLI event and action commands. Only one event command is allowed in an EEM applet. Multiple action commands are permitted. If no event and no action commands are specified, the applet is removed when you exit configuration mode.
The SNMP event detector and the syslog action commands used in this task are just representing any event detector and action commands. For examples using other event detectors and action commands, see the "Embedded Event Manager Applet Configuration: Examples" section.
EEM Environment Variables
EEM environment variables for EEM policies are defined using the EEM event manager environment configuration command. By convention, all Cisco EEM environment variables begin with "_". In order to avoid future conflict, customers are urged not to define new variables that start with "_".
You can display the EEM environment variables set on your system by using the show event manager environment privileged EXEC command.
For example, you can create EEM policies that can send e-mails when an event occurs. Table 2 describes the e-mail-specific environment variables that can be used in EEM policies.
Alphabetical Order of EEM Action Labels
An EEM action label is a unique identifier that can be any string value. Actions are sorted and run in ascending alphanumeric (lexicographical) key sequence using the label as the sort key. If you are using numbers as labels be aware that alphanumerical sorting will sort 10.0 after 1.0, but before 2.0, and in this situation we recommend that you use numbers such as 01.0, 02.0, and so on, or use an initial letter followed by numbers.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() show event manager environment [all | variable-name]
show event manager environment [all | variable-name]
3. ![]() configure terminal
configure terminal
4. ![]() event manager environment variable-name string
event manager environment variable-name string
5. ![]() Repeat Step 4 for all the required environment variables.
Repeat Step 4 for all the required environment variables.
6. ![]() event manager applet applet-name
event manager applet applet-name
7. ![]() event snmp oid oid-value get-type {exact | next} entry-op operator entry-val entry-value [exit-comb {or | and}] [exit-op operator] [exit-val exit-value] [exit-time exit-time-value] poll-interval poll-int-value
event snmp oid oid-value get-type {exact | next} entry-op operator entry-val entry-value [exit-comb {or | and}] [exit-op operator] [exit-val exit-value] [exit-time exit-time-value] poll-interval poll-int-value
8. ![]() action label cli command cli-string [pattern pattern-string]
action label cli command cli-string [pattern pattern-string]
9. ![]() action label syslog [priority priority-level] msg msg-text facility string
action label syslog [priority priority-level] msg msg-text facility string
10. ![]() action label mail server server-address to to-address from from-address [cc cc-address] subject subject body body-text
action label mail server server-address to to-address from from-address [cc cc-address] subject subject body body-text
11. ![]() Add more action commands as required.
Add more action commands as required.
12. ![]() end
end
DETAILED STEPS
|
|
|
|
|---|---|---|
Step 1 |
enable Router> enable |
Enables privileged EXEC mode. • |
Step 2 |
show event manager environment [all | variable-name] Router# show event manager environment all |
(Optional) Displays the name and value of EEM environment variables. • • |
Step 3 |
configure terminal Router# configure terminal |
Enters global configuration mode. |
Step 4 |
event manager environment variable-name string Router(config)# event manager environment _email_to engineering@example.com |
Configures the value of the specified EEM environment variable. • |
Step 5 |
Repeat Step 4 for all the required environment variables. |
Repeat Step 4 to configure all the environment variables required by the policy to be registered in Step 6. |
Step 6 |
event manager applet applet-name Router(config)# event manager applet memory-fail |
Registers the applet with the Embedded Event Manager (EEM) and enters applet configuration mode. |
Step 7 |
event snmp oid oid-value get-type {exact | next} entry-op operator entry-val entry-value [exit-comb {or | and}] [exit-op operator] [exit-val exit-value] [exit-time exit-time-value] poll-interval poll-int-value Router(config-applet)# event snmp oid 1.3.6.1.4.1.9.9.48.1.1.1.6.1 get-type exact entry-op lt entry-val 5120000 poll-interval 90 |
Specifies the event criteria that cause the EEM applet to run. • • |
Step 8 |
action label cli command cli-string [pattern pattern-string] Router(config-applet)# action 1.0 cli command "enable" Router(config-applet)# action 2.0 cli command "clear counters Ethernet0/1" pattern "confirm" Router(config-applet)# action 3.0 cli command "y" |
Specifies the action of executing a Cisco IOS CLI command when an EEM applet is triggered. The pattern keyword is optional and is used only when the command string solicits input. The action cli command ends when the solicited prompt as specified in the optional pattern keyword is received. You are required to specify a regular expression pattern that will match the next solicited prompt. Specification of an incorrect pattern will cause the action cli command to wait forever until the applet execution times out due to the maxrun timer expiration. • |
Step 9 |
action label syslog [priority priority-level] msg msg-text facility string Router(config-applet)# action 1.0 syslog priority critical msg "Memory exhausted; current available memory is $_snmp_oid_val bytes" Router(config-applet)# action 1.0 syslog priority errors facility EEM-FAC message "TEST MSG" |
Specifies the action to be taken when an EEM applet is triggered. In this example, the action taken is to write a message to syslog. • • • • |
Step 10 |
action label mail server server-address to to-address from from-address [cc cc-address] subject subject body body-text Router(config-applet)# action 2.0 mail server 192.168.1.10 to engineering@example.com from devtest@example.com subject "Memory failure" body "Memory exhausted; current available memory is $_snmp_oid_val bytes" |
Specifies the action of sending a short e-mail when an EEM applet is triggered. • • • • • |
Step 11 |
Add more action commands as required. |
— |
Step 12 |
end Router(config-applet)# end |
Exits applet configuration mode and returns to privileged EXEC mode. |
Troubleshooting Tips
Use the debug event manager command in privileged EXEC mode to troubleshoot EEM command operations. Use any debugging command with caution as the volume of generated output can slow or stop the router operations. We recommend that this command be used only under the supervision of a Cisco engineer.
Registering and Defining an Embedded Event Manager Policy to Run Manually
There are two ways to manually run an EEM policy. EEM usually schedules and runs policies on the basis of an event specification that is contained within the policy itself. The event none command allows EEM to identify an EEM policy that can be manually triggered. To run the policy, use either the action policy command in applet configuration mode or the event manager run command in privileged EXEC mode.
Perform this task to register an EEM policy to be run manually using the event manager run command. For an example of how to manually run a policy using the action policy command, see the "Embedded Event Manager Manual Policy Execution: Examples" section.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager applet applet-name
event manager applet applet-name
4. ![]() event none
event none
5. ![]() action label syslog [priority priority-level] msg msg-text facility string
action label syslog [priority priority-level] msg msg-text facility string
6. ![]() end
end
7. ![]() event manager run applet-name
event manager run applet-name
DETAILED STEPS
Unregistering Embedded Event Manager Policies
Perform this task to remove an EEM policy from the running configuration file. Execution of the policy is canceled.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() show event manager policy registered [description [policy-name] | detailed policy-filename [system | user] | [event-type event-name] [system | user] [time-ordered | name-ordered]]
show event manager policy registered [description [policy-name] | detailed policy-filename [system | user] | [event-type event-name] [system | user] [time-ordered | name-ordered]]
3. ![]() configure terminal
configure terminal
4. ![]() no event manager policy policy-filename
no event manager policy policy-filename
5. ![]() exit
exit
6. ![]() Repeat Step 2 to ensure that the policy has been removed.
Repeat Step 2 to ensure that the policy has been removed.
DETAILED STEPS
Examples
In the following example, the show event manager policy registered privileged EXEC command is used to display the two EEM applets that are currently registered:
Router# show event manager policy registered
No. Class Type Event Type Trap Time Registered Name
1 applet system snmp Off Fri Aug 12 17:42:52 2005 IPSLAping1
oid {1.3.6.1.4.1.9.9.42.1.2.9.1.6.4} get-type exact entry-op eq entry-val {1}
exit-op eq exit-val {2} poll-interval 90.000
action 1.0 syslog priority critical msg "Server IPecho Failed: OID=$_snmp_oid_val"
action 1.1 snmp-trap strdata "EEM detected server reachability failure to 10.1.88.9"
action 1.2 publish-event sub-system 88000101 type 1 arg1 "10.1.88.9" arg2 "IPSLAEcho"
arg3 "fail"
action 1.3 counter name _IPSLA1F op inc value 1
2 applet system snmp Off Thu Sep 15 05:57:16 2005 memory-fail
oid {1.3.6.1.4.1.9.9.48.1.1.1.6.1} get-type exact entry-op lt entry-val {5120000}
poll-interval 90
action 1.0 syslog priority critical msg Memory exhausted; current available memory is $_snmp_oid_val bytes
action 2.0 force-switchover
In the following example, the show event manager policy registered privileged EXEC command is used to show that applet IPSLAping1 has been removed after entering the no event manager policy command:
Router# show event manager policy registered
No. Class Type Event Type Trap Time Registered Name
1 applet system snmp Off Thu Sep 15 05:57:16 2005 memory-fail
oid {1.3.6.1.4.1.9.9.48.1.1.1.6.1} get-type exact entry-op lt entry-val {5120000}
poll-interval 90
action 1.0 syslog priority critical msg Memory exhausted; current available memory is $_snmp_oid_val bytes
action 2.0 force-switchover
Suspending All Embedded Event Manager Policy Execution
Perform this task to immediately suspend the execution of all EEM policies. Suspending policies, instead of unregistering them might be necessary for reasons of temporary performance or security.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() show event manager policy registered [description [policy-name] | detailed policy-filename [system | user] | [event-type event-name] [system | user] [time-ordered | name-ordered]]
show event manager policy registered [description [policy-name] | detailed policy-filename [system | user] | [event-type event-name] [system | user] [time-ordered | name-ordered]]
3. ![]() configure terminal
configure terminal
4. ![]() event manager scheduler suspend
event manager scheduler suspend
5. ![]() exit
exit
DETAILED STEPS
Configuring and Tracking a Stub Object Using Embedded Event Manager
Perform this task to create a stub object, set the state of the stub object, and configure an EEM applet to be run when the tracked object changes. Actions are specified within the EEM applet to both set and read the state of the object. This task allows EEM to define an enhanced object tracking (EOT) object that may be manipulated by other EOT clients. An EEM policy can be a trigger for any EOT object including objects defined for other EOT clients or for an object defined by EEM.
Enhanced Object Tracking
Object tracking was first introduced into the Hot Standby Router Protocol (HSRP) as a simple tracking mechanism that allowed you to track the interface line-protocol state only. Enhanced object tracking provides complete separation between the objects to be tracked and the action to be taken by a client when a tracked object changes. Thus, several clients such as EEM, VRRP, or GLBP can register their interest with the tracking process, track the same object, and each take different action when the object changes.
Each tracked object is identified by a unique number that is specified on the tracking command-line interface (CLI). Client processes use this number to track a specific object. The tracking process periodically polls the tracked objects and notes any change of value. The changes in the tracked object are communicated to interested client processes, either immediately or after a specified delay. The object values are reported as either up or down.
The EOT event detector publishes an event when the tracked object changes.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() track object-number stub-object
track object-number stub-object
4. ![]() default-state {up | down}
default-state {up | down}
5. ![]() exit
exit
6. ![]() event manager applet applet-name
event manager applet applet-name
7. ![]() event [label] track object-number [state {up | down | any}]
event [label] track object-number [state {up | down | any}]
8. ![]() action label track set object-number state {up | down}
action label track set object-number state {up | down}
9. ![]() action label track read object-number
action label track read object-number
10. ![]() end
end
11. ![]() show track [object-number [brief]]
show track [object-number [brief]]
DETAILED STEPS
Examples
In the following example, the show track privileged EXEC command is used to display information about tracked object number 2.
Router# show track 2
Track 2
Stub-object
State is Up
1 change, last change 00:00:04, by Undefined
Displaying Embedded Event Manager History Data
Perform this optional task to change the size of the history tables and to display EEM history data.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager history size {events | traps} [size]
event manager history size {events | traps} [size]
4. ![]() exit
exit
5. ![]() show event manager history events [detailed] [maximum number]
show event manager history events [detailed] [maximum number]
6. ![]() show event manager history traps {server | policy}
show event manager history traps {server | policy}
DETAILED STEPS
Step 1 ![]() enable
enable
Enables privileged EXEC mode. Enter your password if prompted.
Router> enable
Step 2 ![]() configure terminal
configure terminal
Enters global configuration mode.
Router# configure terminal
Step 3 ![]() event manager history size {events | traps} [size]
event manager history size {events | traps} [size]
Use this command to change the size of the EEM event history table or the size of the EEM SNMP trap history table. In the following example, the size of the EEM event history table is changed to 30 entries:
Router(config)# event manager history size events 30
Step 4 ![]() exit
exit
Exits global configuration mode and returns to privileged EXEC mode.
Router(config)# exit
Step 5 ![]() show event manager history events [detailed] [maximum number]
show event manager history events [detailed] [maximum number]
Use this command to display detailed information about each EEM event, for example:
Router# show event manager history events
No. Time of Event Event Type Name
1 Fri Aug13 21:42:57 2004 snmp applet: SAAping1
2 Fri Aug13 22:20:29 2004 snmp applet: SAAping1
3 Wed Aug18 21:54:48 2004 snmp applet: SAAping1
4 Wed Aug18 22:06:38 2004 snmp applet: SAAping1
5 Wed Aug18 22:30:58 2004 snmp applet: SAAping1
6 Wed Aug18 22:34:58 2004 snmp applet: SAAping1
7 Wed Aug18 22:51:18 2004 snmp applet: SAAping1
8 Wed Aug18 22:51:18 2004 application applet: CustApp1
Step 6 ![]() show event manager history traps {server | policy}
show event manager history traps {server | policy}
Use this command to display the EEM SNMP traps that have been sent either from the EEM server or from an EEM policy. In the following example, the EEM SNMP traps that were triggered from within an EEM policy are displayed.
Router# show event manager history traps policy
No. Time Trap Type Name
1 Wed Aug18 22:30:58 2004 policy EEM Policy Director
2 Wed Aug18 22:34:58 2004 policy EEM Policy Director
3 Wed Aug18 22:51:18 2004 policy EEM Policy Director
Displaying Embedded Event Manager Registered Policies
Perform this optional task to display registered EEM policies.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() show event manager policy registered [event-type event-name] [time-ordered | name-ordered]
show event manager policy registered [event-type event-name] [time-ordered | name-ordered]
DETAILED STEPS
Step 1 ![]() enable
enable
Enables privileged EXEC mode. Enter your password if prompted.
Router> enable
Step 2 ![]() show event manager policy registered [event-type event-name] [time-ordered | name-ordered]
show event manager policy registered [event-type event-name] [time-ordered | name-ordered]
Use this command with the time-ordered keyword to display information about currently registered policies sorted by time, for example:
Router# show event manager policy registered time-ordered
No. Type Event Type Time Registered Name
1 applet snmp Thu May30 05:57:16 2004 memory-fail
oid {1.3.6.1.4.1.9.9.48.1.1.1.6.1} get-type exact entry-op lt entry-val
{5120000} poll-interval 90
action 1.0 syslog priority critical msg "Memory exhausted; current available memory is $_snmp_oid_val bytes"
action 2.0 force-switchover
2 applet syslog Wed Jul16 00:05:17 2004 intf-down
pattern {.*UPDOWN.*Ethernet1/0.*}
action 1.0 cns-event msg "Interface state change: $_syslog_msg"
Use this command with the name-ordered keyword to display information about currently registered policies sorted by name, for example:
Router# show event manager policy registered name-ordered
No. Type Event Type Time Registered Name
1 applet syslog Wed Jul16 00:05:17 2004 intf-down
pattern {.*UPDOWN.*Ethernet1/0.*}
action 1.0 cns-event msg "Interface state change: $_syslog_msg"
2 applet snmp Thu May30 05:57:16 2004 memory-fail
oid {1.3.6.1.4.1.9.9.48.1.1.1.6.1} get-type exact entry-op lt entry-val
{5120000} poll-interval 90
action 1.0 syslog priority critical msg "Memory exhausted; current available memory is $_snmp_oid_val bytes"
action 2.0 force-switchover
Use this command with the event-type keyword to display information about currently registered policies for the event type specified in the event-name argument, for example:
Router# show event manager policy registered event-type syslog
No. Type Event Type Time Registered Name
1 applet syslog Wed Jul16 00:05:17 2004 intf-down
pattern {.*UPDOWN.*Ethernet1/0.*}
action 1.0 cns-event msg "Interface state change: $_syslog_msg"
Configuring Event SNMP Notification
Perform this task to configure SNMP notifications.
Prerequisites
•![]() You must be running Cisco IOS Release 12.4(20)T, 12.2(33)SXI or later release.
You must be running Cisco IOS Release 12.4(20)T, 12.2(33)SXI or later release.
•![]() SNMP event manager must be configured using the snmp-server manager command.
SNMP event manager must be configured using the snmp-server manager command.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager applet applet-name
event manager applet applet-name
4. ![]() event [tag event-tag] snmp-notification oid oid-string oid-val comparison-value op operator [maxrun maxruntime-number] [src-ip-address ip-address] [dest-ip-address ip-address] [default seconds] [direction {incoming | outgoing}] [msg-op {drop | send}]
event [tag event-tag] snmp-notification oid oid-string oid-val comparison-value op operator [maxrun maxruntime-number] [src-ip-address ip-address] [dest-ip-address ip-address] [default seconds] [direction {incoming | outgoing}] [msg-op {drop | send}]
5. ![]() exit
exit
DETAILED STEPS
Configuring Multiple Event Support
The multiple event support feature introduced in Cisco IOS Release 12.4(20)T and later releases, adds the ability to register multiple events in the EEM server. The multiple event support involves one or more event occurrences, one or more tracked object states, and a time period for the event to occur. The event parameters are specified in the CLI commands. The data structure to handle multiple events contains multiple event identifiers and correlation logic. This data is used to register multiple events in the EEM Server.
Setting the Event Configuration Parameters
The trigger command enters the trigger applet configuration mode and specifies the multiple event configuration statements for EEM applets. The trigger statement is used to relate multiple event statement using the tag argument specified in each event statement. The events are raised based on the specified parameters.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager applet applet-name
event manager applet applet-name
4. ![]() event [tag event-tag] cli pattern regular-expression sync {yes | no skip {yes | no}} [occurs num-occurrences] [period period-value] [maxrun maxruntime-number]
event [tag event-tag] cli pattern regular-expression sync {yes | no skip {yes | no}} [occurs num-occurrences] [period period-value] [maxrun maxruntime-number]
5. ![]() trigger [occurs occurs-value] [period period-value] [period-start period-start-value] [delay delay-value]
trigger [occurs occurs-value] [period period-value] [period-start period-start-value] [delay delay-value]
6. ![]() correlate {event event-tag | track object-number} [boolean-operator { event event-tag | track tracked-object} ...]
correlate {event event-tag | track object-number} [boolean-operator { event event-tag | track tracked-object} ...]
7. ![]() attribute tag event-tag [occurs occurs-value]
attribute tag event-tag [occurs occurs-value]
8. ![]() action label cli command cli-string
action label cli command cli-string
DETAILED STEPS
Examples
In the following example, applet is run if the show bgp all CLI command and any syslog message that contains the string "COUNT" occurred within a period 60 seconds.
event manager applet delay_50
event tag 1.0 cli pattern "show bgp all" sync yes occurs 32 period 60 maxrun 60
event tag 2.0 syslog pattern "COUNT"
trigger occurs 1 delay 50
correlate event 1.0 or event 2.0
attribute tag 1.0 occurs 1
attribute tag 2.0 occurs 1
action 1.0 cli command "show memory"
action 2.0 cli command "enable"
action 3.0 cli command "config terminal"
action 4.0 cli command " ip route 192.0.2.0 255.255.255.224 192.0.2.12"
action 91.0 cli command "exit"
action 99.0 cli command "show ip route | incl 192.0.2.5"
Configuring EEM Class-Based Scheduling
To schedule Embedded Event Manager (EEM) policies and set policy scheduling options, perform this task. In this task, two EEM execution threads are created to run applets assigned to the default class.
The EEM policies will be assigned a class using the class keyword when they are registered. EEM policies registered without a class will be assigned to the default class. Threads that have default class, will service the default class when the thread is available for work. Threads that are assigned specific class letters will service any policy with a matching class letter when the thread is available for work.
If there is no EEM execution thread available to run the policy in the specified class and a scheduler rule for the class is configured, the policy will wait until a thread of that class is available for execution. Synchronous policies that are triggered from the same input event should be scheduled in the same execution thread.
Prerequisites
To use this feature, you must be running Cisco IOS Release 12.4(22)T or a later release.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager scheduler {applet | axp | call-home} thread class class-options number thread-number
event manager scheduler {applet | axp | call-home} thread class class-options number thread-number
4. ![]() exit
exit
DETAILED STEPS
Holding a Scheduled EEM Policy Event or Event Queue
To hold a scheduled EEM policy event or event queue in the EEM scheduler, perform this task. In this task, all pending EEM policies are displayed. A policy identified using a job ID of 2 is held in the EEM scheduler, and the final step shows that the policy with a job ID of 2 has changed status from pending to held.
Prerequisites
To use this feature, you must be running Cisco IOS Release 12.4(22)T or a later release.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() show event manager policy pending [queue-type {applet | call-home | axp | script} class class-options | detailed]
show event manager policy pending [queue-type {applet | call-home | axp | script} class class-options | detailed]
3. ![]() event manager scheduler hold {policy job-id | queue-type {applet | call-home | axp | script} class class-options | all} [processor {rp_primary | rp_standby}]
event manager scheduler hold {policy job-id | queue-type {applet | call-home | axp | script} class class-options | all} [processor {rp_primary | rp_standby}]
4. ![]() show event manager policy pending [queue-type {applet | call-home | axp | script} class class-options | detailed]
show event manager policy pending [queue-type {applet | call-home | axp | script} class class-options | detailed]
DETAILED STEPS
|
|
|
|
|---|---|---|
Step 1 |
enable Router> enable |
Enables privileged EXEC mode. • |
Step 2 |
show event manager policy pending [queue-type {applet | call-home | axp | script} class class-options | detailed] Router# show event manager policy pending |
Displays the pending EEM policies. |
Step 3 |
event manager scheduler hold {all | policy job-id | queue-type {applet | call-home | axp | script} class class-options} [processor {rp_primary | rp_standby}] Router# event manager scheduler hold policy 2 |
Holds a scheduled EEM policy event or event queue in the EEM scheduler. • |
Step 4 |
show event manager policy pending [queue-type {applet | call-home | axp | script} class class-options | detailed] Router# show event manager policy pending |
Displays the status of EEM policy put on hold in Step 3 as held, along with other pending policies. |
Examples
The following example shows how to view all pending EEM policies and to hold the EEM policy with a job ID of 2.
Router# show event manager policy pending
no. job id status time of event event type name
1 1 pend Thu Sep 7 02:54:04 2006 syslog applet: one
2 2 pend Thu Sep 7 02:54:04 2006 syslog applet: two
3 3 pend Thu Sep 7 02:54:04 2006 syslog applet: three
Router# event manager scheduler hold policy 2
Router# show event manager policy pending
no. job id status time of event event type name
1 1 pend Thu Sep 7 02:54:04 2006 syslog applet: one
2 2 held Thu Sep 7 02:54:04 2006 syslog applet: two
3 3 pend Thu Sep 7 02:54:04 2006 syslog applet: three
Resuming Execution of EEM Policy Events or Event Queues
To resume the execution of specified EEM policies, perform this task. In this task, the policy that was put on hold in the "Holding a Scheduled EEM Policy Event or Event Queue" section is now allowed to resume execution.
Prerequisites
To use this feature, you must be running Cisco IOS Release 12.4(22)T or a later release.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() show event manager policy pending
show event manager policy pending
3. ![]() event manager scheduler release {all | policy policy-id | queue-type {applet | call-home | axp | script}} class class-options [processor {rp_primary | rp_standby}]
event manager scheduler release {all | policy policy-id | queue-type {applet | call-home | axp | script}} class class-options [processor {rp_primary | rp_standby}]
4. ![]() show event manager policy pending
show event manager policy pending
DETAILED STEPS
|
|
|
|
|---|---|---|
Step 1 |
enable Router> enable |
Enables privileged EXEC mode. • |
Step 2 |
show event manager policy pending Router# show event manager policy pending |
Displays the pending and held EEM policies. Note |
Step 3 |
event manager scheduler release {all | policy policy-id | queue-type {applet | call-home | axp | script}} class class-options [processor {rp_primary | rp_standby}] Router# event manager scheduler release policy 2 |
Resumes execution of specified EEM policies. • |
Step 4 |
show event manager policy pending Router# show event manager policy pending |
Displays the status of the EEM policy resumed in Step 3 as pending, along with other pending policies. Note |
Examples
The following example shows how to view all pending EEM policies, to specify the policy that will resume execution, and to see that the policy is now back in a pending status.
Router# show event manager policy pending
no. job id status time of event event type name
1 1 pend Thu Sep 7 02:54:04 2006 syslog applet: one
2 2 held Thu Sep 7 02:54:04 2006 syslog applet: two
3 3 pend Thu Sep 7 02:54:04 2006 syslog applet: three
Rotuer# event manager scheduler release policy 2
Rotuer# show event manager policy pending
no. job id status time of event event type name
1 1 pend Thu Sep 7 02:54:04 2006 syslog applet: one
2 2 pend Thu Sep 7 02:54:04 2006 syslog applet: two
3 3 pend Thu Sep 7 02:54:04 2006 syslog applet: three
Clearing Pending EEM Policy Events or Event Queues
Perform this task to clear EEM policies that are executing or pending execution. In this task, the EEM policy with a job ID of 2 is cleared from the pending queue. The show event manager policy pending command is used to display the policies that are pending before and after the policy is cleared.
Prerequisites
To use this feature, you must be running Cisco IOS Release 12.4(22)T or a later release.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() show event manager policy pending
show event manager policy pending
3. ![]() event manager scheduler clear {all | policy policy-id | queue-type {applet | call-home | axp | script}} class class-options [processor {rp_primary | rp_standby}
event manager scheduler clear {all | policy policy-id | queue-type {applet | call-home | axp | script}} class class-options [processor {rp_primary | rp_standby}
4. ![]() show event manager policy pending
show event manager policy pending
DETAILED STEPS
|
|
|
|
|---|---|---|
Step 1 |
enable Router> enable |
Enables privileged EXEC mode. • |
Step 2 |
show event manager policy pending Router# show event manager policy pending |
Displays the pending EEM policies. Note |
Step 3 |
event manager scheduler clear {all | policy job-id | queue-type {applet | call-home | axp | script} class class-options} [processor {rp_primary | rp_standby}] Router# event manager scheduler clear policy 2 |
Clears EEM policies that are executing or pending execution. • |
Step 4 |
show event manager policy pending Router# show event manager policy pending |
Displays all the pending EEM policies except the policy cleared in Step 3. Note |
Examples
The following example shows how to clear the EEM policy with a job ID of 2 that was pending execution. The show commands are used to display the policies that are pending before and after the policy is cleared.
Router# show event manager policy pending
no. job id status time of event event type name
1 1 pend Thu Sep 7 02:54:04 2006 syslog applet: one
2 2 pend Thu Sep 7 02:54:04 2006 syslog applet: two
3 3 pend Thu Sep 7 02:54:04 2006 syslog applet: three
Router# event manager scheduler clear policy 2
Router# show event manager policy pending
no. job id status time of event event type name
1 1 pend Thu Sep 7 02:54:04 2006 syslog applet: one
3 3 pend Thu Sep 7 02:54:04 2006 syslog applet: three
Modifying the Scheduling Parameters of EEM Policy Events or Event Queues
To modify the scheduling parameters of the EEM policies, perform this task. The show event manager policy pending command displays policies that are assigned to the B or default class. All the currently pending policies are then changed to class A. After the configuration modification, the show event manager policy pending command shows all policies assigned as class A.
Prerequisites
To use this feature, you must be running Cisco IOS Release 12.4(22)T or a later release.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() show event manager policy pending
show event manager policy pending
3. ![]() event manager scheduler modify {all | policy job-id | queue-type {applet | call-home | axp | script} | class class-options} [queue-priority {high | last | low | normal}] [processor {rp_primary | rp_standby}]
event manager scheduler modify {all | policy job-id | queue-type {applet | call-home | axp | script} | class class-options} [queue-priority {high | last | low | normal}] [processor {rp_primary | rp_standby}]
4. ![]() show event manager policy pending
show event manager policy pending
DETAILED STEPS
|
|
|
|
|---|---|---|
Step 1 |
enable Router> enable |
Enables privileged EXEC mode. • |
Step 2 |
show event manager policy pending Router# show event manager policy pending |
Displays the pending EEM policies. Note |
Step 3 |
event manager scheduler modify {all | policy job-id | queue-type {applet | call-home | axp | script} | class class-options} [queue-priority {high | last | low | normal}] [processor {rp_primary | rp_standby}] Router# event manager scheduler modify all class A |
Modifies the scheduling parameters of the EEM policies. • |
Step 4 |
show event manager policy pending Router# show event manager policy pending |
Displays the EEM policies modified in Step 3 along with other pending policies. Note |
Examples
The following example shows how to modify the scheduling parameters of the EEM policies. In this example, the show event manager policy pending command displays policies that are assigned to the B or default class. All the currently pending policies are then changed to class A. After the configuration modification, the show event manager policy pending command verifies that all policies are now assigned as class A.
Router# show event manager policy pending
no. class status time of event event type name
1 default pend Thu Sep 7 02:54:04 2006 syslog applet: one
2 default pend Thu Sep 7 02:54:04 2006 syslog applet: two
3 B pend Thu Sep 7 02:54:04 2006 syslog applet: three
Router# event manager scheduler modify all class A
Router# show event manager policy pending
no. class status time of event event type name
1 A pend Thu Sep 7 02:54:04 2006 syslog applet: one
2 A pend Thu Sep 7 02:54:04 2006 syslog applet: two
3 A pend Thu Sep 7 02:54:04 2006 syslog applet: three
Verifying Class-Based Scheduled Activities of EEM Policies
To verify the scheduled activities of the EEM policies, use the show event manager scheduler command.
Prerequisites
To use this feature, you must be running Cisco IOS Release 12.4(22)T or a later release.
SUMMARY STEPS
1. ![]() show event manager scheduler thread [queue-type {applet | call-home | axp | script} class class-options | detailed]
show event manager scheduler thread [queue-type {applet | call-home | axp | script} class class-options | detailed]
DETAILED STEPS
Step 1 ![]() show event manager scheduler thread [queue-type {applet | call-home | axp | script} class class-options | detailed]
show event manager scheduler thread [queue-type {applet | call-home | axp | script} class class-options | detailed]
This command displays all the EEM execution threads from the scheduler perspective and the details of the running policies. This command includes detailed and queue-type optional keywords. The following is sample output from this command:
Router# show event manager scheduler thread
1 Script threads service class default
total: 1 running: 1 idle: 0
2 Script threads service class range A-D
total: 3 running: 0 idle: 3
3 Applet threads service class default
total: 32 running: 0 idle: 32
4 Applet threads service class W X
total: 5 running: 0 idle: 5
To display the details of the running policies using the scheduler threads use the detailed keyword. The following is sample output for this keyword:
Router# show event manager scheduler thread detailed
1 Script threads service class default
total: 5 running: 5 idle: 0
1 job id: 12341, pid: 101, name: loop.tcl
2 job id: 12352, pid: 52, name: loop.tcl
3 job id: 12363, pid: 55, name: loop.tcl
4 job id: 12395, pid: 53, name: loop.tcl
5 job id: 12588, pid: 102, name: loop.tcl
2 Applet threads service class default
total: 32 running: 5 idle: 27
1 job id: 15585, pid: 104, name: WDOG_SYSLG_CNTR_TRACK_INTF_APPL
2 job id: 15586, pid: 105, name: WDOG_SYSLG_CNTR_TRACK_INTF_APPL
3 job id: 15587, pid: 106, name: WDOG_SYSLG_CNTR_TRACK_INTF_APPL
4 job id: 15589, pid: 107, name: WDOG_SYSLG_CNTR_TRACK_INTF_APPL
5 job id: 15590, pid: 80, name: WDOG_SYSLG_CNTR_TRACK_INTF_APPL
To display the scheduler threads of a queue-type use the queue-type keyword. The following are the sample output for this keyword:
Router# show event manager sched thread queue-type applet
1 Applet threads service class default
total: 32 running: 7 idle: 25
Router# show event manager sched thread queue-type applet detailed
1 Applet threads service class default
total: 32 running: 5 idle: 27
1 job id: 15700, pid: 103, name: WDOG_SYSLG_CNTR_TRACK_INTF_APPL
2 job id: 15701, pid: 104, name: WDOG_SYSLG_CNTR_TRACK_INTF_APPL
3 job id: 15703, pid: 106, name: WDOG_SYSLG_CNTR_TRACK_INTF_APPL
4 job id: 15704, pid: 107, name: WDOG_SYSLG_CNTR_TRACK_INTF_APPL
5 job id: 15706, pid: 55, name: WDOG_SYSLG_CNTR_TRACK_INTF_APPL
Verifying Class-Based Active EEM Policies
To verify the active or the running EEM policies, use the show event manager policy active command.
Prerequisites
To use this feature, you must be running Cisco IOS Release 12.4(22)T or a later release.
SUMMARY STEPS
1. ![]() show event manager policy active [queue-type {applet | call-home | axp | script} class class-options | detailed]
show event manager policy active [queue-type {applet | call-home | axp | script} class class-options | detailed]
DETAILED STEPS
Step 1 ![]() show event manager policy active [queue-type {applet | call-home | axp | script} class class-options | detailed]
show event manager policy active [queue-type {applet | call-home | axp | script} class class-options | detailed]
This command displays only the running EEM policies. This command includes class, detailed and queue-type optional keywords. The following is sample output from this command:
Router# show event manager policy active
no. job id p s status time of event event type name
1 12598 N A running Mon Oct29 20:49:37 2007 timer watchdog loop.tcl
2 12609 N A running Mon Oct29 20:49:42 2007 timer watchdog loop.tcl
3 12620 N A running Mon Oct29 20:49:46 2007 timer watchdog loop.tcl
4 12650 N A running Mon Oct29 20:49:59 2007 timer watchdog loop.tcl
5 12842 N A running Mon Oct29 20:51:13 2007 timer watchdog loop.tcl
default class - 6 applet events
no. job id p s status time of event event type name
1 15852 N A running Mon Oct29 21:11:09 2007 counter WDOG_SYSLG_CNTR_TRACK_INTF_APPL
2 15853 N A running Mon Oct29 21:11:09 2007 counter WDOG_SYSLG_CNTR_TRACK_INTF_APPL
3 15854 N A running Mon Oct29 21:11:10 2007 counter WDOG_SYSLG_CNTR_TRACK_INTF_APPL
4 15855 N A running Mon Oct29 21:11:10 2007 timer watchdog WDOG_SYSLG_CNTR_TRACK_INTF_APPL
5 15856 N A running Mon Oct29 21:11:11 2007 counter WDOG_SYSLG_CNTR_TRACK_INTF_APPL
6 15858 N A running Mon Oct29 21:11:11 2007 counter WDOG_SYSLG_CNTR_TRACK_INTF_APPL
Verifying Pending EEM Policies
To verify the EEM policies that are pending for execution, use the show event manager policy pending command. In Cisco IOS Release 12.4(22)T, optional keywords were added to this command to specify EEM class-based scheduling options.
Prerequisites
To use this feature, you must be running Cisco IOS Release 12.4(22)T or later release.
SUMMARY STEPS
1. ![]() show event manager policy pending [queue-type {applet | call-home | axp | script} class class-options | detailed]
show event manager policy pending [queue-type {applet | call-home | axp | script} class class-options | detailed]
DETAILED STEPS
Step 1 ![]() show event manager policy pending [queue-type {applet | call-home | axp | script} class class-options | detailed]
show event manager policy pending [queue-type {applet | call-home | axp | script} class class-options | detailed]
This command displays only the pending policies. This command includes class, detailed and queue-type optional keywords. The following is sample output from this command:
Router# show event manager policy pending
no. job id p s status time of event event type name
1 12851 N A pend Mon Oct29 20:51:18 2007 timer watchdog loop.tcl
2 12868 N A pend Mon Oct29 20:51:24 2007 timer watchdog loop.tcl
3 12873 N A pend Mon Oct29 20:51:27 2007 timer watchdog loop.tcl
4 12907 N A pend Mon Oct29 20:51:41 2007 timer watchdog loop.tcl
5 13100 N A pend Mon Oct29 20:52:55 2007 timer watchdog loop.tcl
Configring EEM Applet (Interactive CLI) Support
The synchronous applets are enhanced to support interaction with the local console (tty) in Cisco IOS Release 12.4(22)T. Two new commands action gets and action puts are introduced to allow users to enter and display input directly on the console. The output for synchronous applets will bypass the system logger. The local console will be opened by the applets and serviced by the corresponding synchronous Event Detector pty. Synchronous output will be directed to the opened console.
For details on configuring EEM applet interactive CLI support, see the "Reading and Writing Input from the Active Console for Synchronous EEM Applets" section.
Reading and Writing Input from the Active Console for Synchronous EEM Applets
The synchronous applets are enhanced to support interaction with the local console (tty) in Cisco IOS Release 12.4(22)T.
Use the following tasks to implement EEM applet interactive CLI support:
•![]() Reading Input from the Active Console
Reading Input from the Active Console
•![]() Writing Input to the Active Console
Writing Input to the Active Console
Reading Input from the Active Console
When a synchronous policy is triggered, the related console is stored in the publish information specification. The policy director will query this information in an event_reqinfo call, and store the given console information for use by the action gets command.
The action gets command reads a line of the input from the active console and stores the input in the variable. The trailing new line will not be returned.
Prerequisites
To use this feature, you must be running Cisco IOS Release 12.4(22)T, or later releases.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager applet applet-name
event manager applet applet-name
4. ![]() event none
event none
5. ![]() action label gets variable
action label gets variable
6. ![]() action label syslog [priority priority-level] msg msg-text
action label syslog [priority priority-level] msg msg-text
7. ![]() exit
exit
DETAILED STEPS
|
|
|
|
|---|---|---|
Step 1 |
enable Router> enable |
Enables privileged EXEC mode. • |
Step 2 |
configure terminal Router# configure terminal |
Enters global configuration mode. |
Step 3 |
event manager applet applet-name Router(config)# event manager applet action |
Registers the applet with the EEM and enters applet configuration mode. |
Step 4 |
event none Router(config-applet)# event none |
Specifies that an EEM policy is to be registered with the EEM and can be run manually. |
Step 5 |
action label gets variable Router(config-applet)# action label2 gets input |
Gets input from the local console in a synchronous applet and stores the value in the given variable when an EEM applet is triggered. |
Step 6 |
action label syslog [priority priority-level] Router(config-applet)# action label3 syslog msg "Input entered was \"$input\"" |
Specifies the action to be taken when an EEM applet is triggered. • |
Step 7 |
exit Router(config-applet)# exit |
Exits applet configuration mode and returns to privileged EXEC mode. |
Example
The following example shows how to get the input from the local tty in a synchronous applet and store the value
Router(config)# event manager applet action
Router(config-applet)# event none
Router(config-applet)# action label2 gets input
Router(config-applet)# action label3 syslog msg "Input entered was \"$input\""
Writing Input to the Active Console
When a synchronous policy is triggered, the related console is stored in the publish information specification. The policy director will query this information in an event_reqinfo call, and store the given console information for use by the action puts command.
The action puts command will write the string to the active console. A new line will be displayed unless the nonewline keyword is specified. The output from the action puts command for a synchronous applet is displayed directly to the console, bypassing the system logger. The output of the action puts command for an asynchronous applet is directed to the system logger.
Prerequisites
To use this feature, you must be running Cisco IOS Release 12.4(22)T, or a later release.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager applet applet-name
event manager applet applet-name
4. ![]() event none
event none
5. ![]() action label regexp string-pattern string-input [string-match [string-submatch1] [string-submatch2] [string-submatch3]]
action label regexp string-pattern string-input [string-match [string-submatch1] [string-submatch2] [string-submatch3]]
6. ![]() action label puts [nonewline] string
action label puts [nonewline] string
7. ![]() exit
exit
8. ![]() event manager run applet-name
event manager run applet-name
DETAILED STEPS
|
|
|
|
|---|---|---|
Step 1 |
enable Router> enable |
Enables privileged EXEC mode. • |
Step 2 |
configure terminal Router# configure terminal |
Enters global configuration mode. |
Step 3 |
event manager applet applet-name Router(config)# event manager applet action |
Registers the applet with the EEM and enters applet configuration mode. |
Step 4 |
event none Router(config-applet)# event none |
Specifies that an EEM policy is to be registered with the EEM and can be run manually. |
Step 5 |
action label regexp string-pattern string-input [string-match [string-submatch1] [string-submatch2] [string-submatch3]] Router(config-applet)# action 1 regexp "(.*) (.*) (.*)" "one two three" _match _sub1 |
Specifies the action to match the regular expression pattern on an input string when an EEM applet is triggered. |
Step 6 |
action label puts [nonewline] string Router(config-applet)# action 2 puts "match is $_match" |
Specifies the action of printing data directly to the local console when an EEM applet is triggered. • |
Step 7 |
exit Router(config-applet)# exit |
Exits applet configuration mode and returns to privileged EXEC mode. |
Step 8 |
event manager run applet-name Router# event manager run action |
Manually runs a registered EEM policy. • |
Example
The following example shows how the action puts command prints data directly to the local console:
Router(config-applet)# event manager applet puts
Router(config-applet)# event none
Router(config-applet)# action 1 regexp "(.*) (.*) (.*)" "one two three" _match _sub1
Router(config-applet)# action 2 puts "match is $_match"
Router(config-applet)# action 3 puts "submatch 1 is $_sub1"
Router# event manager run puts
match is one two three
submatch 1 is one
Configuring SNMP Library Extensions
To configure SNMP Library Extensions for an EEM policy, you must be familiar with the following concepts:
•![]() SNMP Traps and Inform Requests
SNMP Traps and Inform Requests
Prerequisites
To use this feature, you must be running Cisco IOS Release 12.4(22)T or a later release.
SNMP Get and Set Operations
With the Cisco IOS Release 12.4(22)T, the SNMP Library Extensions feature extends the EEM applet action info and Tcl sys_reqinfo_snmp commands to include functionality for SNMP get-one, get-next, getid and set-any operations.
SNMP Get Operation
The SNMP event manager performs the SNMP get operation to retrieve one or more variables for the managed objects. Using the action info type snmp oid get-type and action info type snmp getid commands, you can configure the SNMP event manager to send an SNMP get request by specifying the variables to retrieve, and the IP address of the agent.
For example, if you want to retrieve the variable with the OID value of 1.3.6.1.2.1.1.1, you should specify the variable value, that is 1.3.6.1.2.1.1.1. If the specified values do not match, a trap will be generated and an error message will be written to the syslog history.
The action info type snmp oid get-type command specifies the type of the get operation to be performed. To retrieve the exact variable, the get operation type should be specified as exact. To retrieve a lexicographical successor of the specified OID value, the get operation type should be set to next.
Table 3 shows the built-in variables, in which the values retrieved from SNMP get operation are stored.
GetID Operation
The action info type snmp getid command retrieves the following variables from the SNMP entity:
•![]() sysDescr.0
sysDescr.0
•![]() sysObjectID.0
sysObjectID.0
•![]() sysUpTime.0
sysUpTime.0
•![]() sysContact.0
sysContact.0
•![]() sysName.0
sysName.0
•![]() sysLocation.0
sysLocation.0
Table 4 shows the built-in variables, in which the values retrieved from the SNMP getID operation are stored.
The get operation requests can be sent to both local and remote hosts.
SNMP Set Operation
All SNMP variables are assigned a default value in the MIB view. The SNMP event manager can modify the value of these MIB variables through set operation. The set operation can be performed only on the system that allows read-write access.
To perform a set operation, you must specify the type of the variable and the value associated with it.
Table 5 shows the valid OID types and values for each OID type.
The set operation can carried out on both local and remote hosts.
SNMP Traps and Inform Requests
Traps are SNMP notifications that alert the SNMP manager or the NMS to a network condition.
SNMP inform requests refer to the SNMP notifications that alert the SNMP manager to a network condition and request for confirmation of receipt from the SNMP manager.
An SNMP event occurs when SNMP MIB object ID values are sampled, or when the SNMP counter crosses a defined threshold. If the notifications are enabled and configured for such events, the SNMP traps or inform messages generated. An SNMP notification event is triggered when an SNMP trap or inform message is received by the event manager server.
To send an SNMP trap or inform message when an Embedded Event Manager (EEM) applet is triggered, the action info type snmp trap and action info type snmp inform commands are used. The CISCO-EMBEDDED-EVENT-MGR-MIB.my is used to define the trap and inform messages.
How to Configure SNMP Library Extensions
This section contains the following tasks:
•![]() Configuring EEM Applet for SNMP Get and Set Operations
Configuring EEM Applet for SNMP Get and Set Operations
•![]() Configuring EEM Applet for SNMP OID Notifications
Configuring EEM Applet for SNMP OID Notifications
Configuring EEM Applet for SNMP Get and Set Operations
While registering a policy with the event manager server, the actions associated with an SNMP event can be configured.
Perform this task to configure EEM applet for SNMP set and get operations.
Prerequisites
•![]() You must be running Cisco IOS Release 12.4(22)T or a later release.
You must be running Cisco IOS Release 12.4(22)T or a later release.
•![]() SNMP event manager must be configured using the snmp-server manager command.
SNMP event manager must be configured using the snmp-server manager command.
•![]() The SNMP community string should be set by using the snmp-server community command to enable access to the SNMP entity.
The SNMP community string should be set by using the snmp-server community command to enable access to the SNMP entity.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager applet applet-name
event manager applet applet-name
4. ![]() event snmp oid oid-value get-type {exact | next} entry-op operator entry-val entry-value [exit-comb {or | and}] [exit-op operator] [exit-val exit-value] [exit-time exit-time-value] poll-interval poll-int-value
event snmp oid oid-value get-type {exact | next} entry-op operator entry-val entry-value [exit-comb {or | and}] [exit-op operator] [exit-val exit-value] [exit-time exit-time-value] poll-interval poll-int-value
5. ![]() action label info type snmp oid oid-value get-type {exact | next} [community community-string] [ipaddr ip-address]
action label info type snmp oid oid-value get-type {exact | next} [community community-string] [ipaddr ip-address]
6. ![]() action label info type snmp oid oid-value set-type oid-type oid-type-value community community-string [ipaddr ip-address]
action label info type snmp oid oid-value set-type oid-type oid-type-value community community-string [ipaddr ip-address]
7. ![]() action label info type snmp getid oid-value [community community-string] [ipaddr ip-address]
action label info type snmp getid oid-value [community community-string] [ipaddr ip-address]
8. ![]() exit
exit
DETAILED STEPS
Configuring EEM Applet for SNMP OID Notifications
Perform this task to configure SNMP notifications.
Prerequisites
•![]() You must be running Cisco IOS Release 12.4(22)T or later release.
You must be running Cisco IOS Release 12.4(22)T or later release.
•![]() SNMP event manager must be configured using the snmp-server manager command and SNMP agents must be configured to send and receive SNMP traps generated for an EEM policy.
SNMP event manager must be configured using the snmp-server manager command and SNMP agents must be configured to send and receive SNMP traps generated for an EEM policy.
•![]() SNMP traps and informs must be enabled by using the snmp-server enable traps event-manager and snmp-server enable traps commands, to allow traps and inform requests to be sent from the Cisco IOS device to the event manager server.
SNMP traps and informs must be enabled by using the snmp-server enable traps event-manager and snmp-server enable traps commands, to allow traps and inform requests to be sent from the Cisco IOS device to the event manager server.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager applet applet-name
event manager applet applet-name
4. ![]() event snmp oid oid-value get-type {exact | next} entry-op operator entry-val entry-value [exit-comb {or | and}] [exit-op operator] [exit-val exit-value] [exit-time exit-time-value] poll-interval poll-int-value
event snmp oid oid-value get-type {exact | next} entry-op operator entry-val entry-value [exit-comb {or | and}] [exit-op operator] [exit-val exit-value] [exit-time exit-time-value] poll-interval poll-int-value
5. ![]() action label info type snmp var variable-name oid oid-value oid-type oid-type-value
action label info type snmp var variable-name oid oid-value oid-type oid-type-value
6. ![]() action label info type snmp trap enterprise-oid enterprise-oid-value generic-trapnum generic-trap-number specific-trapnum specific-trap-number trap-oid trap-oid-value trap-var trap-variable
action label info type snmp trap enterprise-oid enterprise-oid-value generic-trapnum generic-trap-number specific-trapnum specific-trap-number trap-oid trap-oid-value trap-var trap-variable
7. ![]() action label info type snmp inform trap-oid trap-oid-value trap-var trap-variable community community-string ipaddr ip-address
action label info type snmp inform trap-oid trap-oid-value trap-var trap-variable community community-string ipaddr ip-address
8. ![]() exit
exit
DETAILED STEPS
Configuring Variable Logic for EEM Applets
The Variable Logic for EEM Applets feature introduced in Cisco IOS Release 12.4(22)T and later releases, adds the ability to apply conditional logic within EEM applets. Before variable logic is introduced, applets have a linear structure where each action is executed in the order in which they are configured when the event is triggered. Conditional logic introduces a control structure that can change the flow of actions within applets depending on conditional expressions. Each control structure can contain a list of applet actions including looping and if/else actions which determine if the structure is executed or not.
The information in applet configuration mode is presented as background to set the context for the action commands.
To provide a consistent user interface between the Tool Command Language (Tcl) and the applet (CLI) based EEM policies, the following criteria are followed:
•![]() Event specification criteria are written in Tcl in the Tcl based implementation.
Event specification criteria are written in Tcl in the Tcl based implementation.
•![]() Event specification data is written using the CLI applet submode configuration statements in the applet-based implementation.
Event specification data is written using the CLI applet submode configuration statements in the applet-based implementation.
Applet configuration mode is entered using the event manager applet command. In applet configuration mode the config prompt changes to (config-applet)#. In applet configuration mode two types of config statements are supported:
•![]() event - used to specify the event criteria to cause this applet to run.
event - used to specify the event criteria to cause this applet to run.
•![]() action - used to specify a built-in action to perform.
action - used to specify a built-in action to perform.
Multiple action applet config commands are allowed within an applet configuration. If no action applet config command is present, a warning is displayed, upon exit, stating no statements are associated with this applet. When no statements are associated with this applet, events get triggered but no action is taken. If no commands are specified in applet configuration mode, the applet will be removed upon exit. The exit applet config command is used to exit from applet configuration mode.
Prerequisites
To use this feature, you must be running Cisco IOS Release 12.4(22)T or a later release.
Configuring Variable Logic for EEM Applets
EEM 3.0 adds new applet action commands to permit simple variable logic within applets.
To configure the variable logic using action commands perform the followng tasks.
•![]() Specifying a Loop of Conditional Blocks
Specifying a Loop of Conditional Blocks
•![]() Specifying if else Conditional Blocks
Specifying if else Conditional Blocks
•![]() Specifying foreach Iterating Statements
Specifying foreach Iterating Statements
•![]() Incrementing the Values of Variables
Incrementing the Values of Variables
Specifying a Loop of Conditional Blocks
To specify a loop of a conditional block when an EEM applet is triggered, perform this task. In this task, a conditional loop is set to check if the value of the variable is less than 10. If the value of the variable is less than 10, then the message `i is $_i' is written to the syslog.

Note ![]() Effective with Cisco IOS Release 12.4(22)T, the set (EEM) command is replaced by the action set command. See the action label set command for more information. If the set (EEM) command is entered in 12.4(22)T and later releases, the IOS parser translates the set command to the action label set command.
Effective with Cisco IOS Release 12.4(22)T, the set (EEM) command is replaced by the action set command. See the action label set command for more information. If the set (EEM) command is entered in 12.4(22)T and later releases, the IOS parser translates the set command to the action label set command.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager applet applet-name
event manager applet applet-name
4. ![]() action label set
action label set
5. ![]() action label while string_op1 operator string_op2
action label while string_op1 operator string_op2
6. ![]() Add any action as required.
Add any action as required.
7. ![]() action label end
action label end
DETAILED STEPS
Specifying if else Conditional Blocks
To specify the beginning of an if conditional statement followed by an else conditional statement, perform this task. The if or else conditional statements can be used in conjunction with each other or separately. In this task, the value of a variable is set to 5. An if conditional block is then specified to check if the value of the variable is less than 10. Provided the if conditional block is satisfied, an action command to output the message `x is less than 10' is specified.
Following the if conditional block, an else conditional block is specified. Provided the if conditional block is not satisfied, an action command to output the message `x is greater than 10' is specified.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager applet applet-name
event manager applet applet-name
4. ![]() action label set variable-name variable-value
action label set variable-name variable-value
5. ![]() action label if [stringop1] {eq | gt | ge | lt | le | ne} [stringop2]
action label if [stringop1] {eq | gt | ge | lt | le | ne} [stringop2]
6. ![]() Add any action as required.
Add any action as required.
7. ![]() action label else
action label else
8. ![]() Add any action as required.
Add any action as required.
9. ![]() action label end
action label end
DETAILED STEPS
Specifying foreach Iterating Statements
To specify a conditional statement that iterates over an input string using the delimiter as a tokenizing pattern, perform this task. The foreach iteration statement is used to iterate through a collection to get the desired information. The delimiter is a regular expression pattern string. The token found in each iteration is assigned to the given iterator variable. All arithmetic calculations are performed as long integers with out any checks for overflow. In this task, the value of the variable x is set to 5. An iteration statement is set to run through the input string red, blue, green, orange. For every element in the input string, a corresponding message is displayed on the screen.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager applet applet-name
event manager applet applet-name
4. ![]() action label foreach [string-iterator] [string-input] [string-delimiter]
action label foreach [string-iterator] [string-input] [string-delimiter]
5. ![]() Specify any action command.
Specify any action command.
6. ![]() action label end
action label end
DETAILED STEPS
Using Regular Expressions
To match a regular expression pattern with an input string, perform this task. Using regular expressions, you can specify the rules for a set of possible strings to be matched.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager applet applet-name
event manager applet applet-name
4. ![]() action label regexp string-pattern string-input [string-match [string-submatch1] [string-submatch2] [string-submatch3]]
action label regexp string-pattern string-input [string-match [string-submatch1] [string-submatch2] [string-submatch3]]
DETAILED STEPS
Incrementing the Values of Variables
To increment the value of variables, perform this task. In this task, the value of a variable is set to 20 and then the value is incremented by 12.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager applet applet-name
event manager applet applet-name
4. ![]() action label set
action label set
5. ![]() action label increment variable-name long-integer
action label increment variable-name long-integer
DETAILED STEPS
Configuring Event SNMP Object
Perform this task to register the Simple Network Management Protocol (SNMP) object event for an Embedded Event Manager (EEM) applet that is run by sampling SNMP object.
Prerequisites
To use this feature, you must be running Cisco IOS Release 15.0(1)M or a later release.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager applet applet-name
event manager applet applet-name
4. ![]() event snmp-object oid oid-value type value sync {yes | no} skip {yes | no} istable {yes | no} [default seconds] [maxrun maxruntime-number]
event snmp-object oid oid-value type value sync {yes | no} skip {yes | no} istable {yes | no} [default seconds] [maxrun maxruntime-number]
5. ![]() exit
exit
DETAILED STEPS
Disabling AAA Authorization
Perform this task to allow EEM policies to bypass AAA authorization when triggered.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager applet applet-name [authorization bypass] [class class-options] [trap]
event manager applet applet-name [authorization bypass] [class class-options] [trap]
4. ![]() exit
exit
DETAILED STEPS
Configuring Description of an Embedded Event Manager Applet
Perform this task to describe an EEM applet. The description of an applet can be added in any order, before or after any other applet configuration. Configuring a new description for an applet that already has a description overwrites the current description. An applet description is optional.
Perform this task to configure a new description for an applet.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() event manager applet applet-name
event manager applet applet-name
4. ![]() description line
description line
5. ![]() event syslog pattern regular-expression
event syslog pattern regular-expression
6. ![]() action label syslog msg msg-text
action label syslog msg msg-text
7. ![]() end
end
DETAILED STEPS
|
|
|
|
|---|---|---|
Step 7 |
end Router(config-applet)# end |
Exits applet configuration mode and returns to privileged EXEC mode. |
Configuration Examples for Writing EEM Policies Using the Cisco IOS CLI
This section provides the following configuration examples:
•![]() Embedded Event Manager Applet Configuration: Examples
Embedded Event Manager Applet Configuration: Examples
•![]() Embedded Event Manager Manual Policy Execution: Examples
Embedded Event Manager Manual Policy Execution: Examples
•![]() Configuring and Tracking a Stub Object Using Embedded Event Manager: Example
Configuring and Tracking a Stub Object Using Embedded Event Manager: Example
•![]() Embedded Event Manager Watchdog System Monitor (Cisco IOS) Event Detector Configuration: Example
Embedded Event Manager Watchdog System Monitor (Cisco IOS) Event Detector Configuration: Example
•![]() Configuration SNMP Library Extensions: Examples
Configuration SNMP Library Extensions: Examples
•![]() Configuring Variable Logic for EEM Applets: Examples
Configuring Variable Logic for EEM Applets: Examples
•![]() Configuring Description of an EEM Applet: Examples
Configuring Description of an EEM Applet: Examples
Embedded Event Manager Applet Configuration: Examples
The following examples show how to create an EEM applet for some of the EEM event detectors. These examples follow steps outlined in the "Registering and Defining an Embedded Event Manager Applet" section.
Application-Specific Event Detector
The following example shows how a policy named EventPublish_A runs every 20 seconds and publishes an event type numbered 1 to an EEM subsystem numbered 798. The subsystem value of 798 specifies that a publish event has occurred from an EEM policy. A second policy named EventPublish_B is registered to run when the EEM event type 1 occurs with subsystem 798. When the EventPublish_B policy runs, it sends a message to syslog containing data passed as an argument from the EventPublish_A policy.
event manager applet EventPublish_A
event timer watchdog time 20.0
action 1.0 syslog msg "Applet EventPublish_A"
action 2.0 publish-event sub-system 798 type 1 arg1 twenty
exit
event manager applet EventPublish_B
event application sub-system 798 type 1
action 1.0 syslog msg "Applet EventPublish_B arg1 $_application_data1"
CLI Event Detector
The following example shows how to specify an EEM applet to run when the Cisco IOS write memory CLI command is run. The applet provides a notification that this event has occurred via a syslog message. In the example, the sync keyword is configured with the yes argument, and this means that the event detector is notified when this policy completes running. The exit status of the policy determines whether the CLI command will be executed. In this example, the policy exit status is set to one and the CLI command runs.
event manager applet cli-match
event cli pattern "write mem.*" sync yes
action 1.0 syslog msg "$_cli_msg Command Executed"
set 2.0 _exit_status 1
The following example shows an applet which matches the cli pattern with the test argument. When show access-list test is entered, the CLI event detector matches the test argument, and the applet is triggered. The debug event manager detector cli output is added to show num_matches is set to one.
!
event manager applet EEM-PIPE-TEST
event cli pattern "test" sync yes
action 1.0 syslog msg "Pattern matched!"
!
*Aug 23 23:19:59.827: check_eem_cli_policy_handler: command_string=show access-lists test
*Aug 23 23:19:59.827: check_eem_cli_policy_handler: num_matches = 1, response_code = 4
*Aug 23 23:19:59.843: %HA_EM-6-LOG: EEM-PIPE-TEST: Pattern matched!

Note ![]() The functionality provided in the CLI event detector only allows a regular expression pattern match on a valid IOS CLI command itself. This does not include text after a pipe (|) character when redirection is used.
The functionality provided in the CLI event detector only allows a regular expression pattern match on a valid IOS CLI command itself. This does not include text after a pipe (|) character when redirection is used.
The following example shows that when show version | include test is entered, the applet fails to trigger because the CLI event detector does not match on characters entered after the pipe (|) character and the debug event manager detector cli output shows num_matches is set to zero.
*Aug 23 23:20:16.827: check_eem_cli_policy_handler: command_string=show version
*Aug 23 23:20:16.827: check_eem_cli_policy_handler: num_matches = 0, response_code = 1
Counter Event Detector and Timer Event Detector
The following example shows that the EventCounter_A policy is configured to run once a minute and to increment a well-known counter called critical_errors. A second policy—EventCounter_B—is registered to be triggered when the well-known counter called critical_errors exceeds a threshold of 3. When the EventCounter_B policy runs, it resets the counter to 0.
event manager applet EventCounter_A
event timer watchdog time 60.0
action 1.0 syslog msg "EventCounter_A"
action 2.0 counter name critical_errors op inc value 1
exit
event manager applet EventCounter_B
event counter name critical_errors entry-op gt entry-val 3 exit-op lt exit-val 3
action 1.0 syslog msg "EventCounter_B"
action 2.0 counter name critical_errors op set value 0
Interface Counter Event Detector
The following example shows how a policy named EventInterface is triggered every time the receive_throttle counter for Fast Ethernet interface 0/0 is incremented by 5. The polling interval to check the counter is specified to run once every 90 seconds.
event manager applet EventInterface
event interface name FastEthernet0/0 parameter receive_throttle entry-op ge entry-val 5
entry-val-is-increment true poll-interval 90
action 1.0 syslog msg "Applet EventInterface"
Resource Event Detector
The following example shows how to specify event criteria based on an ERM event report for a policy defined to report high CPU usage:
event manager applet policy-one
event resource policy cpu-high
action 1.0 syslog msg "CPU high at $_resource_current_value percent"
RF Event Detector
The RF event detector is only available on networking devices that contain dual Route Processors (RPs). The following example shows how to specify event criteria based on an RF state change notification:
event manager applet start-rf
event rf event rf_prog_initialization
action 1.0 syslog msg "rf state rf_prog_initialization reached"
RPC Event Detector
The RPC event detector allows an outside entity to make a Simple Object Access Protocol (SOAP) request to the router or a switch and invokes a defined EEM policy or script. The following example shows how an EEM applet called Event_RPC is being registered to run an EEM script:
event manager applet Event_RPC
event rpc
action print puts "hello there"
The following example shows the format of the SOAP request and reply message:
<?xml version="1.0" encoding="UTF-8"?>
<SOAP:Envelope xmlns:SOAP="http://www.cisco.com/eem.xsd">
<SOAP:Body>
<run_eemscript>
<script_name>Event_RPC</script_name>
</run_eemscript>
</SOAP:Body>
</SOAP:Envelope>
]]>]]>
<?xml version="1.0" encoding="UTF-8"?><SOAP:Envelope xmlns:SOAP="http://www.cisco.com/eem.xsd"><SOAP:Body><run_eemscript_response><return_code> 0</return_code><output></output></run_eemscript_response></SOAP:Body></SOAP:Envelope>]]>]] >
SNMP Event Detector
The following example shows how to specify an EEM applet to run when the CPU usage is greater than 75 percent. When the EEM applet runs, the CLI commands enable and show cpu processes are run, and an e-mail containing the result of the show cpu processes command is sent to an engineer.
event manager applet snmpcpuge75
event snmp oid 1.3.6.1.4.1.9.9.109.1.1.1.1.3.1 get-type exact entry-op ge entry-val 75 poll-interval 10
action 1.0 cli command "enable"
action 2.0 cli command "show process cpu"
action 3.0 mail server "192.168.1.146" to "engineer@cisco.com" from "devtest@cisco.com" subject "B25 PBX Alert" body "$_cli_result"
The next example is more complex and shows how to configure an EEM applet that causes a switch to the secondary (redundant) Route Processor (RP) when the primary RP runs low on memory.
This example illustrates a method for taking preventative action against a software fault that causes a memory leak. The action taken here is designed to reduce downtime by switching over to a redundant RP when a possible memory leak is detected.
Figure 1 Dual RP Topology
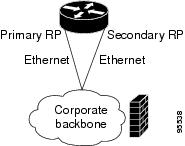
The commands used to register the policy are shown below.
event manager applet memory-demo
event snmp oid 1.3.6.1.4.1.9.9.48.1.1.1.6.1 get-type exact entry-op lt entry-val 5120000 poll-interval 90
action 1.0 syslog priority critical msg "Memory exhausted; current available memory is $_snmp_oid_val bytes"
action 2.0 force-switchover
The registered applet is displayed using the show event manager policy registered command:
Router# show event manager policy registered
No. Type Event Type Time Registered Name
1 applet snmp Thu Jan30 05:57:16 2003 memory-demo
oid {1.3.6.1.4.1.9.9.48.1.1.1.6.1} get-type exact entry-op lt entry-val {5120000}
poll-interval 90
action 1.0 syslog priority critical msg "Memory exhausted; current available memory is $_snmp_oid_val bytes"
action 2.0 force-switchover
For the purpose of this example, a memory depletion is forced on the router, and a series of show memory commands are executed to watch the memory deplete:
Router# show memory
Head Total(b) Used(b) Free(b) Lowest(b) Largest(b)
Processor 53585260 212348444 119523060 92825384 92825384 92365916
Fast 53565260 131080 70360 60720 60720 60668
Router# show memory
Head Total(b) Used(b) Free(b) Lowest(b) Largest(b)
Processor 53585260 212364664 164509492 47855172 47855172 47169340
Fast 53565260 131080 70360 60720 60720 60668
Router# show memory
Head Total(b) Used(b) Free(b) Lowest(b) Largest(b)
Processor 53585260 212369492 179488300 32881192 32881192 32127556
Fast 53565260 131080 70360 60720 60720 60668
When the threshold is reached, an EEM event is triggered. The applet named memory-demo runs, causing a syslog message to be written to the console and a switch to be made to the secondary RP. The following messages are logged:
00:08:31: %HA_EM-2-LOG: memory-demo: Memory exhausted; current available memory is 4484196 bytes
00:08:31: %HA_EM-6-FMS_SWITCH_HARDWARE: fh_io_msg: Policy has requested a hardware switchover
The following is partial output from the show running-config command on both the primary RP and the secondary (redundant) RP:
redundancy
mode sso
.
.
!
event manager applet memory-demo
event snmp oid 1.3.6.1.4.1.9.9.48.1.1.1.6.1 get-type exact entry-op lt entry-val 5120000 poll-interval 90
action 1.0 syslog priority critical msg "Memory exhausted; current available memory is $_snmp_oid_val bytes"
action 2.0 force-switchover
SNMP Notification Event Detector
The following example shows how to configure the snmp-server community public RW and snmp-server manager commands before event snmp-notification is configured.
snmp-server community public RW
snmp-server manager
The following example shows how an EEM applet called SNMP_Notification is being registered to run an EEM script when the router receives an SNMP notification on destination IP address 192.168.1.1 for object ID 1 whose value equals 10.
event manager applet SNMP_Notification
event snmp-notification dest_ip_address 192.168.1.1 oid 1 op eq oid-value 10
action 1 policy eem_script
Syslog Event Detector
The following example shows how to specify an EEM applet to run when syslog identifies that Ethernet interface 1/0 is down. The applet sends a message about the interface to syslog.
event manager applet interface-down
event syslog pattern ".*UPDOWN.*Ethernet1/0.*" occurs 4
action 1.0 syslog msg "Ethernet interface 1/0 changed state 4 times"
Embedded Event Manager Manual Policy Execution: Examples
The following examples show how to use the none event detector to configure an EEM policy (applet or script) to be run manually.
Using the event manager run Command
This example shows how to run a policy manually using the event manager run command. The policy is registered using the event none command under applet configuration mode and then run from global configuration mode using the event manager run command.
event manager applet manual-policy
event none
action 1.0 syslog msg "Manual-policy triggered"
end
!
event manager run manual-policy
Using the action policy Command
This example shows how to run a policy manually using the action policy command. The policy is registered using the event none command under applet configuration mode, and then the policy is executed using the action policy command in applet configuration mode.
event manager applet manual-policy
event none
action 1.0 syslog msg "Manual-policy triggered"
exit
!
event manager applet manual-policy-two
event none
action 1.0 policy manual-policy
end
!
event manager run manual-policy-two
Configuring and Tracking a Stub Object Using Embedded Event Manager: Example
This example shows how to create a stub object, set the state of the stub object, and configure an EEM applet to be run when the tracked object changes. The enhanced object tracking (EOT) event detector is used, and actions are specified to both set and read the state of the object. This example allows EEM to define an EOT object that may be manipulated by other EOT clients. An EEM policy can be a trigger for any EOT object including objects defined for other EOT clients or for an object defined by EEM.
track 10 stub-object
default-state down
!
event manager applet track-ten
event track 10 state any
action 1.0 track set 10 state up
action 2.0 track read 10
Embedded Event Manager Watchdog System Monitor (Cisco IOS) Event Detector Configuration: Example
The following example shows how to configure three EEM applets to demonstrate how the Cisco IOS watchdog system monitor (IOSWDSysMon) event detector works.
Watchdog System Monitor Sample1 Policy
The first policy triggers an applet when the average CPU usage for the process named IP Input is greater than or equal to 1 percent for 10 seconds:
event manager applet IOSWD_Sample1
event ioswdsysmon sub1 cpu-proc taskname "IP Input" op ge val 1 period 10
action 1.0 syslog msg "IOSWD_Sample1 Policy Triggered"
Watchdog System Monitor Sample2 Policy
The second policy triggers an applet when the total amount of memory used by the process named Net Input is greater than 100 kb:
event manager applet IOSWD_Sample2
event ioswdsysmon sub1 mem-proc taskname "Net Input" op gt val 100 is-percent false
action 1.0 syslog msg "IOSWD_Sample2 Policy Triggered"
Watchdog System Monitor Sample3 Policy
The third policy triggers an applet when the total amount of memory used by the process named IP RIB Update has increased by more than 50 percent over the sample period of 60 seconds:
event manager applet IOSWD_Sample3
event ioswdsysmon sub1 mem-proc taskname "IP RIB Update" op gt val 50 is-percent true period 60
action 1.0 syslog msg "IOSWD_Sample3 Policy Triggered"
The three policies are configured, and then repetitive large pings are made to the networking device from several workstations, causing the networking device to register some usage. This will trigger policies 1 and 2, and the console will display the following messages:
00:42:23: %HA_EM-6-LOG: IOSWD_Sample1: IOSWD_Sample1 Policy Triggered
00:42:47: %HA_EM-6-LOG: IOSWD_Sample2: IOSWD_Sample2 Policy Triggered
To view the policies that are registered, use the show event manager policy registered command:
Router# show event manager policy registered
No. Class Type Event Type Trap Time Registered Name
1 applet system ioswdsysmon Off Fri Jul 23 02:27:28 2004 IOSWD_Sample1
sub1 cpu_util {taskname {IP Input} op ge val 1 period 10.000 }
action 1.0 syslog msg "IOSWD_Sample1 Policy Triggered"
2 applet system ioswdsysmon Off Fri Jul 23 02:23:52 2004 IOSWD_Sample2
sub1 mem_used {taskname {Net Input} op gt val 100 is_percent FALSE}
action 1.0 syslog msg "IOSWD_Sample2 Policy Triggered"
3 applet system ioswdsysmon Off Fri Jul 23 03:07:38 2004 IOSWD_Sample3
sub1 mem_used {taskname {IP RIB Update} op gt val 50 is_percent TRUE period 60.000 }
action 1.0 syslog msg "IOSWD_Sample3 Policy Triggered"
Configuration SNMP Library Extensions: Examples
This section provides the following configuration examples:
•![]() SNMP Get Operations: Examples
SNMP Get Operations: Examples
•![]() SNMP GetID Operations: Examples
SNMP GetID Operations: Examples
•![]() Generating SNMP Notifications: Examples
Generating SNMP Notifications: Examples
SNMP Get Operations: Examples
The following example shows how to send a get request to the local host.
Router(config)# event manager applet snmp
Router(config-applet)# event snmp oid 1.3.6.1.2.1.1.1.0 get-type exact entry-op lt entry-val 5120000 poll-interval 90
Router(config-applet)# action 1.3 info type snmp oid 1.3.6.1.2.1.1.1.0 get-type exact community public
Router(config-applet)# action 1.3 info type snmp oid 1.3.6.1.2.1.1.4.0 get-type next community public
The following log message will be written to the SNMP event manager log:
1d03h:%HA_EM-6-LOG: lg: 1.3.6.1.2.1.1.1.0
1d04h:%HA_EM-6-LOG: lgn: 1.3.6.1.2.1.1.5.0
The following example shows how to send a get request to a remote host.
Router(config)# event manager applet snmp
Router(config-applet)# event snmp oid 1.3.6.1.2.1.1.1.0 get-type exact entry-op lt entry-val 5120000 poll-interval 90
Router(config-applet)# action 1.3 info type snmp oid 1.3.6.1.2.1.1.4.0 get-type next community public ipaddr 172.17.16.69
Router(config-applet)# action 1.3 info type snmp getid 1.3.6.1.2.1.1.1.0 community public ipaddr 172.17.16.69
The following log message is written to the SNMP event manager log:
1d03h:%HA_EM-6-LOG: lg: 1.3.6.1.2.1.1.1.0
1d04h:%HA_EM-6-LOG: lgn: 1.3.6.1.2.1.1.5.0
SNMP GetID Operations: Examples
The following example shows how to send a getid request to the local host.
Router(config)# event manager applet snmp
Router(config-applet)# event snmp oid 1.3.6.1.2.1.1.1.0 get-type exact entry-op lt entry-val 5120000 poll-interval 90
Router(config-applet)# action 1.3 info type snmp getid community public
The following log message is written to the SNMP event manager log:
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_sysname_oid=1.3.6.1.2.1.1.5.0
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_sysname_value=jubjub.cisco.com
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_syslocation_oid=1.3.6.1.2.1.1.6.0
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_syslocation_value=
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_sysdescr_oid=1.3.6.1.2.1.1.1.0
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_sysobjectid_oid=1.3.6.1.2.1.1.2.0
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_sysobjectid_value=products.222
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_sysuptime_oid=1.3.6.1.2.1.1.3.0
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_sysuptime_oid=10131676
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_syscontact_oid=1.3.6.1.2.1.1.4.0
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_syscontact_value=YYY
The following example shows how to send a getid request to a remote host.
Router(config)# event manager applet snmp
Router(config-applet)# event snmp oid 1.3.6.1.2.1.1.1.0 get-type exact entry-op lt entry-val 5120000 poll-interval 90
Router(config-applet)# action 1.3 info type snmp getid 1.3.6.1.2.1.1.1.0 community public ipaddr 172.17.16.69
The following log message is written to the SNMP event manager log:
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_sysname_oid=1.3.6.1.2.1.1.5.0
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_sysname_value=jubjub.cisco.com
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_syslocation_oid=1.3.6.1.2.1.1.6.0
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_syslocation_value=
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_sysdescr_oid=1.3.6.1.2.1.1.1.0
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_sysobjectid_oid=1.3.6.1.2.1.1.2.0
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_sysobjectid_value=products.222
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_sysuptime_oid=1.3.6.1.2.1.1.3.0
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_sysuptime_oid=10131676
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_syscontact_oid=1.3.6.1.2.1.1.4.0
1d04h:%HA_EM-6-LOG: lgid: _info_snmp_syscontact_value=YYY
Set Operations: Examples
The following example shows how to perform a set operation on the local host.
Router(config)# event manager applet snmp
Router(config-applet)# event snmp oid 1.3.6.1.2.1.1.1.0 get-type exact entry-op lt entry-val 5120000 poll-interval 90
Router(config-applet)# action 1.3 info type snmp oid 1.3.6.1.2.1.1.4.0 set-type integer 5 sysName.0 community public
The following log message is written to the SNMP event manager log:
1d04h:%HA_EM-6-LOG: lset: 1.3.6.1.2.1.1.4.0
1d04h:%HA_EM-6-LOG: lset: XXX
The following example shows how to perform a set operation on a remote host.
Router(config)# event manager applet snmp
Router(config-applet)# event snmp oid 1.3.6.1.2.1.1.1.0 get-type exact entry-op lt entry-val 5120000 poll-interval 90
Router(config-applet)# action 1.3 info type snmp oid 1.3.6.1.2.1.1.4.0 set-type integer 5 sysName.0 community public ipaddr 172.17.16.69
The following log message is written to the SNMP event manager log:
1d04h:%HA_EM-6-LOG: lset: 1.3.6.1.2.1.1.4.0
1d04h:%HA_EM-6-LOG: lset: XXX
Generating SNMP Notifications: Examples
The following example shows how to configure SNMP traps for the sysUpTime.0 variable:
Router(config)# event manager applet snmp
Router(config-applet)# event snmp oid 1.3.6.1.4.1.9.9.48.1.1.1.6.1 get-type exact entry-op lt entry-val 5120000 poll-interval 90
Router(config-applet)# action 1.3 info type snmp var sysUpTime.0 oid 1.3.6.1.4.1.9.9.43.1.1.6.1.3.41 integer 2
Router(config-applet)# action 1.4 info type snmp trap enterprise-oid ciscoSyslogMIB.2 generic-trapnum 6 specific-trapnum 1 trap-oid 1.3.6.1.4.1.9.9.41.2.0.1 trap-var sysUpTime.0
The following output is generated if the debug snmp packets command is enabled:
Router# debug snmp packets
1d04h: SNMP: Queuing packet to 172.69.16.2
1d04h: SNMP: V1 Trap, ent ciscoSyslogMIB.2, addr 172.19.rap 1
clogHistoryEntry.3 = 4
clogHistoryEntry.6 = 9999
1d04h: SNMP: Queuing packet to 172.19.208.130
1d04h: SNMP: V1 Trap, ent ciscoSyslogMIB.2, addr 172.19.rap 1
clogHistoryEntry.3 = 4
clogHistoryEntry.6 = 9999
1d04h: SNMP: Packet sent via UDP to 172.69.16.2
1d04h: SNMP: Packet sent via UDP to 172.69.16.2
infra-view10:
Packet Dump:
30 53 02 01 00 04 04 63 6f 6d 6d a4 48 06 09 2b
06 01 04 01 09 09 29 02 40 04 ac 13 d1 17 02 01
06 02 01 01 43 04 00 9b 82 5d 30 29 30 12 06 0d
2b 06 01 04 01 09 09 29 01 02 03 01 03 02 01 04
30 13 06 0d 2b 06 01 04 01 09 09 29 01 02 03 01
06 02 02 27 0f
Received SNMPv1 Trap:
Community: comm
Enterprise: ciscoSyslogMIBNotificationPrefix
Agent-addr: 172.19.209.23
Enterprise Specific trap.
Enterprise Specific trap: 1
Time Ticks: 10191453
clogHistSeverity = error(4)
clogHistTimestamp = 9999
The following example shows how to configure SNMP inform requests for the sysUpTime.0 variable:
Router(config)# event manager applet snmp
Router(config-applet)# event snmp oid 1.3.6.1.4.1.9.9.48.1.1.1.6.1 get-type exact entry-op lt entry-val 5120000 poll-interval 90
Router(config-applet)# action 1.3 info type snmp var sysUpTime.0 oid 1.3.6.1.4.1.9.9.43.1.1.6.1.3.41 integer 2
Router(config-applet)# action 1.4 info type snmp inform trap-oid 1.3.6.1.4.1.9.9.43.2.0.1 trap-var sysUpTime.0 community public ipaddr 172.19.209.24
The following output is generated if the debug snmp packets command is enabled:
Router# debug snmp packets
1d04h: SNMP: Inform request, reqid 24, errstat 0, erridx 0
sysUpTime.0 = 10244391
snmpTrapOID.0 = ciscoConfigManMIB.2.0.1
ccmHistoryEventEntry.3.40 = 1
1d04h: SNMP: Packet sent via UDP to 172.19.209.24.162
1d04h: SNMP: Packet received via UDP from 172.19.209.24 on FastEthernet0/0
1d04h: SNMP: Response, reqid 24, errstat 0, erridx 0
1d04h: SNMP: Response, reqid 24, errstat 0, erridx 0
1d04h: SNMP: Inform request, reqid 25, errstat 0, erridx 0
sysUpTime.0 = 10244396
snmpTrapOID.0 = ciscoConfigManMIB.2.0.1
ccmHistoryEventEntry.3.41 = 2
1d04h: SNMP: Packet sent via UDP to 172.19.209.24.162
1d04h: SNMP: Packet received via UDP from 172.19.209.24 on FastEthernet0/0
1d04h: SNMP: Response, reqid 25, errstat 0, erridx 0
1d04h: SNMP: Response, reqid 25, errstat 0, erridx 0
Router# debug snmp packets
5d04h: SNMP: Packet received via UDP from 172.19.209.23 on FastEthernet0/0
5d04h: SNMP: Inform request, reqid 24, errstat 0, erridx 0
sysUpTime.0 = 10244391
snmpTrapOID.0 = ciscoConfigManMIB.2.0.1
ccmHistoryEventEntry.3.40 = 1
5d04h: dest if_index = 1
5d04h: dest ip addr= 172.19.209.24
5d04h: SNMP: Response, reqid 24, errstat 0, erridx 0
5d04h: SNMP: Packet sent via UDP to 172.19.209.23.57748
5d04h: SNMP: Packet received via UDP from 172.19.209.23 on FastEthernet0/0
5d04h: SNMP: Inform request, reqid 25, errstat 0, erridx 0
Configuring Variable Logic for EEM Applets: Examples
The following sections provide examples on some selected action commands. For information on all the action commands supporting variable logic within applets, see Table 6.
In this example, conditional loops while, if and foreach are used to print data. Other action commands such as action divide, action increment and action puts are used to define the actions to be performed when the conditions are met.
event manager applet printdata
event none
action 100 set colors "red green blue"
action 101 set shapes "square triangle rectange"
action 102 set i "1"
action 103 while $i lt 6
action 104 divide $i 2
action 105 if $_remainder eq 1
action 106 foreach _iterator "$colors"
action 107 puts nonewline "$_iterator "
action 108 end
action 109 puts ""
action 110 else
action 111 foreach _iterator "$shapes"
action 112 puts nonewline "$_iterator "
action 113 end
action 114 puts ""
action 115 end
action 116 increment i
action 117 end
When the event manager applet ex is run, the following output is obtained:
event manager run printdata
red green blue
square triangle rectange
red green blue
square triangle rectange
red green blue
In this example, two environment variables poll_interface and max_rx_rate are set to F0/0 and 3 respectively. Every 30 seconds there is a poll on an interface for rx rate. If the rx rate is greater than the threshold, a syslog message is displayed.
This applet makes use of the foreach conditional statement to poll the interface, the if conditional block to compare the value under RXPS with max_rx_rate that was set in the EEM environment variable.
event manager environment poll_interfaces F0/0
event manager environment max_rx_rate 3
ev man app check_rx_rate
ev timer watchdog name rx_timer time 30
action 100 foreach int $poll_interfaces
action 101 cli command "en"
action 102 cli command "show int $int summ | beg ------"
action 103 foreach line $_cli_result "\n"
action 105 regexp ".*[0-9]+\s+[0-9]+\s+[0-9]+\s+[0-9]+\s+[0-9]+\s+([0-9]+)\s+.*" $line junk rxps
action 106 if $_regexp_result eq 1
action 107 if $rxps gt $max_rx_rate
action 108 syslog msg "Warning rx rate for $int is > than threshold. Current value is $rxps (threshold is $max_rx_rate)"
action 109 end
action 110 end
action 111 end
action 112 end
Example syslog message:
Oct 16 09:29:26.153: %HA_EM-6-LOG: c: Warning rx rate for F0/0 is > than threshold. Current value is 4 (threshold is 3)
The output of show int F0/0 summ is of the format:
#show int f0/0 summ
*: interface is up
IHQ: pkts in input hold queue IQD: pkts dropped from input queue
OHQ: pkts in output hold queue OQD: pkts dropped from output queue
RXBS: rx rate (bits/sec) RXPS: rx rate (pkts/sec)
TXBS: tx rate (bits/sec) TXPS: tx rate (pkts/sec)
TRTL: throttle count
Interface IHQ IQD OHQ OQD RXBS RXPS TXBS TXPS TRTL
-------------------------------------------------------------------------
* FastEthernet0/0 0 87283 0 0 0 0 0 0 0

Note ![]() To use other action commands supporting variable logic within applets, use the commands listed in Table 6.
To use other action commands supporting variable logic within applets, use the commands listed in Table 6.
Configuring Event SNMP-Object: Examples
The following example shows the SET operation and the value to set is in $_snmp_value and it is managed by the script. The example below saves the oid and its value as contexts to be retrieved later.
event manager applet snmp-object1
description "APPLET SNMP-OBJ-1"
event snmp-object oid 1.3.6.1.2.1.31.1.1.1.18 type string sync no skip no istable yes default 0 action 1 syslog msg "SNMP-OBJ1:TRIGGERED" facility "SNMP_OBJ"
action 2 context save key myoid variable "_snmp_oid"
action 3 context save key myvalue variable "_snmp_value"
Configuring Description of an EEM Applet: Examples
The following example shows how to add or modify the description for an Embedded Event Manager (EEM) applet that is run by sampling Simple Network Management Protocol (SNMP):
event manager applet test
description "This applet looks for the word count in syslog messages"
event syslog pattern "count"
action 1 syslog msg hi
Where to Go Next
•![]() For information about EEM overview, go to "Embedded Event Manager Overview" module.
For information about EEM overview, go to "Embedded Event Manager Overview" module.
•![]() For information about writing EEM policies using Tcl, go to "Writing Embedded Event Manager Policies Using Tcl" module.
For information about writing EEM policies using Tcl, go to "Writing Embedded Event Manager Policies Using Tcl" module.
Additional References
The following sections provide references related to writing EEM policies Using the Cisco IOS CLI.
Related Documents
Standards
|
|
|
|---|---|
No new or modified standards are supported, and support for existing standards has not been modified. |
— |
MIBs
|
|
|
|---|---|
CISCO-EMBEDDED-EVENT-MGR-MIB |
To locate and download MIBs for selected platforms, Cisco IOS releases, and feature sets, use Cisco MIB Locator found at the following URL: |
RFCs
|
|
|
|---|---|
No new or modified RFCs are supported, and support for existing RFCs has not been modified. |
— |
Technical Assistance
Feature Information for Writing EEM Policies Using the Cisco IOS CLI
Table 7 lists the features in this module and provides links to specific configuration information. Only features that were introduced or modified in Cisco IOS Releases 12.3(14)T, 12.2(25)S, 12.0(26)S, 12.2(18)SXF4, 12.2(28)SB, 12.2(33)SRA, 12.2(33)SXH, 12.2(33)SXI, 12.4(20)T, 12.4(22)T, 15.0(1)M, 12.2(33)SRE or a later release appear in the table.
Not all commands may be available in your Cisco IOS software release. For release information about a specific command, see the command reference documentation.
Use Cisco Feature Navigator to find information about platform support and software image support. Cisco Feature Navigator enables you to determine which Cisco IOS and Catalyst OS software images support a specific software release, feature set, or platform. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.

Note ![]() Table 7 lists only the Cisco IOS software release that introduced support for a given feature in a given Cisco IOS software release train. Unless noted otherwise, subsequent releases of that Cisco IOS software release train also support that feature.
Table 7 lists only the Cisco IOS software release that introduced support for a given feature in a given Cisco IOS software release train. Unless noted otherwise, subsequent releases of that Cisco IOS software release train also support that feature.
|
|
|
|
|---|---|---|
Embedded Event Manager 1.0 |
12.0(26)S |
EEM 1.0 introduced Embedded Event Manager applet creation with the SNMP and syslog event detectors. EEM 1.0 also introduced the following actions: generating prioritized syslog messages, generating a CNS event for upstream processing by Cisco CNS devices, reloading the Cisco IOS software, and switching to a secondary processor in a fully redundant hardware configuration. The following sections provide information about this feature: • • • • The following commands were introduced by this feature: action cns-event, action force-switchover, action reload, action syslog, debug event manager, event manager applet, event snmp, event syslog, show event manager policy registered. |
Embedded Event Manager 2.0 |
12.2(25)S |
EEM 2.0 introduced the application-specific event detector, the counter event detector, the interface counter event detector, the timer event detector, and the watchdog event detector. New actions included modifying a named counter, publishing an application-specific event, and generating an SNMP trap. The ability to define environment variables and to run EEM policies written using Tcl was introduced, and two sample policies were included with the software. The following sections provide information about this feature: • • • • • • • • The following commands were introduced by this feature: action counter, action publish-event, action snmp-trap, event application, event counter, event interface, event ioswdsysmon, event manager environment, event manager history size, event manager policy, event manager scheduler suspend, event timer, show event manager environment, show event manager history events, show event manager history traps, show event manager policy available, show event manager policy pending. |
Embedded Event Manager 2.1 |
12.3(14)T 12.2(18)SXF5 |
EEM 2.1 introduced some new event detectors and actions with new functionality to allow EEM policies to be run manually and the ability to run multiple concurrent policies. Support for Simple Network Management Protocol (SNMP) event detector rate-based events was provided as was the ability to create policies using Tool Command Language (Tcl). The following sections provide information about this feature: • • • • The following commands were introduced or modified by this feature: action cli, action counter, action info, action mail, action policy, debug event manager, event cli, event manager directory user, event manager policy, event manager run, event manager scheduler script, event manager session cli username, event none, event oir, event snmp, event syslog, set (EEM), show event manager directory user, show event manager policy registered, show event manager session cli username. |
Embedded Event Manager 2.1 (Software Modularity) |
12.2(18)SXF4Cisco IOS Software Modularity images |
EEM 2.1 for Software Modularity images introduced the GOLD, system manager, and WDSysMon (Cisco IOS Software Modularity watchdog) event detectors, and the ability to display Cisco IOS Software Modularity processes and process metrics. The following sections provide information about this, feature: • • • The following commands were introduced by this feature: event gold, event process, show event manager metric process. Note |
Embedded Event Manager 2.2 |
12.4(2)T |
EEM 2.2 introduced the enhanced object tracking, resource, and RF event detectors. The actions of reading and setting the state of a tracked object were also introduced. The following sections provide information about this feature: • • • • The following commands were introduced or modified by this feature: action track read, action track set, default-state, event resource, event rf, event track, show track, track stub-object. |
SNMP event detector delta environment variable |
12.4(11)T |
A new SNMP event detector environment variable, _snmp_oid_delta_val, was introduced. This is a minor enhancement. Minor enhancements are not typically listed in Feature Navigator. |
Embedded Event Manager 2.3 |
12.2(33)SXH |
EEM 2.3 introduced some new features relative to the Generic Online Diagnostics (GOLD) Event Detector on the Cisco Catalyst 6500 Series switches. The event gold command was enhanced in addition to the Tcl keywords—action-notify, testing-type, test-name, test-id, consecutive-failure, platform-action, and maxrun—for improved reaction to GOLD test failures and conditions The following section was updated to describe the enhanced functionality of the event gold command: • Read-only variables were added under the GOLD Event Detector category to provide access to platform-wide and test-specific GOLD event detector information for a detected event. |
Embedded Event Manager 2.4 |
12.4(20)T |
EEM 2.4 is supported in Cisco IOS Release 12.4(20)T and later releases, and introduced several new features. The following sections provide information about this feature: • • • • The following commands were introduced by this feature: attribute (EEM), correlate, event manager detector rpc, event manager directory user repository, event manager update user policy, event manager scheduler clear, event manager update user policy, event owner, event rpc, event snmp-notification, show event manager detector, show event manager version, trigger (EEM). |
Embedded Event Manger 3.0 |
12.4(22)T |
EEM 3.0 is supported in Cisco IOS Release 12.4(22)T and later releases, and introduced several new features. The following sections provide information about this feature: • • • • The following commands were introduced or modified by this feature: action add, action append, action break, action comment, action context retrieve, action context save, action continue, action decrement, action divide, action else, action elseif, action end, action exit, action foreach, action gets, action if, action if goto, action increment, action info type interface-names, action info type snmp getid, action info type snmp inform, action info type snmp oid, action info type snmp trap, action info type snmp var, action multiply, action puts, action regexp, action set (EEM), action string compare, action string equal, action string first, action string index, action string last, action string length, action string match, action string range, action string replace, action string tolower, action string toupper, action string trim, action string trimleft, action string trimright, action subtract, action while, event cli, event ipsla, event manager detector routing, event manager scheduler, event manager scheduler clear, event manager scheduler hold, event manager scheduler modify, event manager scheduler release, event nf, event routing, show event manager policy active, show event manager policy pending, and show event manager scheduler. |
Embedded Event Manager 3.1 |
15.0(1)M |
EEM 3.1 is supported in Cisco IOS Release 15.0(1)M and later releases, and introduced several new features. The following sections provide information about this feature: • • • • The following commands were introduced or modified by this feature: action syslog, description, event manager applet, event manager policy, event snmp-notification, event snmp-object, show event manager policy registered, and show event manager policy available. |
Cisco and the Cisco Logo are trademarks of Cisco Systems, Inc. and/or its affiliates in the U.S. and other countries. A listing of Cisco's trademarks can be found at www.cisco.com/go/trademarks. Third party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1005R)
© 2005-2010 Cisco Systems, Inc. All rights reserved.
 Feedback
Feedback