Web Authentication Using LDAP on Wireless LAN Controllers (WLCs) Configuration Example
Available Languages
Download Options
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
Contents
Introduction
Prerequisites
Requirements
Components Used
Background Information
Conventions
Web Authentication Process
Configure
Network Diagram
Configurations
Configure the LDAP Server
Create Users on the Domain Controller
Create a User Database Under an OU
Configure the User for LDAP Access
Anonymous Bind
Enable Anonymous Bind Feature on the Windows 2012 Essentials Server
Granting ANONYMOUS LOGON Access to the User
Grant List Contents Permission on the OU
Authenticated Bind
Granting Administrator privilages to WLC-admin
Use LDP to Identify the User Attributes
Configure WLC for LDAP Server
Configure the WLAN for Web Authentication
Verify
Troubleshoot
Introduction
This document describes how to setup a Wireless LAN Controller (WLC) for web authentication. It explains how to configure a Lightweight Directory Access Protocol (LDAP) server as the backend database for web authentication to retrieve user credentials and authenticate the user.
Prerequisites
Requirements
Cisco recommends that you have knowledge of these topics:
-
Knowledge of the configuration of Lightweight Access Points (LAPs) and Cisco WLCs
-
Knowledge of Control And Provisioning of Wireless Access Point protocol (CAPWAP)
-
Knowledge of how to set up and configure Lightweight Directory Access Protocol (LDAP), Active Directory and domain controllers
Components Used
The information in this document is based on these software and hardware versions:
-
Cisco 5508 WLC that runs firmware release 8.2.100.0
-
Cisco 1142 Series LAP
-
Cisco 802.11a/b/g Wireless Client Adapter.
-
Microsoft Windows 2012 Essentials server that performs the role of the LDAP server
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Background Information
Conventions
Refer to the Cisco Technical Tips Conventions for more information on document conventions.
Web Authentication Process
Web authentication is a Layer 3 security feature that causes the controller to disallow IP traffic (except DHCP and DNS-related packets) from a particular client until that client has correctly supplied a valid username and password. When you use web authentication to authenticate clients, you must define a username and password for each client. Then, when the clients attempt to join the wireless LAN, they must enter the username and password when prompted by a login page.
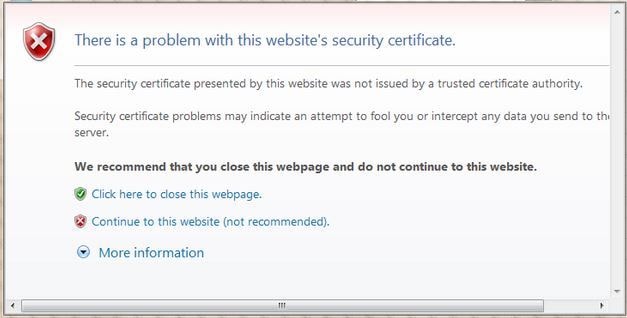
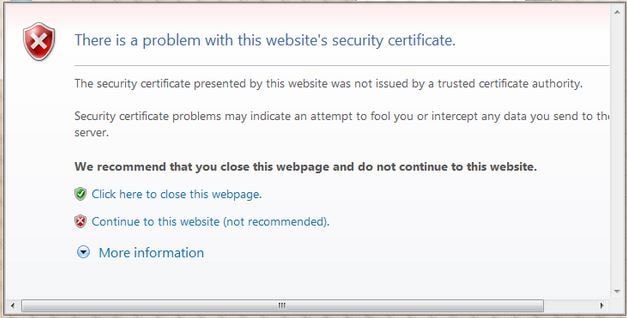
When web authentication is enabled (under Layer 3 Security), users occasionally receive a web-browser security alert the first time that they attempt to access a URL.
Tip: To remove this certificate warning, please revert back to the following guide on how to install a 3rd party trusted certificate http://www.cisco.com/c/en/us/support/docs/wireless/4400-series-wireless-lan-controllers/109597-csr-chained-certificates-wlc-00.html
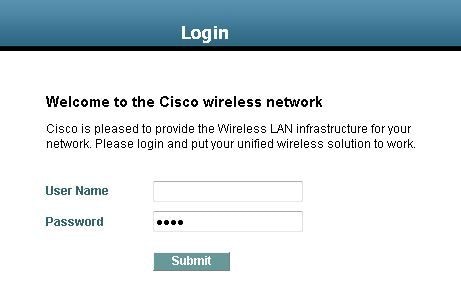
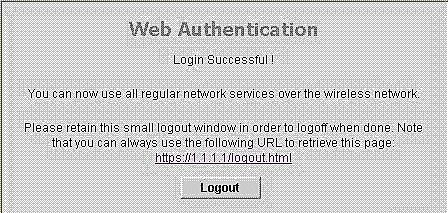
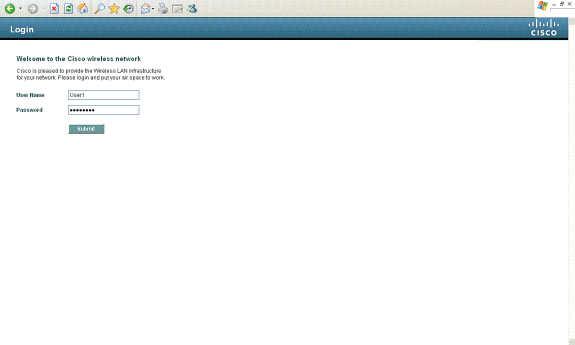
After you click Yes to proceed (or more precisely Continue to this website (not recommended) for Firefox browser for example), or if the browser of the client does not display a security alert, the web authentication system redirects the client to a login page, as shown in the image:
The default login page contains a Cisco logo and Cisco-specific text. You can choose to have the web authentication system display one of these:
-
The default login page
-
A modified version of the default login page
-
A customized login page that you configure on an external web server
-
A customized login page that you download to the controller
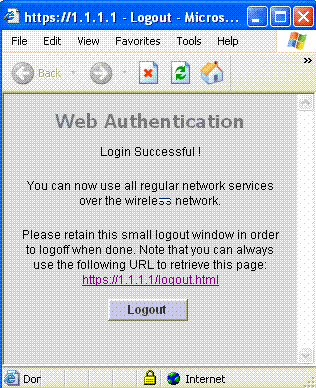
When you enter a valid username and password on the web authentication login page and click Submit, you are authenticated based upon the credentials submitted and a successful authentication from the backend database (LDAP in this case). The web authentication system then displays a successful login page and redirects the authenticated client to the requested URL.
The default successful login page contains a pointer to a virtual gateway address URL: https://1.1.1.1/logout.html. The IP address that you set for the controller virtual interface serves as the redirect address for the login page.
This document explains how to use the internal web page on the WLC for web authentication. This example uses a LDAP server as the backend database for web authentication to retrieve user credentials and authenticate the user.
Configure
In this section, you are presented with the information to configure the features described in this document.
Note: Use the Command Lookup Tool (registered customers only) to obtain more information on the commands used in this section.
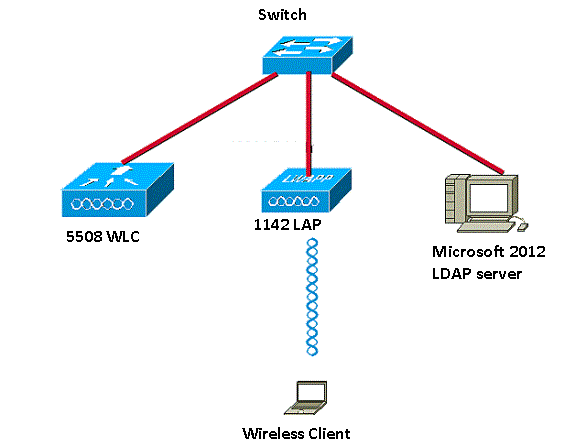
Network Diagram
This document uses this network setup:
Configurations
Complete these steps in order to successfully implement this setup:
Configure the LDAP Server
The first step is to configure the LDAP server, which serves as a backend database to store user credentials of the wireless clients. In this example, the Microsoft Windows 2012 Essentials server is used as the LDAP server.
The first step in the configuration of the LDAP server is to create a user database on the LDAP server so that the WLC can query this database to authenticate the user.
Create Users on the Domain Controller
An Organizational Unit (OU) contains multiple groups that carry references to personal entries in a PersonProfile. A person can be a member of multiple groups. All object class and attribute definitions are LDAP schema default. Each group contains references (dn) for each person that belongs to it.
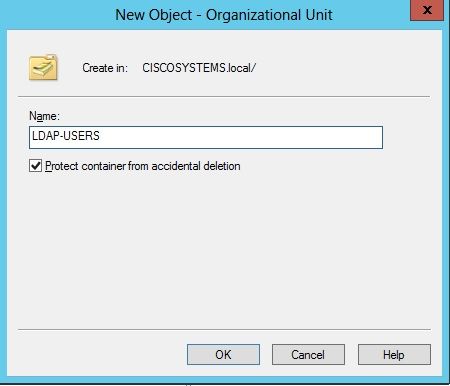
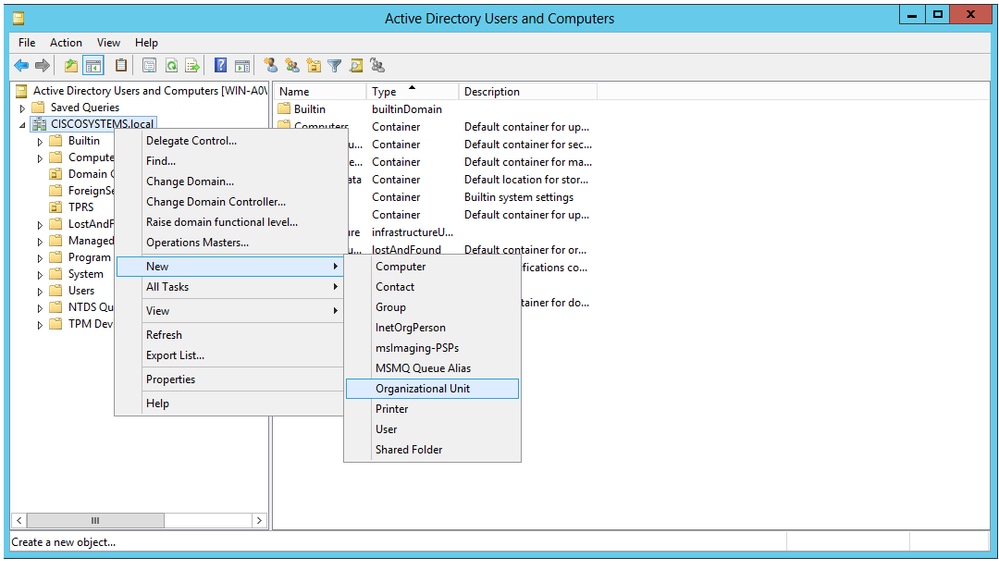
In this example, a new OU LDAP-USERS is created, and the user User1 is created under this OU. When you configure this user for LDAP access, the WLC can query this LDAP database for user authentication.
The domain used in this example is CISCOSYSTEMS.local.
Create a User Database Under an OU
This section explains how to create a new OU in your domain and create a new user on this OU.
-
Open Windows PowerShell and type servermanager.exe
- In the Server Manager window, click on AD DS. Then right-click your server name to choose Active Directory Users and Computers.
-
Right-click your domain name, which is CISCOSYSTEMS.local in this example, and then navigate to New > Organizational Unit from the context menu in order to create a new OU.
-
Assign a name to this OU and click OK, as shown in the image:
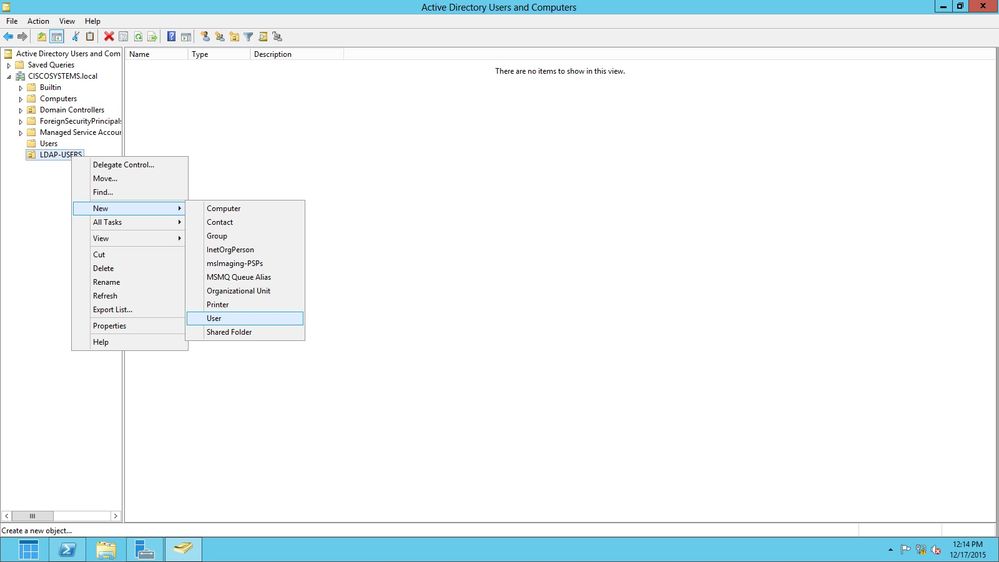
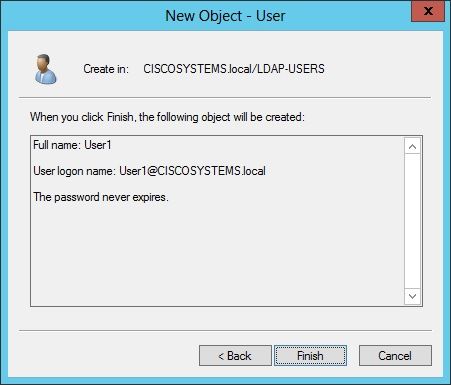
Now that the new OU LDAP-USERS is created on the LDAP server, the next step is to create user User1 under this OU. In order to achieve this, complete these steps:
-
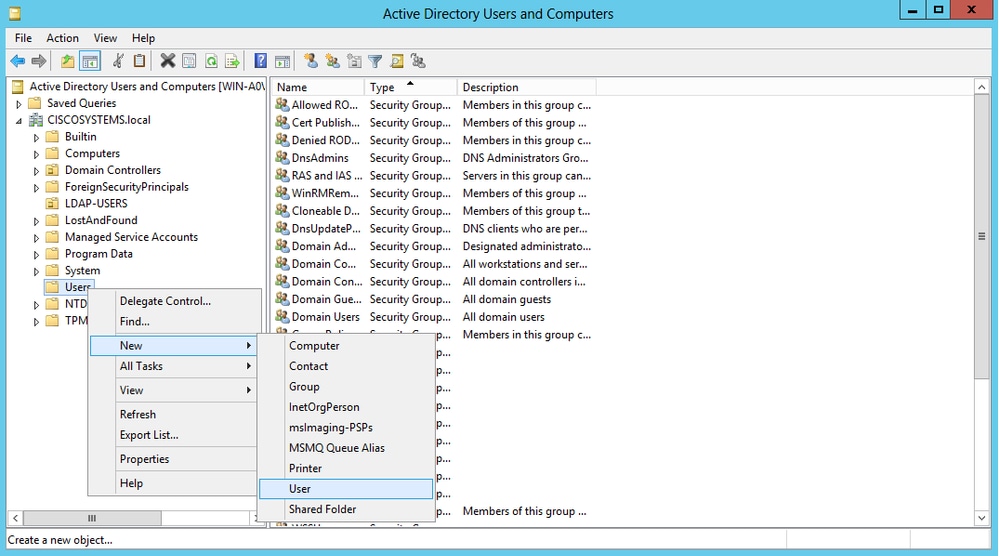
Right-click the new OU created. Navigate to LDAP-USERS> New > User from the resultant context menus in order to create a new user, as shown in the image:
-
In the User setup page, fill in the required fields as shown in this example. This example has User1 in the User logon name field.
This is the username that is verified in the LDAP database to authenticate the client. This example uses User1 in the First name and Full Name fields. Click Next.
-
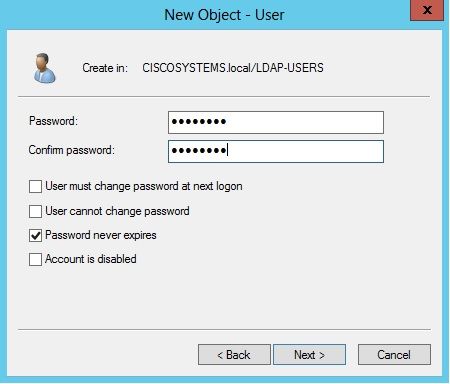
Enter a password and confirm the password. Choose the Password never expires option and click Next.
-
Click Finish.
A new user User1 is created under the OU LDAP-USERS. These are the user credentials:
Now that the user is created under an OU, the next step is to configure this user for LDAP access.
Configure the User for LDAP Access
You can choose either Anonymous or Authenticated to specify the local authentication bind method for the LDAP server. The Anonymous method allows anonymous access to the LDAP server. The Authenticated method requires that a username and password to be entered to secure access. The default value is Anonymous.
This section explains how to configure both Anonymous and Authenticated methods.
Anonymous Bind
Note: Using Anonymous Bind is not recommended. An LDAP server that allows anonymous bind does not require any type of credentialed authentication. An attacker could take advantage of the Anonymous bind entry to view files on the LDAP director.
Perform the steps in this section in order to configure anonymous user for LDAP access.
Enable Anonymous Bind Feature on the Windows 2012 Essentials Server
For any third-party applications (in our case WLC) to access Windows 2012 AD on the LDAP, the Anonymous Bind feature must be enabled on Windows 2012. By default, anonymous LDAP operations are not permitted on Windows 2012 domain controllers. Perform these steps in order to enable the Anonymous Bind feature:
-
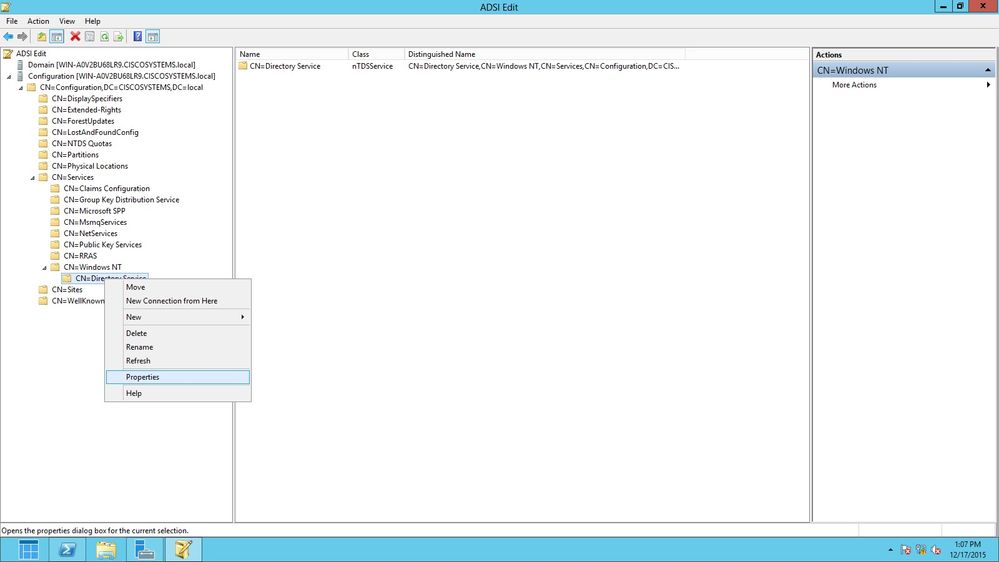
Launch the ADSI Edit tool by typing: ADSIEdit.msc in Windows PowerShell. This tool is part of the Windows 2012 support tools.
-
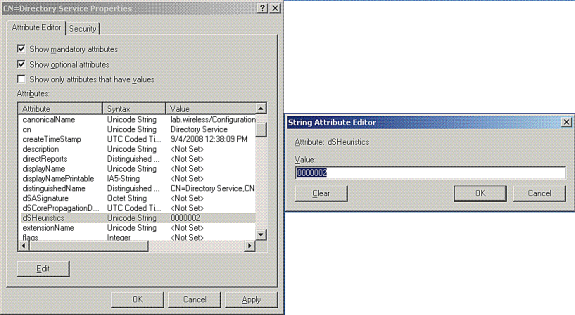
In the ADSI Edit window, expand the root domain (Configuration [WIN-A0V2BU68LR9.CISCOSYSTEMS.local]).
Navigate to CN=Services > CN=Windows NT > CN=Directory Service. Right-click the CN=Directory Service container, and choose Properties from the context menu, as shown in the image:
-
In the CN=Directory Service Properties window, under Attributes, click the dsHeuristics attribute under the Attribute field and choose Edit. In the String Attribute Editor window of this attribute, enter the value 0000002; click Apply and OK, as shown in the image. The Anonymous Bind feature is enabled on the Windows 2012 server.
Note: The last (seventh) character is the one that controls the way you can bind to LDAP service. 0 (zero) or no seventh character means that anonymous LDAP operations are disabled. If you set the seventh character to 2, it enables the Anonymous Bind feature.
Granting ANONYMOUS LOGON Access to the User
The next step is to grant ANONYMOUS LOGON access to the user User1. Complete these steps in order to achieve this:
-
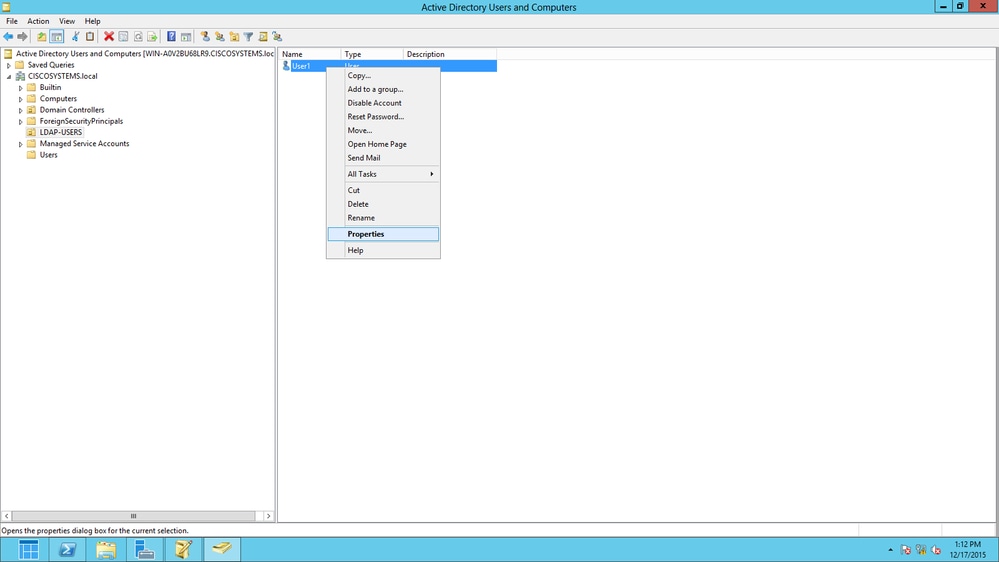
Open Active Directory Users and Computers.
-
Ensure that the View Advanced Features is checked.
-
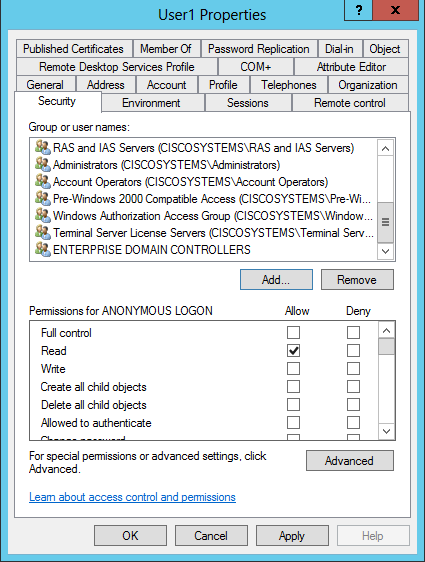
Navigate to the user User1 and right-click it. Choose Properties from the context menu. This user is identified with the first name User1.
-
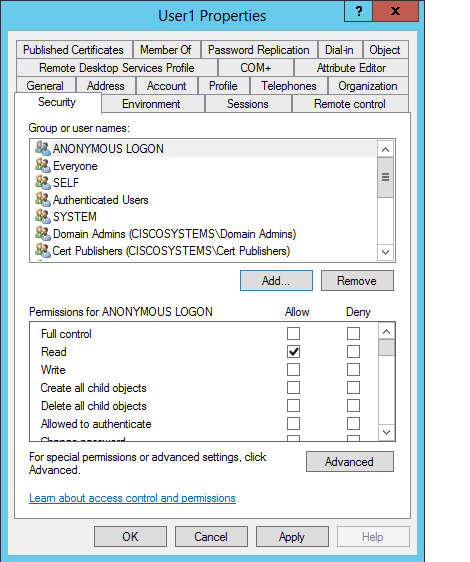
Click the Security tab, as shown in the image:
-
Click Add in the resultant window.
-
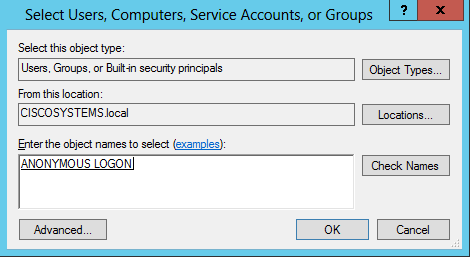
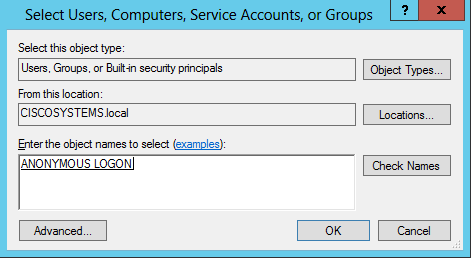
Enter ANONYMOUS LOGON under the Enter the object names to select box and acknowledge the dialog, as shown in the image:
-
In the ACL, notice that ANONYMOUS LOGON has access to some property sets of the user. Click OK. The ANONYMOUS LOGON access is granted to this user, as shown in the image:
Grant List Contents Permission on the OU
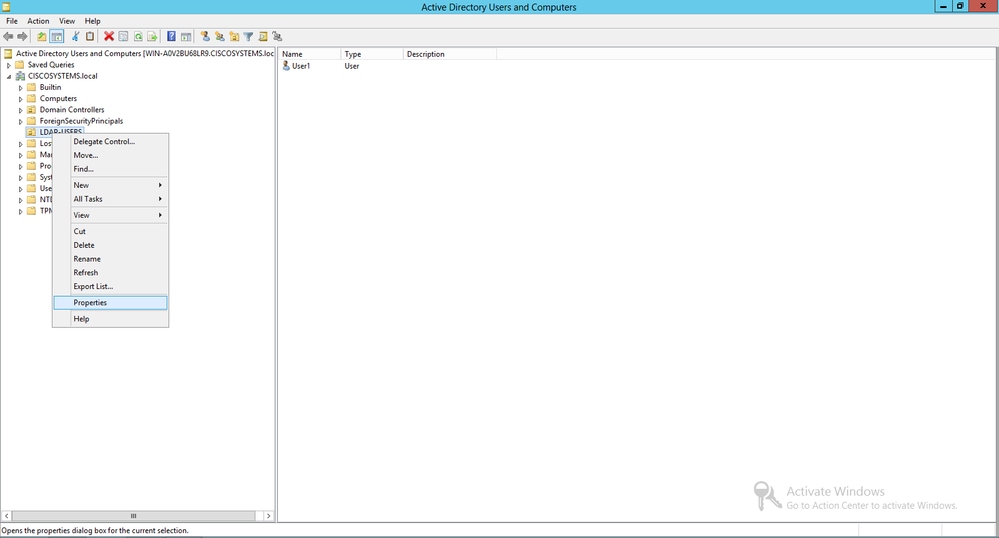
The next step is to grant at least List Contents permission to the ANONYMOUS LOGON on the OU in which the user is located. In this example, User1 is located on the OU LDAP-USERS. Complete these steps in order to achieve this:
-
In Active Directory Users and Computers, right-click the OU LDAP-USERS and choose Properties, as shown in the image:
-
Click Security.
-
Click Add. In the dialog that opens, enter ANONYMOUS LOGON and Acknowledge the dialog, as shown in the image:
Authenticated Bind
Perform the steps in this section in order to configure a user for local authentication to the LDAP server.
- Open Windows PowerShell and type servermanager.exe
- In the Server Manager window, click on AD DS. Then right-click your server name to choose Active Directory Users and Computers.
- Right-click Users. Navigate to New > User from the resultant context menus in order to create a new user.
-
In the User setup page, fill in the required fields as shown in this example. This example has WLC-admin in the User logon name field. This is the username to be used for local authentication to the LDAP server. Click Next.
-
Enter a password and confirm the password. Choose the Password never expires option and click Next.
-
Click Finish.
A new user WLC-admin is created under the Users container. These are the user credentials:
-
username: WLC-admin
-
password: Admin123
-
Granting Administrator privilages to WLC-admin
Now that the local authentication user is created, we need to grant it Administrator privilages. Complete these steps in order to achieve this:
-
Open Active Directory Users and Computers.
-
Ensure that the View Advanced Features is checked.
-
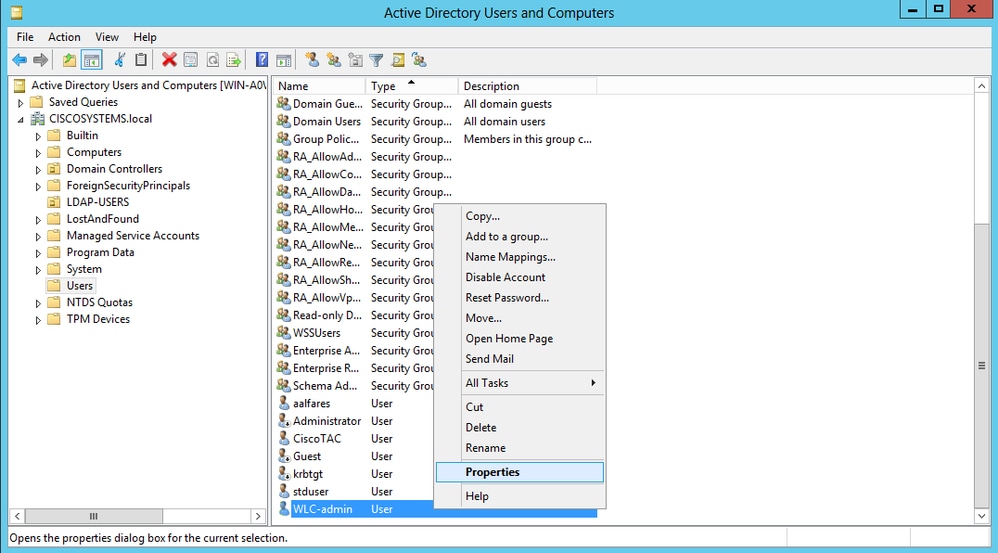
Navigate to the user WLC-admin and right-click it. Choose Properties from the context menu, as shown in the image. This user is identified with the first name WLC-admin.
- Click the Memeber Of tab, as shown in the image:
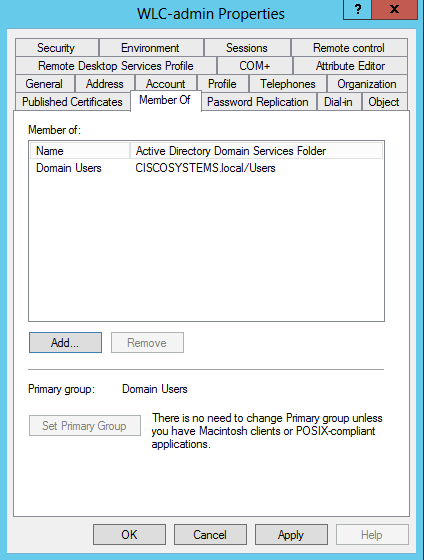
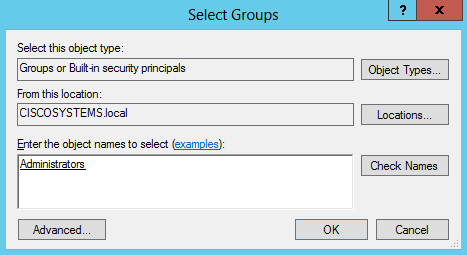
:: - Click Add. In the dialog that opens, enter Administrators and click OK, As shown in the image:
Use LDP to Identify the User Attributes
This GUI tool is a LDAP client that allows users to perform operations, such as connect, bind, search, modify, add, or delete, against any LDAP-compatible directory, such as Active Directory. LDP is used to view objects that are stored in Active Directory along with their metadata, such as security descriptors and replication metadata.
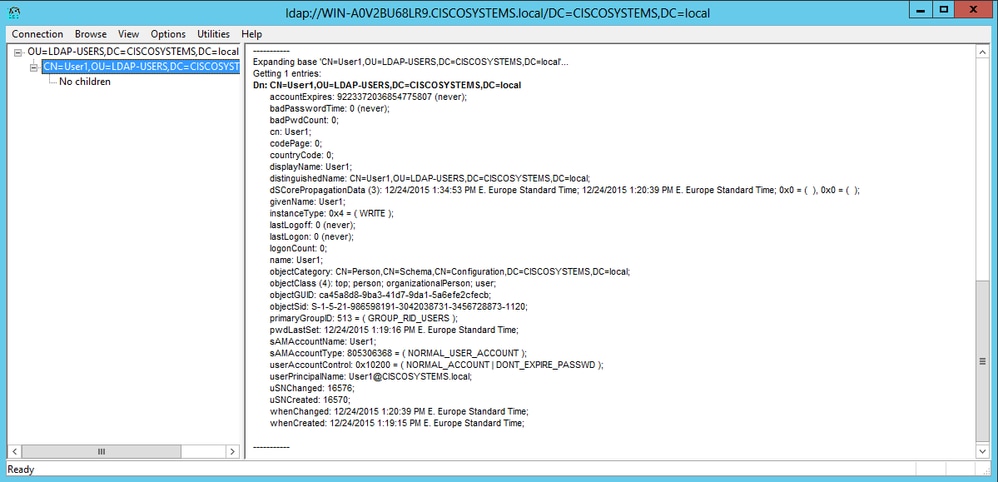
The LDP GUI tool is included when you install the Windows Server 2003 Support Tools from the product CD. This section explains how to use the LDP utility to identify the specific attributes associated to the user User1. Some of these attributes are used to fill in the LDAP server configuration parameters on the WLC, such as User Attribute type and User Object type.
-
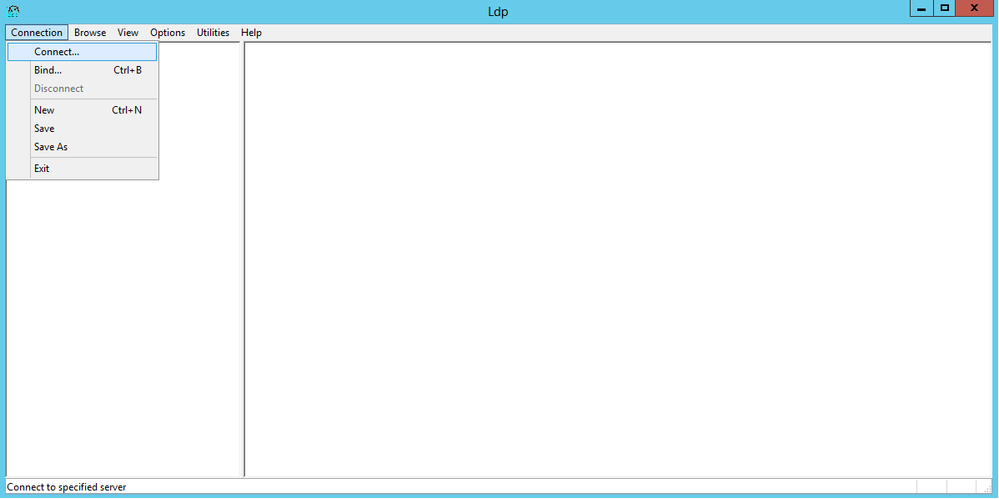
On the Windows 2012 server (even on the same LDAP server), open the Windows PowerShell and enter LDP in order to access the LDP browser.
-
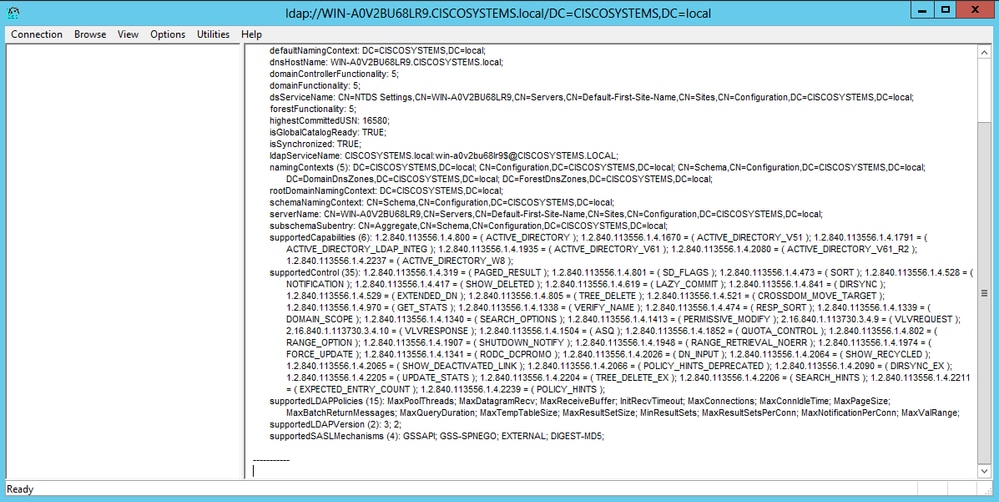
In the LDP main window, Navigate to Connection > Connect and connect to the LDAP server when you enter the IP address of the LDAP server, as shown in the image.
-
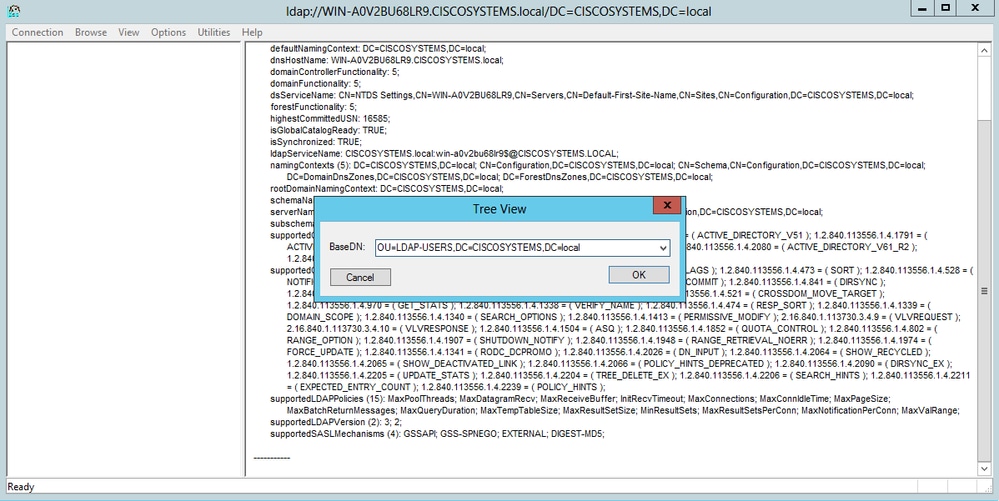
Once connected to the LDAP server, choose View from the main menu and click Tree, as shown in the image:
-
In the resultant Tree View window, enter the BaseDN of the user. In this example, User1 is located under the OU "LDAP-USERS" under the domain CISCOSYSTEMS.local. Click OK, as shown in the image:
-
The left side of the LDP browser displays the entire tree that appears under the specified BaseDN (OU=LDAP-USERS, dc=CISCOSYSTEMS, dc=local). Expand the tree to locate the user User1. This user can be identified with the CN value that represents the first name of the user. In this example, it is CN=User1. Double-click CN=User1. In the right-side pane of the LDP browser, LDP displays all the attributes associated with User1, as shown in the image:
-
When you configure the WLC for the LDAP server, in the User Attribute field, enter the name of the attribute in the user record that contains the username. From this LDP output, you can see that sAMAccountName is one attribute that contains the username "User1," so enter the sAMAccountName attribute that corresponds to the User Attribute field on the WLC.
-
When you configure the WLC for the LDAP server, in the User Object Type field, enter the value of the LDAP objectType attribute that identifies the record as a user. Often, user records have several values for the objectType attribute, some of which are unique to the user and some of which are shared with other object types. In the LDP output, CN=Person is one value that identifies the record as a user, so specify Person as the User Object Type attribute on the WLC.
The next step is to configure the WLC for the LDAP server.
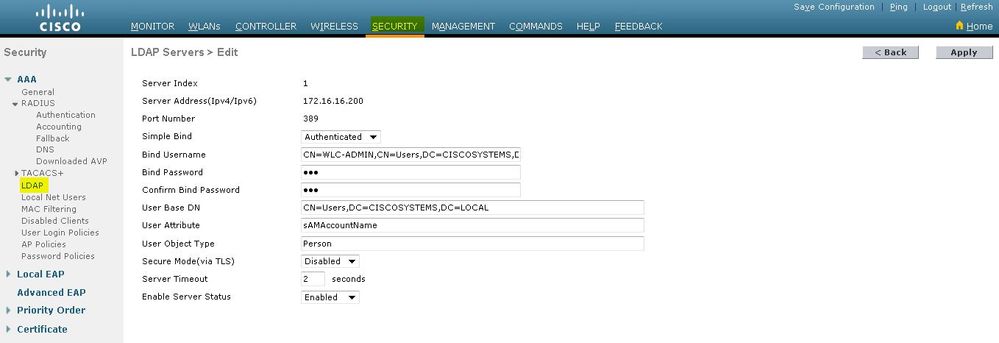
Configure WLC for LDAP Server
Now that the LDAP server is configured, the next step is to configure the WLC with details of the LDAP server. Complete these steps on the WLC GUI:
Note:This document assumes that the WLC is configured for basic operation and that the LAPs are registered to the WLC. If you are a new user who wants to setup the WLC for basic operation with LAPs, refer to Lightweight AP (LAP) Registration to a Wireless LAN Controller (WLC).
-
In the Security page of the WLC, choose AAA > LDAP from the left-side task pane in order to move to the LDAP server configuration page.
In order to add an LDAP server, click New. The LDAP Servers > New page appears.
-
In the LDAP Servers Edit page, specify the details of the LDAP server, such as the IP address of LDAP server, Port Number, Enable Server status, and so on.
-
Choose a number from the Server Index (Priority) drop-down box to specify the priority order of this server in relation to any other configured LDAP servers. You can configure up to seventeen servers. If the controller cannot reach the first server, it tries the second one in the list and so on.
-
Enter the IP address of the LDAP server in the Server IP Address field.
-
Enter the TCP port number of the LDAP server in the Port Number field. The valid range is 1 to 65535, and the default value is 389.
- for the Simple bind, we used Authenticated, for the bind username which is the location of the WLC admin user that will be used to access the LDAP server and its password
-
In the User Base DN field, enter the distinguished name (DN) of the subtree in the LDAP server that contains a list of all the users. For example, ou=organizational unit, .ou=next organizational unit, and o=corporation.com. If the tree that contains users is the base DN, enter o=corporation.com or dc=corporation, dc=com.
In this example, the user is located under the Organizational Unit (OU) LDAP-USERS, which, in turn, is created as part of the lab.wireless domain.
The User Base DN must point the full path where the user information (user credential as per EAP-FAST authentication method) is located. In this example, the user is located under the base DN OU=LDAP-USERS, DC=CISCOSYSTEMS, DC=local.
-
In the User Attribute field, enter the name of the attribute in the user record that contains the username.
In the User Object Type field, enter the value of the LDAP objectType attribute that identifies the record as a user. Often, user records have several values for the objectType attribute, some of which are unique to the user and some of which are shared with other object types
You can obtain the value of these two fields from your directory server with the LDAP browser utility that comes as part of the Windows 2012 support tools. This Microsoft LDAP browser tool is called LDP. With the help of this tool, you can know the User Base DN, User Attribute, and User Object Type fields of this particular user. Detailed information on how to use LDP to know these User specific attributes is discussed in the Using LDP to Identify the User Attributes section of this document.
-
In the Server Timeout field, enter the number of seconds between retransmissions. The valid range is 2 to 30 seconds, and the default value is 2 seconds.
-
Check the Enable Server Status check box to enable this LDAP server, or uncheck it to disable it. The default value is disabled.
-
Click Apply to commit your changes. This is an example already configured with this information:
-
-
Now that details about the LDAP server are configured on the WLC, the next step is to configure a WLAN for web authentication.
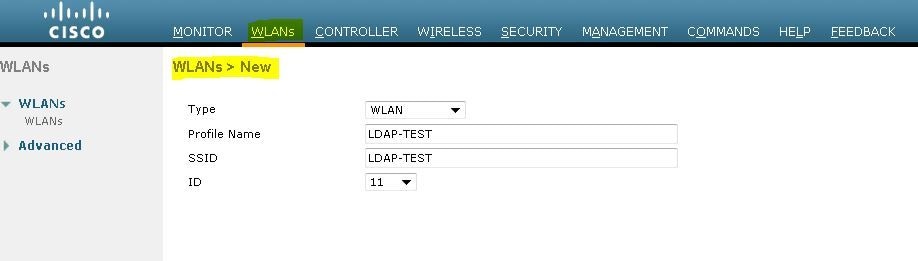
Configure the WLAN for Web Authentication
The first step is to create a WLAN for the users. Complete these steps:
-
Click WLANs from the controller GUI in order to create a WLAN.
The WLANs window appears. This window lists the WLANs configured on the controller.
-
Click New in order to configure a new WLAN.
In this example, the WLAN is named Web-Auth.
-
Click Apply.
-
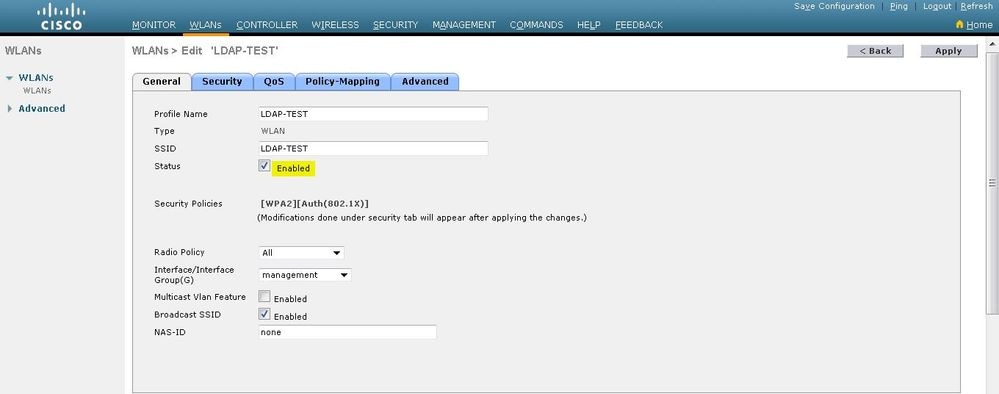
In the WLAN > Edit window, define the parameters specific to the WLAN.
-
Check the Status check box to enable the WLAN.
-
For the WLAN, choose the appropriate interface from the Interface Name field.
This example maps the management interface that connects to the WLAN Web-Auth.
-
-
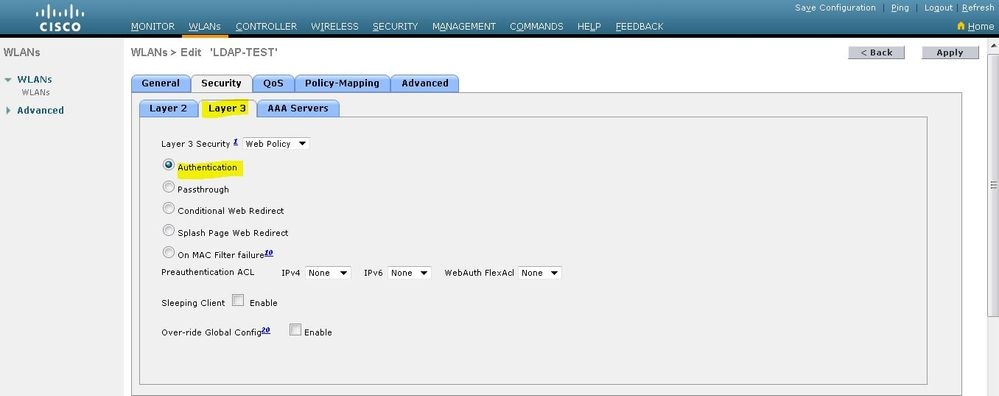
Click the Security tab. In the Layer 3 Security field, check the Web Policy check box, and choose the Authentication option.
This option is chosen because web authentication is used to authenticate the wireless clients. Check the Override Global Config check box to enable per the WLAN web authentication configuration. Choose the appropriate web authentication type from the Web Auth type drop-down menu. This example uses Internal Web Authentication.
Note: Web authentication is not supported with 802.1x authentication. This means you cannot choose 802.1x or a WPA/WPA2 with 802.1x as the Layer 2 security when you use web authentication. Web authentication is supported with all other Layer 2 security parameters.
-
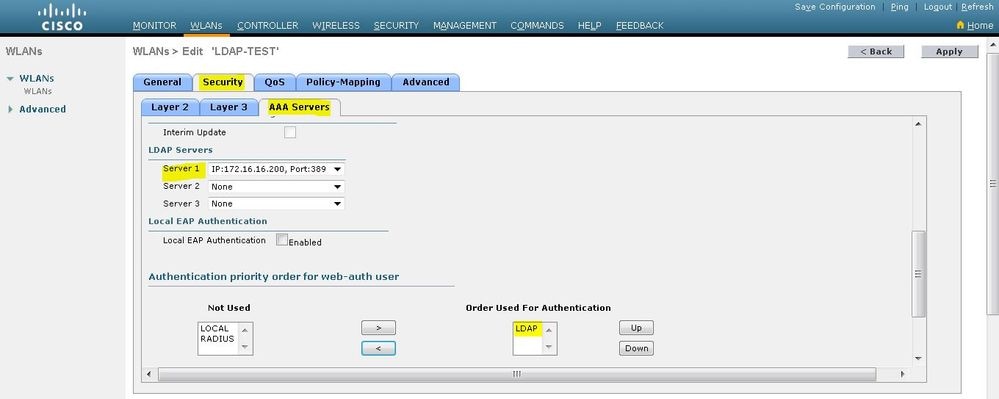
Click the AAA Servers tab. Choose the configured LDAP server from the LDAP server pull-down menu. If you use a local database or RADIUS server, you can set the authentication priority under the Authentication priority order for web-auth userfield.
-
Click Apply.
Note: In this example, Layer 2 Security methods to authenticate users are not used, so choose None in the Layer 2 Security field.
Verify
Use this section in order to confirm that your configuration works properly.
In order to verify this setup, connect a Wireless client and check if the configuration works as expected.
The wireless client comes up, and the user enters the URL, such as www.yahoo.com, in the web browser. Because the user has not been authenticated, the WLC redirects the user to the internal web login URL.
The user is prompted for the user credentials. Once the user submits the username and password, the login page takes the user credentials input and, upon submit, sends the request back to the action_URL example, http://1.1.1.1/login.html, of the WLC web server. This is provided as an input parameter to the customer redirect URL, where 1.1.1.1 is the Virtual Interface Address on the switch.
The WLC authenticates the user against the LDAP user database. After successful authentication, the WLC web server either forwards the user to the configured redirect URL or to the URL with which the client started, such as www.yahoo.com.
Troubleshoot
This section provides information you can use to troubleshoot your configuration.
Use these commands to Troubleshoot your configuration:
-
debug mac addr <client-MAC-address xx:xx:xx:xx:xx:xx>
-
debug aaa all enable
-
debug pem state enable
-
debug pem events enable
-
debug dhcp message enable
-
debug dhcp packet enable
This is a sample output from the commands debug mac addr cc:fa:00:f7:32:35
debug aaa ldap enable
(Cisco_Controller) >*pemReceiveTask: Dec 24 03:45:23.089: cc:fa:00:f7:32:35 Sent an XID frame
*apfMsConnTask_1: Dec 24 03:45:43.554: cc:fa:00:f7:32:35 Processing assoc-req station:cc:fa:00:f7:32:35 AP:00:23:eb:e5:04:10-01 thread:18ec9330
*apfMsConnTask_1: Dec 24 03:45:43.554: cc:fa:00:f7:32:35 Association received from mobile on BSSID 00:23:eb:e5:04:1f AP AP1142-1
*apfMsConnTask_1: Dec 24 03:45:43.554: cc:fa:00:f7:32:35 Global 200 Clients are allowed to AP radio
*apfMsConnTask_1: Dec 24 03:45:43.554: cc:fa:00:f7:32:35 Max Client Trap Threshold: 0 cur: 1
*apfMsConnTask_1: Dec 24 03:45:43.554: cc:fa:00:f7:32:35 Rf profile 600 Clients are allowed to AP wlan
*apfMsConnTask_1: Dec 24 03:45:43.554: cc:fa:00:f7:32:35 override for default ap group, marking intgrp NULL
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 Applying Interface policy on Mobile, role Local. Ms NAC State 2 Quarantine Vlan 0 Access Vlan 16
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 Re-applying interface policy for client
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) Changing IPv4 ACL 'none' (ACL ID 255) ===> 'none' (ACL ID 255) --- (caller apf_policy.c:2699)
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) Changing IPv6 ACL 'none' (ACL ID 255) ===> 'none' (ACL ID 255) --- (caller apf_policy.c:2720)
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 apfApplyWlanPolicy: Apply WLAN Policy over PMIPv6 Client Mobility Type, Tunnel User - 0
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 In processSsidIE:6246 setting Central switched to TRUE
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 In processSsidIE:6249 apVapId = 1 and Split Acl Id = 65535
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 Applying site-specific Local Bridging override for station cc:fa:00:f7:32:35 - vapId 1, site 'default-group', interface 'management'
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 Applying Local Bridging Interface Policy for station cc:fa:00:f7:32:35 - vlan 16, interface id 0, interface 'management'
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 processSsidIE statusCode is 0 and status is 0
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 processSsidIE ssid_done_flag is 0 finish_flag is 0
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 STA - rates (3): 24 164 48 0 0 0 0 0 0 0 0 0 0 0 0 0
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 suppRates statusCode is 0 and gotSuppRatesElement is 1
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 AID 2 in Assoc Req from flex AP 00:23:eb:e5:04:10 is same as in mscb cc:fa:00:f7:32:35
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 apfMs1xStateDec
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) Change state to START (0) last state WEBAUTH_REQD (8)
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 pemApfAddMobileStation2: APF_MS_PEM_WAIT_L2_AUTH_COMPLETE = 0.
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 172.16.16.122 START (0) Initializing policy
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 172.16.16.122 START (0) Change state to AUTHCHECK (2) last state START (0)
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 172.16.16.122 AUTHCHECK (2) Change state to L2AUTHCOMPLETE (4) last state AUTHCHECK (2)
*pemReceiveTask: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 172.16.16.122 Removed NPU entry.
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 Not Using WMM Compliance code qosCap 00
*apfMsConnTask_1: Dec 24 03:45:43.555: cc:fa:00:f7:32:35 172.16.16.122 L2AUTHCOMPLETE (4) Plumbed mobile LWAPP rule on AP 00:23:eb:e5:04:10 vapId 1 apVapId 1 flex-acl-name:
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 172.16.16.122 L2AUTHCOMPLETE (4) Change state to WEBAUTH_REQD (8) last state L2AUTHCOMPLETE (4)
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) pemApfAddMobileStation2 3802, Adding TMP rule
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) Adding Fast Path rule
type = Airespace AP Client - ACL passthru
on AP 00:23:eb:e5:04:10, slot 1, interface = 1, QOS = 0
IPv4 ACL I
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) Fast Path rule (contd...) 802.1P = 0, DSCP = 0, TokenID = 15206, IntfId = 0 Local Bridging Vlan = 16, Local Bridging intf id = 0
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) Fast Path rule (contd...) AVC Ratelimit: AppID = 0 ,AppAction = 4, AppToken = 15206 AverageRate = 0, BurstRate = 0
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) Fast Path rule (contd...) AVC Ratelimit: AppID = 0 ,AppAction = 4, AppToken = 15206 AverageRate = 0, BurstRate = 0
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) Fast Path rule (contd...) AVC Ratelimit: AppID = 0 ,AppAction = 4, AppToken = 15206 AverageRate = 0, BurstRate = 0
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) Successfully plumbed mobile rule (IPv4 ACL ID 255, IPv6 ACL ID 255, L2 ACL ID 255)
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) pemApfAddMobileStation2 3911, Adding TMP rule
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) Replacing Fast Path rule
type = Airespace AP Client - ACL passthru
on AP 00:23:eb:e5:04:10, slot 1, interface = 1, QOS = 0
IPv4 AC
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) Fast Path rule (contd...) 802.1P = 0, DSCP = 0, TokenID = 15206, IntfId = 0 Local Bridging Vlan = 16, Local Bridging intf id = 0
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) Fast Path rule (contd...) AVC Ratelimit: AppID = 0 ,AppAction = 4, AppToken = 15206 AverageRate = 0, BurstRate = 0
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) Fast Path rule (contd...) AVC Ratelimit: AppID = 0 ,AppAction = 4, AppToken = 15206 AverageRate = 0, BurstRate = 0
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) Fast Path rule (contd...) AVC Ratelimit: AppID = 0 ,AppAction = 4, AppToken = 15206 AverageRate = 0, BurstRate = 0
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) Successfully plumbed mobile rule (IPv4 ACL ID 255, IPv6 ACL ID 255, L2 ACL ID 255)
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 apfPemAddUser2 (apf_policy.c:359) Changing state for mobile cc:fa:00:f7:32:35 on AP 00:23:eb:e5:04:10 from Associated to Associated
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 apfPemAddUser2:session timeout forstation cc:fa:00:f7:32:35 - Session Tout 1800, apfMsTimeOut '1800' and sessionTimerRunning flag is 1
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 Scheduling deletion of Mobile Station: (callerId: 49) in 1800 seconds
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 Func: apfPemAddUser2, Ms Timeout = 1800, Session Timeout = 1800
*apfMsConnTask_1: Dec 24 03:45:43.556: cc:fa:00:f7:32:35 Sending assoc-resp with status 0 station:cc:fa:00:f7:32:35 AP:00:23:eb:e5:04:10-01 on apVapId 1
*apfMsConnTask_1: Dec 24 03:45:43.557: cc:fa:00:f7:32:35 Sending Assoc Response to station on BSSID 00:23:eb:e5:04:1f (status 0) ApVapId 1 Slot 1
*apfMsConnTask_1: Dec 24 03:45:43.557: cc:fa:00:f7:32:35 apfProcessAssocReq (apf_80211.c:10187) Changing state for mobile cc:fa:00:f7:32:35 on AP 00:23:eb:e5:04:10 from Associated to Associated
*pemReceiveTask: Dec 24 03:45:43.557: cc:fa:00:f7:32:35 172.16.16.122 Added NPU entry of type 2, dtlFlags 0x0
*pemReceiveTask: Dec 24 03:45:43.557: cc:fa:00:f7:32:35 Sent an XID frame
*pemReceiveTask: Dec 24 03:45:43.557: cc:fa:00:f7:32:35 172.16.16.122 Added NPU entry of type 2, dtlFlags 0x0
*pemReceiveTask: Dec 24 03:45:43.558: cc:fa:00:f7:32:35 Sent an XID frame
*DHCP Socket Task: Dec 24 03:45:43.708: cc:fa:00:f7:32:35 DHCP received op BOOTREQUEST (1) (len 322,vlan 16, port 1, encap 0xec03, xid 0x62743488)
*DHCP Socket Task: Dec 24 03:45:43.708: cc:fa:00:f7:32:35 DHCP (encap type 0xec03) mstype 0ff:ff:ff:ff:ff:ff
*DHCP Socket Task: Dec 24 03:45:43.708: cc:fa:00:f7:32:35 DHCP selecting relay 1 - control block settings:
dhcpServer: 172.16.16.25, dhcpNetmask: 255.255.254.0,
dhcpGateway: 172.16.16.1, dhcpRelay: 172.16.16.25 VLAN: 16
*DHCP Socket Task: Dec 24 03:45:43.708: cc:fa:00:f7:32:35 DHCP mscbVapLocalAddr=172.16.16.25 mscbVapLocalNetMask= 255.255.254.0 mscbdhcpRelay=172.16.16.25
*DHCP Socket Task: Dec 24 03:45:43.708: cc:fa:00:f7:32:35 DHCP selected relay 1 - 172.16.16.25 (local address 172.16.16.25, gateway 172.16.16.25, VLAN 16, port 1)
*DHCP Socket Task: Dec 24 03:45:43.709: cc:fa:00:f7:32:35 DHCP selecting relay 2 - control block settings:
dhcpServer: 172.16.16.25, dhcpNetmask: 255.255.254.0,
dhcpGateway: 172.16.16.1, dhcpRelay: 172.16.16.25 VLAN: 16
*DHCP Socket Task: Dec 24 03:45:43.709: cc:fa:00:f7:32:35 DHCP selected relay 2 - NONE
*DHCP Socket Task: Dec 24 03:45:43.709: cc:fa:00:f7:32:35 DHCP selecting relay 1 - control block settings:
dhcpServer: 172.16.16.25, dhcpNetmask: 0.0.0.0,
dhcpGateway: 0.0.0.0, dhcpRelay: 172.16.16.25 VLAN: 16
*DHCP Socket Task: Dec 24 03:45:43.709: cc:fa:00:f7:32:35 DHCP mscbVapLocalAddr=172.16.16.25 mscbVapLocalNetMask= 255.255.254.0 mscbdhcpRelay=172.16.16.25
*DHCP Socket Task: Dec 24 03:45:43.709: cc:fa:00:f7:32:35 DHCP selected relay 1 - 172.16.16.25 (local address 172.16.16.25, gateway 172.16.16.25, VLAN 16, port 1)
*DHCP Socket Task: Dec 24 03:45:43.709: cc:fa:00:f7:32:35 DHCP transmitting DHCP DISCOVER (1)
*DHCP Socket Task: Dec 24 03:45:43.709: cc:fa:00:f7:32:35 DHCP op: BOOTREQUEST, htype: Ethernet, hlen: 6, hops: 1
*DHCP Socket Task: Dec 24 03:45:43.709: cc:fa:00:f7:32:35 DHCP xid: 0x62743488 (1651782792), secs: 0, flags: 0
*DHCP Socket Task: Dec 24 03:45:43.709: cc:fa:00:f7:32:35 DHCP chaddr: cc:fa:00:f7:32:35
*DHCP Socket Task: Dec 24 03:45:43.709: cc:fa:00:f7:32:35 DHCP ciaddr: 0.0.0.0, yiaddr: 0.0.0.0
*DHCP Socket Task: Dec 24 03:45:43.709: cc:fa:00:f7:32:35 DHCP siaddr: 0.0.0.0, giaddr: 172.16.16.25
*DHCP Socket Task: Dec 24 03:45:43.709: cc:fa:00:f7:32:35 DHCP selecting relay 2 - control block settings:
dhcpServer: 172.16.16.25, dhcpNetmask: 0.0.0.0,
dhcpGateway: 0.0.0.0, dhcpRelay: 172.16.16.25 VLAN: 16
*DHCP Socket Task: Dec 24 03:45:43.709: cc:fa:00:f7:32:35 DHCP selected relay 2 - NONE
*DHCP Proxy Task: Dec 24 03:45:43.709: cc:fa:00:f7:32:35 DHCP received op BOOTREPLY (2) (len 572,vlan 0, port 0, encap 0x0, xid 0x62743488)
*DHCP Proxy Task: Dec 24 03:45:43.710: cc:fa:00:f7:32:35 DHCP sending REPLY to STA (len 418, port 1, vlan 16)
*DHCP Proxy Task: Dec 24 03:45:43.710: cc:fa:00:f7:32:35 DHCP transmitting DHCP OFFER (2)
*DHCP Proxy Task: Dec 24 03:45:43.710: cc:fa:00:f7:32:35 DHCP op: BOOTREPLY, htype: Ethernet, hlen: 6, hops: 0
*DHCP Proxy Task: Dec 24 03:45:43.710: cc:fa:00:f7:32:35 DHCP xid: 0x62743488 (1651782792), secs: 0, flags: 0
*DHCP Proxy Task: Dec 24 03:45:43.710: cc:fa:00:f7:32:35 DHCP chaddr: cc:fa:00:f7:32:35
*DHCP Proxy Task: Dec 24 03:45:43.710: cc:fa:00:f7:32:35 DHCP ciaddr: 0.0.0.0, yiaddr: 172.16.16.122
*DHCP Proxy Task: Dec 24 03:45:43.710: cc:fa:00:f7:32:35 DHCP siaddr: 0.0.0.0, giaddr: 0.0.0.0
*DHCP Proxy Task: Dec 24 03:45:43.710: cc:fa:00:f7:32:35 DHCP server id: 1.1.1.1 rcvd server id: 172.16.16.25
*DHCP Socket Task: Dec 24 03:45:43.714: cc:fa:00:f7:32:35 DHCP received op BOOTREQUEST (1) (len 334,vlan 16, port 1, encap 0xec03, xid 0x62743488)
*DHCP Socket Task: Dec 24 03:45:43.714: cc:fa:00:f7:32:35 DHCP (encap type 0xec03) mstype 0ff:ff:ff:ff:ff:ff
*DHCP Socket Task: Dec 24 03:45:43.714: cc:fa:00:f7:32:35 DHCP selecting relay 1 - control block settings:
dhcpServer: 172.16.16.25, dhcpNetmask: 0.0.0.0,
dhcpGateway: 0.0.0.0, dhcpRelay: 172.16.16.25 VLAN: 16
*DHCP Socket Task: Dec 24 03:45:43.714: cc:fa:00:f7:32:35 DHCP mscbVapLocalAddr=172.16.16.25 mscbVapLocalNetMask= 255.255.254.0 mscbdhcpRelay=172.16.16.25
*DHCP Socket Task: Dec 24 03:45:43.714: cc:fa:00:f7:32:35 DHCP selected relay 1 - 172.16.16.25 (local address 172.16.16.25, gateway 172.16.16.25, VLAN 16, port 1)
*DHCP Socket Task: Dec 24 03:45:43.714: cc:fa:00:f7:32:35 DHCP transmitting DHCP REQUEST (3)
*DHCP Socket Task: Dec 24 03:45:43.714: cc:fa:00:f7:32:35 DHCP op: BOOTREQUEST, htype: Ethernet, hlen: 6, hops: 1
*DHCP Socket Task: Dec 24 03:45:43.714: cc:fa:00:f7:32:35 DHCP xid: 0x62743488 (1651782792), secs: 0, flags: 0
*DHCP Socket Task: Dec 24 03:45:43.714: cc:fa:00:f7:32:35 DHCP chaddr: cc:fa:00:f7:32:35
*DHCP Socket Task: Dec 24 03:45:43.715: cc:fa:00:f7:32:35 DHCP ciaddr: 0.0.0.0, yiaddr: 0.0.0.0
*DHCP Socket Task: Dec 24 03:45:43.715: cc:fa:00:f7:32:35 DHCP siaddr: 0.0.0.0, giaddr: 172.16.16.25
*DHCP Socket Task: Dec 24 03:45:43.715: cc:fa:00:f7:32:35 DHCP requested ip: 172.16.16.122
*DHCP Socket Task: Dec 24 03:45:43.715: cc:fa:00:f7:32:35 DHCP server id: 172.16.16.25 rcvd server id: 1.1.1.1
*DHCP Socket Task: Dec 24 03:45:43.715: cc:fa:00:f7:32:35 DHCP selecting relay 2 - control block settings:
dhcpServer: 172.16.16.25, dhcpNetmask: 0.0.0.0,
dhcpGateway: 0.0.0.0, dhcpRelay: 172.16.16.25 VLAN: 16
*DHCP Socket Task: Dec 24 03:45:43.715: cc:fa:00:f7:32:35 DHCP selected relay 2 - NONE
*DHCP Proxy Task: Dec 24 03:45:43.715: cc:fa:00:f7:32:35 DHCP received op BOOTREPLY (2) (len 572,vlan 0, port 0, encap 0x0, xid 0x62743488)
*DHCP Proxy Task: Dec 24 03:45:43.715: cc:fa:00:f7:32:35 DHCP setting server from ACK (mscb=0x40e64b88 ip=0xac10107a)(server 172.16.16.25, yiaddr 172.16.16.122)
*DHCP Proxy Task: Dec 24 03:45:43.715: cc:fa:00:f7:32:35 DHCP sending REPLY to STA (len 418, port 1, vlan 16)
*DHCP Proxy Task: Dec 24 03:45:43.715: cc:fa:00:f7:32:35 DHCP transmitting DHCP ACK (5)
*DHCP Proxy Task: Dec 24 03:45:43.715: cc:fa:00:f7:32:35 DHCP op: BOOTREPLY, htype: Ethernet, hlen: 6, hops: 0
*DHCP Proxy Task: Dec 24 03:45:43.715: cc:fa:00:f7:32:35 DHCP xid: 0x62743488 (1651782792), secs: 0, flags: 0
*DHCP Proxy Task: Dec 24 03:45:43.715: cc:fa:00:f7:32:35 DHCP chaddr: cc:fa:00:f7:32:35
*DHCP Proxy Task: Dec 24 03:45:43.715: cc:fa:00:f7:32:35 DHCP ciaddr: 0.0.0.0, yiaddr: 172.16.16.122
*DHCP Proxy Task: Dec 24 03:45:43.715: cc:fa:00:f7:32:35 DHCP siaddr: 0.0.0.0, giaddr: 0.0.0.0
*DHCP Proxy Task: Dec 24 03:45:43.715: cc:fa:00:f7:32:35 DHCP server id: 1.1.1.1 rcvd server id: 172.16.16.25
*ewmwebWebauth1: Dec 24 03:46:01.222: cc:fa:00:f7:32:35 Username entry (User1) created for mobile, length = 7
*ewmwebWebauth1: Dec 24 03:46:01.222: cc:fa:00:f7:32:35 Username entry (User1) created in mscb for mobile, length = 7
*aaaQueueReader: Dec 24 03:46:01.222: AuthenticationRequest: 0x2b6bdc3c
*aaaQueueReader: Dec 24 03:46:01.222: Callback.....................................0x12088c50
*aaaQueueReader: Dec 24 03:46:01.222: protocolType.................................0x00000002
*aaaQueueReader: Dec 24 03:46:01.222: proxyState...................................CC:FA:00:F7:32:35-00:00
*aaaQueueReader: Dec 24 03:46:01.222: Packet contains 15 AVPs (not shown)
*LDAP DB Task 1: Dec 24 03:46:01.222: ldapTask [1] received msg 'REQUEST' (2) in state 'IDLE' (1)
*LDAP DB Task 1: Dec 24 03:46:01.222: LDAP server 1 changed state to INIT
*LDAP DB Task 1: Dec 24 03:46:01.223: LDAP_OPT_REFERRALS = -1
*LDAP DB Task 1: Dec 24 03:46:01.223: ldapInitAndBind [1] called lcapi_init (rc = 0 - Success)
*LDAP DB Task 1: Dec 24 03:46:01.225: ldapInitAndBind [1] configured Method Authenticated lcapi_bind (rc = 0 - Success)
*LDAP DB Task 1: Dec 24 03:46:01.225: LDAP server 1 changed state to CONNECTED
*LDAP DB Task 1: Dec 24 03:46:01.225: disabled LDAP_OPT_REFERRALS
*LDAP DB Task 1: Dec 24 03:46:01.225: LDAP_CLIENT: UID Search (base=CN=Users,DC=CISCOSYSTEMS,DC=local, pattern=(&(objectclass=Person)(sAMAccountName=User1)))
*LDAP DB Task 1: Dec 24 03:46:01.226: LDAP_CLIENT: ldap_search_ext_s returns 0 -5
*LDAP DB Task 1: Dec 24 03:46:01.226: LDAP_CLIENT: Returned 2 msgs including 0 references
*LDAP DB Task 1: Dec 24 03:46:01.226: LDAP_CLIENT: Returned msg 1 type 0x64
*LDAP DB Task 1: Dec 24 03:46:01.226: LDAP_CLIENT: Received 1 attributes in search entry msg
*LDAP DB Task 1: Dec 24 03:46:01.226: LDAP_CLIENT: Returned msg 2 type 0x65
*LDAP DB Task 1: Dec 24 03:46:01.226: LDAP_CLIENT : No matched DN
*LDAP DB Task 1: Dec 24 03:46:01.226: LDAP_CLIENT : Check result error 0 rc 1013
*LDAP DB Task 1: Dec 24 03:46:01.226: LDAP_CLIENT: Received no referrals in search result msg
*LDAP DB Task 1: Dec 24 03:46:01.226: ldapAuthRequest [1] 172.16.16.200 - 389 called lcapi_query base="CN=Users,DC=CISCOSYSTEMS,DC=local" type="Person" attr="sAMAccountName" user="User1" (rc = 0 - Success)
*LDAP DB Task 1: Dec 24 03:46:01.226: Attempting user bind with username CN=User1,CN=Users,DC=CISCOSYSTEMS,DC=local
*LDAP DB Task 1: Dec 24 03:46:01.228: LDAP ATTR> dn = CN=User1,CN=Users,DC=CISCOSYSTEMS,DC=local (size 45)
*LDAP DB Task 1: Dec 24 03:46:01.228: Handling LDAP response Success
*LDAP DB Task 1: Dec 24 03:46:01.228: Authenticated bind : Closing the binded session
*ewmwebWebauth1: Dec 24 03:46:01.228: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_REQD (8) Change state to WEBAUTH_NOL3SEC (14) last state WEBAUTH_REQD (8)
*ewmwebWebauth1: Dec 24 03:46:01.228: cc:fa:00:f7:32:35 apfMsRunStateInc
*LDAP DB Task 1: Dec 24 03:46:01.228: ldapClose [1] called lcapi_close (rc = 0 - Success)
*ewmwebWebauth1: Dec 24 03:46:01.228: cc:fa:00:f7:32:35 172.16.16.122 WEBAUTH_NOL3SEC (14) Change state to RUN (20) last state WEBAUTH_NOL3SEC (14)
*ewmwebWebauth1: Dec 24 03:46:01.228: cc:fa:00:f7:32:35 Stopping deletion of Mobile Station: (callerId: 74)
*ewmwebWebauth1: Dec 24 03:46:01.228: cc:fa:00:f7:32:35 Setting Session Timeout to 1800 sec - starting session timer for the mobile
*ewmwebWebauth1: Dec 24 03:46:01.228: cc:fa:00:f7:32:35 172.16.16.122 RUN (20) Reached PLUMBFASTPATH: from line 6972
*ewmwebWebauth1: Dec 24 03:46:01.228: cc:fa:00:f7:32:35 172.16.16.122 RUN (20) Replacing Fast Path rule
type = Airespace AP Client
on AP 00:23:eb:e5:04:10, slot 1, interface = 1, QOS = 0
IPv4 ACL ID = 255, IPv6 ACL ID
*ewmwebWebauth1: Dec 24 03:46:01.228: cc:fa:00:f7:32:35 172.16.16.122 RUN (20) Fast Path rule (contd...) 802.1P = 0, DSCP = 0, TokenID = 15206, IntfId = 0 Local Bridging Vlan = 16, Local Bridging intf id = 0
*ewmwebWebauth1: Dec 24 03:46:01.228: cc:fa:00:f7:32:35 172.16.16.122 RUN (20) Fast Path rule (contd...) AVC Ratelimit: AppID = 0 ,AppAction = 4, AppToken = 15206 AverageRate = 0, BurstRate = 0
*ewmwebWebauth1: Dec 24 03:46:01.228: cc:fa:00:f7:32:35 172.16.16.122 RUN (20) Fast Path rule (contd...) AVC Ratelimit: AppID = 0 ,AppAction = 4, AppToken = 15206 AverageRate = 0, BurstRate = 0
*ewmwebWebauth1: Dec 24 03:46:01.228: cc:fa:00:f7:32:35 172.16.16.122 RUN (20) Fast Path rule (contd...) AVC Ratelimit: AppID = 0 ,AppAction = 4, AppToken = 15206 AverageRate = 0, BurstRate = 0
*ewmwebWebauth1: Dec 24 03:46:01.229: cc:fa:00:f7:32:35 172.16.16.122 RUN (20) Successfully plumbed mobile rule (IPv4 ACL ID 255, IPv6 ACL ID 255, L2 ACL ID 255)
*pemReceiveTask: Dec 24 03:46:01.229: cc:fa:00:f7:32:35 172.16.16.122 Added NPU entry of type 1, dtlFlags 0x0
(Cisco_Controller) >show client detail cc:fa:00:f7:32:35
Client MAC Address............................... cc:fa:00:f7:32:35
Client Username ................................. User1
AP MAC Address................................... 00:23:eb:e5:04:10
AP Name.......................................... AP1142-1
AP radio slot Id................................. 1
Client State..................................... Associated
Client User Group................................ User1
Client NAC OOB State............................. Access
Wireless LAN Id.................................. 1
Wireless LAN Network Name (SSID)................. LDAP-TEST
Wireless LAN Profile Name........................ LDAP-TEST
Hotspot (802.11u)................................ Not Supported
BSSID............................................ 00:23:eb:e5:04:1f
Connected For ................................... 37 secs
Channel.......................................... 36
IP Address....................................... 172.16.16.122
Gateway Address.................................. 172.16.16.1
Netmask.......................................... 255.255.254.0
Association Id................................... 2
Authentication Algorithm......................... Open System
Reason Code...................................... 1
Status Code...................................... 0
--More or (q)uit current module or <ctrl-z> to abort
Session Timeout.................................. 1800
Client CCX version............................... No CCX support
QoS Level........................................ Silver
Avg data Rate.................................... 0
Burst data Rate.................................. 0
Avg Real time data Rate.......................... 0
Burst Real Time data Rate........................ 0
802.1P Priority Tag.............................. disabled
CTS Security Group Tag........................... Not Applicable
KTS CAC Capability............................... No
Qos Map Capability............................... No
WMM Support...................................... Enabled
APSD ACs....................................... BK BE VI VO
Current Rate..................................... m7
Supported Rates.................................. 12.0,18.0,24.0
Mobility State................................... Local
Mobility Move Count.............................. 0
Security Policy Completed........................ Yes
Policy Manager State............................. RUN
Audit Session ID................................. ac10101900000005567b69f8
AAA Role Type.................................... none
Local Policy Applied............................. none
IPv4 ACL Name.................................... none
--More or (q)uit current module or <ctrl-z> to abort
FlexConnect ACL Applied Status................... Unavailable
IPv4 ACL Applied Status.......................... Unavailable
IPv6 ACL Name.................................... none
IPv6 ACL Applied Status.......................... Unavailable
Layer2 ACL Name.................................. none
Layer2 ACL Applied Status........................ Unavailable
Client Type...................................... SimpleIP
mDNS Status...................................... Enabled
mDNS Profile Name................................ default-mdns-profile
No. of mDNS Services Advertised.................. 0
Policy Type...................................... N/A
Encryption Cipher................................ None
Protected Management Frame ...................... No
Management Frame Protection...................... No
EAP Type......................................... Unknown
FlexConnect Data Switching....................... Central
FlexConnect Dhcp Status.......................... Central
FlexConnect Vlan Based Central Switching......... No
FlexConnect Authentication....................... Central
FlexConnect Central Association.................. No
Interface........................................ management
VLAN............................................. 16
Quarantine VLAN.................................. 0
--More or (q)uit current module or <ctrl-z> to abort
Access VLAN...................................... 16
Local Bridging VLAN.............................. 16
Client Capabilities:
CF Pollable................................ Not implemented
CF Poll Request............................ Not implemented
Short Preamble............................. Not implemented
PBCC....................................... Not implemented
Channel Agility............................ Not implemented
Listen Interval............................ 10
Fast BSS Transition........................ Not implemented
11v BSS Transition......................... Not implemented
Client Wifi Direct Capabilities:
WFD capable................................ No
Manged WFD capable......................... No
Cross Connection Capable................... No
Support Concurrent Operation............... No
Fast BSS Transition Details:
Client Statistics:
Number of Bytes Received................... 16853
Number of Bytes Sent....................... 31839
Total Number of Bytes Sent................. 31839
Total Number of Bytes Recv................. 16853
Number of Bytes Sent (last 90s)............ 31839
--More or (q)uit current module or <ctrl-z> to abort
Number of Bytes Recv (last 90s)............ 16853
Number of Packets Received................. 146
Number of Packets Sent..................... 92
Number of Interim-Update Sent.............. 0
Number of EAP Id Request Msg Timeouts...... 0
Number of EAP Id Request Msg Failures...... 0
Number of EAP Request Msg Timeouts......... 0
Number of EAP Request Msg Failures......... 0
Number of EAP Key Msg Timeouts............. 0
Number of EAP Key Msg Failures............. 0
Number of Data Retries..................... 2
Number of RTS Retries...................... 0
Number of Duplicate Received Packets....... 0
Number of Decrypt Failed Packets........... 0
Number of Mic Failured Packets............. 0
Number of Mic Missing Packets.............. 0
Number of RA Packets Dropped............... 0
Number of Policy Errors.................... 0
Radio Signal Strength Indicator............ -48 dBm
Signal to Noise Ratio...................... 41 dB
Client Rate Limiting Statistics:
Number of Data Packets Received............ 0
Number of Data Rx Packets Dropped.......... 0
--More or (q)uit current module or <ctrl-z> to abort
Number of Data Bytes Received.............. 0
Number of Data Rx Bytes Dropped............ 0
Number of Realtime Packets Received........ 0
Number of Realtime Rx Packets Dropped...... 0
Number of Realtime Bytes Received.......... 0
Number of Realtime Rx Bytes Dropped........ 0
Number of Data Packets Sent................ 0
Number of Data Tx Packets Dropped.......... 0
Number of Data Bytes Sent.................. 0
Number of Data Tx Bytes Dropped............ 0
Number of Realtime Packets Sent............ 0
Number of Realtime Tx Packets Dropped...... 0
Number of Realtime Bytes Sent.............. 0
Number of Realtime Tx Bytes Dropped........ 0
Nearby AP Statistics:
AP1142-1(slot 0)
antenna0: 25 secs ago.................... -37 dBm
antenna1: 25 secs ago.................... -37 dBm
AP1142-1(slot 1)
antenna0: 25 secs ago.................... -44 dBm
antenna1: 25 secs ago.................... -57 dBm
DNS Server details:
DNS server IP ............................. 0.0.0.0
--More or (q)uit current module or <ctrl-z> to abort
DNS server IP ............................. 0.0.0.0
Assisted Roaming Prediction List details:
Client Dhcp Required: False
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
19-Sep-2008
|
Initial Release |
Contributed by Cisco Engineers
- Ayman AlfaresCisco TAC
- Yahya JaberCisco TAC
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)


 Feedback
Feedback