Cisco TrustSec Fibre Channel Link Encryption White Paper
Available Languages
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
Cisco TrustSec Fibre Channel Link Encryption overview
Supported ports across different modules
Data integrity and confidentiality are a top priority for Cisco’s customers. Storage networks may span large areas or multiple sites, and relying solely on physical security is not practical. Two requirements that are essential for secure communications are authentication and encryption.
Current Cisco® MDS 9000 family of storage networking solutions support peer authentication according to the Fibre Channel Security Protocol (FC-SP) standard using the Diffie-Hellman Challenge Handshake Authentication Protocol (DH-CHAP), but this process does not prevent unwanted activities such as traffic interception. To help ensure data integrity and privacy, data must be encrypted.
Cisco TrustSec® Fibre Channel Link Encryption addresses customer needs for data integrity and privacy.
Cisco TrustSec Fibre Channel Link Encryption overview
Cisco TrustSec Fibre Channel Link Encryption is an extension of the FC-SP standard and uses the existing FC-SP architecture. Starting with Cisco MDS 9000 NX-OS Software Release 4.2(1), Fibre Channel data traveling between E-ports on 2/4/8/16-Gbps modules is encrypted. Cisco uses the 128-bit Advanced Encryption Standard (AES) encryption algorithm and enables either AES-Galois/Counter Mode (GCM) or AES-Galois Message Authentication Code (AES-GMAC). AES-GCM encrypts and authenticates frames, and AES-GMAC authenticates only the frames that are being passed between the two peers. Encryption is performed at line rates by encapsulating frames at egress with encryption using the GCM authentication mode with 128-bit AES encryption. At ingress, frames are decrypted and authenticated with integrity checks.
Beginning with Cisco MDS NX-OS Release 9.4(3), the default global maximum encryption key size has been increased to 256 bits for directors equipped with Supervisor Module-4 and 64Gbps module and 64Gbps Fabric switches. All other devices support a maximum key size of 128 bits.
There are two primary use cases for Cisco TrustSec Fibre Channel Link Encryption. In the first use case, customers communicate outside the data center over native Fibre Channel (for example, dark fiber, Coarse Wavelength- Division Multiplexing [CWDM], or Dense Wavelength-Division Multiplexing [DWDM]). In the second use case, encryption is performed within the data center for security-focused customers such as defense and intelligence services. This feature is competitively unique and should provide a clear differentiator for campus and Metropolitan-Area Network (MAN) deployments and high-security accounts.
The figure below illustrates the Cisco TrustSec Fibre Channel Link Encryption feature.
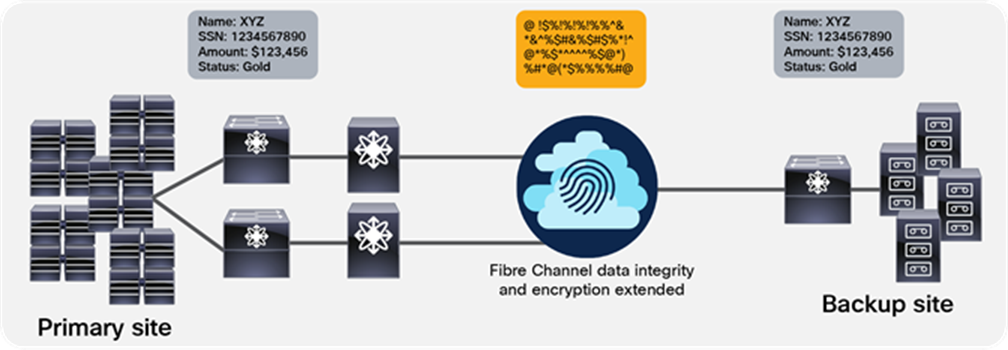
Cisco TrustSec Fibre Channel Link Encryption between multiple sites
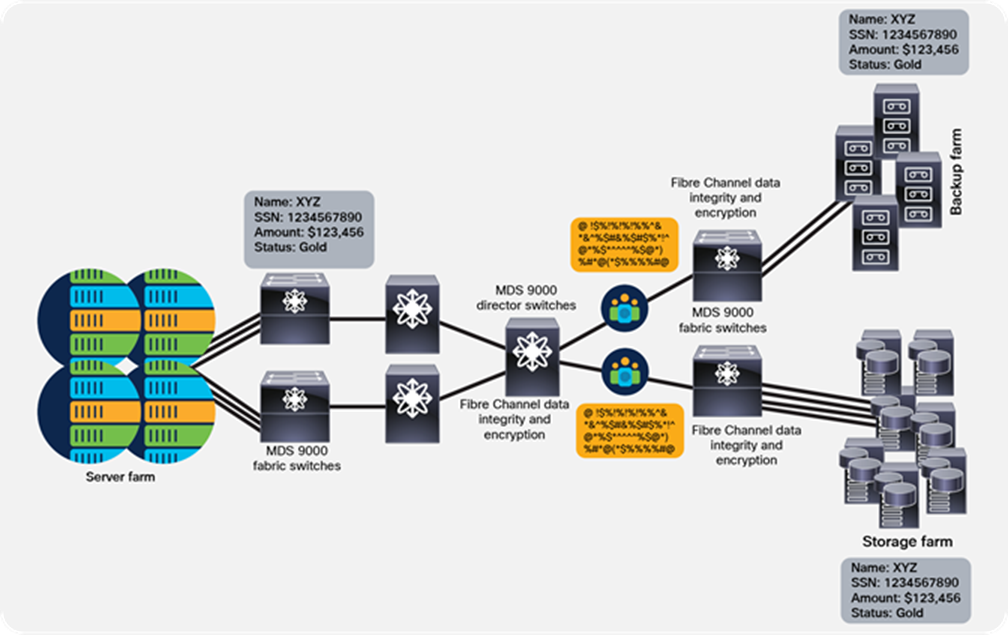
Cisco TrustSec Fibre Channel Link Encryption within the same site
Cisco TrustSec Fibre Channel Link Encryption with hardware and software integration using Cisco MDS 9000 family of storage networking solutions provides an easier solution for link-to-link encryption. Cisco TrustSec Fibre Channel Link Encryption is configured and provisioned using Cisco MDS NX-OS Software and Cisco Nexus Dashboard Fabric Controller (Formerly DCNM), the same software used to manage other data center products such as the Cisco MDS 9000 family.
To perform encryption between switches, a security association needs to be established. An administrator must manually configure the security association before the encryption can take place. The security association includes parameters such as encryption keys and salt (a 32-bit hexadecimal number that is used during encryption and decryption) are required for encryption. We can set up 2000 Security Associations (SAs) per switch. Security key management is not required, as they are stored locally.
To use Cisco TrustSec Fibre Channel Link Encryption, the minimum version of MDS NX-OS Release is provided in the following table:
| Cisco MDS 9000 Series Switches/Modules |
Minimum MDS NX-OS Release required |
| MDS 9000 Series Multilayer Switches [1] |
Release 4.2(1) or later |
| 16-Gbps modules such as the DS-X9448-768K9 |
Release 6.2(9) |
| 32-Gbps modules such as the DS-X9648-1536K9 |
Release 8.1(1) |
| 64-Gbps module DS-X9748-3072K9 |
Release 9.2(1) |
| MDS 9124V and MDS 9148V fabric switches |
Release 9.3(1) |
| MDS 9396V fabric switch |
Release 9.4(1) |
Following Cisco MDS 9500 and 9700 Series Multilayer Directors switching modules and MDS 9000 Fibre Channel Fabric Switches support Cisco TrustSec Fibre Channel Link Encryption:
● 4/44-port 1/2/4/8-Gbps Fibre Channel switching module (DS-X9248-48K9)
● 48-port 1/2/4/8-Gbps Fibre Channel switching module (DS-X9248-96K9)
● 24-port 1/2/4/8-Gbps Fibre Channel switching module (DS-X9224-96K9)
● 48-port 8-Gbps Advanced Fibre Channel switching module (DS-X9248-256K9)
● 32-port 8-Gbps Advanced Fibre Channel switching module (DS-X9232-256K9)
● 48-port 2/4/8/16-Gbps Fibre Channel switching module (DS-X9448-768K9)
● 48-port 4/8/16/32-Gbps Fibre Channel switching module (DS-X9648-1536K9)
● 48-port 8/16/32/64-Gbps Fibre Channel switching module (DS-X9748-3072K9)
● Cisco MDS 9000 24/10-Port SAN Extension Module (DS-X9334-K9)
● Cisco MDS 9396S 16-Gbps 96-Port Fibre Channel Fabric Switch
● Cisco MDS 9132T 32-Gbps 32-Port Fibre Channel Fabric Switch
● Cisco MDS 9148T 32-Gbps 48-Port Fibre Channel Fabric Switch
● Cisco MDS 9396T 32-Gbps 96-Port Fibre Channel Fabric Switch
● Cisco MDS 9124V 64-Gbps 24-Port Fibre Channel Fabric Switch
● Cisco MDS 9148V 64-Gbps 48-Port Fibre Channel Fabric Switch
● Cisco MDS 9396V 64-Gbps 96-Port Fibre Channel Fabric Switch
Supported ports across different modules
The Cisco TrustSec Fibre Channel Link Encryption feature is supported on selected ports out of each port group on modules and/or switches. Here is the list of ports where this feature can be enabled:
● 48-port 32-Gbps Fibre Channel Switching Module (DS-X9648-1536K9) — supported on ports 9-12, 25-28, and 41-44
● Cisco MDS 9132T Fibre Channel Switch — supported on ports 9-12 and 25-28
● Cisco MDS 9148T Fibre Channel Switch — supported on ports 9-12, 25-28, and 41-44
● Cisco MDS 9396T Fibre Channel Switch — supported on 9-12, 25-28, 41-44, 57-60, 73-76, and 89-92 ports
● 48-port 64-Gbps Fibre Channel Switching Module (DS-X9748-3072K9) — supported on ports 9, 11, 13, 15, 25, 27, 29 and 31
● Cisco MDS 9124V Fibre Channel Switch — supported on ports 9-12
● Cisco MDS 9148V Fibre Channel Switch — supported on ports 9-12, and 33-36
● Cisco MDS 9396V Fibre Channel Switch — supported on 1-4, 25-28, 57-60, and 81-84 ports
The Cisco TrustSec Fibre Channel Link Encryption feature is included with the Cisco MDS 9000 ENTERPRISE_PKG license (Advantage or Premier tiers). Customers who already have an installed Cisco MDS 9000 Enterprise license can use this feature; no additional licenses are required. For more information about Cisco MDS 9000 Enterprise license packages, see Cisco MDS 9000 Family Enterprise Package Data Sheet.
· For more information about how to configure Cisco TrustSec encryption, please visit Configuring Cisco TrustSec Fibre Channel Link Encryption Guide.
· To learn more about Cisco storage solutions for the data center, visit https://www.cisco.com/site/us/en/products/networking/cloud-networking-switches/storage-area-networking/index.html.
Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affiliates in the U.S. and other countries. To view a list of Cisco trademarks, go to this URL: https://www.cisco.com/c/en/us/about/legal/trademarks.html. Third-party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1721R)
Any Internet Protocol (IP) addresses and phone numbers used in this document are not intended to be actual addresses and phone numbers. Any examples, command display output, network topology diagrams, and other figures in the document are shown for illustrative purposes only. Any use of actual IP addresses or phone numbers in illustrative content is unintentional and coincidental.
© 2020-2025 Cisco Systems, Inc. All rights reserved.
[1] Note that Cisco TrustSec is supported only on E-ports configured between supported Cisco MDS 9000 Series Multilayer switches.