Ultra Cloud Core User Plane Function
Introduction
This Release Notes identifies changes and issues related to this software release.
Release Lifecycle Milestones
|
Release Lifecycle Milestone |
Milestone |
Date |
|---|---|---|
|
First Customer Ship |
FCS |
30-Apr-2025 |
|
End of Life |
EoL |
30-Apr-2025 |
|
End of Software Maintenance |
EoSM |
29-Oct-2026 |
|
End of Vulnerability and Security Support |
EoVSS |
29-Oct-2026 |
|
Last Date of Support |
LDoS |
31-Oct-2027 |
These milestones and the intervals between them are defined in the Cisco Ultra Cloud Core (UCC) Software Release Lifecycle Product Bulletin available on cisco.com.
Release Package Version Information
|
Software Packages |
Version |
|---|---|
|
companion-vpc-2025.02.0.zip.SPA.tar.gz |
2025.02.0 (21.28.m35.97821) |
|
qvpc-si-2025.02.0.bin.SPA.tar.gz |
2025.02.0 (21.28.m35.97821) |
|
qvpc-si-2025.02.0.qcow2.zip.SPA.tar.gz |
2025.02.0 (21.28.m35.97821) |
|
NED package |
ncs-6.4.3-cisco-staros-5.56.1 |
|
NSO |
6.4.3 |
Use this link to download the NED package associated with the software.
Descriptions for the various packages provided with this release are available in the Release Package Descriptions section.
Verified Compatibility
|
Products |
Version |
|---|---|
|
ADC Plugin |
2.74.8.2658 |
|
RCM |
2025.02.0.i46 |
|
Ultra Cloud Core SMI |
2025.02.1.i17 |
|
Ultra Cloud Core SMF |
2025.02.0 |
What's New in this Release
Features and Enhancements
This section covers a brief description of the features and enhancements introduced in this release. It also includes links to detailed documentation, where available.
| Feature | Description | ||
|---|---|---|---|
|
DHCP-based IP Address Allocation |
This feature allows the network operator to use an external DHCP server to receive IP addresses for subscriber UEs. Allocating IP addresses using a DHCP server enables the enterprises with complex 5G networks to manage and control the IP address allocation centrally.
Commands Introduced: dhcp server enable-discover slot/port slot_port_number dhcp-node-id node_id : This CLI is configured under DHCP service configuration mode to allow UPF to discover the DHCP server. Commands Enhanced: dhcp ip skip-validation : This CLI is configured under the DHCP service configuration mode to skip the IPv4 address validation. Default Settings: Disabled—Configuration Required to Enable |
Behavior Changes
There are no behavior changes in this release.
Installation and Upgrade Notes
This Release Note does not contain general installation and upgrade instructions. Refer to the existing installation documentation for specific installation and upgrade considerations.
Software Integrity Verification
To verify the integrity of the software image you have from Cisco, you can validate the SHA512 checksum information against the checksum identified by Cisco for the software.
Image checksum information is available through Cisco.com Software Download Details. To find the checksum, hover the mouse pointer over the software image you have downloaded.
The following screenshot is an example of a UPF release posted in the Software Download page.
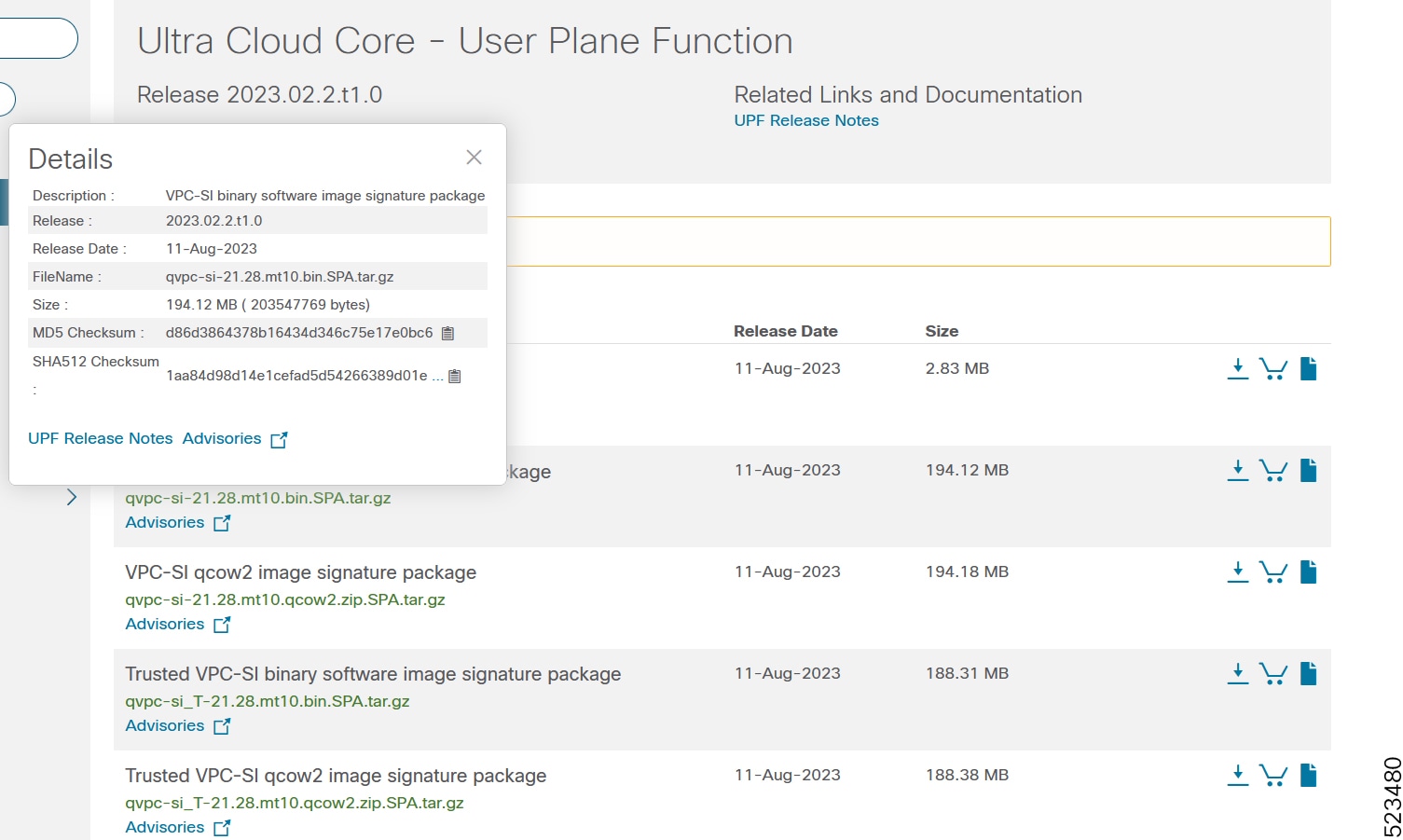
At the bottom you find the SHA512 checksum, if you do not see the whole checksum you can expand it by pressing the "..." at the end.
To validate the information, calculate a SHA512 checksum using the information in Table 1 and verify that it matches either the one provided on the software download page.
To calculate a SHA512 checksum on your local desktop, refer to the following table.
|
Operating System |
SHA512 checksum calculation command examples |
|---|---|
|
Microsoft Windows |
Open a command line window and type the following command: |
|
Apple MAC |
Open a terminal window and type the following command: |
|
Linux |
Open a terminal window and type the following command: OR |
|
NOTES: filename is the name of the file. extension is the file extension (for example, .zip or .tgz). |
|
If the SHA512 checksum matches, you can be sure that no one has tampered with the software image or the image has not been corrupted during download.
If the SHA512 checksum does not match, we advise you to not attempt upgrading any systems with the corrupted software image. Download the software again and verify the SHA512 checksum again. If there is a constant mismatch, please open a case with the Cisco Technical Assistance Center.
Certificate Validation
UPF software images are signed via x509 certificates. Please view the .README file packaged with the software for information and instructions on how to validate the certificates.
Open Bugs for this Release
The following table lists the open bugs in this specific software release.
 Note |
This software release may contain open bugs first identified in other releases. Additional information for all resolved bugs for this release are available in the Cisco Bug Search Tool. |
|
Bug ID |
Headline |
|---|---|
|
Continuous sxdemux error logs "MISMATCH: IMSI ENTRY [SMGR-ID:10 IMSI:123456789123456]" |
|
|
sessmgr restart function sessmgr_uplane_gtpu_tx_setup_n4 |
|
|
CRR recovery failure recovery-invalid-crr-clp-uplane-record-info observed with ICSR UPF swo |
|
|
UPF should allow to configure dhcpv6 service without server-profile under apn |
|
|
vpnctrl restart observed at Function: vc_cdr_update_xdr_reset_ind() |
|
|
UPF should send Decline if DHCP Server assigns same IP to a second UE |
|
|
DHCP Partially allocated calls are not recovered on new ICSR Active after SW |
|
|
UPF sends different chaddr after session recovery |
|
|
Incorrect disconnect reasons and cause codes during DHCP failure scenarios |
|
|
UPF showing incorrect disconnect reason when dhcp serive or vlan port shut down & new call attach |
|
|
DHCPv6 solicit - sessmgr wrongly sending sw_if_index to VPP causing packet to be blackholed packets |
|
|
sessmgr restart observed at libc.so.6/__memset_sse2_rep() |
|
|
sessmgr restart observed at sessmgr_uplane_send_ddn_n_buff_dl_pkts_before_processing() |
|
|
smp-fp-strm-chrg-oper-failure pegging in session disconnect-reasons on RCM UPFs |
|
|
Sessmgr restart at sessmgr_Uplane_collect_pdr_info() |
|
|
Sx instance checkpoint is arriving late in Sx demux is not included |
|
|
GR Checkpoint ignored for callid<> and cmd 232 as clp audit is completed |
Resolved Bugs for this Release
The following table lists the resolved bugs in this specific software release.
 Note |
This software release may contain open bugs first identified in other releases. Additional information for all open bugs for this release are available in the Cisco Bug Search Tool. |
|
Bug ID |
Headline |
Behavior Change |
|---|---|---|
|
Seen Uplane received invalid far id in PDU on task kill |
No |
|
|
Time quota is not reset post UPF 1:1 ICSR, in case new quota is not provisioned. |
No |
|
|
Idletimer is triggered post switchover, even if UE is not in idle state for defined duration. |
No |
|
|
Nat IP and Port chunk struck in scenario of ICMPv6 traffic involving config modification |
No |
|
|
Need cli enhancement to clear monsub session at npu and sessmgr. |
No |
|
|
UPF Crash - Assertion failure at sess/smgr/sessmgr_uplane.c:32102 |
No |
|
|
EDRs w/non-zero byte count and w/o NAT IP in CUPS UP |
Yes |
|
|
Data stall issue is reported for CUPS |
No |
|
|
DIMM failure induced b2b switchover results in all session loss |
No |
|
|
TCP OOO observed in Converged core only for Pure S SGW-U session after exiting VPP |
No |
|
|
Continuous sessmgr restart with function dhcpv6app_server_fsm_handler() |
No |
|
|
'show rcm monitor' CLI may report 'SX monitors down' even though peers are up |
No |
|
|
sessmgr gives error at libc.so.6/__strncpy_sse2() |
No |
|
|
Seen sessmgr restarted at sessmgr_uplane_sx_update_far_apply_action() |
No |
|
|
HTTP GET packets not getting forwarded from CUPS |
No |
|
|
sessmgr restart @ sessmgr_uplane_start_self_protection_call_cleanup_timer |
No |
|
|
DNS Snoop rules changes causing high CPU in UPF |
No |
Operator Notes
StarOS Version Numbering System
The outputof the showversion command displays detailed information about the version of StarOS currently running on the ASR 5500 or Cisco Virtualized Packet Core platform.
 Note |
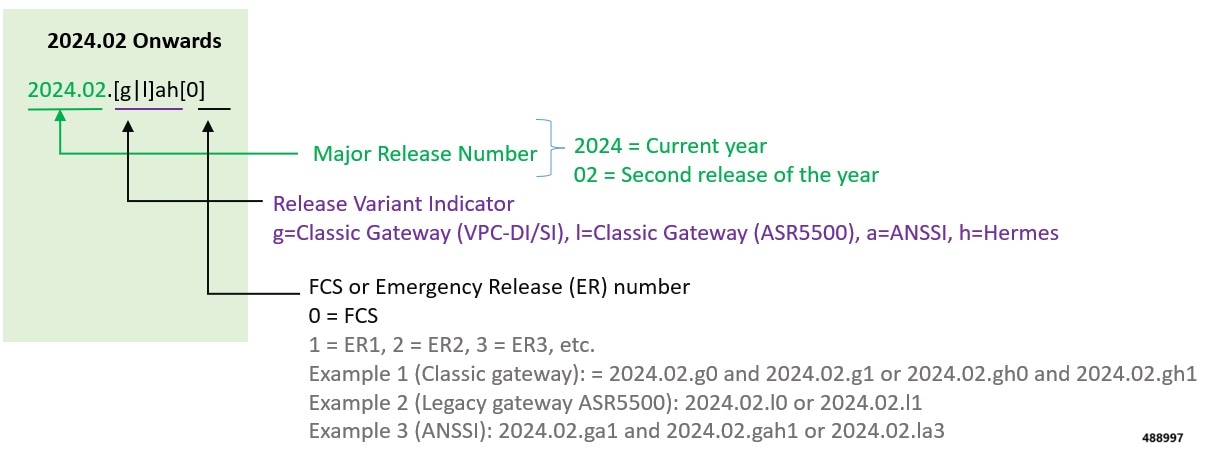
Starting 2024.01.0 release (January 2024), Cisco is transitioning to a new release versioning scheme. The release version is based on the current year and product. Refer to the figure for more details. |
During the transition phase, some file names willreflect the new versioning whereas others will refer to the 21.28.x- based naming convention. With the next release, StarOS-related packages will be completely migrated to the new versioning scheme.
 Note |
For any clarification, contact your Cisco account representative. |
Cloud Native Product Version Numbering System
The show helm list command displays detailed information about the version of the cloud native product currently deployed.
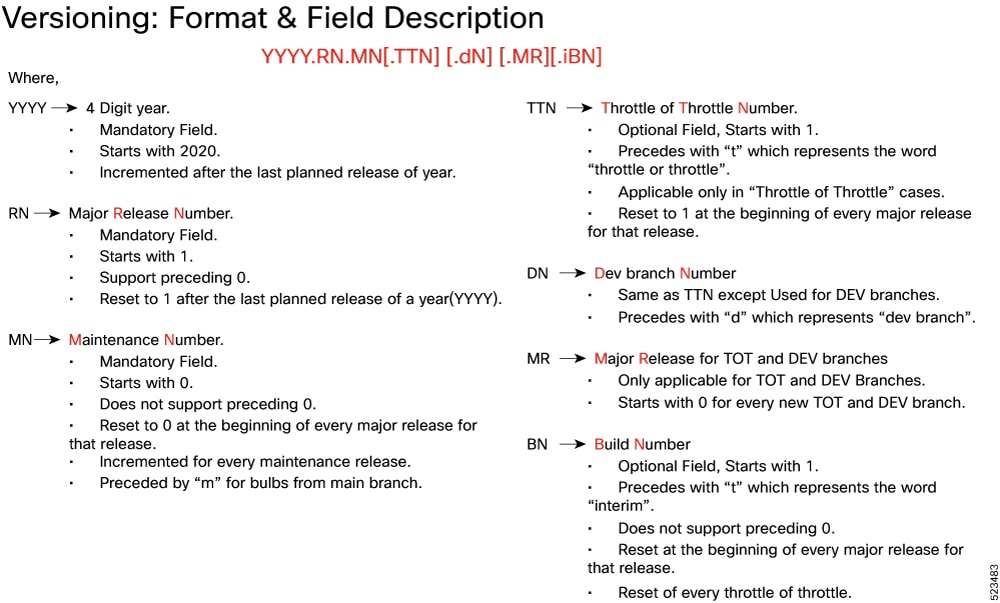
The appropriate version number field increments after a version has been released. The new version numbering format is a contiguous sequential number that represents incremental changes between releases. This format facilitates identifying the changes between releases when using Bug Search Tool to research software releases.
Release Package Descriptions
The following table provides descriptions for the packages that are available with this release.
|
Software Packages |
Description |
|---|---|
|
companion-vpc-<staros_version>.zip.SPA.tar.gz |
Contains files pertaining to VPC, including SNMP MIBs, RADIUS dictionaries, ORBEM clients, etc. These files pertain to both trusted and non-trusted build variants. The VPC companion package also includes the release signature file, a verification script, the x.509 certificate, and a README file containing information on how to use the script to validate the certificate. |
|
qvpc-si-<staros_version>.bin.SPA.tar.gz |
The UPF release signature package. This package contains the VPC-SI deployment software for the UPF as well as the release signature, certificate, and verification information. Files within this package are nested under a top-level folder pertaining to the corresponding StarOS build. |
|
qvpc-si-<staros_version>.qcow2.zip.SPA.tar.gz |
The UPF release signature package. This package contains the VPC-SI deployment software for the UPF as well as the release signature, certificate, and verification information. Files within this package are nested under a top-level folder pertaining to the corresponding StarOS build. |
|
ncs-<nso_version>-cisco-staros-<version>.signed.bin |
The NETCONF NED package. This package includes all the files that are used for NF configuration. Note that NSO is used for NED file creation. |
Obtaining Documentation and Submitting a Service Request
For information on obtaining documentation, using the Cisco Bug Search Tool (BST), submitting a service request, and gathering additional information, refer to https://www.cisco.com/c/en/us/support/index.html.
 Feedback
Feedback