Security Suite Settings on 300 Series Managed Switches
Available Languages
Objective
The Security Suite on the Cisco 300 Series Managed Switches offer protection from Denial of Service (DoS) attacks. DoS attacks flood networks with false traffic, which makes network server resources unavailable or unresponsive to legitimate users. Generally, there are two types of DoS attacks. Brute force DoS attacks flood the server and consume server and network bandwidth. Systematic attacks manipulate protocols vulnerabilities like TCP SYN message to crash systems. This article explains the settings available in the Security Suite on the 300 Series Managed Switches.
Note: Access Control Lists (ACLs) and advanced QoS policies are not active on a port when DoS attack protection is enabled.
Applicable Devices
• SF/SG 300 Series Managed Switches
Software Version
• 1.3.0.62
Security Suite Settings Configuration
Step 1. Log in to the web configuration utility and choose Security > Denial of Service Prevention > Security Suite Settings. The Security Suite Settings page opens:
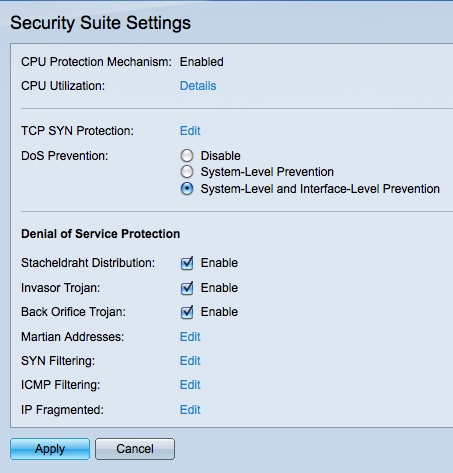
Note: CPU protection mechanism is enabled by default on 300 Series Managed Switches and cannot be disabled. The switch uses Secure Core Technology (SCT), which allows the switch to handle management and protocol traffic no matter how much total traffic is received.
Step 2. (Optional) Click Details in the CPU Utilization field to view the CPU utilization. Refer to the article CPU Utilization on 200/300 Series Managed Switches for more information.
Step 3. (Optional) Click Edit in the TCP SYN Protection field to edit the TCP SYN Protection settings. Refer to the article Synchronize (SYN) Filtering Configuration on the 300 Series Managed Switches for more information.
Step 4. In the DoS Prevention field, click the radio button that corresponds to the method of DoS prevention you would like to employ. The available options are:
• Disable — Disable DoS protection feature. If Disable is chosen, skip to Step 13.
• System - Level-Prevention — Enables DoS protection features which protect from Invasor Trojan, Stacheldraht Distribution, Back Orifice Trojan, and Martian Addresses.
• System - Level-Prevention and Interface-Level Protection — Enables all security measures defined in the Denial of Service Protection area.
Step 5. Check the Enable check box in the Stacheldraht Distribution field to discard TCP packets with a source TCP port number of 16660.
Step 6. Check the Enable check box in the Invasor Trojan field to discard TCP packets with a destination TCP port of 2140 and a source TCP port of 1024.
Step 7. Check the Enable check box in the Back Orifice Trojan field to discard UDP packets with a destination UDP port equal to 31337 and a source UDP port of 1024.
Note: While there are hundreds of DoS attacks, the ports mentioned above are commonly exploited for malicious activity. However, they are also used for legitimate traffic as well. If you have a device that uses any of the above ports, that information will be blocked.
Step 8. Click Edit in the Martian Addresses field to edit the Martian Addresses Table. The Martian Addresses Table discards packets from select IP addresses. To edit the list of Martian addresses, refer to the article Denial of Service (DoS) Martian Address Configuration on 300 Series Managed Switches.
Note: Steps 9-12 require System-Level and Interface-Level Prevention be chosen at Step 4. Skip to Step 13 if you have chosen another DoS prevention type.
Step 9. Click Edit in the SYN Filtering field to allow the administrator to block certain TCP ports. To configure SYN Filtering, refer to the article Denial of Service (DoS) SYN Filtering Configuration on 300 Series Managed Switches.
Step 10. Click Edit in the SYN Rate Protection field to limit the number of SYN packets received. To configure SYN Rate Protection, refer to the article SYN Rate Protection on 300 Series Managed Switches.
Step 11. Click Edit in the ICMP Filtering field to allow ICMP packets from certain sources to be blocked. To configure ICMP Filtering, refer to the article Internet Control Message Protocol (ICMP) Filtering Configuration on the 300 Series Managed Switches.
Step 12. Click Edit in the IP Fragmented field to block fragmented IP packets. To configure IP Fragments Filtering, refer to the article Denial of Service (DoS) IP Fragments Filtering Configuration on 300 Series Managed Switches.
Step 13. Click Apply to save changes or click Cancel to cancel your changes.
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
10-Dec-2018
|
Initial Release |
 Feedback
Feedback