What is the purpose of endpoint analytics?
As organizations undergo digital transformation, they're adding more and more devices to their networks. Studies indicate that endpoints--both user and IoT (Internet of Things) devices--are projected to grow in number exponentially in the foreseeable future.
IoT devices present management and security challenges. Not only are they proliferating, but some are added in an ad hoc manner outside of IT's controlled environment, without an overall plan and with minimal security provisions. Others may have been added years ago, obtained from vendors that don't scrupulously keep their software updated. All these conditions can increase the threat surface. In 2019, Cisco's Talos Security Research Team published 87 advisories about IoT, 23% more advisories than the next-largest category, desktop computing.
There is growing evidence that bad actors are taking advantage of these weaknesses. The number of cyber attacks on IoT devices surged by more than 300% in 2019 (Melissa Michael, Attack Landscape H1 2019: IoT, SMB Traffic Abounds, December 2019), and over 75% of vulnerabilities discovered in 2019 were from IoT devices (Martin Zeisser, Talos Vulnerability Discovery Year in Review--2019, December 2019).
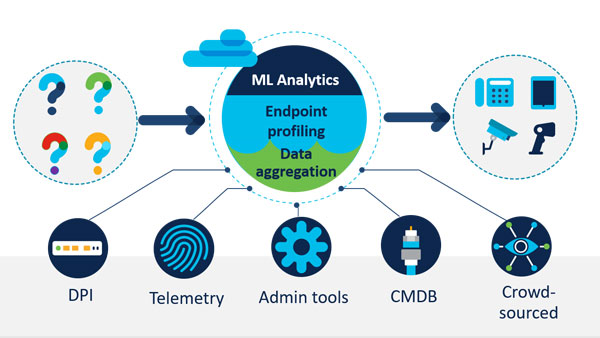
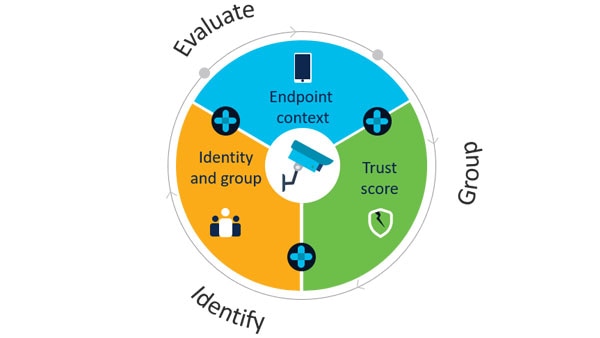
It is clear, therefore, that organizations must build in appropriate security as they deploy IoT devices at scale. The first step in securing IoT devices is knowing what devices you have in your network. Endpoint analytics is a way to identify and profile IoT devices, uncover spoofed devices, and detect and contain potential threats.