- Finding Feature Information
- Contents
- Information About Embedded Event Manager
- Embedded Event Manager
- Embedded Event Manager 2.0
- Embedded Event Manager 2.1
- Embedded Event Manager 2.1 (Software Modularity)
- Embedded Event Manager 2.2
- Embedded Event Manager 2.3
- EEM Event Detectors Available on Cisco IOS XE Software Release
- Event Detectors
- Embedded Event Manager Actions
- Embedded Event Manager Environment Variables
- Embedded Event Manager Policy Creation
- Where to Go Next
- Additional References
- Feature Information for Embedded Event Manager Overview
Embedded Event Manager Overview
Embedded Event Manager (EEM) is a distributed and customized approach to event detection and recovery offered directly in a Cisco IOS XE device. EEM offers the ability to monitor events and take informational, corrective, or any desired EEM action when the monitored events occur or when a threshold is reached. An EEM policy is an entity that defines an event and the actions to be taken when that event occurs.
This module contains a technical overview of EEM. EEM can be used alone, or with other network management technologies to help monitor and maintain your network. Before you begin to implement EEM, it is important that you understand the information presented in this module.
Finding Feature Information
For the latest feature information and caveats, see the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the "Feature Information for Embedded Event Manager Overview" section.
Use Cisco Feature Navigator to find information about platform support and Cisco IOS XE software image support. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Contents
•![]() Information About Embedded Event Manager
Information About Embedded Event Manager
•![]() Feature Information for Embedded Event Manager Overview
Feature Information for Embedded Event Manager Overview
Information About Embedded Event Manager
To use EEM in your network, you should understand the following concepts:
•![]() Embedded Event Manager 2.1 (Software Modularity)
Embedded Event Manager 2.1 (Software Modularity)
•![]() EEM Event Detectors Available on Cisco IOS XE Software Release
EEM Event Detectors Available on Cisco IOS XE Software Release
•![]() Embedded Event Manager Actions
Embedded Event Manager Actions
•![]() Embedded Event Manager Environment Variables
Embedded Event Manager Environment Variables
•![]() Embedded Event Manager Policy Creation
Embedded Event Manager Policy Creation
Embedded Event Manager
Event tracking and management has traditionally been performed by devices external to the networking device. Embedded Event Manager (EEM) has been designed to offer event management capability directly in Cisco IOS XE devices. The on-device, proactive event management capabilities of EEM are useful because not all event management can be done off router because some problems compromise communication between the router and the external network management device. Capturing the state of the router during such situations can be invaluable in taking immediate recovery actions and gathering information to perform root-cause analysis. Network availability is also improved if automatic recovery actions are performed without the need to fully reboot the routing device.
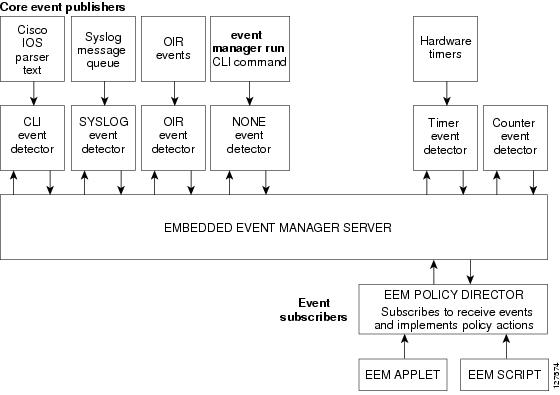
EEM is a flexible, policy-driven framework that supports in-box monitoring of different components of the system with the help of software agents known as event detectors. Figure 1 shows the relationship between the EEM server, core event publishers (event detectors), and the event subscribers (policies). Basically, event publishers screen events and publish them when there is a match on an event specification that is provided by the event subscriber. Event detectors notify the EEM server when an event of interest occurs. The EEM policies that are configured using the Cisco IOS XE command-line interface (CLI) then implement recovery on the basis of the current state of the system and the actions specified in the policy for the given event.
EEM offers the ability to monitor events and take informational or corrective action when the monitored events occur or when a threshold is reached. An EEM policy is an entity that defines an event and the actions to be taken when that event occurs. There are two types of EEM policies: an applet or a script. An applet is a simple form of policy that is defined within the CLI configuration. A script is a form of policy that is written in Tool Command Language (Tcl).
Figure 1 Embedded Event Manager Core Event Detectors
Embedded Event Manager 2.0
EEM 2.0 is supported in Cisco IOS XE releases and introduces some new features. EEM 2.0 introduced the following event detectors:
•![]() Application-Specific—The application-specific event detector allows any Embedded Event Manager policy to publish an event.
Application-Specific—The application-specific event detector allows any Embedded Event Manager policy to publish an event.
•![]() Counter—The counter event detector publishes an event when a named counter crosses a specified threshold.
Counter—The counter event detector publishes an event when a named counter crosses a specified threshold.
•![]() Interface Counter—The interface counter event detector publishes an event when a generic Cisco IOS interface counter for a specified interface crosses a defined threshold.
Interface Counter—The interface counter event detector publishes an event when a generic Cisco IOS interface counter for a specified interface crosses a defined threshold.
•![]() Timer—The timer event detector publishes events for the following four different types of timers: absolute-time-of-day, countdown, watchdog, and CRON.
Timer—The timer event detector publishes events for the following four different types of timers: absolute-time-of-day, countdown, watchdog, and CRON.
•![]() Watchdog System Monitor (IOSWDSysMon)—The Cisco IOS XE watchdog system monitor event detector publishes an event when CPU or memory utilization for a Cisco IOS XE process crosses a threshold.
Watchdog System Monitor (IOSWDSysMon)—The Cisco IOS XE watchdog system monitor event detector publishes an event when CPU or memory utilization for a Cisco IOS XE process crosses a threshold.
EEM 2.0 introduced the following actions:
•![]() Setting or modifying a named counter.
Setting or modifying a named counter.
•![]() Publishing an application-specific event
Publishing an application-specific event
•![]() Generating an SNMP trap.
Generating an SNMP trap.
The ability to run a Cisco defined sample policy written using Tool Command Language (Tcl) was introduced. A sample policy was provided that could be stored in the system policy directory.
Embedded Event Manager 2.1
EEM 2.1 is supported in Cisco IOS XE releases, and introduces some new features. EEM 2.1 introduced the following new event detectors:
•![]() CLI—The CLI event detector screens command-line interface (CLI) commands for a regular expression match.
CLI—The CLI event detector screens command-line interface (CLI) commands for a regular expression match.
•![]() None—The none event detector publishes an event when the Cisco IOS XE event manager run CLI command executes an EEM policy.
None—The none event detector publishes an event when the Cisco IOS XE event manager run CLI command executes an EEM policy.
•![]() OIR—The online insertion and removal (OIR) event detector publishes an event when a particular hardware insertion or removal event occurs.
OIR—The online insertion and removal (OIR) event detector publishes an event when a particular hardware insertion or removal event occurs.
EEM 2.1 introduced the following actions:
•![]() Executing a Cisco IOS XE CLI command.
Executing a Cisco IOS XE CLI command.
•![]() Requesting system information when an event occurs.
Requesting system information when an event occurs.
•![]() Sending a short e-mail.
Sending a short e-mail.
•![]() Manually running an EEM policy.
Manually running an EEM policy.
EEM 2.1 also permits multiple concurrent policies to be run using the new event manager scheduler script command. Support for SNMP event detector rate-based events is provided as is the ability to create policies using Tool Command Language (Tcl).
Embedded Event Manager 2.1 (Software Modularity)
EEM 2.1 (Software Modularity) is supported in Cisco IOS XE releases on Cisco IOS XE Software Modularity images. EEM 2.1 (Software Modularity) introduced the following event detectors:
•![]() GOLD—The Generic Online Diagnostic (GOLD) event detector publishes an event when a GOLD failure event is detected on a specified card and subcard.
GOLD—The Generic Online Diagnostic (GOLD) event detector publishes an event when a GOLD failure event is detected on a specified card and subcard.

Note ![]() GOLD is not supported on the Cisco ASR 1000 Series routers.
GOLD is not supported on the Cisco ASR 1000 Series routers.
•![]() System Manager—The system manager event detector generates events for Cisco IOS XE Software Modularity process start, normal or abnormal stop, and restart events. The events generated by the system manager allows policies to change the default behavior of the process restart.
System Manager—The system manager event detector generates events for Cisco IOS XE Software Modularity process start, normal or abnormal stop, and restart events. The events generated by the system manager allows policies to change the default behavior of the process restart.
•![]() Watchdog System Monitor (WDSysMon)—The Cisco IOS XE Software Modularity watchdog system monitor event detector detects infinite loops, deadlocks, and memory leaks in Cisco IOS XE Software Modularity processes.
Watchdog System Monitor (WDSysMon)—The Cisco IOS XE Software Modularity watchdog system monitor event detector detects infinite loops, deadlocks, and memory leaks in Cisco IOS XE Software Modularity processes.
EEM 2.1 for Software Modularity introduced the ability to display EEM reliability metric data for processes.

Note ![]() EEM 2.1 for Software Modularity images also supports the resource and RF event detectors introduced in EEM 2.2, but it does not support the enhanced object tracking event detector or the actions to read and set tracked objects.
EEM 2.1 for Software Modularity images also supports the resource and RF event detectors introduced in EEM 2.2, but it does not support the enhanced object tracking event detector or the actions to read and set tracked objects.
Embedded Event Manager 2.2
EEM 2.2 is supported in Cisco IOS XE releases, and introduces some new features. EEM 2.2 introduced the following event detectors:
•![]() Enhanced Object Tracking—The enhanced object tracking event detector publishes an event when the tracked object changes. Enhanced object tracking provides complete separation between the objects to be tracked and the action to be taken by a client when a tracked object changes.
Enhanced Object Tracking—The enhanced object tracking event detector publishes an event when the tracked object changes. Enhanced object tracking provides complete separation between the objects to be tracked and the action to be taken by a client when a tracked object changes.
•![]() Resource—The resource event detector publishes an event when the Embedded Resource Manager (ERM) reports an event for the specified policy.
Resource—The resource event detector publishes an event when the Embedded Resource Manager (ERM) reports an event for the specified policy.
•![]() RF—The redundancy framework (RF) event detector publishes an event when one or more RF events occur during synchronization in a dual Route Processor (RP) system. The RF event detector can also detect an event when a dual RP system continuously switches from one RP to another RP (referred to as a ping-pong situation).
RF—The redundancy framework (RF) event detector publishes an event when one or more RF events occur during synchronization in a dual Route Processor (RP) system. The RF event detector can also detect an event when a dual RP system continuously switches from one RP to another RP (referred to as a ping-pong situation).
EEM 2.2 introduced the following actions:
•![]() Reading the state of a tracked object.
Reading the state of a tracked object.
•![]() Setting the state of a tracked object.
Setting the state of a tracked object.
Embedded Event Manager 2.3
EEM 2.3 introduces enhancements to the Generic Online Diagnostics (GOLD) Event Detector on that product.

Note ![]() GOLD is not supported on the Cisco ASR 1000 Series routers.
GOLD is not supported on the Cisco ASR 1000 Series routers.
•![]() The event gold command was enhanced with the addition of the action-notify, testing-type, test-name, test-id, consecutive-failure, platform-action, and maxrun keywords for improved reaction to GOLD test failures and conditions.
The event gold command was enhanced with the addition of the action-notify, testing-type, test-name, test-id, consecutive-failure, platform-action, and maxrun keywords for improved reaction to GOLD test failures and conditions.
•![]() The following platform-wide GOLD Event Detector information can be accessed through new read-only EEM built-in environment variables:
The following platform-wide GOLD Event Detector information can be accessed through new read-only EEM built-in environment variables:
–![]() Boot-up diagnostic level
Boot-up diagnostic level
–![]() Card index, name, serial number
Card index, name, serial number
–![]() Port counts
Port counts
–![]() Test counts
Test counts
•![]() The following test-specific GOLD Event Detector information can be accessed through new read-only EEM built-in environment variables (available to EEM applets only):
The following test-specific GOLD Event Detector information can be accessed through new read-only EEM built-in environment variables (available to EEM applets only):
–![]() Test name, attribute, total run count
Test name, attribute, total run count
–![]() Test result per test, port, or device
Test result per test, port, or device
–![]() Total failure count, last fail time
Total failure count, last fail time
–![]() Error code
Error code
–![]() Occurrence of consecutive failures
Occurrence of consecutive failures
These enhancements result in reduced mean time to recovery (MTTR) and higher availability through improved automation and fault detection.
EEM Event Detectors Available on Cisco IOS XE Software Release
EEM uses software programs known as event detectors to determine when an EEM event occurs. Some event detectors are available on every Cisco IOS XE software release, but most event detectors have been introduced in a specific release. Use Table 1 to determine which event detectors are available in your specific Cisco IOS release. A blank entry (—) indicates that the event detector is not available: the text "Yes" indicates that the event detector is available. The event detectors shown in Table 1 are supported in later releases of the same Cisco IOS XE software release train. For more details on each event detector, see the "Event Detectors" section.
Event Detectors
Embedded Event Manager (EEM) uses software programs known as event detectors to determine when an EEM event occurs. Event detectors are separate systems that provide an interface between the agent being monitored, for example Simple Network Management Protocol (SNMP), and the EEM policies where an action can be implemented. EEM contains the following event detectors.
Application-Specific Event Detector
The application-specific event detector allows any Embedded Event Manager policy to publish an event. When an EEM policy publishes an event it must use an EEM subsystem number of 798 with any event type. If an existing policy is registered for subsystem 798 and a specified event type, a second policy of the same event type will trigger the first policy to run when the specified event is published.
CLI Event Detector
The CLI event detector screens command-line interface (CLI) commands for a regular expression match. When a match is found, an event is published. The match logic is performed on the fully expanded CLI command after the command is successfully parsed and before it is executed. The CLI event detector supports three publish modes:
•![]() Synchronous publishing of CLI events—The CLI command is not executed until the EEM policy exits, and the EEM policy can control whether the command is executed. The read/write variable, _exit_status, allows you to set the exit status at policy exit for policies triggered from synchronous events. If _exit_status is 0, the command is skipped, if _exit_status is 1, the command is run.
Synchronous publishing of CLI events—The CLI command is not executed until the EEM policy exits, and the EEM policy can control whether the command is executed. The read/write variable, _exit_status, allows you to set the exit status at policy exit for policies triggered from synchronous events. If _exit_status is 0, the command is skipped, if _exit_status is 1, the command is run.
•![]() Asynchronous publishing of CLI events—The CLI event is published, and then the CLI command is executed.
Asynchronous publishing of CLI events—The CLI event is published, and then the CLI command is executed.
•![]() Asynchronous publishing of CLI events with command skipping—The CLI event is published, but the CLI command is not executed.
Asynchronous publishing of CLI events with command skipping—The CLI event is published, but the CLI command is not executed.
Counter Event Detector
The counter event detector publishes an event when a named counter crosses a specified threshold. There are two or more participants that affect counter processing. The counter event detector can modify the counter, and one or more subscribers define the criteria that cause the event to be published. After a counter event has been published, the counter monitoring logic can be reset to start monitoring the counter immediately or it can be reset when a second threshold—called an exit value—is crossed.
GOLD Event Detector
The GOLD event detector publishes an event when a GOLD failure event is detected on a specified card and subcard.
Interface Counter Event Detector
The interface counter event detector publishes an event when a generic Cisco IOS XE interface counter for a specified interface crosses a defined threshold. A threshold can be specified as an absolute value or an incremental value. If the incremental value is set to 50, for example, an event would be published when the interface counter increases by 50.
After an interface counter event has been published, the interface counter monitoring logic is reset using two methods. The interface counter is reset either when a second threshold—called an exit value—is crossed or when an elapsed period of time occurs.
None Event Detector
The none event detector publishes an event when the Cisco IOS XE event manager run CLI command executes an EEM policy. EEM schedules and runs policies on the basis of an event specification that is contained within the policy itself. An EEM policy must be identified and registered to be permitted to run manually before the event manager run command will execute.
OIR Event Detector
The online insertion and removal (OIR) event detector publishes an event when one of the following hardware insertion or removal events occurs:
•![]() A card is removed.
A card is removed.
•![]() A card is inserted.
A card is inserted.
Route Processors (RPs), line cards, or feature cards can be monitored for OIR events.
System Manager Event Detector
The system manager event detector generates events for Cisco IOS XE Software Modularity process start, normal or abnormal stop, and restart events. The events generated by the system manager allows policies to change the default behavior of the process restart.
Timer Event Detector
The timer event detector publishes events for the following four different types of timers:
•![]() An absolute-time-of-day timer publishes an event when a specified absolute date and time occurs.
An absolute-time-of-day timer publishes an event when a specified absolute date and time occurs.
•![]() A countdown timer publishes an event when a timer counts down to zero.
A countdown timer publishes an event when a timer counts down to zero.
•![]() A watchdog timer publishes an event when a timer counts down to zero and then the timer automatically resets itself to its initial value and starts to count down again.
A watchdog timer publishes an event when a timer counts down to zero and then the timer automatically resets itself to its initial value and starts to count down again.
•![]() A CRON timer publishes an event using a UNIX standard CRON specification to indicate when the event is to be published. A CRON timer never publishes events more than once per minute.
A CRON timer publishes an event using a UNIX standard CRON specification to indicate when the event is to be published. A CRON timer never publishes events more than once per minute.
Watchdog System Monitor (IOSWDSysMon) Event Detector for Cisco IOS XE
The Cisco IOS XE watchdog system monitor event detector publishes an event when one of the following occurs:
•![]() CPU utilization for a Cisco IOS XE task crosses a threshold.
CPU utilization for a Cisco IOS XE task crosses a threshold.
•![]() Memory utilization for a Cisco IOS XE task crosses a threshold.
Memory utilization for a Cisco IOS XE task crosses a threshold.

Note ![]() Cisco IOS XE processes are now referred to as tasks to distinguish them from Cisco IOS XE Software Modularity processes.
Cisco IOS XE processes are now referred to as tasks to distinguish them from Cisco IOS XE Software Modularity processes.
Two events may be monitored at the same time, and the event publishing criteria can be specified to require one event or both events to cross their specified thresholds.
Watchdog System Monitor (WDSysMon) Event Detector for Cisco IOS XE Software Modularity
The Cisco IOS XE Software Modularity watchdog system monitor event detector detects infinite loops, deadlocks, and memory leaks in Cisco IOS XE Software Modularity processes.
Embedded Event Manager Actions
The CLI-based corrective actions that are taken when event detectors report events enable a powerful on-device event management mechanism. Some EEM actions are available on every Cisco IOS XE release, but most EEM actions have been introduced in a specific release. For details of which EEM action is supported in each Cisco IOS XE release, see the EEM Actions Available by Cisco IOS XE Release concept in the "Writing Embedded Event Manager Policies Using the Cisco IOS XE CLI" or the "Writing Embedded Event Manager Policies Using Tcl" modules. EEM supports the following actions:
•![]() Executing a Cisco IOS XE command-line interface (CLI) command.
Executing a Cisco IOS XE command-line interface (CLI) command.
•![]() Setting or modifying a named counter.
Setting or modifying a named counter.
•![]() Requesting system information when an event occurs.
Requesting system information when an event occurs.
•![]() Sending a short e-mail.
Sending a short e-mail.
•![]() Manually running an EEM policy.
Manually running an EEM policy.
•![]() Publishing an application-specific event.
Publishing an application-specific event.
•![]() Generating an SNMP trap.
Generating an SNMP trap.
EEM action CLI commands contain an EEM action label that is a unique identifier that can be any string value. Actions are sorted and run in ascending alphanumeric (lexicographical) key sequence using the label as the sort key. If you are using numbers as labels be aware that alphanumerical sorting will sort 10.0 after 1.0, but before 2.0, and in this situation we recommend that you use numbers such as 01.0, 02.0, and so on, or use an initial letter followed by numbers.
Embedded Event Manager Environment Variables
EEM allows environment variables to be used in EEM policies. Tool Command Language (Tcl) allows global variables to be defined that are known to all procedures within a Tcl script. EEM allows environment variables to be defined using a CLI command, the event manager environment command, for use within an EEM policy. All EEM environment variables are automatically assigned to Tcl global variables before a Tcl script is run. There are three different types of environment variables associated with Embedded Event Manager:
•![]() User-defined—Defined by you if you create an environment variable in a policy that you have written.
User-defined—Defined by you if you create an environment variable in a policy that you have written.
•![]() Cisco-defined—Defined by Cisco for a specific sample policy.
Cisco-defined—Defined by Cisco for a specific sample policy.
•![]() Cisco built-in (available in EEM applets)—Defined by Cisco and can be read only or read/write. The read only variables are set by the system before an applet starts to execute. The single read/write variable, _exit_status, allows you to set the exit status at policy exit for policies triggered from synchronous events.
Cisco built-in (available in EEM applets)—Defined by Cisco and can be read only or read/write. The read only variables are set by the system before an applet starts to execute. The single read/write variable, _exit_status, allows you to set the exit status at policy exit for policies triggered from synchronous events.
Cisco-defined environment variables (see Table 2) and Cisco system-defined environment variables may apply to one specific event detector or to all event detectors. Environment variables that are user-defined or defined by Cisco in a sample policy are set using the event manager environment command. Variables that are used in the EEM policy must be defined before you register the policy. A Tcl policy contains a section called "Environment Must Define" that can be defined to check that any required environment variables are defined before the policy runs.
Cisco built-in environment variables are a subset of the Cisco-defined environment variables and the built-in variables are available to EEM applets only. The built-in variables can be read-only or can be read and write, and these variables may apply to one specific event detector or to all event detectors. For more details and a table listing the Cisco system-defined variables, see the ""Writing Embedded Event Manager Policies Using the Cisco IOS XE CLI" module.

Note ![]() Cisco-defined environment variables begin with an underscore character (_). We strongly recommend that customers avoid the same naming convention to prevent naming conflicts.
Cisco-defined environment variables begin with an underscore character (_). We strongly recommend that customers avoid the same naming convention to prevent naming conflicts.
Table 2 describes the Cisco-defined variables used in the sample EEM policies. Some of the environment variables do not have to be specified for the corresponding sample policy to run and these are marked as optional.
|
|
|
|
|---|---|---|
_config_cmd1 |
The first configuration command that is executed. |
interface fastEthernet1/0 |
_config_cmd2 |
(Optional) The second configuration command that is executed. |
no shutdown |
_crash_reporter_debug |
(Optional) A value that identifies whether debug information for tm_crash_reporter.tcl will be enabled. |
1 |
_crash_reporter_url |
The URL location to which the crash report is sent. |
http://www.yourdomain.com/ |
_cron_entry |
A CRON specification that determines when the policy will run. See the "Writing Embedded Event Manager Policies Using Tcl" module for more information about how to specify a cron entry. |
0-59/1 0-23/1 * * 0-7 |
_email_server |
A Simple Mail Transfer Protocol (SMTP) mail server used to send e-mail. |
mailserver.yourdomain.com |
_email_to |
The address to which e-mail is sent. |
engineer@yourdomain.com |
_email_from |
The address from which e-mail is sent. |
devtest@yourdomain.com |
_email_cc |
The address to which the e-mail is be copied. |
manager@yourdomain.com |
_show_cmd |
The CLI show command to be executed when the policy is run. |
show version |
_syslog_pattern |
A regular expression pattern match string that is used to compare syslog messages to determine when the policy runs. |
.*UPDOWN.*FastEthernet |
_tm_fsys_usage_cron |
(Optional) A CRON specification that is used in the event_register keyword extension. If unspecified, the _tm_fsys_usage.tcl policy is triggered once per minute. |
0-59/1 0-23/1 * * 0-7 |
_tm_fsys_usage_debug |
(Optional) When this variable is set to a value of 1, disk usage information is displayed for all entries in the system. |
1 |
_tm_fsys_usage_ |
(Optional) Free byte threshold for systems or specific prefixes. If free space falls below a given value, a warning is displayed. |
disk2:98000000 |
_tm_fsys_usage_percent |
(Optional) Disk usage percentage thresholds for systems or specific prefixes. If disk usage percentage exceeds a given percentage, a warning is displayed. If unspecified, the default disk usage percentage is 80 percent for all systems. |
nvram:25 disk2:5 |
Embedded Event Manager Policy Creation
EEM is a policy driven process in which the EEM policy engine receives notifications when faults and other events occur in the Cisco IOS XE software system. Embedded Event Manager policies implement recovery based on the current state of the system and the actions specified in the policy for a given event. Recovery actions are triggered when the policy is run.
Although there are some EEM CLI configuration and show commands, EEM is implemented through the creation of policies. An EEM policy is an entity that defines an event and the actions to be taken when that event occurs. There are two types of EEM policies: an applet or a script. An applet is a simple form of policy that is defined within the CLI configuration. A script is a form of policy that is written in Tcl.
The creation of an EEM policy involves:
•![]() Selecting the event for which the policy is run.
Selecting the event for which the policy is run.
•![]() Defining the event detector options associated with logging and responding to the event.
Defining the event detector options associated with logging and responding to the event.
•![]() Defining the environment variables, if required.
Defining the environment variables, if required.
•![]() Choosing the actions to be performed when the event occurs.
Choosing the actions to be performed when the event occurs.
There are two ways to create an EEM policy. The first method is to write applets using CLI commands, and the second method is to write Tcl scripts. Cisco provides enhancements to Tcl in the form of Tcl command extensions that facilitate the development of EEM policies. Scripts are defined off the networking device using an ASCII editor. The script is then copied to the networking device and registered with EEM. When a policy is registered with the Embedded Event Manager, the software examines the policy and registers it to be run when the specified event occurs. Policies can be unregistered or suspended. Both types of policies can be used to implement EEM in your network.
For details on writing EEM policies using the Cisco IOS XE CLI, go to "Writing Embedded Event Manager Policies Using the Cisco IOS XE CLI" module.
For details on writing EEM policies using Tcl, go to "Writing Embedded Event Manager Policies Using Tcl" module.
Where to Go Next
•![]() If you want to write EEM policies using the Cisco IOS XE CLI, see the "Writing Embedded Event Manager Policies Using the Cisco IOS XE CLI" module.
If you want to write EEM policies using the Cisco IOS XE CLI, see the "Writing Embedded Event Manager Policies Using the Cisco IOS XE CLI" module.
•![]() If you want to write EEM policies using Tcl, see the "Writing Embedded Event Manager Policies Using Tcl" module.
If you want to write EEM policies using Tcl, see the "Writing Embedded Event Manager Policies Using Tcl" module.
Additional References
The following sections provide references related to EEM.
Related Documents
|
|
|
|---|---|
Network Management commands (including EEM commands): complete command syntax, defaults, command mode, command history, usage guidelines, and examples |
Standards
|
|
|
|---|---|
No new or modified standards are supported, and support for existing standards has not been modified. |
— |
MIBs
|
|
|
|---|---|
CISCO-EMBEDDED-EVENT-MGR-MIB |
To locate and download MIBs for selected platforms, Cisco IOS XE releases, and feature sets, use Cisco MIB Locator found at the following URL: |
RFCs
|
|
|
|---|---|
No new or modified RFCs are supported, and support for existing RFCs has not been modified. |
— |
Technical Assistance
Feature Information for Embedded Event Manager Overview
Table 3 lists the features in this module and provides links to specific configuration information.
Not all commands may be available in your Cisco IOS XE software release. For release information about a specific command, see the command reference documentation.
Use Cisco Feature Navigator to find information about platform support and software image support. Cisco Feature Navigator enables you to determine which Cisco IOS XE software images support a specific software release, feature set, or platform. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.

Note ![]() Table 3 lists only the Cisco IOS XE software release that introduced support for a given feature in a given Cisco IOS XE software release train. Unless noted otherwise, subsequent releases of that Cisco IOS XE software release train also support that feature.
Table 3 lists only the Cisco IOS XE software release that introduced support for a given feature in a given Cisco IOS XE software release train. Unless noted otherwise, subsequent releases of that Cisco IOS XE software release train also support that feature.
|
|
|
|
|---|---|---|
Embedded Event Manager 2.0 |
Cisco IOS XE Release 2.1 |
EEM 2.0 introduced the application-specific event detector, the counter event detector, the interface counter event detector, the timer event detector, and the IOSWDSysMon event detector. New actions include setting and modifying a named counter, publishing an application-specific event, and generating an SNMP trap. The ability to define environment variables and to run a sample EEM policy (included in the software) written using Tcl was introduced. The following sections provide information about this feature: • • • The following commands were introduced by this feature: action counter, action publish-event, action snmp-trap, event application, event counter, event interface, event ioswdsysmon, event manager environment, event manager history size, event manager policy, event manager scheduler suspend, event timer, show event manager environment, show event manager history events, show event manager history traps, show event manager policy available, show event manager policy pending. |
Embedded Event Manager 2.1 |
Cisco IOS XE Release 2.1 |
EEM 2.1 introduced some new event detectors and actions with new functionality to allow EEM policies to be run manually and the ability to run multiple concurrent policies. Support for Simple Network Management Protocol (SNMP) event detector rate-based events was provided as was the ability to create policies using Tool Command Language (Tcl). The following sections provide information about this feature: • • • The following commands were introduced or modified by this feature: action cli, action counter, action info, action mail, action policy, debug event manager, event cli, event manager directory user, event manager policy, event manager run, event manager scheduler script, event manager session cli username, event none, event oir, event snmp, event syslog, set (EEM), show event manager directory user, show event manager policy registered, show event manager session cli username. |
Embedded Event Manager 2.1 (Software Modularity) |
Cisco IOS XE Release 2.1 |
EEM 2.1 for Software Modularity images introduced the GOLD, system manager, and WDSysMon (Cisco IOS XE Software Modularity watchdog) event detectors, and the ability to display Cisco IOS XE Software Modularity processes and process metrics. Note The following sections provide information about this feature: • • • • The following commands were introduced by this feature: event gold, event process, show event manager metric process. Note |
Embedded Event Manager 2.2 |
Cisco IOS XE Release 2.1 |
EEM 2.2 introduced the enhanced object tracking, resource, and RF event detectors. The actions of reading and setting the state of a tracked object were also introduced. The following sections provide information about this feature: • • • The following commands were introduced or modified by this feature: action track read, action track set, default-state, event resource, event rf, event track, show track, track stub-object. |
Embedded Event Manager 2.3 |
Cisco IOS XE Release 2.1 |
EEM 2.3 introduced some new features relative to the Generic Online Diagnostics (GOLD) Event Detector on the Cisco Catalyst 6500 Series switches. Note The following sections provide information about this feature: • • • The event gold command was enhanced in addition to the Tcl keywords—action-notify, testing-type, test-name, test-id, consecutive-failure, platform-action, and maxrun—for improved reaction to GOLD test failures and conditions. |
 Feedback
Feedback