- Preparing for Broadband Access Aggregation
- Providing Protocol Support for Broadband Access Aggregation of PPPoE Sessions
- Providing Protocol Support for Broadband Access Aggregation of PPP over ATM Sessions
- Providing Connectivity Using ATM Routed Bridge Encapsulation over PVCs
- PPPoE Circuit-Id Tag Processing
- Providing Session Limit Support
- PPPoE Session Limit Local Override
- PPPoE - QinQ Support
- PPP-Max-Payload and IWF PPPoE Tag Support
- PPPoE Session Limiting on Inner QinQ VLAN
- PPPoE Agent Remote-ID and DSL Line Characteristics Enhancement
- Enabling PPPoE Relay Discovery and Service Selection Functionality
- Configuring Cisco Subscriber Service Switch Policies
- Per Session Queuing and Shaping for PPPoEoVLAN Using RADIUS
- 802.1P CoS Bit Set for PPP and PPPoE Control Frames
- PPPoE Smart Server Selection
- Monitoring PPPoE Sessions with SNMP
- PPPoE on ATM
- PPPoE on Ethernet
- PPP IP Unique Address and Prefix Detection
- Remote Access MPLS-VPNs
- Broadband High Availability Stateful Switchover
- Broadband High Availability In Service Software Upgrade
- Controlling Subscriber Bandwidth
- Offering PPPoE Clients a Selection of Services During Call Setup
Broadband Access Aggregation and DSL Configuration Guide, Cisco IOS XE Release 3S
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- November 1, 2008
Chapter: Broadband High Availability In Service Software Upgrade
- Finding Feature Information
- Contents
- Prerequisites for Broadband High Availability In-Service Software Upgrade
- Restrictions for Broadband High Availability In-Service Software Upgrade
- Information About Broadband High Availability In-Service Software Upgrade
- How to Configure Broadband High Availability In-Service Software Upgrade
- Configuration Examples for Broadband High Availability In-Service Software Upgrade
- Additional References
- Feature Information for Broadband High Availability In-Service Software Upgrade
Broadband High Availability In-Service Software Upgrade
The Broadband High Availability (HA) In-Service Software Upgrade (ISSU) feature ensures continuous operations of broadband access protocols during software upgrades, downgrades, and service enhancements.
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest feature information and caveats, see the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the "Feature Information for Broadband High Availability In-Service Software Upgrade" section.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Contents
•![]() Prerequisites for Broadband High Availability In-Service Software Upgrade
Prerequisites for Broadband High Availability In-Service Software Upgrade
•![]() Restrictions for Broadband High Availability In-Service Software Upgrade
Restrictions for Broadband High Availability In-Service Software Upgrade
•![]() Information About Broadband High Availability In-Service Software Upgrade
Information About Broadband High Availability In-Service Software Upgrade
•![]() How to Configure Broadband High Availability In-Service Software Upgrade
How to Configure Broadband High Availability In-Service Software Upgrade
•![]() Configuration Examples for Broadband High Availability In-Service Software Upgrade
Configuration Examples for Broadband High Availability In-Service Software Upgrade
•![]() Feature Information for Broadband High Availability In-Service Software Upgrade
Feature Information for Broadband High Availability In-Service Software Upgrade
Prerequisites for Broadband High Availability In-Service Software Upgrade
The ISSU and nonstop forwarding (NSF) features must be enabled. For more information about In-Service Software Upgrade, see the "Performing an In Service Software Upgrade" module. For more information about NSF, see the "Configuring Nonstop Forwarding" module.
Restrictions for Broadband High Availability In-Service Software Upgrade
•![]() You can perform an ISSU across a major Cisco IOS XE release.
You can perform an ISSU across a major Cisco IOS XE release.
•![]() You can perform an ISSU from a Cisco IOS XE release that supports ISSU capability.
You can perform an ISSU from a Cisco IOS XE release that supports ISSU capability.
Information About Broadband High Availability In-Service Software Upgrade
•![]() Feature Design of Broadband High Availability In-Service Software Upgrade
Feature Design of Broadband High Availability In-Service Software Upgrade
•![]() Benefits of Broadband High Availability In-Service Software Upgrade
Benefits of Broadband High Availability In-Service Software Upgrade
Feature Design of Broadband High Availability In-Service Software Upgrade
Prior to the implementation of the Broadband High Availability In-Service Software Upgrade feature, software upgrades typically required planned outages that took the router or network out of service. The Broadband High Availability In-Service Software Upgrade feature enables the service provider to maximize network availability and eliminate planned outages by allowing the Cisco IOS XE release to be upgraded without taking the router or network out of service. ISSU is a procedure, based on Cisco high availability (HA) architecture, whereby the Cisco IOS XE infrastructure accomplishes an upgrade while packet forwarding continues and broadband sessions are maintained. Cisco HA architecture is based on redundant Route Processors and the NSF and SSO features, such that ports stay active and calls do not drop, eliminating network disruption during upgrades.
The ISSU feature allows deployment of new features, hardware, services, and maintenance fixes in a procedure that is seamless to end users. A critical component of ISSU and Cisco HA technology is the cluster control manager (CCM) that manages session recreation and synchronization on the standby processor. The Broadband High Availability In-Service Software Upgrade feature allows the configuration of subscriber redundancy policies that tune the synchronization process. For more information see the "Configuring Subscriber Redundancy Policy for Broadband High Availability In-Service Software Upgrade" section.
The Broadband High Availability In-Service Software Upgrade feature handles upgrades and downgrades, and supports the following:
•![]() Upgrades from one software feature release to another, as long as both versions support the ISSU feature, for example, from Cisco IOS XE Release 2.2 to Cisco IOS XE Release 2.3.
Upgrades from one software feature release to another, as long as both versions support the ISSU feature, for example, from Cisco IOS XE Release 2.2 to Cisco IOS XE Release 2.3.
•![]() Upgrades from one software maintenance release to another, for example from Cisco IOS XE Release 2.2.1 to Cisco IOS XE Release 2.2.2.
Upgrades from one software maintenance release to another, for example from Cisco IOS XE Release 2.2.1 to Cisco IOS XE Release 2.2.2.
The Broadband High Availability In-Service Software Upgrade feature works with other Cisco IOS XE HA features, NSF and SSO, to maintain broadband sessions.
Performing an ISSU
For detailed information about HA and about performing an ISSU, see the following chapters in the Cisco ASR 1000 Series Aggregation Services Routers Software Configuration Guide:
•![]() "High Availability Overview"
"High Availability Overview"
•![]() "Cisco IOS XE Software Package Compatibility for ISSU"
"Cisco IOS XE Software Package Compatibility for ISSU"
•![]() "In Service Software Upgrade (ISSU)"
"In Service Software Upgrade (ISSU)"
Supported Broadband Aggregation Protocols
The Broadband High Availability In-Service Software Upgrade feature supports the following broadband aggregation protocols described in the following sections:
ISSU PPPoA
The Broadband High Availability In-Service Software Upgrade feature delivers ISSU capability for PPP over ATM (PPPoA) sessions during supported software upgrades, downgrades, and enhancements.
ISSU L2TP
The L2TP HA Session SSO/ISSU on a LAC/LNS feature provides a generic SSO/ISSU mechanism for Layer 2 Tunneling Protocol (L2TP) on a Layer 2 Access Concentrator (LAC) and a Layer 2 Network Server (LNS). This feature preserves all fully established PPP and L2TP sessions during an SSO switchover or an ISSU upgrade or downgrade.
ISSU PPPoE
The Broadband High Availability In-Service Software Upgrade feature delivers ISSU capability for PPP over Ethernet (PPPoE) subscriber access sessions, including PPPoE, PPPoE over VLAN, and PPPoE over QinQ sessions, during supported software upgrades, downgrades, and enhancements.
ISSU RA-MLPS VPN
The Broadband High Availability In-Service Software Upgrade feature delivers ISSU capability for PPPoA and PPPoE (PPPoX) sessions terminated into remote access (RA)-Multiprotocol Label Switching (MPLS) VPN or PPPoX into MPLS VPN during supported software upgrades, downgrades, and enhancements.
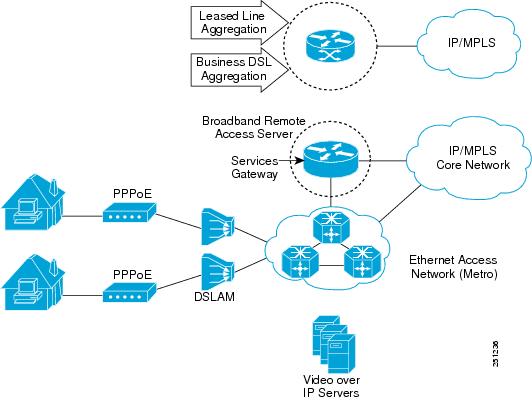
Figure 1 shows a typical broadband aggregation HA deployment with ISSU functionality.
Figure 1 Broadband Aggregation High Availability Deployment
Benefits of Broadband High Availability In-Service Software Upgrade
•![]() Eliminates network downtime for Cisco IOS XE software upgrades.
Eliminates network downtime for Cisco IOS XE software upgrades.
•![]() Eliminates resource scheduling challenges associated with planned outages and late night maintenance windows.
Eliminates resource scheduling challenges associated with planned outages and late night maintenance windows.
•![]() Accelerates deployment of new services and applications and allows faster implementation of new features, hardware, and fixes.
Accelerates deployment of new services and applications and allows faster implementation of new features, hardware, and fixes.
•![]() Reduces operating costs due to outages while delivering higher service levels.
Reduces operating costs due to outages while delivering higher service levels.
•![]() Provides additional options for adjusting maintenance windows.
Provides additional options for adjusting maintenance windows.
•![]() Minimizes the impact of upgrades to service and allows for faster upgrades, resulting in higher availability.
Minimizes the impact of upgrades to service and allows for faster upgrades, resulting in higher availability.
How to Configure Broadband High Availability In-Service Software Upgrade
This section contains the following procedures:
•![]() Configuring Subscriber Redundancy Policy for Broadband High Availability In-Service Software Upgrade (required)
Configuring Subscriber Redundancy Policy for Broadband High Availability In-Service Software Upgrade (required)
•![]() Verifying and Troubleshooting Subscriber Redundancy Policy for Broadband HA ISSU (optional)
Verifying and Troubleshooting Subscriber Redundancy Policy for Broadband HA ISSU (optional)
Configuring Subscriber Redundancy Policy for Broadband High Availability In-Service Software Upgrade
The Broadband High Availability In-Service Software Upgrade feature is enabled by default. This task configures subscriber redundancy policy for HA ISSU capability, allowing you to manage synchronization between HA active and standby processors.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() subscriber redundancy {bulk limit {cpu percentage delay delay-time [allow value] | time seconds | delay delay-time | dynamic limit cpu percentage delay delay-time [allow value] | rate sessions time}
subscriber redundancy {bulk limit {cpu percentage delay delay-time [allow value] | time seconds | delay delay-time | dynamic limit cpu percentage delay delay-time [allow value] | rate sessions time}
4. ![]() exit
exit
Verifying and Troubleshooting Subscriber Redundancy Policy for Broadband HA ISSU
To verify the subscriber redundancy policy configuration, use the show running-config command. Sample output is available in the "Configuration Examples for Broadband High Availability In-Service Software Upgrade" section.
•![]() Step 1, Step 2 and Step 3 are useful for troubleshooting the CCM synchronization component.
Step 1, Step 2 and Step 3 are useful for troubleshooting the CCM synchronization component.
•![]() Step 4, Step 5 and Step 6 are useful for reviewing PPPoX session statistics.
Step 4, Step 5 and Step 6 are useful for reviewing PPPoX session statistics.
•![]() Step 7 and Step 8 are useful for verifying the failure of any L2TP tunnels or VPDN groups.
Step 7 and Step 8 are useful for verifying the failure of any L2TP tunnels or VPDN groups.
•![]() Step 9 and Step 10 are typically used by Cisco engineers for internal debugging purposes.
Step 9 and Step 10 are typically used by Cisco engineers for internal debugging purposes.
SUMMARY STEPS
1. ![]() show ccm clients
show ccm clients
2. ![]() show ccm sessions
show ccm sessions
3. ![]() show ccm queues
show ccm queues
4. ![]() show ppp subscriber statistics
show ppp subscriber statistics
5. ![]() show pppatm statistics
show pppatm statistics
6. ![]() show pppoe statistics
show pppoe statistics
7. ![]() show vpdn redundancy
show vpdn redundancy
8. ![]() show vpdn history failure
show vpdn history failure
9. ![]() debug pppatm redundancy
debug pppatm redundancy
10. ![]() debug pppoe redundancy
debug pppoe redundancy
DETAILED STEPS
Step 1 ![]() show ccm clients
show ccm clients
This command displays information about the CCM, the HA component that manages the capability to synchronize session launch on the standby processor of a redundant processor HA system. Use the show ccm clients command to display information about CCM clients.
Router# show ccm clients
CCM bundles sent since peer up:
Sent Queued for flow control
Sync Session 0 0
Update Session 0 0
Active Bulk Sync End 1 0
Session Down 0 0
ISSU client msgs 350 0
Dynamic Session Sync 0 0
Unknown msgs 0 0
Client events sent since peer up:
PPP 0
PPPoE 0
VPDN FSP 0
AAA 0
PPP SIP 0
LTERM 0
AC 0
L2TP CC 0
SSS FM 0
IP SIP 0
IP IF 0
COA 0
Auto Svc 0
VPDN LNS 0
Step 2 ![]() show ccm sessions
show ccm sessions
This command displays information about sessions managed by CCM.
Router# show ccm sessions
Global CCM state: CCM HA Active - Dynamic Sync
Global ISSU state: Compatible, Clients Cap 0x9EFFE
Current Bulk Sent Bulk Rcvd
----------- ----------- -----------
Number of sessions in state Down: 0 0 0
Number of sessions in state Not Ready: 0 0 0
Number of sessions in state Ready: 0 0 0
Number of sessions in state Dyn Sync: 0 0 0
Timeout: Timer Type Delay Remaining Starts CPU Limit CPU Last
------------ -------- --------- ----------- --------- --------
Rate 00:00:01 - 0 - -
Dynamic CPU 00:00:10 - 0 90 0
Bulk CPU Lim 00:00:10 - 0 90 0
Bulk Time Li 00:00:01 - 0 - -
RF Notif Ext 00:00:01 - 8 - -
Step 3 ![]() show ccm queues
show ccm queues
Use the show ccm queues command to display queue statistics for CCM sessions on active and standby processors. This command is primarily used only by Cisco engineers for internal debugging of CCM processes.
Router# show ccm queues
11 Event Queues
size max kicks starts false suspends ticks(ms)
3 CCM 0 8 82 83 1 0 20
Event Names
Events Queued MaxQueued Suspends usec/evt max/evt
1 3 Sync Session 0 0 0 0 0 0
2 3 Sync Client 0 0 0 0 0 0
3 3 Update 0 0 0 0 0 0
4 3 Session Down 0 0 0 0 0 0
5 3 Bulk Sync Begi 1 0 1 0 0 0
6 3 Bulk Sync Cont 2 0 2 0 0 0
7 3 Bulk Sync End 1 0 1 0 0 0
8 3 Rcv Bulk End 0 0 0 0 0 0
9 3 Dynamic Sync C 0 0 0 0 0 0
10 3 Going Active 0 0 0 0 0 0
11 3 Going Standby 0 0 0 0 0 0
12 3 Standby Presen 1 0 1 0 0 0
13 3 Standby Gone 0 0 0 0 0 0
15 3 CP Message 205 0 8 0 141 1000
16 3 Recr Session 0 0 0 0 0 0
17 3 Recr Update 0 0 0 0 0 0
18 3 Recr Sess Down 0 0 0 0 0 0
19 3 ISSU Session N 1 0 1 0 0 0
20 3 ISSU Peer Comm 0 0 0 0 0 0
21 3 Free Session 0 0 0 0 0 0
22 3 Sync Dyn Sessi 0 0 0 0 0 0
23 3 Recr Dyn Sessi 0 0 0 0 0 0
24 3 Session Ready 0 0 0 0 0 0
25 3 Pending Update 0 0 0 0 0 0
FSM Event Names Events
0 Invalid 0
1 All Ready 0
2 Required Not Re 0
3 Update 0
4 Down 0
5 Error 0
6 Ready 0
7 Not Syncable 0
8 Recreate Down 0
Step 4 ![]() show ppp subscriber statistics
show ppp subscriber statistics
This command is useful for displaying events and statistics for PPP subscribers. Use the show ppp subscriber statistics command to display a cumulative count of PPP subscriber events and statistics, and to display an incremental count since the clear ppp subscriber statistics command was last issued.
Router# show ppp subscriber statistics
PPP Subscriber Events TOTAL SINCE CLEARED
Encap 5 5
DeEncap 0 0
CstateUp 7 7
CstateDown 4 4
FastStart 0 0
LocalTerm 7 7
LocalTermVP 0 0
MoreKeys 7 7
Forwarding 0 0
Forwarded 0 0
SSSDisc 0 0
SSMDisc 0 0
PPPDisc 0 0
PPPBindResp 7 7
PPPReneg 3 3
RestartTimeout 5 5
PPP Subscriber Statistics TOTAL SINCE CLEARED
IDB CSTATE UP 4 4
IDB CSTATE DOWN 8 8
APS UP 0 0
APS UP IGNORE 0 0
APS DOWN 0 0
READY FOR SYNC 8 8
Step 5 ![]() show pppatm statistics
show pppatm statistics
This command is useful for obtaining statistics for PPPoA sessions. Use the show pppatm statistics command to display a total count of PPPoA events since the clear pppatm statistics command was last issued.
Router# show pppatm statistics
4000 : Context Allocated events
3999 : SSS Request events
7998 : SSS Msg events
3999 : PPP Msg events
3998 : Up Pending events
3998 : Up Dequeued events
3998 : Processing Up events
3999 : Vaccess Up events
3999 : AAA unique id allocated events
3999 : No AAA method list set events
3999 : AAA gets nas port details events
3999 : AAA gets retrived attrs events
68202 : AAA gets dynamic attrs events
3999 : Access IE allocated events
Step 6 ![]() show pppoe statistics
show pppoe statistics
This command is useful for obtaining statistics and events for PPPoE sessions. Use the show pppoe statistics command to display a cumulative count of PPPoE events and statistics, and to display an incremental count since the last time the clear pppoe statistics command was issued.
Router# show pppoe statistics
PPP Subscriber Events TOTAL SINCE CLEARED
Encap 5 5
DeEncap 2 2
CstateUp 0 0
CstateDown 0 0
FastStart 0 0
LocalTerm 0 0
LocalTermVP 0 0
MoreKeys 0 0
Forwarding 0 0
Forwarded 0 0
SSSDisc 0 0
SSMDisc 0 0
PPPDisc 0 0
PPPBindResp 0 0
PPPReneg 0 0
RestartTimeout 2 2
PPP Subscriber Statistics TOTAL SINCE CLEARED
IDB CSTATE UP 0 0
IDB CSTATE DOWN 0 0
APS UP 0 0
APS UP IGNORE 0 0
APS DOWN 0 0
READY FOR SYNC 0 0
ASR1006-1#sh pppoe statis
ASR1006-1#sh pppoe statistics ?
| Output modifiers
<cr>
ASR1006-1#sh pppoe statistics
PPPoE Events TOTAL SINCE CLEARED
------------------------------ ------------- -------------
INVALID 0 0
PRE-SERVICE FOUND 0 0
PRE-SERVICE NONE 0 0
SSS CONNECT LOCAL 0 0
SSS FORWARDING 0 0
SSS FORWARDED 0 0
SSS MORE KEYS 0 0
SSS DISCONNECT 0 0
SSS DISCONNECT ACK 0 0
CONFIG UPDATE 0 0
STATIC BIND RESPONSE 0 0
PPP FORWARDING 0 0
PPP FORWARDED 0 0
PPP DISCONNECT 0 0
PPP RENEGOTIATION 0 0
SSM PROVISIONED 0 0
SSM UPDATED 0 0
SSM ACCT STATS UPDATED 0 0
SSM DISCONNECT 0 0
0 0
PPPoE Statistics TOTAL SINCE CLEARED
------------------------------ ------------- -------------
SSS Request 0 0
SSS Response Stale 0 0
SSS Disconnect 0 0
PPPoE Handles Allocated 0 0
PPPoE Handles Freed 0 0
Dynamic Bind Request 0 0
Static Bind Request 0 0
SSM Async Stats Request 0 0
Step 7 ![]() show vpdn redundancy
show vpdn redundancy
Use this command to verify the failure of any L2TP tunnels.
Router# show vpdn redundancy
L2TP HA support: Silent Failover
L2TP HA Status:
Checkpoint Messaging on: TRUE
Standby RP is up: TRUE
Recv'd Message Count: 0
L2TP Tunnels: 0/0/0/0 (total/HA-enabled/HA-est/resync)
L2TP Sessions: 0/0/0 (total/HA-enabled/HA-est)
L2TP Resynced Tunnels: 0/0 (success/fail)
Step 8 ![]() show vpdn history failure
show vpdn history failure
Use this command to verify the failure of any VPDN groups.
Router# show vpdn history failure
% VPDN user failure table is empty
Step 9 ![]() debug pppatm redundancy
debug pppatm redundancy
Use the debug pppatm redundancy command to display CCM events and messages for PPPoA sessions on HA systems. This command is generally used only by Cisco engineers for internal debugging of CCM processes.
Router# debug pppatm redundancy
*Dec 3 02:58:40.784: PPPATM HA: [14000001]: Received the first SHDB
*Dec 3 02:58:40.784: PPPATM HA: [14000001]: Base hwidb not created > yet, queuing SHDB *Dec 3 02:58:40.784: PPPATM HA: [14000001]:
Requesting base vaccess creation
Step 10 ![]() debug pppoe redundancy
debug pppoe redundancy
Use the debug pppoe redundancy command to display CCM events and messages for PPPoE sessions on HA systems. This command is generally used only by Cisco engineers for internal debugging of CCM processes.
Router# debug pppoe redundancy
Nov 22 17:21:11.327: PPPoE HA[0xBE000008] 9: Session ready to sync data
Nov 22 17:21:11.351: PPPoE HA[0xBE000008] 9: code = PADR, length = 58
Nov 22 17:21:11.351: PPPoE HA[0xBE000008] 9: code = SESSION ID, length = 2
Nov 22 17:21:11.351: PPPoE HA[0xBE000008] 9: code = SWITCH HDL, length = 4
Nov 22 17:21:11.351: PPPoE HA[0xBE000008] 9: code = SEGMENT HDL, length = 4
Nov 22 17:21:11.351: PPPoE HA[0xBE000008] 9: code = PHY SWIDB DESC, length = 20
Nov 22 17:21:11.351: PPPoE HA[0xBE000008] 9: code = VACCESS DESC, length = 28
Nov 22 17:21:11.351: PPPoE HA[0xBE000008] 9: Sync collection for ready events
Nov 22 17:21:11.351: PPPoE HA[0xBE000008] 9: code = PADR, length = 58
Nov 22 17:21:11.351: PPPoE HA[0xBE000008] 9: code = SESSION ID, length = 2
Nov 22 17:21:11.351: PPPoE HA[0xBE000008] 9: code = SWITCH HDL, length = 4
Nov 22 17:21:11.351: PPPoE HA[0xBE000008] 9: code = SEGMENT HDL, length = 4
Nov 22 17:21:11.351: PPPoE HA[0xBE000008] 9: code = PHY SWIDB DESC, length = 20
Nov 22 17:21:11.351: PPPoE HA[0xBE000008] 9: code = VACCESS DESC, length = 28
Configuration Examples for Broadband High Availability In-Service Software Upgrade
This section provides the following configuration examples:
•![]() Example: Subscriber Redundancy Policy for Broadband High Availability In-Service Software Upgrade
Example: Subscriber Redundancy Policy for Broadband High Availability In-Service Software Upgrade
Example: Subscriber Redundancy Policy for Broadband High Availability In-Service Software Upgrade
The following example shows how to configure the Broadband High Availability In-Service Software Upgrade feature:
enable
configure terminal
subscriber redundancy bulk limit cpu 75 delay 20 allow 30
end
The following is a sample configuration of PPPoX terminated into an RA-MPLS network with SSO. Commands that appear in the configuration task tables for this feature but that do not appear in the running configuration output are configured for their default settings.
hostname Router
!
boot-start-marker
boot system bootflash:packages.conf !
enable password cisco
!
aaa new-model
!
!
aaa authentication ppp default local
!
!
!
aaa session-id common
ppp hold-queue 80000
ip subnet-zero
no ip gratuitous-arps
no ip domain lookup
ip vrf vrf1
rd 1:1
route-target export 1:1
route-target import 1:1
!
no ip dhcp use vrf connected
!
!
!
!
no subscriber policy recording rules
The following lines show subscriber redundancy policy configuration:
subscriber redundancy dynamic limit cpu 90 delay 10
subscriber redundancy bulk limit cpu 90 delay 10
subscriber redundancy rate 4000 1
subscriber redundancy delay 10
no mpls traffic-eng
mpls ldp graceful-restart
mpls ldp router-id Loopback100
no virtual-template snmp
no issu config-sync policy bulk prc
no issu config-sync policy bulk bem
!
redundancy mode sso
username cisco password 0 cisco
!
buffers small permanent 15000
buffers middle permanent 12000
buffers large permanent 1000
bba-group pppoe grp1
virtual-template 1
!
bba-group pppoe grp2
virtual-template 2
!
bba-group pppoe grp3
virtual-template 3
!
bba-group pppoe grp4
virtual-template 4
!
bba-group pppoe grp5
virtual-template 5
!
bba-group pppoe grp7
virtual-template 7
!
bba-group pppoe grp8
virtual-template 8
!
bba-group pppoe grp6
virtual-template 6
!
!
interface Loopback0
ip vrf forwarding vrf1
ip address 172.16.1.1 255.255.255.255
!
interface Loopback100
ip address 172.31.0.1 255.255.255.255
!
interface FastEthernet0/0/0
ip address 192.168.2.26 255.255.255.0
speed 100
full-duplex
!
interface GigabitEthernet1/0/0
no ip address
load-interval 30
!
interface GigabitEthernet1/0/0.1
encapsulation dot1Q 2
pppoe enable group grp1
!
!
interface GigabitEthernet1/0/0.2
encapsulation dot1Q 2
pppoe enable group grp2
!
!
interface GigabitEthernet1/0/1
no ip address
!
interface GigabitEthernet1/0/1.1
encapsulation dot1Q 2
pppoe enable group grp3
!
!
interface GigabitEthernet1/0/1.2
encapsulation dot1Q 2
pppoe enable group grp4
!
!
interface GigabitEthernet1/0/2
no ip address
!
interface GigabitEthernet1/0/2.1
encapsulation dot1Q 2
pppoe enable group grp5
!
!
interface GigabitEthernet1/0/2.2
encapsulation dot1Q 2
pppoe enable group grp6
!
!
interface GigabitEthernet1/0/3
no ip address
!
interface GigabitEthernet1/0/3.1
encapsulation dot1Q 2
pppoe enable group grp7
!
!
interface GigabitEthernet1/0/3.2
encapsulation dot1Q 2
pppoe enable group grp8
!
interface GigabitEthernet7/0/3
no ip address
!
interface GigabitEthernet8/0/0
mac-address 0011.0022.0033
ip vrf forwarding vrf1
ip address 10.1.1.2 255.255.255.0
negotiation auto
!
interface GigabitEthernet8/1/0
ip address 10.1.1.1 255.255.255.0
negotiation auto
mpls ip
!
interface Virtual-Template1
ip vrf forwarding vrf1
ip unnumbered Loopback0
no logging event link-status
peer default ip address pool pool1
no snmp trap link-status
keepalive 30
ppp authentication pap
!
interface Virtual-Template2
ip vrf forwarding vrf1
ip unnumbered Loopback0
no logging event link-status
peer default ip address pool pool2
no snmp trap link-status
keepalive 30
ppp authentication pap
!
interface Virtual-Template3
ip vrf forwarding vrf1
ip unnumbered Loopback0
no logging event link-status
peer default ip address pool pool3
no snmp trap link-status
keepalive 30
ppp authentication pap
!
interface Virtual-Template4
ip vrf forwarding vrf1
ip unnumbered Loopback0
no logging event link-status
peer default ip address pool pool4
no snmp trap link-status
keepalive 30
ppp authentication pap
!
interface Virtual-Template5
ip vrf forwarding vrf1
ip unnumbered Loopback0
no logging event link-status
peer default ip address pool pool5
no snmp trap link-status
keepalive 30
ppp authentication pap
!
interface Virtual-Template6
ip vrf forwarding vrf1
ip unnumbered Loopback0
no logging event link-status
peer default ip address pool pool6
no snmp trap link-status
keepalive 30
ppp authentication pap
!
interface Virtual-Template7
ip vrf forwarding vrf1
ip unnumbered Loopback0
no logging event link-status
peer default ip address pool pool7
no snmp trap link-status
keepalive 30
ppp authentication pap
!
interface Virtual-Template8
ip vrf forwarding vrf1
ip unnumbered Loopback0
no logging event link-status
peer default ip address pool pool8
no snmp trap link-status
keepalive 30
ppp authentication pap
!
router ospf 1
log-adjacency-changes
nsf
network 10.1.1.0 0.0.0.255 area 0
network 10.0.0.0 0.0.0.255 area 0
!
router bgp 1
no synchronization
bgp log-neighbor-changes
bgp graceful-restart restart-time 120
bgp graceful-restart stalepath-time 360
bgp graceful-restart
neighbor 10.0.0.3 remote-as 1
neighbor 10.0.0.3 update-source Loopback100
no auto-summary
!
address-family vpnv4
neighbor 10.0.0.3 activate
neighbor 10.0.0.3 send-community extended
exit-address-family
!
address-family ipv4 vrf vrf1
redistribute connected
redistribute static
no auto-summary
no synchronization
exit-address-family
!
ip local pool pool2 10.1.1.1 10.1.16.160
ip local pool pool3 10.1.1.1 10.1.16.160
ip local pool pool4 10.1.1.1 10.1.16.160
ip local pool pool5 10.1.1.1 10.1.16.160
ip local pool pool6 10.1.1.1 10.1.16.160
ip local pool pool7 10.1.1.1 10.1.16.160
ip local pool pool8 10.1.1.1 10.1.16.160
ip classless !
!
no ip http server
!
!
arp 10.1.1.1 0020.0001.0001 ARPA
arp vrf vrf1 10.1.1.1 0020.0001.0001 ARPA !
!
!
line con 0
line aux 0
line vty 0 4
password cisco
!
exception crashinfo file bootflash:crash.log !
end
Additional References
Related Documents
|
|
|
|---|---|
Cisco IOS commands |
|
Cisco IOS Broadband commands |
Cisco IOS Broadband Access Aggregation and DSL Command Reference |
High Availability |
"High Availability Overview" chapter in the Cisco ASR 1000 Series Aggregation Services Routers Software Configuration Guide |
Performing an ISSU |
The following chapters in the Cisco ASR 1000 Series Aggregation Services Routers Software Configuration Guide: • • |
Broadband SSO |
|
Stateful switchover |
|
Cisco nonstop forwarding |
|
Layer 2 Tunnel Protocol |
|
Additional information about commands used in this document |
• |
Standards
|
|
|
|---|---|
No new or modified standards are supported by this feature, and support for existing RFCs has not been modified by this feature. |
— |
MIBs
RFCs
|
|
|
|---|---|
No new or modified RFCs are supported by this feature, and support for existing RFCs has not been modified by this feature. |
— |
Technical Assistance
Feature Information for Broadband High Availability In-Service Software Upgrade
Table 1 lists the features in this module and provides links to specific configuration information.
Use Cisco Feature Navigator to find information about platform support and software image support. Cisco Feature Navigator enables you to determine which software images support a specific software release, feature set, or platform. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.

Note ![]() Table 1 lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Table 1 lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
 Feedback
Feedback