Introduction
This document describes the Transport Layer Security (TLS) Session Resumption in Cisco Identity Services Engine (ISE).
Prerequisites
Requirements
- Knowledge of Transport Layer Security (TLS) handshake process.
- Knowledge of Protected Extensible Authentication Protocol (PEAP) flow
- Knowledge of Cisco Identity Services Engine
Components Used
The information in this document is based on these software and hardware versions
- Cisco Identity Services Engine 3.2
- ISE Virtual Machine (VM)
- Windows 10 PC
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, ensure that you understand the potential impact of any command.
Background Information
TLS session resumption is a technique used to eliminate the overhead of the initial TLS handshake. It allows a client and server who have previously established a TLS session to resume that session without repeating the resource-intensive handshake process.
Advantages
- It reduces the latency by avoiding the resource-intensive steps of the initial handshake and the time required to do that.
- It also reduces the computational load on the server by skipping the intensive key exchange and certificate validation processes.
Configure
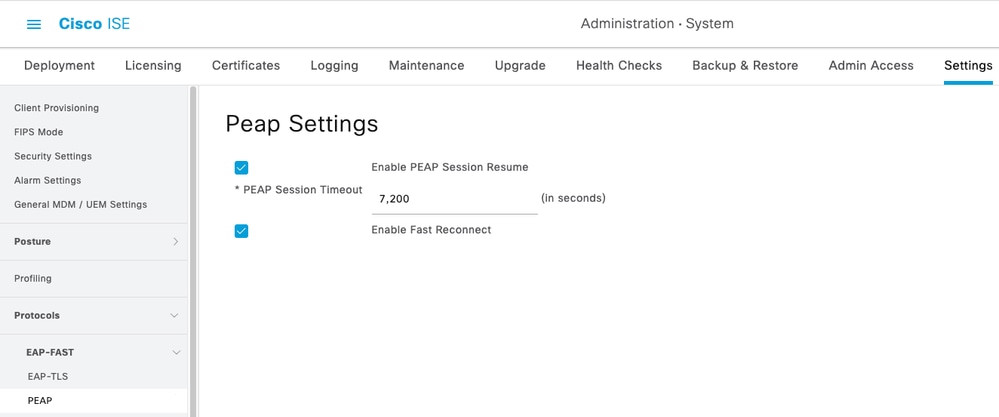
On ISE, to enable the TLS session, resume for PEAP:
Administration > System > Settings > Protocols > PEAP > check the Enable PEAP Session Resume
By default, ISE holds the session for 7200 Seconds.
Optionally, you can enable the Enable Fast Reconnect, which in turns bypasses the inner method of PEAP and allows even faster reauthentication. It is desirable in applications such as wireless roaming.
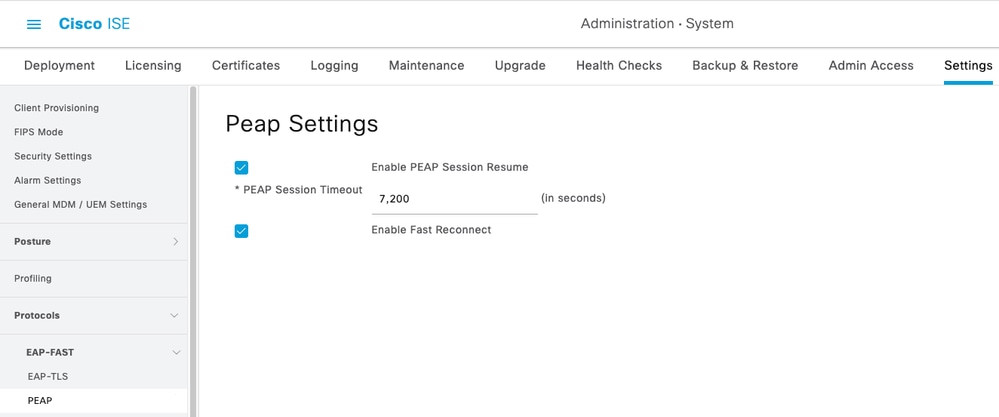 ISE PEAP Session Resume Config
ISE PEAP Session Resume Config
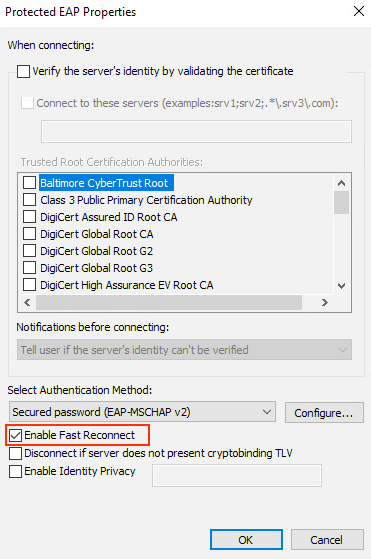
The Fast Reconnect must also be enabled in the supplicant.
This configuration is for Windows native supplicant to enable Fast Reconnect.
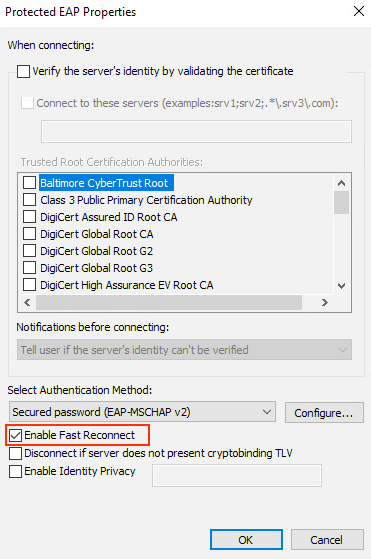 Windows 10 Supplicant Config
Windows 10 Supplicant Config
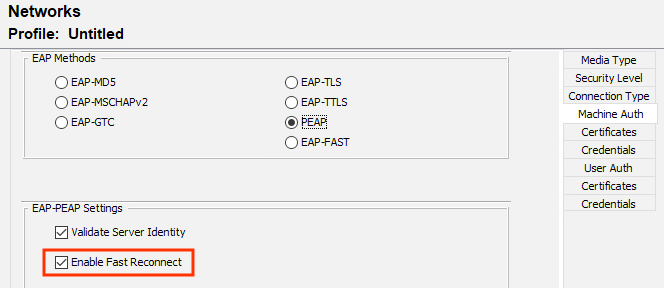
This configuration is for AnyConnect Network Access Module (NAM) profile editor to enable Fast Reconnect.
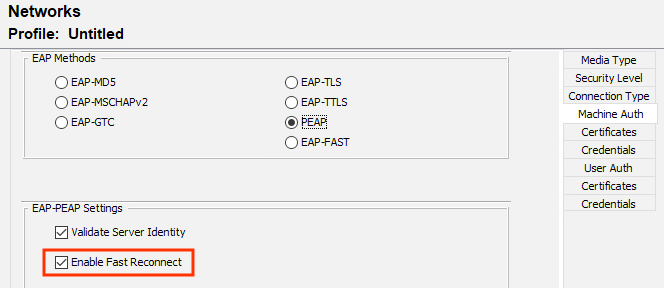 AnyConnect NAM Config
AnyConnect NAM Config
Verify
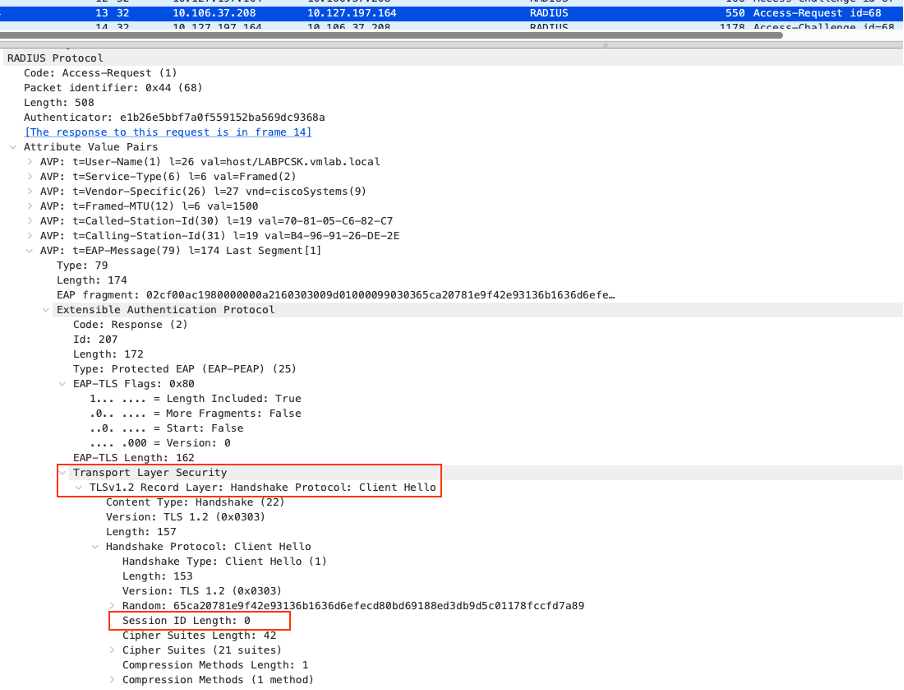
Initial Authentication
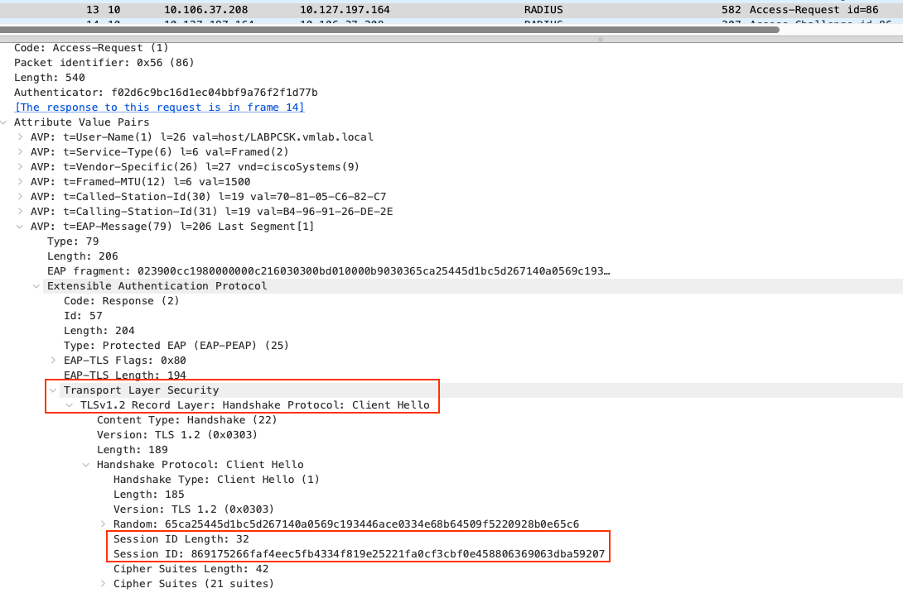
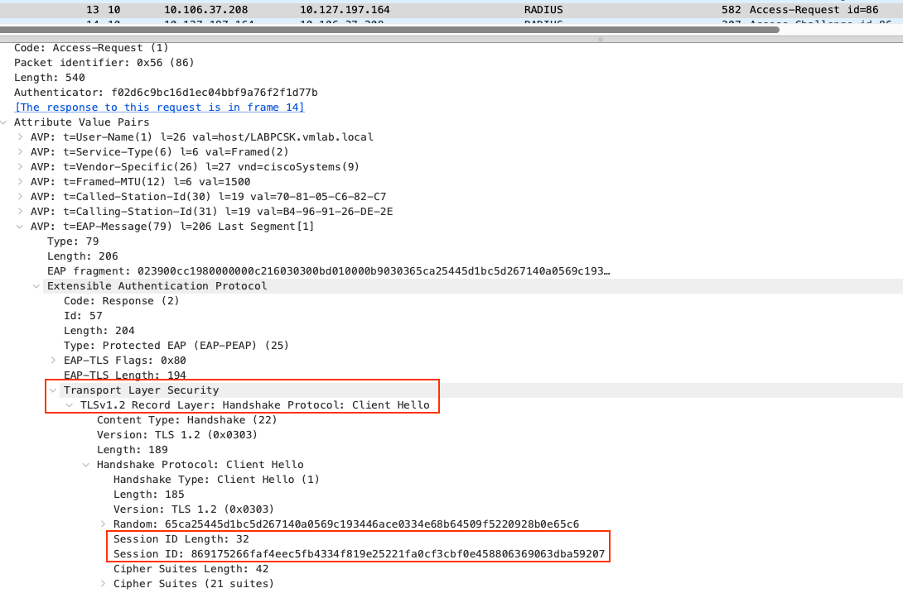
In the initial PEAP authentication, you can see that the Session ID field is blank in the Client Hello during the TLS handshake.
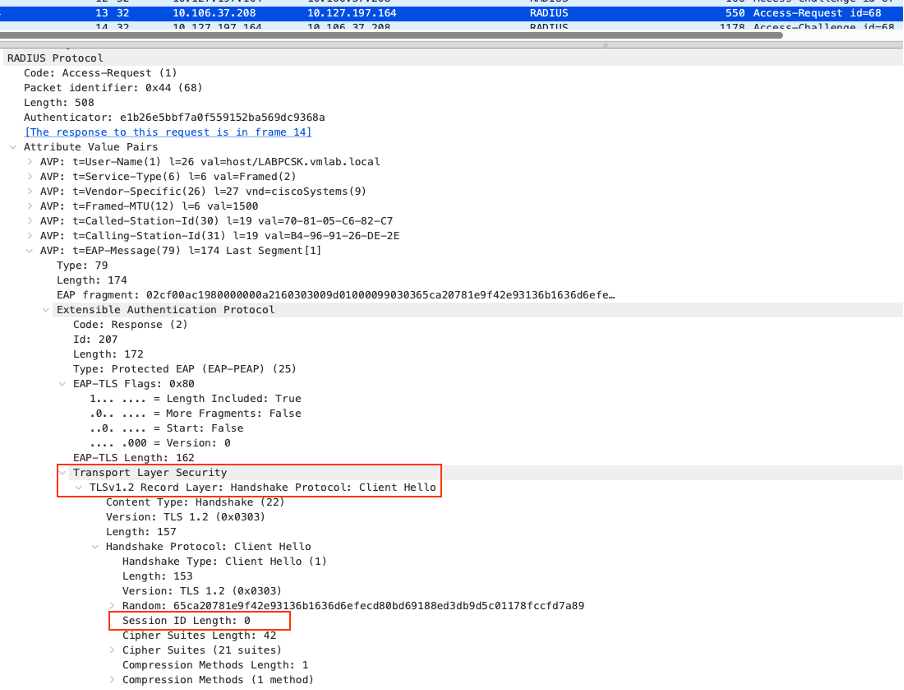 Initial TLS Handshake
Initial TLS Handshake
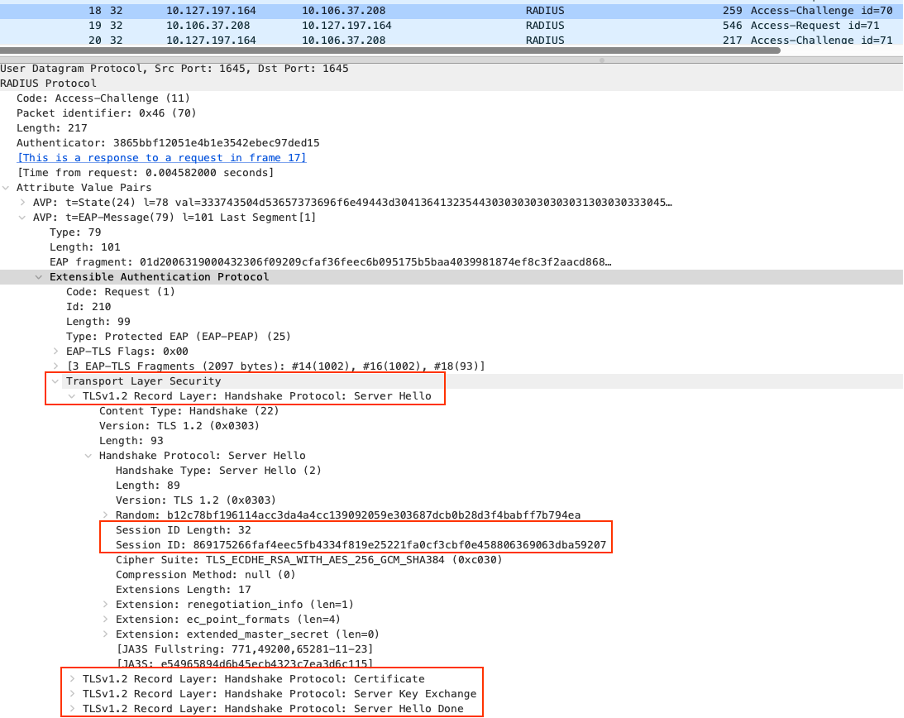
ISE responds with the Server Hello, which includes a Session ID 869175266faf4eec5fb4334f819e25221fa0cf3cbf0e458806369063dba59207 along with the certificate and Server Key.
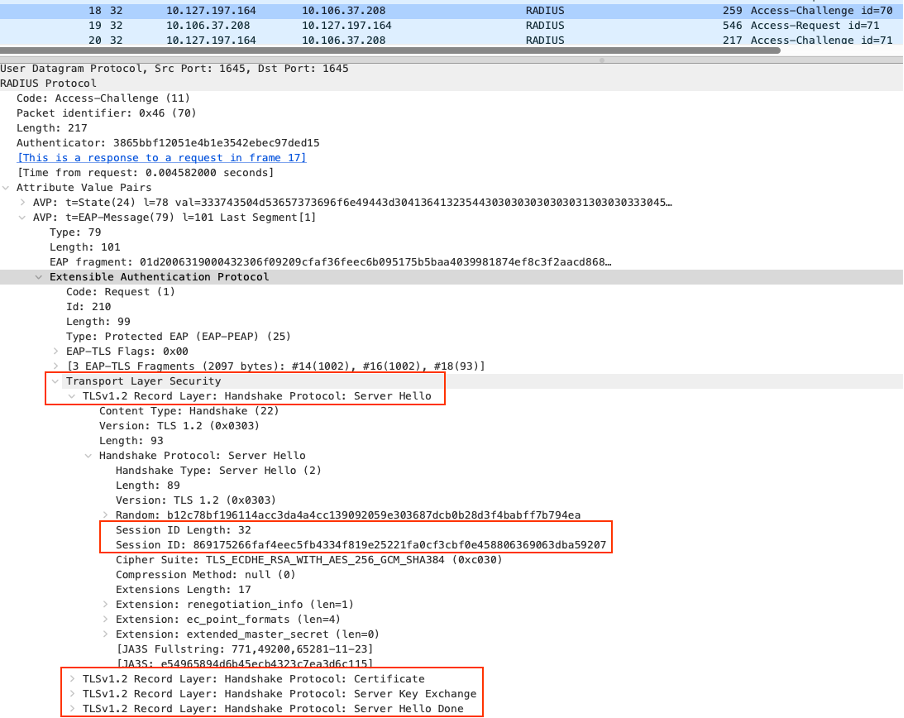 Initial Server Hello with Session ID
Initial Server Hello with Session ID
In the prrt-server.log, you can see the handshake messages along with the session ID, and that it has been preserved in the cache.
Crypto,2024-02-12 19:13:20,542,DEBUG,0x7f8f923fc700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS LOG: where: (0x2001), ssl state (0x14), ret: 1, long string: SSLv3/TLS read client hello,SSLConnection.cpp:4495
Crypto,2024-02-12 19:13:20,542,DEBUG,0x7f8f923fc700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS log: TLS_NOTIFY received client hello message,SSLConnection.cpp:4498
Crypto,2024-02-12 19:13:20,542,DEBUG,0x7f8f923fc700,NIL-CONTEXT,Crypto::Result=0, Call TLS Notify Callback, event 5,SSLConnection.cpp:4510
Eap,2024-02-12 19:13:20,542,DEBUG,0x7f8f923fc700,cntx=0000452308,sesn=labpan01/494696177/7940,CPMSessionID=0A6A25D0000000100030EDBC,user=host/LABPCSK.vmlab.local,CallingStationID=B4-96-91-26-DE-2E,FramedIPAddress=10.106.37.25,CLIENT HELLO, new session,EapTlsProtocol.cpp:1463
Eap,2024-02-12 19:13:20,542,DEBUG,0x7f8f923fc700,cntx=0000452308,sesn=labpan01/494696177/7940,CPMSessionID=0A6A25D0000000100030EDBC,user=host/LABPCSK.vmlab.local,CallingStationID=B4-96-91-26-DE-2E,FramedIPAddress=10.106.37.25,Session id
0000: 86 91 75 26 6f af 4e ec 5f b4 33 4f 81 9e 25 22 ..u&o.N._.3O..%"
0010: 1f a0 cf 3c bf 0e 45 88 06 36 90 63 db a5 92 07 ...<..E..6.c.... ,EapTlsProtocol.cpp:1473
Crypto,2024-02-12 19:13:20,542,DEBUG,0x7f8f923fc700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS LOG: where: (0x2001), ssl state (0x16), ret: 1, long string: SSLv3/TLS write server hello,SSLConnection.cpp:4495
Crypto,2024-02-12 19:13:20,542,DEBUG,0x7f8f923fc700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS log: TLS_NOTIFY sent server hello message,SSLConnection.cpp:4498
Crypto,2024-02-12 19:13:20,542,DEBUG,0x7f8f923fc700,NIL-CONTEXT,Crypto::Result=0, Call TLS Notify Callback, event 9,SSLConnection.cpp:4510
Crypto,2024-02-12 19:13:20,543,DEBUG,0x7f8f923fc700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS LOG: where: (0x2001), ssl state (0x17), ret: 1, long string: SSLv3/TLS write certificate,SSLConnection.cpp:4495
Crypto,2024-02-12 19:13:20,543,DEBUG,0x7f8f923fc700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS log: TLS_NOTIFY sent server certificate,SSLConnection.cpp:4498
Crypto,2024-02-12 19:13:20,543,DEBUG,0x7f8f923fc700,NIL-CONTEXT,Crypto::Result=0, Call TLS Notify Callback, event 11,SSLConnection.cpp:4510
Crypto,2024-02-12 19:13:20,581,DEBUG,0x7f8f923fc700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS LOG: where: (0x2001), ssl state (0x18), ret: 1, long string: SSLv3/TLS write key exchange,SSLConnection.cpp:4495
Crypto,2024-02-12 19:13:20,581,DEBUG,0x7f8f923fc700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS log: TLS_NOTIFY sent server key exchange message,SSLConnection.cpp:4498
Crypto,2024-02-12 19:13:20,581,DEBUG,0x7f8f923fc700,NIL-CONTEXT,Crypto::Result=0, Call TLS Notify Callback, event 13,SSLConnection.cpp:4510
Crypto,2024-02-12 19:13:20,581,DEBUG,0x7f8f923fc700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS LOG: where: (0x2001), ssl state (0x1a), ret: 1, long string: SSLv3/TLS write server done,SSLConnection.cpp:4495
Crypto,2024-02-12 19:13:20,581,DEBUG,0x7f8f923fc700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS log: TLS_NOTIFY sent server done message,SSLConnection.cpp:4498
Crypto,2024-02-12 19:13:20,737,DEBUG,0x7f8f91df9700,NIL-CONTEXT,shutting session id
0000: 86 91 75 26 6f af 4e ec 5f b4 33 4f 81 9e 25 22 ..u&o.N._.3O..%"
0010: 1f a0 cf 3c bf 0e 45 88 06 36 90 63 db a5 92 07 ...<..E..6.c.... ,SSLConnection.cpp:337
Crypto,2024-02-12 19:13:20,737,DEBUG,0x7f8f91df9700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.pvDone - session is being preserved in cache,SSLConnection.cpp:355
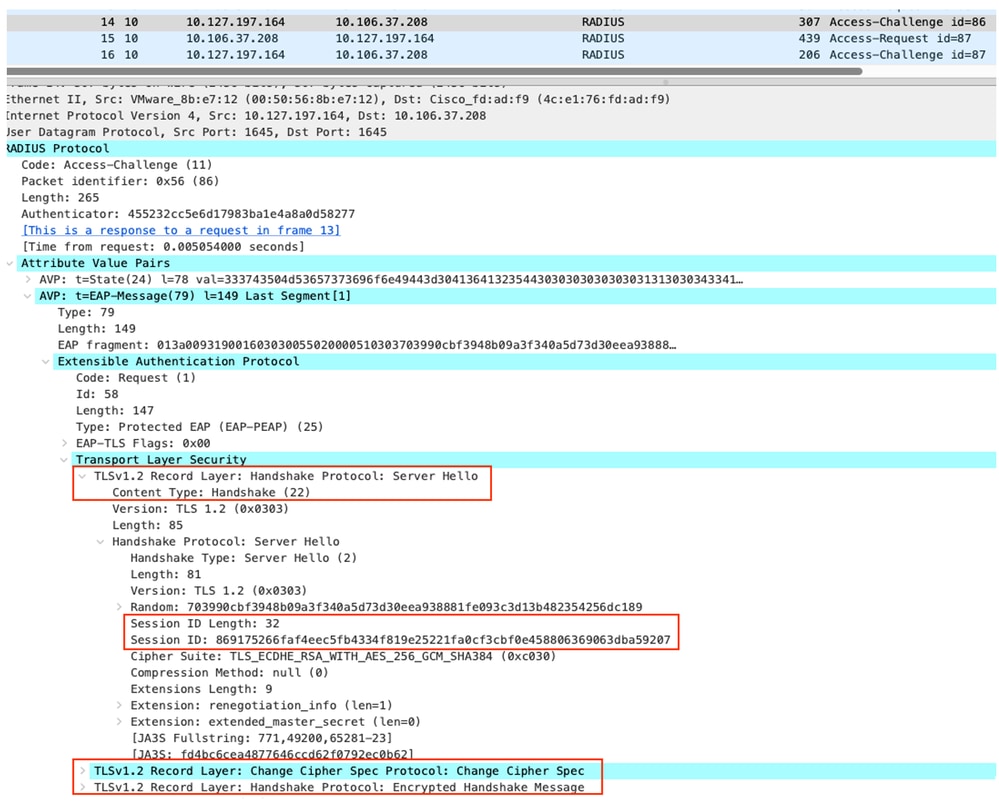
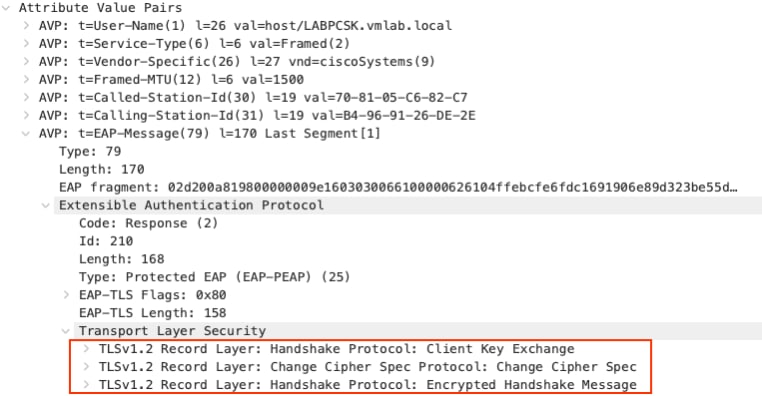
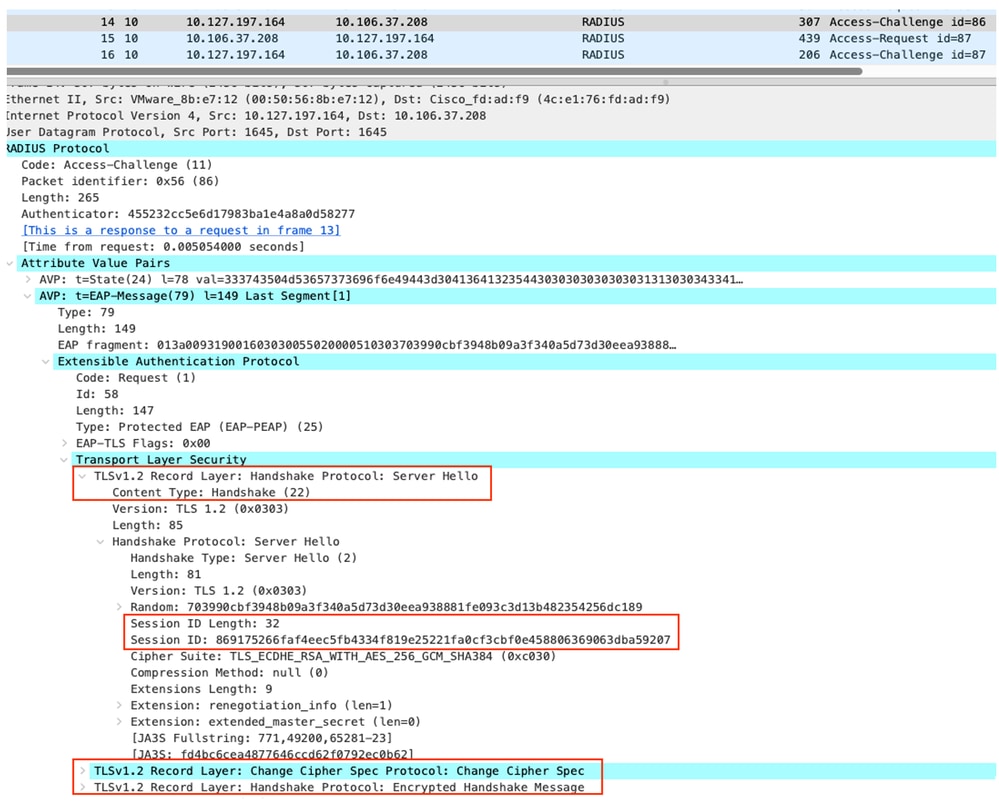
Next, client responds with the Client Key Exchange and Change Cipher Spec.
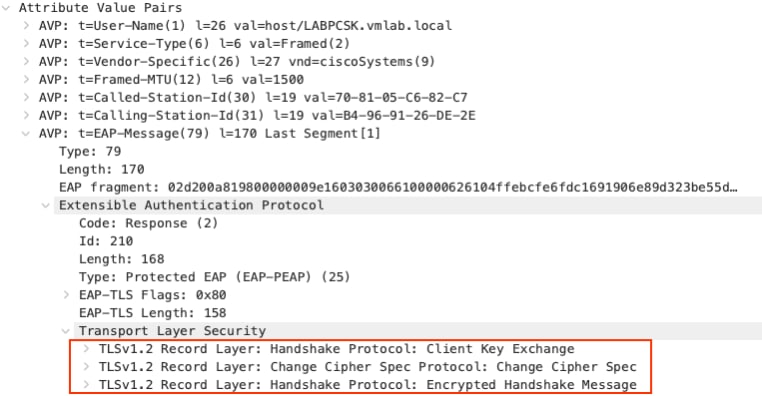 Client Key Exchange and Other Attributes
Client Key Exchange and Other Attributes
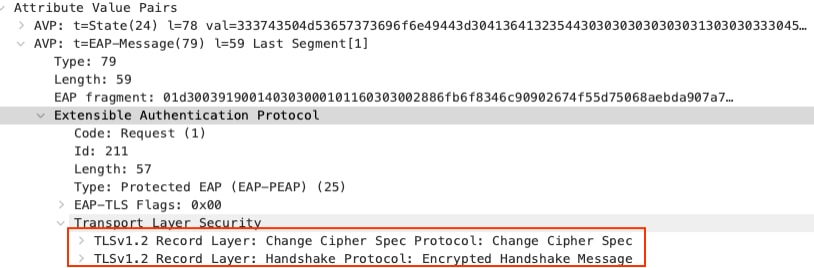
Finally, the server also responds with the Change Cipher Specs and the TLS handshake is completed.
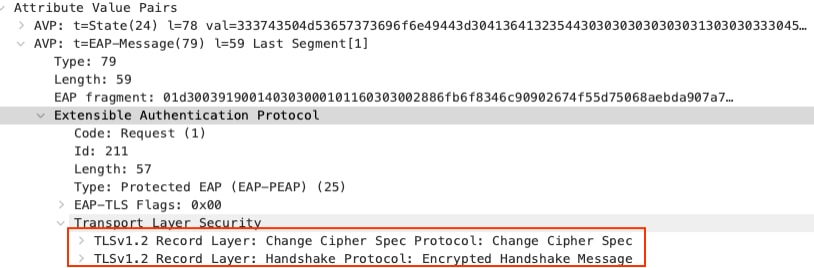 Change Cipher Spec from Server Side
Change Cipher Spec from Server Side
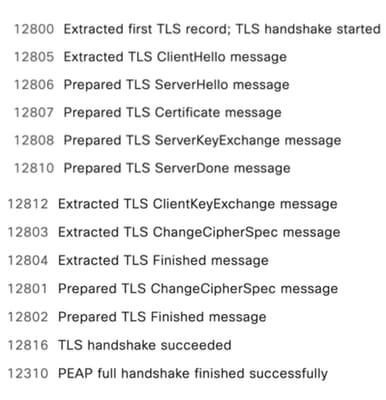
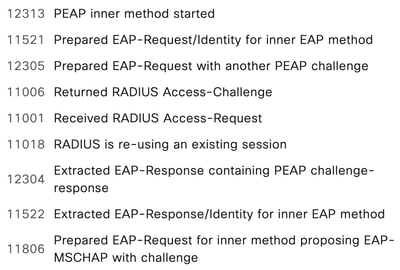
In the RADIUS live log steps, you can see that the full TLS handshake happens during the first authentication.
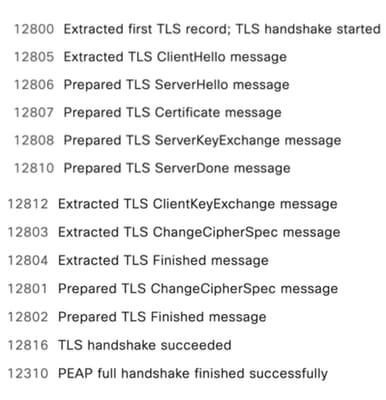 RADIUS Live Log TLS Handshake Steps
RADIUS Live Log TLS Handshake Steps
Inner method also performs the full Microsoft Challenge Handshake Authentication Protocol (MSCHAPv2) authentication.
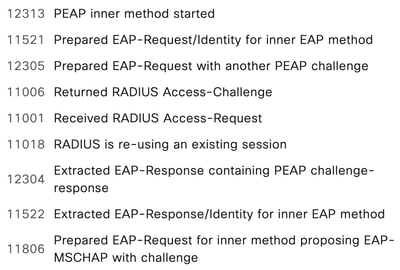 RADIUS Live Log Inner Method Steps
RADIUS Live Log Inner Method Steps
During Reauthentication
During re-authentication, the client sends the same session ID 869175266faf4eec5fb4334f819e25221fa0cf3cbf0e458806369063dba59207 in the Client Hello which has learned from the initial authentication.
 Client Hello During Session Resume
Client Hello During Session Resume
ISE then confirms this session ID is present in Secure Socket Layer (SSL) Session cache and they both go through what is known as abbreviated TLS handshake. No certificate or key information is exchanged during abbreviated TLS handshake and previously negotiated keys are re-used.
 Server Hello in Session Resume
Server Hello in Session Resume
In the prrt-server.log, you can see that after receiving the Client Hello, ISE confirmed that the session is being reused and skips the certificate and key exchange.
Crypto,2024-02-12 19:33:48,821,DEBUG,0x7f8f925fd700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS LOG: where: (0x2001), ssl state (0x14), ret: 1, long string: SSLv3/TLS read client hello,SSLConnection.cpp:4495
Crypto,2024-02-12 19:33:48,821,DEBUG,0x7f8f925fd700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS log: TLS_NOTIFY received client hello message,SSLConnection.cpp:4498
Crypto,2024-02-12 19:33:48,821,DEBUG,0x7f8f925fd700,NIL-CONTEXT,Crypto::Result=0, Call TLS Notify Callback, event 5,SSLConnection.cpp:4510
Eap,2024-02-12 19:33:48,821,DEBUG,0x7f8f925fd700,cntx=0000452772,sesn=labpan01/494696177/7949,CPMSessionID=0A6A25D0000000110043ACB0,user=host/LABPCSK.vmlab.local,CallingStationID=B4-96-91-26-DE-2E,FramedIPAddress=10.106.37.25,CLIENT HELLO, session reused,EapTlsProtocol.cpp:1463
Eap,2024-02-12 19:33:48,821,DEBUG,0x7f8f925fd700,cntx=0000452772,sesn=labpan01/494696177/7949,CPMSessionID=0A6A25D0000000110043ACB0,user=host/LABPCSK.vmlab.local,CallingStationID=B4-96-91-26-DE-2E,FramedIPAddress=10.106.37.25,Session id
0000: 86 91 75 26 6f af 4e ec 5f b4 33 4f 81 9e 25 22 ..u&o.N._.3O..%"
0010: 1f a0 cf 3c bf 0e 45 88 06 36 90 63 db a5 92 07 ...<..E..6.c.... ,EapTlsProtocol.cpp:1473
Crypto,2024-02-12 19:33:48,821,DEBUG,0x7f8f925fd700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS LOG: where: (0x2001), ssl state (0x16), ret: 1, long string: SSLv3/TLS write server hello,SSLConnection.cpp:4495
Crypto,2024-02-12 19:33:48,821,DEBUG,0x7f8f925fd700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS log: TLS_NOTIFY sent server hello message,SSLConnection.cpp:4498
Crypto,2024-02-12 19:33:48,821,DEBUG,0x7f8f925fd700,NIL-CONTEXT,Crypto::Result=0, Call TLS Notify Callback, event 9,SSLConnection.cpp:4510
Crypto,2024-02-12 19:33:48,821,DEBUG,0x7f8f925fd700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS LOG: where: (0x2001), ssl state (0x23), ret: 1, long string: SSLv3/TLS write change cipher spec,SSLConnection.cpp:4495
Crypto,2024-02-12 19:33:48,821,DEBUG,0x7f8f925fd700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS log: TLS_NOTIFY sent change cipher spec message,SSLConnection.cpp:4498
Crypto,2024-02-12 19:33:48,821,DEBUG,0x7f8f925fd700,NIL-CONTEXT,Crypto::Result=0, Call TLS Notify Callback, event 1,SSLConnection.cpp:4510
Crypto,2024-02-12 19:33:48,821,DEBUG,0x7f8f925fd700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS LOG: where: (0x2001), ssl state (0x24), ret: 1, long string: SSLv3/TLS write finished,SSLConnection.cpp:4495
Crypto,2024-02-12 19:33:48,821,DEBUG,0x7f8f925fd700,NIL-CONTEXT,Crypto::Result=0, Crypto.SSLConnection.tlsNotifyLog - TLS log: TLS_NOTIFY sent finished message (server is ready to finish handshake),SSLConnection.cpp:4498
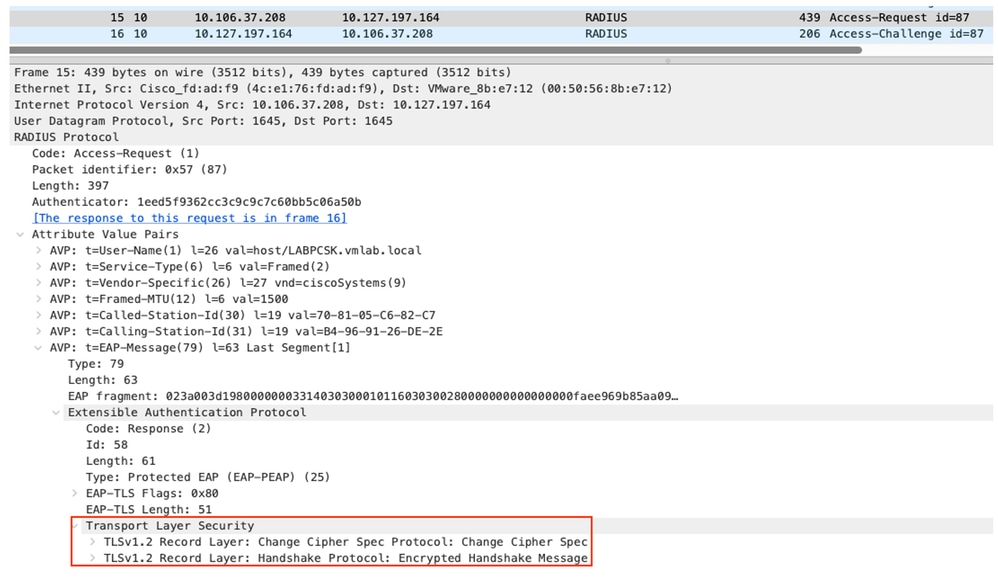
Finally, Client also responds with change cipher specs and TLS handshake gets completed.
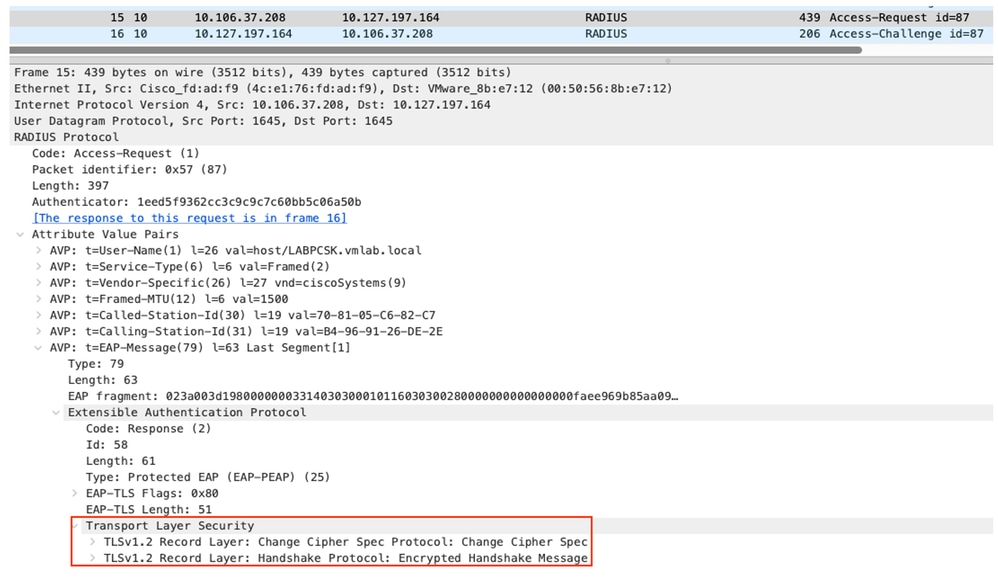 Client Change Cipher Spec Session Resume
Client Change Cipher Spec Session Resume
In the RADIUS live log steps, you can see that the abbreviated TLS handshake happens during the re-authentication.
 RADIUS Live Log TLS Session Resume Steps
RADIUS Live Log TLS Session Resume Steps
In re-authentication, you can see that the inner method get skipped.
 RADIUS Live Log PEAP Fast Reconnect
RADIUS Live Log PEAP Fast Reconnect
Frequently Asked Questions
1) Are Session Resume and Fast Reconnect independent of each other?
Yes, Fast Reconnect is an optional feature where the Inner method of authentication get bypassed. It is not mandatory to enable the Fast Reconnect when Session Resume is enabled.
2) Does enabling session resume cause any security risk?
The server assigns a random session ID during the initial handshake with the browser (client). Client and server store this session ID along with the session keys and connection states. To resume a session, the client sends the stored session ID with the first protocol message (ClientHello) to the server. If the server recognizes the connection and is willing to resume the session, it replies with the same session ID to re-establish the respective session. This allows a secure connection to be established quickly and with no loss of security since you are reusing the previously negotiated session data.
3) Do the TLS session IDs replicate to other nodes?
No, the TLS session IDs store on the PSN itself. It does not replicate to other PSNs. In case of Reboot or Service restart of the PSN, all the session IDs can be lost from cache and the next time full TLS handshake must happen.



 Feedback
Feedback