The move to a cloud-first strategy creates new challenges. Learn how Catalyst SD-WAN can help you navigate them.
The network your organization can count on
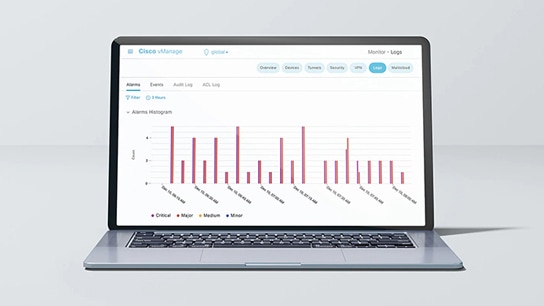
Simplify your IT infrastructure and enjoy secure connectivity from anywhere. Built-in automation, multicloud capabilities, analytics, predictivity, and security let you focus on your business.
Create a network that is smarter, simpler and more secure with Cisco Catalyst SD-WAN
Get the most out of your network
Take advantage of simplified and secure connectivity so you can focus on driving business success, not on managing your network.