ISR4000でのセキュアSIP SRSTの設定
ダウンロード オプション
偏向のない言語
この製品のドキュメントセットは、偏向のない言語を使用するように配慮されています。このドキュメントセットでの偏向のない言語とは、年齢、障害、性別、人種的アイデンティティ、民族的アイデンティティ、性的指向、社会経済的地位、およびインターセクショナリティに基づく差別を意味しない言語として定義されています。製品ソフトウェアのユーザインターフェイスにハードコードされている言語、RFP のドキュメントに基づいて使用されている言語、または参照されているサードパーティ製品で使用されている言語によりドキュメントに例外が存在する場合があります。シスコのインクルーシブ ランゲージの取り組みの詳細は、こちらをご覧ください。
翻訳について
シスコは世界中のユーザにそれぞれの言語でサポート コンテンツを提供するために、機械と人による翻訳を組み合わせて、本ドキュメントを翻訳しています。ただし、最高度の機械翻訳であっても、専門家による翻訳のような正確性は確保されません。シスコは、これら翻訳の正確性について法的責任を負いません。原典である英語版(リンクからアクセス可能)もあわせて参照することを推奨します。
内容
概要
このドキュメントでは、ISR4000シリーズルータおよびCisco Unified Communications Manager(CUCM)でSecure Session Initiation Protocol(SIP)Survivable Remote Site Telephony(SRST)を設定する方法について説明します。
著者:Cisco TACエンジニア、Ankush Vijay
前提条件
要件
次の項目に関する知識があることが推奨されます。
Cisco Unified Communications Manager(CUCM)
Cisco Unified Survivable Remote Site Telephony(SRST)
Transport Layer Security(TLS)
Secure Real-Time Transport Protocol(SRTP)
Real-Time Transport Protocol(RTP; リアルタイム転送プロトコル)
Session Initiation Protocol(SIP)
User Datagram Protocol(UDP; ユーザ データグラム プロトコル)
使用するコンポーネント
CUCM:10.5.2
SIP SRSTバージョン – SRST管理ガイドに従って12.1以上を実行
SRSTルータ:ISR 4451
CA サーバ:ISR 2921およびサードパーティCAサーバでテスト済み。
テストされた電話機:78XXおよび88XX
プラットフォームの容量とファームウェアの要件(SRST互換性マトリクスに従い)。
IOS CAサーバとして使用されるISRG2(同じSRSTゲートウェイをIOS CAサーバとしても使用できます)
注意:このドキュメントの情報は、特定のラボ環境にあるデバイスに基づいて作成されました。このドキュメントで使用するすべてのデバイスは、初期(デフォルト)設定の状態から起動しています。本稼働中のネットワークでは、各コマンドによって起こる可能性がある影響を十分確認してください。
Secure SRSTの概要
Cisco Unified Secure SRSTは、認証、整合性、メディア暗号化などのセキュリティ機能を提供します。
認証では、通話者に対して、通話相手が当人であることを保証します。
整合性により、エンティティ間で特定のデータが変更されていないことを保証します。
暗号化は機密性を意味します。つまり、目的の受信者以外はデータを読み取れないということです。これらのセキュリティ機能により、Cisco Unified SRST音声コールのプライバシーが保護され、音声セキュリティ違反やID盗難から保護されます。
SRST のセキュリティが実現されるための条件を次に示します。
- エンドデバイスは、証明書を使用して認証されます。
- シグナリングは、TCPのTransport Layer Security(TLS)を通じて認証および暗号化されます。
- セキュアなメディアパスは、Secure Real-Time Transport Protocol(SRTP)によって暗号化されます。
- 証明書は、認証局(CA)によって生成および配布されます
背景説明
この設定を行う前に、CUCMをセキュリティイネーブルの混合モードに調整する必要があります。
電話機はセキュアな電話機として登録する必要があります。
セキュアモードで電話機をCUCMに登録する方法については、[IP Phone Security]および[CTL]をオンにしてください
Cisco 4000シリーズサービス統合型ルータでSecure SIP SRSTをサポートするには、ルータで次のテクノロジーパッケージライセンスを有効にします。
セキュリティ uck9
設定手順と例
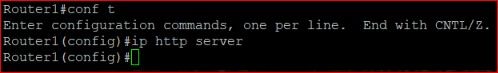
ステップ1:SRSTおよびCAサーバでHttpを有効にする
ip http server
ステップ2:IOSベースのCAサーバまたはサードパーティのCAサーバからの証明書のインストール
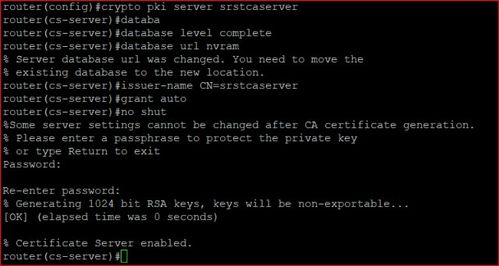
A) IOSベースのCAサーバ。
- Cisco IOS証明書サーバの作成:
1. crypto pki serverCA-Name
2. database level{minimal| names | complete}
minimal: Enough information is stored only to continue to issue new certificates without conflict; this is the default.
names: In addition to the information given in the minimal level, the serial number and subject name of each certificate are stored.
complete: In addition to the information given in the minimal and names levels, each issued certificate is written to the database.
3. database urlroot-url
The default location for the database entries to be written is flash; however, NVRAM is recommended for this task.
4. issuer-nameDN-string
Eg: issuer-name CN= CA-Name
5. grant auto
6. no shutdown
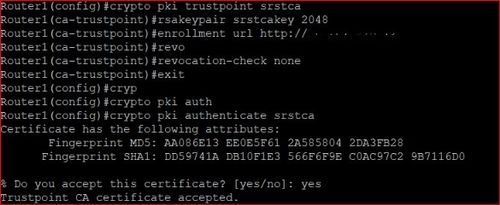
- CAサーバへのSRSTルータの自動登録と認証:
1. crypto pki trustpoint SRST-Trustpoint-Name
2. enrollment url url
If the CA is on your router itself url would be http://router-ip-address
3. revocation-check none
4. rsakeypair keypair-label
5. exit
6. crypto pki authenticate SRST-Trustpoint-Name
Certificate has the following attributes:
Fingerprint MD5: 4C894B7D 71DBA53F 50C65FD7 75DDBFCA
Fingerprint SHA1: 5C3B6B9E EFA40927 9DF6A826 58DA618A BF39F291
% Do you accept this certificate? [yes/no]: y
Trustpoint CA certificate accepted.
- crypto pki enroll SRST-Trustpoint-Name
% Start certificate enrollment ..
% Create a challenge password. You will need to verbally provide this
password to the CA Administrator in order to revoke your certificate.
For security reasons your password will not be saved in the configuration.
Please make a note of it.
Password:
Re-enter password:
% The fully-qualified domain name in the certificate will be: router.cisco.com
% The subject name in the certificate will be: router.cisco.com
% Include the router serial number in the subject name? [yes/no]: y
% The serial number in the certificate will be: D0B9E79C
% Include an IP address in the subject name? [no]: n
Request certificate from CA? [yes/no]: y
% Certificate request sent to Certificate Authority
% The certificate request fingerprint will be displayed.
% The 'show crypto pki certificate' command will also show the fingerprint.
Sep XX 00:41:55.427: CRYPTO_PKI: Certificate Request Fingerprint MD5: D154FB75
2524A24D 3D1F5C2B 46A7B9E4
Sep XX 00:41:55.427: CRYPTO_PKI: Certificate Request Fingerprint SHA1: 0573FBB2
98CD1AD0 F37D591A C595252D A17523C1
Sep XX 00:41:57.339: %PKI-6-CERTRET: Certificate received from Certificate Authority

B)サードパーティCAサーバ
手順の概要:
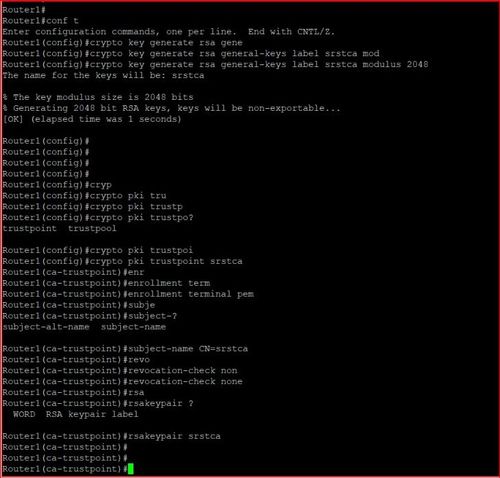
1. crypto key generate rsa general-keys label SRST-Trustpoint-Name modulus 2048
2. Router(config)#crypto pki trustpoint srstca
Router(ca-trustpoint)#enrollment terminal pem
Router(ca-trustpoint)#subject-name CN=srstca
Router(ca-trustpoint)#revocation-check none
Router(ca-trustpoint)#rsakeypair cube
3. Crypto pki enroll srstca
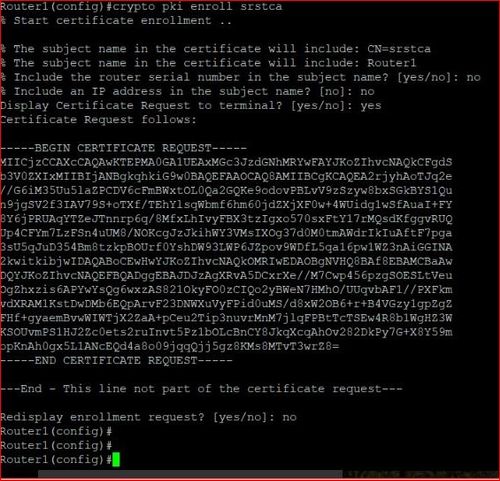
サードパーティCAに証明書を提供します。
4. CA provides the Signed Certificate as well as the Root CA Certificate and any Intermediate (subordinate) CA certificates if any.
5. Install Root CA cert;
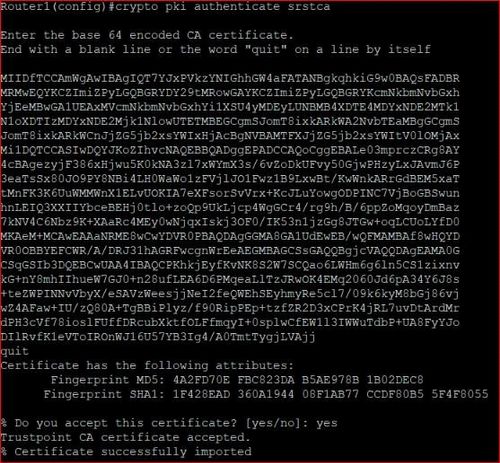
crypto pki authenticate srstca
6. Install Signed cert from CA;
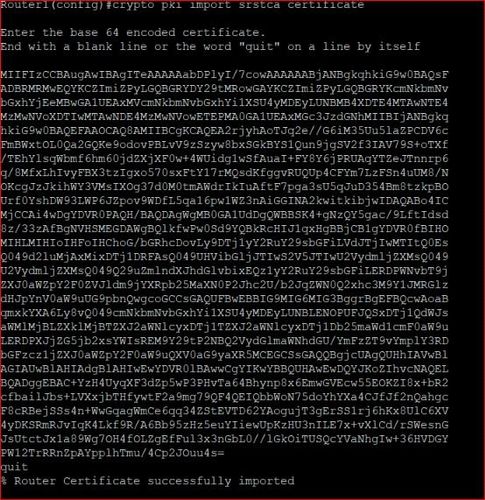
crypto pki import srstca certificate
ステップ3:SRSTルータでクレデンシャルサービスを有効にします。
手順の概要:
1. credentials
2. ip source-address srst-router-ip port 2445
3. trustpoint SRST-trustpoint-name

ステップ4:プライバシー強化メール(PEM)形式の電話証明書ファイルをSecure SRSTルータにインポートします。
CUCMで、[Cisco unified OS administration] > [Security] > [Certificate management]に移動します
Cisco_Manufacturing_CA、Cisco_Root_CA_2048、CAP-RTP-001、CAP-RTP-002、CAPF、およびCAPF-xxxを含む、CAPF-trustにリストされているすべての証明書をダウンロードします。また、CallManager-trustにリストされ、CAPF-trustにリストされていないCAPF-xxx証明書もダウンロードします。

SRSTルータ上の各トラストポイントを設定します。トラストポイント名を.pemと同じにしてください。
手順の概要:
1. crypto pki trustpointname
2. revocation-check none
3. enrollment terminal
4. exit
5. crypto pki authenticate name
ここで、対応する.pemファイルのBEGIN CERTIFICATE - -および – END CERTIFICATEの間に表示されるすべての内容を、末尾に空白行を入れてコピーします。quitという単語を入力し、enterキーを押します。
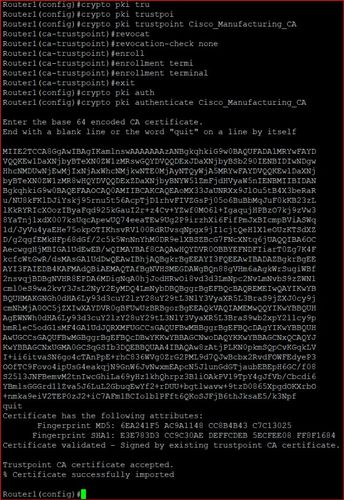
すべてのトラストポイントに対してこの手順を繰り返します
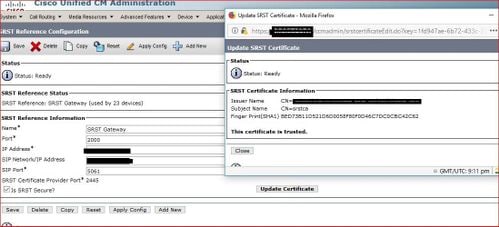
ステップ5:CUCMの設定:
- システムの下にSRST参照を追加します
- [Is SRST Secure]のチェックボックスをオンにします。
- SIP Secure-SRSTの場合は、SRST参照先のポートを5061に変更することを忘れないでください。
- [System] > [Security] > [Phone security profile]で、電話機のセキュリティプロファイルを作成します。このセキュリティプロファイルを[デバイスセキュリティプロファイル]の下の電話機に追加します。
- [Update Certificate]を選択して、srst証明書がCUCMに入力されたことを確認します。
ステップ6:SRSTルータのSRST固有の設定
A) 暗号化された電話機のSIP SRTPの設定
手順の概要:
enable
configure terminal
voice service voip
srtp
allow-connections sip to h323
allow-connections sip to sip
end
注:srtp以外のコールを動作させるには、srtp fallbackを使用します。
B) SIP SRSTセキュリティポリシーの設定
手順の概要:
voice register global
security-policy secure
設定例
Router1#sh run
Building configuration...
Current configuration : 43277 bytes
!
!
!
version 16.8
service timestamps debug datetime msec localtime
service timestamps log datetime msec localtime
service sequence-numbers
platform qfp utilization monitor load 80
no platform punt-keepalive disable-kernel-core
!
hostname Router1
!
boot-start-marker
boot system bootflash:isr4400-universalk9.16.08.01.SPA.bin
boot-end-marker
!
!
vrf definition Mgmt-intf
!
address-family ipv4
exit-address-family
!
address-family ipv6
exit-address-family
!
! card type command needed for slot/bay 0/2
no logging queue-limit
logging buffered 10000000
no logging rate-limit
no logging console
enable password cisco
!
no aaa new-model
!
no ip domain lookup
!
!
!
!
!
!
!
!
!
!
subscriber templating
!
!
!
!
!
!
!
multilink bundle-name authenticated
!
!
!
!
!
!
crypto pki trustpoint TP-self-signed-2252801652
enrollment selfsigned
subject-name cn=IOS-Self-Signed-Certificate-2252801652
revocation-check none
rsakeypair TP-self-signed-2252801652
!
crypto pki trustpoint srstca
enrollment url http://X.X.X.X:80
serial-number
revocation-check none
rsakeypair srstcakey 2048
!
crypto pki trustpoint CAPF
enrollment terminal
revocation-check none
!
crypto pki trustpoint ACT2_SUDI_CA
enrollment terminal
revocation-check none
!
crypto pki trustpoint CAPF-2fbd03a4
enrollment terminal
revocation-check none
!
crypto pki trustpoint CAPF-72c7ffbb
enrollment terminal
revocation-check none
!
crypto pki trustpoint CAPF-851d4452
enrollment terminal
revocation-check none
!
crypto pki trustpoint CAP-RTP-001
enrollment terminal
revocation-check none
!
crypto pki trustpoint CAP-RTP-002
enrollment terminal
revocation-check none
!
crypto pki trustpoint Cisco_Manufacturing_CA
enrollment terminal
revocation-check none
!
crypto pki trustpoint Cisco_Manufacturing_CA_SHA2
enrollment terminal
revocation-check none
!
crypto pki trustpoint Cisco_Root_CA_2048
enrollment terminal
revocation-check none
!
crypto pki trustpoint Cisco_Root_CA_M2
enrollment terminal
revocation-check none
!
crypto pki trustpoint CAPF-19a340e5
enrollment terminal
revocation-check none
!
crypto pki trustpoint CAPF-dc3cda68
enrollment terminal
revocation-check none
!
!
crypto pki certificate chain TP-self-signed-2252801652
certificate self-signed 01
30820330 30820218 A0030201 02020101 300D0609 2A864886 F70D0101 05050030
31312F30 2D060355 04031326 494F532D 53656C66 2D536967 6E65642D 43657274
69666963 6174652D 32323532 38303136 3532301E 170D3138 30353232 31393534
35315A17 0D323030 31303130 30303030 305A3031 312F302D 06035504 03132649
4F532D53 656C662D 5369676E 65642D43 65727469 66696361 74652D32 32353238
30313635 32308201 22300D06 092A8648 86F70D01 01010500 0382010F 00308201
0A028201 01009A19 F3B5F20E E7451414 CB037164 CDE972C0 C3CBA15B 9A1B47AC
36BF9279 B910BBDD 4EB7AA4B 59D2D498 1D9864E7 83FDBA4B 256F99C6 FD4F8BF8
041692BB 6996565C 2B956192 ACAB67B2 50E6A345 0F587D3C D743DA12 FB4720BB
74F45FF9 5030CDAD 6182981C FE9AB5C7 C87FE94F 08FA1D46 37D3AC40 D6AB5311
ED0CE720 AA2CE8FC 38A1B392 86B2D5C9 01E3D052 51CC8925 CBFE790D D5DBC179
FDCA96C7 004483B6 D4A064C6 06D1F593 45610881 94E8AECC 27E71EAF 412E9DE1
DBA67CA5 4C5B8E2F D547A86B 374A04B8 F4A04AE7 9D38D398 B43801AE 779DD7A3
B26FD7AE 542D15BC 71A1E602 E2710F70 587D7380 508FC890 1CD3CF7D A541DCB5
025F645D CF9B0203 010001A3 53305130 0F060355 1D130101 FF040530 030101FF
301F0603 551D2304 18301680 14C3E99A 3F385791 A48AB9CE A8A499B9 D07449D4
58301D06 03551D0E 04160414 C3E99A3F 385791A4 8AB9CEA8 A499B9D0 7449D458
300D0609 2A864886 F70D0101 05050003 82010100 39D88E81 B3762195 4E312E27
1B5F1B0F 41D1F3C1 2BD6D35D 70B8FFCA 9B94DD5F 4176549B 3B91CD8B 63B67B9B
2A0DAE22 F1FF44A4 12FB9E45 2E6A7040 5745F00E E585F4B9 F3358ABA BBA28EF6
2DBE3930 250BC148 37A667EB C8B02B57 8A69AB6C 6F63E7D5 3FE0B6E7 7E0C5187
87948F48 CD2B0275 D7E1538A EB91D857 083D47C1 41D78DB9 2B23E37D A08684C9
4FC9FD8D 16809B90 331A2E28 B11F090B 867D4453 5B00F635 32477591 5D68044F
44AC8679 997F6CA5 A4243FA2 C920A7B9 763881F5 EDA90EC1 F92611A4 E9D00B40
A034343D 8C516C12 01A36C4D 305F85F2 FE76DD08 8B2958FD 44810372 694D80E8
CB836B61 46B7E336 F2993913 BA6A9878 F47D35B7
quit
crypto pki certificate chain srstca
certificate 02
30820291 308201FA A0030201 02020102 300D0609 2A864886 F70D0101 05050030
17311530 13060355 0403130C 73727374 63617365 72766572 301E170D 31383130
30333137 35313332 5A170D31 39313030 33313735 3133325A 3031312F 30120603
55040513 0B464A43 32313337 44313232 30190609 2A864886 F70D0109 02160C41
4E41532D 54455354 5F465830 82012230 0D06092A 864886F7 0D010101 05000382
010F0030 82010A02 82010100 A38F8654 32A14C89 94139845 9BFE0C10 E229EBB4
F4F2466B 1AA81A3C A0C9F48F D421C5D7 A3B7CCC3 61C80E70 82850A29 B862FED8
DE82E342 4E5FAE59 F2EF6DE5 61DCC85A BB9F38C0 0C20C94D 601A7F9B 1FC9DEA0
06690351 44BC61D2 C21AAEC8 92084F45 E3A0E91B D1961D49 F4604B29 78C93417
EF8D8F6C DE842A22 935F99E7 940F8160 37DDB460 6CDAFC36 7A8C9BD6 B05B0D67
D5919817 FEBFA31D 4F681558 2B241BA2 B865E06A AAF68493 B67F86A4 681865BD
6E5794FD BA70435C 910FBFF3 F0A15C26 BBF96D72 05A567F9 B6406E1D A60F559D
A08B7F79 4D0C3201 9E7AA715 E711D4ED 174B6352 340BA097 289E577B E21FC6F6
13A1F17D F2461076 6C68A461 02030100 01A34F30 4D300B06 03551D0F 04040302
05A0301F 0603551D 23041830 1680142B F374EDE2 C716627B CEE1A0F2 BEE9D139
2E4C7B30 1D060355 1D0E0416 04144E01 3013A936 E68046F8 62A3A552 89635BAB
9127300D 06092A86 4886F70D 01010505 00038181 0059B995 2E24119E 731DE753
0D13A8A2 63937E96 834BC76D F6160309 9D6AF8EA FBA0134A 1655731C 8387A0FA
3092B7CA 66947B1C 1B12EF42 E19AB43D 2570664C 82D58CE9 6747F0A5 D1FC1ED7
B25454B2 B1570F1A 783D1FAB E76C2938 136C9475 3F1A63E8 4D931DD0 97B5D0FA
CFC879FD B9CC3A3A 49037341 D61EC7D6 F3781DE8 F5
quit
certificate ca 01
30820207 30820170 A0030201 02020101 300D0609 2A864886 F70D0101 04050030
17311530 13060355 0403130C 73727374 63617365 72766572 301E170D 31383130
30333136 31363338 5A170D32 31313030 32313631 3633385A 30173115 30130603
55040313 0C737273 74636173 65727665 7230819F 300D0609 2A864886 F70D0101
01050003 818D0030 81890281 8100BB90 D2ABF45E 235EC458 80CAF0AC 5E7E9D16
A2BE8B5E DC3C8F78 C6CD325F 5A7DAED0 06FAB17A 1E9A8C50 D661E3EE 8B9DC29E
5DCD1B36 2AC4B89B E844F2F9 B98D54B8 CE539098 BBAC4913 E6822196 00C6964E
16B793DD B7E7A5E7 CFC66CD1 3E01965D FBC29260 052AFBF2 930832E6 DF976644
EC89CDAC 9B48A8C0 47CD30B6 219B0203 010001A3 63306130 0F060355 1D130101
FF040530 030101FF 300E0603 551D0F01 01FF0404 03020186 301F0603 551D2304
18301680 142BF374 EDE2C716 627BCEE1 A0F2BEE9 D1392E4C 7B301D06 03551D0E
04160414 2BF374ED E2C71662 7BCEE1A0 F2BEE9D1 392E4C7B 300D0609 2A864886
F70D0101 04050003 81810021 90395C26 1C020400 22F51B91 84715407 DB17A0C6
63E1D9FD 45F6B4C5 9F20823C 77C6A8E5 36488C3D F6D91F00 87567D03 D6C35A79
665DB0BC 3C96A357 C402ABE8 47472636 28EC20F5 787D79F5 C913B62D 4B4E236F
9FF26BB8 B1BC4A11 82AE890A 83258084 2F288359 5F52E5DB 80F7A7DC A923BE70
83C9B689 6DB4A7F5 59DA9F
quit
crypto pki certificate chain CAPF
certificate ca 6DBF757CC9B4B5D97357362ACF2F6A5B
308203A1 30820289 A0030201 0202106D BF757CC9 B4B5D973 57362ACF 2F6A5B30
0D06092A 864886F7 0D01010B 05003065 310B3009 06035504 06130255 53310E30
0C060355 040A0C05 63697363 6F310C30 0A060355 040B0C03 74616331 16301406
03550403 0C0D4341 50462D37 32633766 66626231 0B300906 03550408 0C027478
31133011 06035504 070C0A72 69636861 7264736F 6E301E17 0D313830 33323032
30303730 385A170D 32333033 31393230 30373037 5A306531 0B300906 03550406
13025553 310E300C 06035504 0A0C0563 6973636F 310C300A 06035504 0B0C0374
61633116 30140603 5504030C 0D434150 462D3732 63376666 6262310B 30090603
5504080C 02747831 13301106 03550407 0C0A7269 63686172 64736F6E 30820122
300D0609 2A864886 F70D0101 01050003 82010F00 3082010A 02820101 00B65FDA
4AA4FBAF 24374D68 110FF40D FDD90234 C0242C1C 6928A6AB 06E98725 62B6F006
A1CE0D00 8C70B706 9961FF19 06FB66F0 66DF762F C739884C 3A29B36C E0F7BF1C
9178182D 19C9AA3C 7B26840F 0B14E615 8B65E27B C1777D57 0DA158C8 0E203B16
A00B5124 2C3A09FE 3871921B E7D3A7BD 8316B6C1 C18F09F2 2F5A62D1 A04E7709
E1C9C0AC 8DE1F853 D63A64DD 7980EE9D 085DBEBB BE788B30 E644E364 868A0F11
2764218A 3B86A603 AE58575B C5D53E47 69819971 2A6C3038 0390138D 904C5632
2167CA22 A3F35409 2A2047BB F09A220F 13796E6D 044C19FB 3C15B2CE F90FFCD5
8ED067DB 6E7F28F6 BE0DE28F 97B99AE8 726E3E75 093B9208 414033B7 DF020301
0001A34D 304B300B 0603551D 0F040403 0202A430 1D060355 1D250416 30140608
2B060105 05070301 06082B06 01050507 0305301D 0603551D 0E041604 145E5F34
7B18A5FE 71A2A609 0DFB5A15 3A8B9A38 A2300D06 092A8648 86F70D01 010B0500
03820101 003364ED 00769497 12D3A98D FB362FAE 4241391D FF8B40D9 C9D28565
B633A082 46EAF721 1E7C96E6 BD82CFB6 64D0908A C0B09941 66C905E1 2FEE394F
560E89A0 E159983A A492D1E3 741A42CC 9B2D75E4 B1145EF1 C0956B76 380A1BE3
B9C1A6BF F1AD89C4 F3A0FDD0 455EAB60 4C85814F 821D4DEA D43AC5DD E43702FA
50F6B7F3 82FF80AC 647731E5 A79372EE 1666EEF6 A18BF2BE B2FDC8BE C9CAA4EE
A658E864 3C66ECFA BA3213D3 576F124F B14B56E3 802B0B9C 9026FB69 00373361
66002D9F EAD2C465 2E473265 2550098E 3FD28A04 3850BDA4 32EBC7FA 03A75A8F
80C2AFEB F108500B 97F5D6E9 06854D5C A6E656F6 0BAD484F B49C0857 8EC4D05E
73379F52 83
quit
crypto pki certificate chain ACT2_SUDI_CA
certificate ca 61096E7D00000000000C
3082043C 30820324 A0030201 02020A61 096E7D00 00000000 0C300D06 092A8648
86F70D01 01050500 30353116 30140603 55040A13 0D436973 636F2053 79737465
6D73311B 30190603 55040313 12436973 636F2052 6F6F7420 43412032 30343830
1E170D31 31303633 30313735 3635375A 170D3239 30353134 32303235 34325A30
27310E30 0C060355 040A1305 43697363 6F311530 13060355 0403130C 41435432
20535544 49204341 30820122 300D0609 2A864886 F70D0101 01050003 82010F00
3082010A 02820101 00D26E65 DD31C8C4 0F6D37F8 52E6A47F E94651A5 D77EF5A1
3625B164 36386DEA 07C729DE 3BEC0912 E5702D52 CE68C436 15B7FCC4 6EC959AB
7F8B47AA ABA8A290 56EE8962 F1F4E546 0B06A0A3 DFCB3BE8 D2E4E77F 74E56CE9
F6945C99 108FB97F 9AEAD1C5 FEA46E3A 2278E267 5E0D8668 DEA3C2A7 1CE9AD62
433DC94C E2260A1E E98C40CA A682683E C6084722 8A164BCD 0139C762 CA711B78
FE6B67BA 91B9EC0A 3299754E 223759D0 4D8D98E7 A5F8E0EB A17E3F84 9A0E419B
0577468F 5DE855E1 7E132156 2EB1638F DEDF2F6F BCA1AB95 E3742BBE 77F777F1
9FA978FB 7B0FB3FE C5E55ED1 0E8D25C9 511B3230 48F9DD17 5DF6D270 1E4CBC9D
E6A9B334 BEAFE91D 55020301 0001A382 015A3082 0156300B 0603551D 0F040403
0201C630 1D060355 1D0E0416 041448D8 F1F1C270 D55BBB7C 730993AF B8B83003
F87F301F 0603551D 23041830 16801427 F3C8151E 6E9A0209 16AD2BA0 89605FDA
7B2FAA30 43060355 1D1F043C 303A3038 A036A034 86326874 74703A2F 2F777777
2E636973 636F2E63 6F6D2F73 65637572 6974792F 706B692F 63726C2F 63726361
32303438 2E63726C 30500608 2B060105 05070101 04443042 30400608 2B060105
05073002 86346874 74703A2F 2F777777 2E636973 636F2E63 6F6D2F73 65637572
6974792F 706B692F 63657274 732F6372 63613230 34382E63 6572305C 0603551D
20045530 53305106 0A2B0601 04010915 010C0030 43304106 082B0601 05050702
01163568 7474703A 2F2F7777 772E6369 73636F2E 636F6D2F 73656375 72697479
2F706B69 2F706F6C 69636965 732F696E 6465782E 68746D6C 30120603 551D1301
01FF0408 30060101 FF020100 300D0609 2A864886 F70D0101 05050003 82010100
6875A9C9 6BF6DC78 8735A00C 4466DFBD 727AE126 A9C21F8B D6FDF866 CC4896E2
64773F09 C0A5D252 6ED1AF73 4D703DC3 8EC7F7FB 7A95E76E 1B16F859 E2F17300
A2520BC5 B426B9D4 8925B7C9 CD6DC298 FF8770D5 EC7EEDA9 804D440E E1082020
4EBBC152 0FBBA6E0 004DC96B F9D14B7C 4A6129E3 F07E537A 18A6052B FA4C40A2
8B98D484 E5ABC802 B8755A3C 8428E48C 4933BB7B 9F05325A A67BFCF6 0F4E13E1
F754A338 2FEFCA76 450EFB9D 9D8C52A7 872978ED DEDC651E 036382C8 B853363F
502CF18C A3CE8369 2BFBAB49 1235E167 48969951 D671FB28 D0E5E7AD 7CC9F54F
D0814964 11ABA280 91063392 C05BFC72 95826E65 9D3DA090 4F69F022 34DF63C7
quit
crypto pki certificate chain CAPF-2fbd03a4
certificate ca 7FA76BD99C1DDA013BE037763BC78C33
3082029C 30820205 A0030201 0202107F A76BD99C 1DDA013B E037763B C78C3330
0D06092A 864886F7 0D010105 05003065 310B3009 06035504 06130255 53310E30
0C060355 040A1305 63697363 6F310C30 0A060355 040B1303 74616331 16301406
03550403 130D4341 50462D32 66626430 33613431 0B300906 03550408 13027478
31133011 06035504 07130A72 69636861 7264736F 6E301E17 0D313430 38313831
39333633 395A170D 31393038 31373139 33363338 5A306531 0B300906 03550406
13025553 310E300C 06035504 0A130563 6973636F 310C300A 06035504 0B130374
61633116 30140603 55040313 0D434150 462D3266 62643033 6134310B 30090603
55040813 02747831 13301106 03550407 130A7269 63686172 64736F6E 30819F30
0D06092A 864886F7 0D010101 05000381 8D003081 89028181 00A175B5 F8D9CED4
A7972459 B51B335C E1DCCF3B 6E2D9504 78A95267 C5BFEC43 5FD0B430 AD87632F
8643B1AF 542F3028 526EA7AC F7721A3B 79BBF5BE E650883B B7AD60F1 62C7EA02
A1DBAA49 738FE258 B47F9D28 1D6CF1E5 7974151B 9D4F8CFB 68EA7D17 68E47D75
61787FB3 3A64CC9D 26FAB9D0 684A4F15 EA917F79 7696E0C5 7B020301 0001A34D
304B300B 0603551D 0F040403 0202A430 1D060355 1D250416 30140608 2B060105
05070301 06082B06 01050507 0305301D 0603551D 0E041604 1470BF75 2404D5FB
8F0197BE 8AAD174A AB785D53 FB300D06 092A8648 86F70D01 01050500 03818100
4C39EC6E 28E512E1 B034E827 F9034E5B B01A33CF DB321FFD 30374692 8521592E
CD7583BE 5BAB0CD7 A03E12B0 0B4E8120 A028E08C CEBEB871 67DF12B6 20000DD2
CE77ED30 188F728A B60D877D 513B9BB1 FCF79545 9FC38909 D8808EEE BB013106
5560DAAB 3AE7ADA5 E437063E 8A50F3A7 FC5584D5 66A6B9D7 261E9331 53A66AB9
quit
crypto pki certificate chain CAPF-72c7ffbb
certificate ca 6DBF757CC9B4B5D97357362ACF2F6A5B
308203A1 30820289 A0030201 0202106D BF757CC9 B4B5D973 57362ACF 2F6A5B30
0D06092A 864886F7 0D01010B 05003065 310B3009 06035504 06130255 53310E30
0C060355 040A0C05 63697363 6F310C30 0A060355 040B0C03 74616331 16301406
03550403 0C0D4341 50462D37 32633766 66626231 0B300906 03550408 0C027478
31133011 06035504 070C0A72 69636861 7264736F 6E301E17 0D313830 33323032
30303730 385A170D 32333033 31393230 30373037 5A306531 0B300906 03550406
13025553 310E300C 06035504 0A0C0563 6973636F 310C300A 06035504 0B0C0374
61633116 30140603 5504030C 0D434150 462D3732 63376666 6262310B 30090603
5504080C 02747831 13301106 03550407 0C0A7269 63686172 64736F6E 30820122
300D0609 2A864886 F70D0101 01050003 82010F00 3082010A 02820101 00B65FDA
4AA4FBAF 24374D68 110FF40D FDD90234 C0242C1C 6928A6AB 06E98725 62B6F006
A1CE0D00 8C70B706 9961FF19 06FB66F0 66DF762F C739884C 3A29B36C E0F7BF1C
9178182D 19C9AA3C 7B26840F 0B14E615 8B65E27B C1777D57 0DA158C8 0E203B16
A00B5124 2C3A09FE 3871921B E7D3A7BD 8316B6C1 C18F09F2 2F5A62D1 A04E7709
E1C9C0AC 8DE1F853 D63A64DD 7980EE9D 085DBEBB BE788B30 E644E364 868A0F11
2764218A 3B86A603 AE58575B C5D53E47 69819971 2A6C3038 0390138D 904C5632
2167CA22 A3F35409 2A2047BB F09A220F 13796E6D 044C19FB 3C15B2CE F90FFCD5
8ED067DB 6E7F28F6 BE0DE28F 97B99AE8 726E3E75 093B9208 414033B7 DF020301
0001A34D 304B300B 0603551D 0F040403 0202A430 1D060355 1D250416 30140608
2B060105 05070301 06082B06 01050507 0305301D 0603551D 0E041604 145E5F34
7B18A5FE 71A2A609 0DFB5A15 3A8B9A38 A2300D06 092A8648 86F70D01 010B0500
03820101 003364ED 00769497 12D3A98D FB362FAE 4241391D FF8B40D9 C9D28565
B633A082 46EAF721 1E7C96E6 BD82CFB6 64D0908A C0B09941 66C905E1 2FEE394F
560E89A0 E159983A A492D1E3 741A42CC 9B2D75E4 B1145EF1 C0956B76 380A1BE3
B9C1A6BF F1AD89C4 F3A0FDD0 455EAB60 4C85814F 821D4DEA D43AC5DD E43702FA
50F6B7F3 82FF80AC 647731E5 A79372EE 1666EEF6 A18BF2BE B2FDC8BE C9CAA4EE
A658E864 3C66ECFA BA3213D3 576F124F B14B56E3 802B0B9C 9026FB69 00373361
66002D9F EAD2C465 2E473265 2550098E 3FD28A04 3850BDA4 32EBC7FA 03A75A8F
80C2AFEB F108500B 97F5D6E9 06854D5C A6E656F6 0BAD484F B49C0857 8EC4D05E
73379F52 83
quit
crypto pki certificate chain CAPF-851d4452
certificate ca 497E1692253769919F72D12F6754F2CF
308203A1 30820289 A0030201 02021049 7E169225 3769919F 72D12F67 54F2CF30
0D06092A 864886F7 0D010105 05003065 310B3009 06035504 06130255 53310E30
0C060355 040A0C05 63697363 6F310C30 0A060355 040B0C03 74616331 16301406
03550403 0C0D4341 50462D38 35316434 34353231 0B300906 03550408 0C027478
31133011 06035504 070C0A72 69636861 7264736F 6E301E17 0D313630 35323631
37313234 345A170D 32313035 32353137 31323433 5A306531 0B300906 03550406
13025553 310E300C 06035504 0A0C0563 6973636F 310C300A 06035504 0B0C0374
61633116 30140603 5504030C 0D434150 462D3835 31643434 3532310B 30090603
5504080C 02747831 13301106 03550407 0C0A7269 63686172 64736F6E 30820122
300D0609 2A864886 F70D0101 01050003 82010F00 3082010A 02820101 00A59E68
74D20933 FAC49493 2B2F1955 46C04608 B9D0037F 4608875C 29BC674C 2A28A147
1213EFC5 7FFDC43E F6CD6863 AF135F2C D379B790 D2508D3C 131FA04A F6ABC3CE
D2B1AF30 EEB6D323 3BF82553 47C83415 FCEA183B 3D6405F3 019B5CF9 D337FFE2
D53D14F5 5E5E3CAE 6398617A F3AACD79 0FDF2503 62E71F7E 8EFBE8C3 822CBBDE
748805B0 79C36694 C3430D8E ABF7541D B258FD44 E1191E56 13B08CCA FCDE02BB
F4E14129 3EDB3D19 98DA5464 9E0DCC92 F84E95D3 EB318D8F AEAFB6CB 941843F2
19864A3F 2781B7DF 5818F0FD 7A073630 D8DCB9AE 345408B5 BA58F03D C5986FFF
7F60E295 82A8567B F11A5950 D2F0DD35 83A9AF2F 66B0AE27 93BFFEE5 89020301
0001A34D 304B300B 0603551D 0F040403 0202A430 1D060355 1D250416 30140608
2B060105 05070301 06082B06 01050507 0305301D 0603551D 0E041604 14698E82
A731BD61 85FC77BD 9B02E372 73A49A04 CA300D06 092A8648 86F70D01 01050500
03820101 0059B0E2 30452666 B3362F87 B746A682 BF1CB181 A7F472F0 478EEAB1
45A547C8 8C37C53F 2D2E594E 9D539081 ED931849 80368136 B2CB39D6 D93DDA36
B4E0FFF3 1EF6DC28 6386BE6E FC85E859 292993E8 28C8635E E793AF76 493934F1
654FADF2 16B11AA0 9E73F81B 9DE787A3 A683343E 60D4FF2E 5F478199 EFC8DC6F
8650BCA9 5EBF6FF5 09060341 0ED13620 A08C53C7 9012E2F6 7DC439DA 3C4C0DE7
AF1B7FD9 C5E019ED 6EE6D573 5FA1569B C82E54B6 7748A171 AF6A7F44 46A9E3C0
B2B74889 39D8CA52 0A46B2FE 196AD4F4 3E0E327C 98DF3850 43FD421A D7CB64F8
F789913E 7CF07503 4D522DC2 4952C16D 7A9751AA 7900DB9F D55F0E1D 5EAE3160
FE203183 86
quit
crypto pki certificate chain CAP-RTP-001
certificate ca 7612F960153D6F9F4E42202032B72356
308203A8 30820290 A0030201 02021076 12F96015 3D6F9F4E 42202032 B7235630
0D06092A 864886F7 0D010105 0500302E 31163014 06035504 0A130D43 6973636F
20537973 74656D73 31143012 06035504 03130B43 41502D52 54502D30 3031301E
170D3033 30323036 32333237 31335A17 0D323330 32303632 33333633 345A302E
31163014 06035504 0A130D43 6973636F 20537973 74656D73 31143012 06035504
03130B43 41502D52 54502D30 30313082 0120300D 06092A86 4886F70D 01010105
00038201 0D003082 01080282 010100AC 55BBED18 DE9B8709 FFBC8F2D 509AB83A
21C1967F DEA7F4B0 969694B7 80CC196A 463DA516 54A28F47 5D903B5F 104A3D54
A981389B 2FC7AC49 956262B8 1C143038 5345BB2E 273FA7A6 46860573 CE5C998D
55DE78AA 5A5CFE14 037D695B AC816409 C6211F0B 3BBF09CF B0BBB2D4 AC362F67
0FD145F1 620852B3 1F07E2F1 AA74F150 367632ED A289E374 AF0C5B78 CE7DFB9F
C8EBBE54 6ECF4C77 99D6DC04 47476C0F 36E58A3B 6BCB24D7 6B6C84C2 7F61D326
BE7CB4A6 60CD6579 9E1E3A84 8153B750 5527E865 423BE2B5 CB575453 5AA96093
58B6A2E4 AA3EF081 C7068EC1 DD1EBDDA 53E6F0D6 E2E0486B 109F1316 78C696A3
CFBA84CC 7094034F C1EB9F81 931ACB02 0103A381 C33081C0 300B0603 551D0F04
04030201 86300F06 03551D13 0101FF04 05300301 01FF301D 0603551D 0E041604
14E917B1 82C71FCF ACA91B6E F4A9269C 70AE05A0 9A306F06 03551D1F 04683066
3064A062 A060862D 68747470 3A2F2F63 61702D72 74702D30 30312F43 65727445
6E726F6C 6C2F4341 502D5254 502D3030 312E6372 6C862F66 696C653A 2F2F5C5C
6361702D 7274702D 3030315C 43657274 456E726F 6C6C5C43 41502D52 54502D30
30312E63 726C3010 06092B06 01040182 37150104 03020100 300D0609 2A864886
F70D0101 05050003 82010100 AB64FDEB F60C32DC 360F0E10 5FE175FA 0D574AB5
02ACDCA3 C7BBED15 A4431F20 7E9286F0 770929A2 17E4CDF4 F2629244 2F3575AF
E90C468C AE67BA08 AAA71C12 BA0C0E79 E6780A5C F814466C 326A4B56 73938380
73A11AED F9B9DE74 1195C48F 99454B8C 30732980 CD6E7123 8B3A6D68 80B97E00
7F4BD4BA 0B5AB462 94D9167E 6D8D48F2 597CDE61 25CFADCC 5BD141FB 210275A2
0A4E3400 1428BA0F 69953BB5 50D21F78 43E3E563 98BCB2B1 A2D4864B 0616BACD
A61CD9AE C5558A52 B5EEAA6A 08F96528 B1804B87 D26E4AEE AB7AFFE9 2FD2A574
BAFE0028 96304A8B 13FB656D 8FC60094 D5A53D71 444B3CEF 79343385 3778C193
74A2A6CE DC56275C A20A303D
quit
crypto pki certificate chain CAP-RTP-002
certificate ca 353FB24BD70F14A346C1F3A9AC725675
308203A8 30820290 A0030201 02021035 3FB24BD7 0F14A346 C1F3A9AC 72567530
0D06092A 864886F7 0D010105 0500302E 31163014 06035504 0A130D43 6973636F
20537973 74656D73 31143012 06035504 03130B43 41502D52 54502D30 3032301E
170D3033 31303130 32303138 34395A17 0D323331 30313032 30323733 375A302E
31163014 06035504 0A130D43 6973636F 20537973 74656D73 31143012 06035504
03130B43 41502D52 54502D30 30323082 0120300D 06092A86 4886F70D 01010105
00038201 0D003082 01080282 010100C4 266504AD 7DC3FD8D 65556FA6 308FAE95
B570263B 575ABD96 1CC8F394 5965D9D0 D8CE02B9 F808CCD6 B7CD8C46 24801878
57DC4440 A7301DDF E40FB1EF 136212EC C4F3B50F BCAFBB4B CD2E5826 34521B65
01555FE4 D4206776 03368357 83932638 D6FC953F 3A179E44 67255A73 45C69DEE
FB4D221B 21D7A3AD 38184171 8FD8C271 42183E65 09461434 736C77CC F380EEBF
632C7B3F A5F92AA6 A8EF3490 8724A84F 4DAF7FD7 0928F585 764D3558 3C0FE9AF
1ED8763F A299A802 970004AD 1912D265 7DE335B4 BCB6F789 DC68B9FA C8FDF85E
8A28AD8F 0F4883C0 77112A47 141DBEE0 948FBE53 FE67B308 D40C8029 87BD790E
CDAB9FD7 A190C1A2 A462C5F2 4A6E0B02 0103A381 C33081C0 300B0603 551D0F04
04030201 86300F06 03551D13 0101FF04 05300301 01FF301D 0603551D 0E041604
1452922B E288EE2E 098A4E7E 702C56A5 9AB4D49B 96306F06 03551D1F 04683066
3064A062 A060862D 68747470 3A2F2F63 61702D72 74702D30 30322F43 65727445
6E726F6C 6C2F4341 502D5254 502D3030 322E6372 6C862F66 696C653A 2F2F5C5C
6361702D 7274702D 3030325C 43657274 456E726F 6C6C5C43 41502D52 54502D30
30322E63 726C3010 06092B06 01040182 37150104 03020100 300D0609 2A864886
F70D0101 05050003 82010100 56838CEF C4DA3AD1 EA8FBB15 2FFE6EE5 50A1972B
D4D7AF1F D298892C D5A2A76B C3462866 13E0E55D DC0C4B92 5AA94B6E 69277F9B
FC73C697 11266E19 451C0FAB A55E6A28 901A48C5 B9911EE6 348A8920 0AEDE1E0
B6EA781C FFD97CA4 B03C0E34 0E5B0649 8B0A34C9 B73A654E 09050C1F 4DA53E44
BF78443D B08C3A41 2EEEB873 78CB8089 34F9D16E 91512F0D 3A8674AD 0991ED1A
92841E76 36D7740E CB787F11 685B9E9D 0C67E85D AF6D05BA 3488E86D 7E2F7F65
6918DE0F BD3C7F67 D8A33F70 9C4A596E D9F62B3B 1EDEE854 D5882AD4 3D71F72B
8FAB7F3C 0B5F0759 D9828F83 954D7BB1 57A638EC 7D72BFF1 8933C16F 760BCA94
4C5B1931 67947A4F 89A1BDB5
quit
crypto pki certificate chain Cisco_Manufacturing_CA
certificate ca 6A6967B3000000000003
308204D9 308203C1 A0030201 02020A6A 6967B300 00000000 03300D06 092A8648
86F70D01 01050500 30353116 30140603 55040A13 0D436973 636F2053 79737465
6D73311B 30190603 55040313 12436973 636F2052 6F6F7420 43412032 30343830
1E170D30 35303631 30323231 3630315A 170D3239 30353134 32303235 34325A30
39311630 14060355 040A130D 43697363 6F205379 7374656D 73311F30 1D060355
04031316 43697363 6F204D61 6E756661 63747572 696E6720 43413082 0120300D
06092A86 4886F70D 01010105 00038201 0D003082 01080282 010100A0 C5F7DC96
943515F1 F4994EBB 9B41E17D DB791691 BBF354F2 414A9432 6262C923 F79AE7BB
9B79E807 294E30F5 AE1BC521 5646B0F8 F4E68E81 B816CCA8 9B85D242 81DB7CCB
94A91161 121C5CEA 33201C9A 16A77DDB 99066AE2 36AFECF8 0AFF9867 07F430EE
A5F8881A AAE8C73C 1CCEEE48 FDCD5C37 F186939E 3D71757D 34EE4B14 A9C0297B
0510EF87 9E693130 F548363F D8ABCE15 E2E8589F 3E627104 8726A415 620125AA
D5DFC9C9 5BB8C9A1 077BBE68 92939320 A86CBD15 75D3445D 454BECA8 DA60C7D8
C8D5C8ED 41E1F55F 578E5332 9349D5D9 0FF836AA 07C43241 C5A7AF1D 19FFF673
99395A73 67621334 0D1F5E95 70526417 06EC535C 5CDB6AEA 35004102 0103A382
01E73082 01E33012 0603551D 130101FF 04083006 0101FF02 0100301D 0603551D
0E041604 14D0C522 26AB4F46 60ECAE05 91C7DC5A D1B047F7 6C300B06 03551D0F
04040302 01863010 06092B06 01040182 37150104 03020100 30190609 2B060104
01823714 02040C1E 0A005300 75006200 43004130 1F060355 1D230418 30168014
27F3C815 1E6E9A02 0916AD2B A089605F DA7B2FAA 30430603 551D1F04 3C303A30
38A036A0 34863268 7474703A 2F2F7777 772E6369 73636F2E 636F6D2F 73656375
72697479 2F706B69 2F63726C 2F637263 61323034 382E6372 6C305006 082B0601
05050701 01044430 42304006 082B0601 05050730 02863468 7474703A 2F2F7777
772E6369 73636F2E 636F6D2F 73656375 72697479 2F706B69 2F636572 74732F63
72636132 3034382E 63657230 5C060355 1D200455 30533051 060A2B06 01040109
15010200 30433041 06082B06 01050507 02011635 68747470 3A2F2F77 77772E63
6973636F 2E636F6D 2F736563 75726974 792F706B 692F706F 6C696369 65732F69
6E646578 2E68746D 6C305E06 03551D25 04573055 06082B06 01050507 03010608
2B060105 05070302 06082B06 01050507 03050608 2B060105 05070306 06082B06
01050507 0307060A 2B060104 0182370A 0301060A 2B060104 01823714 02010609
2B060104 01823715 06300D06 092A8648 86F70D01 01050500 03820101 0030F330
2D8CF2CA 374A6499 24290AF2 86AA42D5 23E8A2EA 2B6F6923 7A828E1C 4C09CFA4
4FAB842F 37E96560 D19AC6D8 F30BF5DE D027005C 6F1D91BD D14E5851 1DC9E3F7
38E7D30B D168BE8E 22A54B06 E1E6A4AA 337D1A75 BA26F370 C66100A5 C379265B
A719D193 8DAB9B10 11291FA1 82FDFD3C 4B6E65DC 934505E9 AF336B67 23070686
22DAEBDC 87CF5921 421AE9CF 707588E0 243D5D7D 4E963880 97D56FF0 9B71D8BA
6019A5B0 6186ADDD 6566F6B9 27A2EE2F 619BBAA1 3061FDBE AC3514F9 B82D9706
AFC3EF6D CC3D3CEB 95E981D3 8A5EB6CE FA79A46B D7A25764 C43F4CC9 DBE882EC
0166D410 88A256E5 3C57EDE9 02A84891 6307AB61 264B1A13 9FE4DCDA 5F
quit
crypto pki certificate chain Cisco_Manufacturing_CA_SHA2
certificate ca 02
30820465 3082034D A0030201 02020102 300D0609 2A864886 F70D0101 0B050030
2B310E30 0C060355 040A1305 43697363 6F311930 17060355 04031310 43697363
6F20526F 6F742043 41204D32 301E170D 31323131 31323133 35303538 5A170D33
37313131 32313330 3031375A 3036310E 300C0603 55040A13 05436973 636F3124
30220603 55040313 1B436973 636F204D 616E7566 61637475 72696E67 20434120
53484132 30820122 300D0609 2A864886 F70D0101 01050003 82010F00 3082010A
02820101 00F4364B 42023267 DE493DF2 153BC145 69E9094E 16B948B4 471EE82A
5B7D8A5E 2DD51E65 DB80A3E4 B4A2DCD3 949C12D8 194C859B 5A72EF6F 5297E65B
DC3B9D0A 3DCD54F7 7B23EE84 5FFAFFD4 C4755067 EF9CDBE4 27D5F84E A577E7C7
9EE3E217 206EF870 C3251777 EF73A9FB DE7B21DA 16C8FBC3 F211D1D4 7246149D
C924A060 D1449C2F 8242C257 AEF7C5EA FF23E502 A0611316 BB6B6FDF A9299903
4BD9206D 5B05F599 63C66D49 E4F12A0D DE5B29D5 FB112569 B1EA4C33 1859FFB6
A1BB3860 1E6520D4 DB6201F2 4444CFE9 3F17AFA4 ED0F4877 EB9E0E50 7716FB59
9E06EFE3 72D96E30 AA697928 D5B6BA1F E6FB7EA5 B9028348 900008EC 2F4A9CCD
3DF268D5 EF020301 0001A382 01873082 0183300E 0603551D 0F0101FF 04040302
01063012 0603551D 130101FF 04083006 0101FF02 0100305C 0603551D 20045530
53305106 0A2B0601 04010915 01120030 43304106 082B0601 05050702 01163568
7474703A 2F2F7777 772E6369 73636F2E 636F6D2F 73656375 72697479 2F706B69
2F706F6C 69636965 732F696E 6465782E 68746D6C 301D0603 551D0E04 1604147A
D77995CA BB482BB8 5514FDA3 C00FBCA7 0F961930 41060355 1D1F043A 30383036
A034A032 86306874 74703A2F 2F777777 2E636973 636F2E63 6F6D2F73 65637572
6974792F 706B692F 63726C2F 63726361 6D322E63 726C307C 06082B06 01050507
01010470 306E303E 06082B06 01050507 30028632 68747470 3A2F2F77 77772E63
6973636F 2E636F6D 2F736563 75726974 792F706B 692F6365 7274732F 63726361
6D322E63 6572302C 06082B06 01050507 30018620 68747470 733A2F2F 746F6F6C
732E6369 73636F2E 636F6D2F 706B692F 6F637370 301F0603 551D2304 18301680
14C900F9 1F8A1FC2 66BDA5D2 6D650E22 2E34C305 A0300D06 092A8648 86F70D01
010B0500 03820101 00735936 AC7E984F 88EE171B 3DABB39B CDF70A6C DBCEC83B
1A53B6AF E081C55E 69FF2717 E706652F 631008D8 7C77C516 F42AD1B5 24691F7D
08D502D0 5BA135F2 9CB690B2 8FE38F8E 993AE6C8 17CCBA1E 8DE74C0B FB43A547
92A48275 90A556EF 75CDB1D5 F4515843 32718F0D 50801D1A E08B52E3 285D9A09
77A03344 71BDEDAD 07B3AD0D FFF39EFF 212A8119 52C46CA1 CEBBC1FA CCE2E1C4
0819D3C6 9ED68410 409A3092 2D086DDF 8B44B1A8 BED1302E 0F32CAA8 93206BDE
ED514BDA C45AF19D EB2BDB65 C0A547DA 4A4528D0 1E377ADF 285AABD3 FC1E4747
322A998B 32B4814C 165CC507 09098178 5FA14EFF 7D8A3AA7 3124520E 28654852
3BC0BE2A 0EAA876E 73
quit
crypto pki certificate chain Cisco_Root_CA_2048
certificate ca 5FF87B282B54DC8D42A315B568C9ADFF
30820343 3082022B A0030201 0202105F F87B282B 54DC8D42 A315B568 C9ADFF30
0D06092A 864886F7 0D010105 05003035 31163014 06035504 0A130D43 6973636F
20537973 74656D73 311B3019 06035504 03131243 6973636F 20526F6F 74204341
20323034 38301E17 0D303430 35313432 30313731 325A170D 32393035 31343230
32353432 5A303531 16301406 0355040A 130D4369 73636F20 53797374 656D7331
1B301906 03550403 13124369 73636F20 526F6F74 20434120 32303438 30820120
300D0609 2A864886 F70D0101 01050003 82010D00 30820108 02820101 00B09AB9
ABA7AF0A 77A7E271 B6B46662 94788847 C6625584 4032BFC0 AB2EA51C 71D6BC6E
7BA8AABA 6ED21588 48459DA2 FC83D0CC B98CE026 68704A78 DF21179E F46105C9
15C8CF16 DA356189 9443A884 A8319878 9BB94E6F 2C53126C CD1DAD2B 24BB31C4
2BFF8344 6FB63D24 7709EABF 2AA81F6A 56F6200F 11549781 75A725CE 596A8265
EFB7EAE7 E28D758B 6EF2DD4F A65E629C CF100A64 D04E6DCE 2BCC5BF5 60A52747
8D69F47F CE1B70DE 701B20D6 6ECDA601 A83C12D2 A93FA06B 5EBB8E20 8B7A91E3
B568EEA0 E7C40174 A8530B2B 4A9A0F65 120E824D 8E63FDEF EB9B1ADB 53A61360
AFC27DD7 C76C1725 D473FB47 64508180 944CE1BF AE4B1CDF 92ED2E05 DF020103
A351304F 300B0603 551D0F04 04030201 86300F06 03551D13 0101FF04 05300301
01FF301D 0603551D 0E041604 1427F3C8 151E6E9A 020916AD 2BA08960 5FDA7B2F
AA301006 092B0601 04018237 15010403 02010030 0D06092A 864886F7 0D010105
05000382 0101009D 9D8484A3 41A97C77 0CB753CA 4E445062 EF547CD3 75171CE8
E0C6484B B6FE4C3A 198156B0 56EE1996 62AA5AA3 64C1F64E 5433C677 FEC51CBA
E55D25CA F5F0939A 83112EE6 CBF87445 FEE705B8 ABE7DFCB 4BE13784 DAB98B97
701EF0E2 8BD7B0D8 0E9DB169 D62A917B A9494F7E E68E95D8 83273CD5 68490ED4
9DF62EEB A7BEEB30 A4AC1F44 FC95AB33 06FB7D60 0ADEB48A 63B09CA9 F2A4B953
0187D068 A4277FAB FFE9FAC9 40388867 B439C684 6F57C953 DBBA8EEE C043B2F8
09836EFF 66CF3EEF 17B35818 2509345E E3CBD614 B6ECF292 6F74E42F 812AD592
91E0E097 3C326805 854BD1F7 57E2521D 931A549F 0570C04A 71601E43 0B601EFE
A3CE8119 E10B35
quit
crypto pki certificate chain Cisco_Root_CA_M2
certificate ca 01
30820313 308201FB A0030201 02020101 300D0609 2A864886 F70D0101 0B050030
2B310E30 0C060355 040A1305 43697363 6F311930 17060355 04031310 43697363
6F20526F 6F742043 41204D32 301E170D 31323131 31323133 30303138 5A170D33
37313131 32313330 3031385A 302B310E 300C0603 55040A13 05436973 636F3119
30170603 55040313 10436973 636F2052 6F6F7420 4341204D 32308201 22300D06
092A8648 86F70D01 01010500 0382010F 00308201 0A028201 0100D806 2521134F
8D3A757C E93DC874 413B4DA0 65F9C2BF 9484EF6B 0B7187D4 58C26032 2CBACCBA
BB6334DB B312426A 798586B3 E87FC992 8BE3A737 45D39483 686520DB 8AD44341
DFCA4CD4 D710CD68 2795724E 744A54F5 DA71E9A5 AF4D0CB1 6C31FB0C DE73829A
50095E0E E335BEBA 4EC2CAE0 6EC8842D 8AB3EE92 EC0482E4 C76E4D18 B5E964CB
6486D2F0 B8E15916 3AA62648 05EE6329 1E1583EF 1E79C182 0029D456 8F0A6DC2
C858392D 63B87180 3AE1DCEB B3135222 05514700 88876DED D13CD7B8 DA857924
C62A5D1D F2834D81 1FA7CDD4 198EAB69 40E6FB07 0AF28E65 3E6DE53D C132EE06
262DECBB 1EB14562 512BF059 1731721A CC0074C3 0CBB84CA 73AD0203 010001A3
42304030 0E060355 1D0F0101 FF040403 02010630 0F060355 1D130101 FF040530
030101FF 301D0603 551D0E04 160414C9 00F91F8A 1FC266BD A5D26D65 0E222E34
C305A030 0D06092A 864886F7 0D01010B 05000382 0101007A BE3C8D27 E8CDE492
1CA68B30 6EC1D9D6 891AC3C0 9975F74E B582C895 2259B7A0 A8508E59 190B6F16
D90FF219 274D504D DEF46D0C E6745C74 F1447F82 92BC5C5E E3B37E25 A38BB910
3C6B5D5D 3E693BDC A85BEDA7 C2BAE8C2 F768CB28 8B707291 CF2C3FBA 75597333
52198294 ED709ED2 67147631 1B26A6A9 F97E7B19 B6E2A752 A2D453EA 6F867833
07C1DE7D DF15D03D 6CA225BC C732F049 7B6DF230 669BD914 5DB60FA5 6C5B926B
86B41304 8763F57D 69AE2262 6C767292 9AF3055E 6633E597 20E00D79 346F311D
585ECDE0 25C1C3A5 DD10DCCE 7E95F6DB 44A75DC6 7192CFA1 81FAF08D E9A6D992
C3E4F0AD DB6CAFEE ADDA8B09 4AFBDA2A 9E981650 077F87
quit
crypto pki certificate chain CAPF-19a340e5
certificate ca 4745CDD0D3E0387C09316AE7ED0914CD
308203A1 30820289 A0030201 02021047 45CDD0D3 E0387C09 316AE7ED 0914CD30
0D06092A 864886F7 0D010105 05003065 310B3009 06035504 06130255 53310E30
0C060355 040A0C05 63697363 6F310C30 0A060355 040B0C03 74616331 16301406
03550403 0C0D4341 50462D31 39613334 30653531 0B300906 03550408 0C027478
31133011 06035504 070C0A72 69636861 7264736F 6E301E17 0D313630 35323031
37303530 385A170D 32313035 31393137 30353037 5A306531 0B300906 03550406
13025553 310E300C 06035504 0A0C0563 6973636F 310C300A 06035504 0B0C0374
61633116 30140603 5504030C 0D434150 462D3139 61333430 6535310B 30090603
5504080C 02747831 13301106 03550407 0C0A7269 63686172 64736F6E 30820122
300D0609 2A864886 F70D0101 01050003 82010F00 3082010A 02820101 0097753D
51483CE9 66F8EF0D DC131D63 C6B7408E C0B465A0 0D597B8E 2F7EEEBB 34E0E4F8
77D2C53C 4C9AF2E0 D75D6F92 C5CCBDC6 C7CCB58D A1CC7288 300D9678 94E1645B
109DD7DF A7104B07 C98B41CD 7262096D A9DE1076 7F40F787 16BA70DF C18C3C66
9453CC28 F294A7F2 BFFE8F8C 0D7268D4 55C63554 6C6B28ED 073BF7F9 BED32D99
A5D63ACD 673D8476 5E26F6A4 73526766 7E34063D 86AFFFA5 E5B509BB 962FF514
8263F539 2542A9DB A4473F49 E2D79CF4 C495E608 DBBA015A B2F69281 50FB0400
8D946575 42DD1689 B2435512 0BEBC2E5 6C223C1B D5B45F40 527C67F1 F89A97AF
5ECFD7ED 738F4D19 D5421F95 E0E940DF 1F8C83B0 28F80862 F5CDC690 55020301
0001A34D 304B300B 0603551D 0F040403 0202A430 1D060355 1D250416 30140608
2B060105 05070301 06082B06 01050507 0305301D 0603551D 0E041604 14F66D8B
E1B34990 F0483694 A2D1D37E ACA52C59 22300D06 092A8648 86F70D01 01050500
03820101 006C0E8F 9E3B17B5 C902C177 F931099A 3177669F C1196185 0A3F72E4
EB046423 FB1C7BB1 D0D7255C BB4C6074 9AD2815F 9059FF2E 8216E473 6839DB2A
9600C167 40172BAF 17679406 3EDDB4CD E5F5B96D 1354C6C2 7ACE1867 74EB5CB2
0423ACE8 B66FF253 13393E13 BE08C8D6 28AF907B 2FCECC91 C1A86A2B C311DEC0
9A20C3AF FD0629A0 2A30ED70 7369F570 1A38FD85 B4BEA740 4D87AF64 42B68F99
C8B16842 F75F49A5 2FA41571 BA9757F0 F0C7D22D 221A4442 9E20D7C7 5A90D912
7C4BAD41 BB929AC5 89526810 F6B96C28 FC6BFE69 BEBFF33B ECC59282 0F20D269
13A662BB E11D2E69 B1D8561B 881F35DF 8E1549A7 2154A8E1 AE967842 5CC6FC22
0F99CE3D 90
quit
crypto pki certificate chain CAPF-dc3cda68
certificate ca 55FF50FABA2D6E7EBD5EF96F32451117
308203A1 30820289 A0030201 02021055 FF50FABA 2D6E7EBD 5EF96F32 45111730
0D06092A 864886F7 0D010105 05003065 310B3009 06035504 06130255 53310E30
0C060355 040A0C05 63697363 6F310C30 0A060355 040B0C03 74616331 16301406
03550403 0C0D4341 50462D64 63336364 61363831 0B300906 03550408 0C027478
31133011 06035504 070C0A72 69636861 7264736F 6E301E17 0D313630 35323632
30303430 345A170D 32313035 32353230 30343033 5A306531 0B300906 03550406
13025553 310E300C 06035504 0A0C0563 6973636F 310C300A 06035504 0B0C0374
61633116 30140603 5504030C 0D434150 462D6463 33636461 3638310B 30090603
5504080C 02747831 13301106 03550407 0C0A7269 63686172 64736F6E 30820122
300D0609 2A864886 F70D0101 01050003 82010F00 3082010A 02820101 0088A466
E4A472FB BA1CF50D CF98FA6A BC625C9B 51B46772 30ECA673 6226002C 2E6A5F53
FD193E14 E08DEEB9 0DDF2485 1EE7DBC1 2B45973A 94659A40 37E1AAE0 CF56AE82
78C369F2 B0BF2D7C 9072CA2C F00D9754 E641F27D 140A849C A1D71922 35167213
30BED42B 11C7A601 C12F5DFC 0F3C4277 0638F285 9FF6F3A4 CD017CBA A4B4685B
62BDF035 2A570A48 1ACA0618 763BBA81 C2734558 9575E08B 008A365C EE376461
31D3FEE1 0A579F46 4CEAF0F3 4231A81B 9A82ABD7 60D91735 1DE7F325 79D15BD5
55DD807E D37008DD F4440C36 5A8ABB0E 15EF5530 07031278 D0BFB69F 6F3BDC95
046F7949 0A848C86 7B72BEDF 496748BC 300B3772 6E997BA8 73204638 FF020301
0001A34D 304B300B 0603551D 0F040403 0202A430 1D060355 1D250416 30140608
2B060105 05070301 06082B06 01050507 0305301D 0603551D 0E041604 147B0417
3B747718 BBA4521F 3727684A 05DBDE19 5A300D06 092A8648 86F70D01 01050500
03820101 007F6D12 E049495C 081D95F9 49FC254A EA3144DA 9CAA8A9A 5A865938
F43D2FC3 1B060434 720B2F85 EF5EEA48 3E5F528B 9F222526 42FE5E83 59F91EBA
EAC14360 4A05BEE3 2FA68B9E 5C49091F 34D8A956 B1ABA51F 8CD416A5 24A57763
A26A59AC 9B525EE2 B927D87F E28DA955 7EC0D322 04AAA2A1 BB92CF21 A5D14151
6E551D5E AEE4BE5C F205AF08 AFEB44D4 624D34AE A9ECD8DE CD09A1E1 212DAA19
61555E04 29A2A688 76515E91 EB2600CE F005C570 7F37C514 654F2A5C 7E52B88B
6341575E 08C71102 BC536A18 D5797501 AC8C775A 230ACCC2 41FA0B03 D3B01653
D3083B3C F942F0A6 FC71969B 006B3975 B9DA33D1 5041A500 38646FFA 2BB0DCC4
DB80BE20 2C
quit
!
!
!
voice service voip
ip address trusted list
ipv4 0.0.0.0 0.0.0.0
no ip address trusted authenticate
media bulk-stats
media disable-detailed-stats
srtp
allow-connections sip to sip
no supplementary-service sip refer
no supplementary-service sip handle-replaces
supplementary-service media-renegotiate
fax protocol t38 version 0 ls-redundancy 0 hs-redundancy 0 fallback none
modem passthrough nse codec g711ulaw
sip
bind control source-interface GigabitEthernet0/0/0
bind media source-interface GigabitEthernet0/0/0
rel1xx disable
registrar server expires max 120 min 60
!
voice class codec 1
codec preference 1 g711ulaw
!
!
!
!
!
voice iec syslog
!
voice register global
default mode
no allow-hash-in-dn
security-policy secure
max-dn 50
max-pool 40
!
voice register pool 1
id network A.B.C.0 mask 255.255.255.0
dtmf-relay rtp-nte
codec g711ulaw
!
!
!
voice-card 0/1
no local-bypass
no watchdog
!
voice-card 0/3
no watchdog
!
voice-card 0/4
no watchdog
!
license udi pid ISR4431/K9 sn FOCXXXXXXXX
license accept end user agreement
license boot level uck9
license boot level securityk9
diagnostic bootup level minimal
!
spanning-tree extend system-id
!
!
!
!
redundancy
mode none
!
!
interface GigabitEthernet0/0/0
ip address A.B.C.D 255.255.255.192
negotiation auto
!
interface GigabitEthernet0/0/1
no ip address
shutdown
negotiation auto
!
interface GigabitEthernet0/0/2
no ip address
shutdown
negotiation auto
!
interface GigabitEthernet0/0/3
no ip address
shutdown
negotiation auto
!
interface Service-Engine0/1/0
!
interface Service-Engine0/3/4
!
interface Service-Engine0/4/0
!
interface GigabitEthernet0
vrf forwarding Mgmt-intf
no ip address
shutdown
negotiation auto
!
interface BRI0/3/0:0
isdn incoming-voice voice
!
interface BRI0/3/1:0
isdn incoming-voice voice
!
interface BRI0/3/2:0
isdn incoming-voice voice
!
interface BRI0/3/3:0
isdn incoming-voice voice
!
ip forward-protocol nd
ip http server
ip http authentication local
ip http secure-server
ip tftp source-interface GigabitEthernet0/0/0
ip route 0.0.0.0 0.0.0.0 GigabitEthernet0/0/0 XX.XX.XX.XX
!
!
!
!
!
!
control-plane
!
!
voice-port 0/1/0
no battery-reversal
!
voice-port 0/1/1
!
voice-port 0/1/2
!
voice-port 0/1/3
!
voice-port 0/1/4
!
voice-port 0/1/5
!
voice-port 0/3/0
!
voice-port 0/3/1
!
voice-port 0/3/2
!
voice-port 0/3/3
!
mgcp behavior rsip-range tgcp-only
mgcp behavior comedia-role none
mgcp behavior comedia-check-media-src disable
mgcp behavior comedia-sdp-force disable
!
mgcp profile default
!
!
!
!
!
!
!
credentials
ip source-address A.B.C.D port 2445
trustpoint srstca
!
sip-ua
crypto signaling default trustpoint srstca
!
!
!
line con 0
logging synchronous
transport input none
stopbits 1
line aux 0
stopbits 1
line vty 0 4
logging synchronous
login local
transport input all
!
wsma agent exec
!
wsma agent config
!
wsma agent filesys
!
wsma agent notify
!
!
end
Router1#
確認
ここでは、設定が正常に機能しているかどうかを確認します。
Cisco IOS証明書サーバをCAとして使用した場合は、 show running-config 証明書の登録または show crypto pki server コマンドを発行して、CAサーバのステータスを確認します。
Router# show crypto pki server
Certificate Server srstcaserver:
Status: enabled
Server's configuration is locked (enter "shut" to unlock it)
Issuer name: CN=srstcaserver
CA cert fingerprint: AC9919F5 CAFE0560 92B3478A CFF5EC00
Granting mode is: auto
Last certificate issued serial number: 0x2
CA certificate expiration timer: 13:46:57 PST Dec 1 2021
CRL NextUpdate timer: 14:54:57 PST Jan 19 2019
Current storage dir: nvram
Database Level: Complete - all issued certs written as <serialnum>.cer
登録を確認するには、show sip-ua status registrarを使用します
トラブルシュート
現在、この設定に関する特定のトラブルシューティング情報はありません。
関連情報
シスコ エンジニア提供
- Ankush VijayCisco TAC Engineer
シスコに問い合わせ
- サポート ケースをオープン

- (シスコ サービス契約が必要です。)
 フィードバック
フィードバック