- New and Changed Information
- Preface
- Overview
- Configuring FIPS
- Common Roles
- Configuring Security Features on an External AAA Server
- Configuring IPv4 and IPv6 Access Control Lists
- Configuring Certificate Authorities and Digital Certificates
- Configuring IPSec Network Security
- Configuring FC-SP and DHCHAP
- Configuring Port Security
- Configuring Fibre Channel Common Transport Management Security
- Configuring Fabric Binding
- Configuring Cisco TrustSec Fibre Channel Link Encryption
Cisco MDS 9000 Family NX-OS Security Configuration Guide
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- February 13, 2016
Chapter: Configuring FC-SP and DHCHAP
- About Fabric Authentication
- DHCHAP
- DHCHAP Compatibility with Existing Cisco MDS Features
- About Enabling DHCHAP
- Enabling DHCHAP
- About DHCHAP Authentication Modes
- Configuring the DHCHAP Mode
- About DHCHAP Hash Algorithm
- Configuring the DHCHAP Hash Algorithm
- About DHCHAP Group Settings
- Configuring the DHCHAP Group Settings
- About DHCHAP Password
- Configuring DHCHAP Passwords for the Local Switch
- About Password Configuration for Remote Devices
- Configuring DHCHAP Passwords for Remote Devices
- About DHCHAP Timeout Value
- Configuring the DHCHAP Timeout Value
- Configuring DHCHAP AAA Authentication
- Displaying Protocol Security Information
- Sample Configuration
- Default Settings
Configuring FC-SP and DHCHAP
About Fabric Authentication
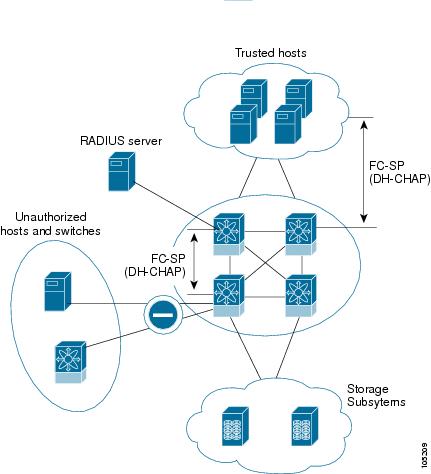
Fibre Channel Security Protocol (FC-SP) capabilities provide switch-switch and host-switch authentication to overcome security challenges for enterprise-wide fabrics. Diffie-Hellman Challenge Handshake Authentication Protocol (DHCHAP) is an FC-SP protocol that provides authentication between Cisco MDS 9000 Family switches and other devices. DHCHAP consists of the CHAP protocol combined with the Diffie-Hellman exchange.

Note![]() Cisco NX-OS Release 6.2(1) does not support the Fibre Channel Security Protocol (FC-SP) feature only on Cisco MDS 9710. Support for FC-SP on Cisco MDS 9710 begins in Cisco NX-OS Release 6.2(9).
Cisco NX-OS Release 6.2(1) does not support the Fibre Channel Security Protocol (FC-SP) feature only on Cisco MDS 9710. Support for FC-SP on Cisco MDS 9710 begins in Cisco NX-OS Release 6.2(9).
To authenticate through VFC ports, FC-SP peers use the port VSAN for communication. Hence, the port VSAN needs to be the same and active on both the peers to send and receive authentication messages.
All switches in the Cisco MDS 9000 Family enable fabric-wide authentication from one switch to another switch, or from a switch to a host. These switch and host authentications are performed locally or remotely in each fabric. As storage islands are consolidated and migrated to enterprise-wide fabrics new security challenges arise. The approach of securing storage islands cannot always be guaranteed in enterprise-wide fabrics.
For example, in a campus environment with geographically distributed switches someone could maliciously interconnect incompatible switches or you could accidentally do so, resulting in Inter-Switch Link (ISL) isolation and link disruption. This need for physical security is addressed by switches in the Cisco MDS 9000 Family (see Figure 8-1).
Figure 8-1 Switch and Host Authentication

Note![]() Fibre Channel (FC) host bus adapters (HBAs) with appropriate firmware and drivers are required for host-switch authentication.
Fibre Channel (FC) host bus adapters (HBAs) with appropriate firmware and drivers are required for host-switch authentication.
DHCHAP
DHCHAP is an authentication protocol that authenticates the devices connecting to a switch. Fibre Channel authentication allows only trusted devices to be added to a fabric, which prevents unauthorized devices from accessing the switch.

Note![]() The terms FC-SP and DHCHAP are used interchangeably in this chapter.
The terms FC-SP and DHCHAP are used interchangeably in this chapter.
DHCHAP is a mandatory password-based, key-exchange authentication protocol that supports both switch-to-switch and host-to-switch authentication. DHCHAP negotiates hash algorithms and DH groups before performing authentication. It supports MD5 and SHA-1 algorithm-based authentication.
Configuring the DHCHAP feature requires the ENTERPRISE_PKG license (see the Cisco MDS 9000 Family NX-OS Licensing Guide).
To configure DHCHAP authentication using the local password database, follow these steps:
Step 2![]() Identify and configure the DHCHAP authentication modes.
Identify and configure the DHCHAP authentication modes.
Step 3![]() Configure the hash algorithm and DH group.
Configure the hash algorithm and DH group.
Step 4![]() Configure the DHCHAP password for the local switch and other switches in the fabric.
Configure the DHCHAP password for the local switch and other switches in the fabric.
Step 5![]() Configure the DHCHAP timeout value for reauthentication.
Configure the DHCHAP timeout value for reauthentication.
Step 6![]() Verify the DHCHAP configuration.
Verify the DHCHAP configuration.
This section includes the following topics:
- DHCHAP Compatibility with Existing Cisco MDS Features
- About Enabling DHCHAP
- Enabling DHCHAP
- About DHCHAP Authentication Modes
- Configuring the DHCHAP Mode
- About DHCHAP Hash Algorithm
- Configuring the DHCHAP Hash Algorithm
- About DHCHAP Group Settings
- Configuring the DHCHAP Group Settings
- About DHCHAP Password
- Configuring DHCHAP Passwords for the Local Switch
- About Password Configuration for Remote Devices
- Configuring DHCHAP Passwords for Remote Devices
- About DHCHAP Timeout Value
- Configuring the DHCHAP Timeout Value
- Configuring DHCHAP AAA Authentication
- Displaying Protocol Security Information
DHCHAP Compatibility with Existing Cisco MDS Features
This section identifies the impact of configuring the DHCHAP feature along with existing Cisco MDS features:
- PortChannel interfaces—If DHCHAP is enabled for ports belonging to a PortChannel, DHCHAP authentication is performed at the physical interface level, not at the PortChannel level.
- FCIP interfaces—The DHCHAP protocol works with the FCIP interface just as it would with a physical interface.
- Port security or fabric binding—Fabric binding policies are enforced based on identities authenticated by DHCHAP.
- VSANs—DHCHAP authentication is not done on a per-VSAN basis.
- High availability—DHCHAP authentication works transparently with existing HA features.
About Enabling DHCHAP
By default, the DHCHAP feature is disabled in all switches in the Cisco MDS 9000 Family.
You must explicitly enable the DHCHAP feature to access the configuration and verification commands for fabric authentication. When you disable this feature, all related configurations are automatically discarded.
Enabling DHCHAP
To enable DHCHAP for a Cisco MDS switch, follow these steps:
|
|
|
|
|---|---|---|
About DHCHAP Authentication Modes
The DHCHAP authentication status for each interface depends on the configured DHCHAP port mode.
When the DHCHAP feature is enabled in a switch, each Fibre Channel interface or FCIP interface may be configured to be in one of four DHCHAP port modes:
- On—During switch initialization, if the connecting device supports DHCHAP authentication, the software performs the authentication sequence. If the connecting device does not support DHCHAP authentication, the software moves the link to an isolated state.
- Auto-Active—During switch initialization, if the connecting device supports DHCHAP authentication, the software performs the authentication sequence. If the connecting device does not support DHCHAP authentication, the software continues with the rest of the initialization sequence.
- Auto-Passive (default)—The switch does not initiate DHCHAP authentication, but participates in DHCHAP authentication if the connecting device initiates DHCHAP authentication.
- Off—The switch does not support DHCHAP authentication. Authentication messages sent to such ports return error messages to the initiating switch.

Note![]() Whenever DHCHAP port mode is changed to a mode other than the Off mode, reauthentication is performed.
Whenever DHCHAP port mode is changed to a mode other than the Off mode, reauthentication is performed.

Note![]() Changing DHCHAP port mode for a VE link requires a port flap on both the ends.
Changing DHCHAP port mode for a VE link requires a port flap on both the ends.
Table 8-1 identifies the switch-to-switch authentication behavior between two Cisco MDS switches in various modes.
|
|
|
|||
|---|---|---|---|---|
|
|
|
|
|
|
|
|
||||
|
|
||||
|
|
||||
|
|
||||
Configuring the DHCHAP Mode
To configure the DHCHAP mode for a particular interface, follow these steps:
About DHCHAP Hash Algorithm
Cisco MDS switches support a default hash algorithm priority list of MD5 followed by SHA-1 for DHCHAP authentication.

Tip![]() If you change the hash algorithm configuration, then change it globally for all switches in the fabric.
If you change the hash algorithm configuration, then change it globally for all switches in the fabric.

Configuring the DHCHAP Hash Algorithm
To configure the hash algorithm, follow these steps:
About DHCHAP Group Settings
FC-SP supports multiple DHCHAP groups. The allowed groups may be changed from the default list. The list is configured in the order of highest to lowest priority to be used when negotiating with the FC-SP peer. Each side compares the list of groups received with the local group list and the highest priority group is used. Each group should be specified no more than once in the configuration command.
Refer to the fcsp dhchap command in the Cisco MDS 9000 Series NX-OS Command Reference Guide for details about the groups.

Tip![]() If you change the DH group configuration, change it globally for all switches in the fabric.
If you change the DH group configuration, change it globally for all switches in the fabric.
Configuring the DHCHAP Group Settings
To change the DH group settings, follow these steps:
|
|
|
|
|---|---|---|
Specifies the list of DH groups to be use. The list is specified in order of descending priority. Unspecified groups are excluded from use by DHCHAP. |
||
About DHCHAP Password
DHCHAP authentication in each direction requires a shared secret password between the connected devices. To do this, you can use one of three approaches to manage passwords for all switches in the fabric that participate in DHCHAP.
- Approach 1—Use the same password for all switches in the fabric. This is the simplest approach. When you add a new switch, you use the same password to authenticate that switch in this fabric. It is also the most vulnerable approach if someone from the outside maliciously attempts to access any one switch in the fabric.
- Approach 2—Use a different password for each switch and maintain that password list in each switch in the fabric. When you add a new switch, you create a new password list and update all switches with the new list. Accessing one switch yields the password list for all switches in that fabric.
- Approach 3—Use different passwords for different switches in the fabric. When you add a new switch, multiple new passwords corresponding to each switch in the fabric must be generated and configured in each switch. Even if one switch is compromised, the password of other switches are still protected. This approach requires considerable password maintenance by the user.

Note![]() All passwords are restricted to 64 alphanumeric characters and can be changed, but not deleted.
All passwords are restricted to 64 alphanumeric characters and can be changed, but not deleted.

Tip![]() We recommend using RADIUS or TACACS+ for fabrics with more than five switches. If you need to use a local password database, you can continue to do so using Approach 3 and using the Cisco MDS 9000 Family Fabric Manager to manage the password database.
We recommend using RADIUS or TACACS+ for fabrics with more than five switches. If you need to use a local password database, you can continue to do so using Approach 3 and using the Cisco MDS 9000 Family Fabric Manager to manage the password database.
Configuring DHCHAP Passwords for the Local Switch
To configure the DHCHAP password for the local switch, follow these steps:
To configure the DHCHAP password for the local switch using Fabric Manager, follow these steps:
Step 1![]() Expand Switches > Security and then select FC-SP.
Expand Switches > Security and then select FC-SP.
You see the FC-SP configuration in the Information pane.
Step 2![]() Click the Local Passwords tab.
Click the Local Passwords tab.
Step 3![]() Click the Create Row icon to create a new local password.
Click the Create Row icon to create a new local password.
You see the Create Local Passwords dialog box.
Step 4![]() (Optional) Check the switches that you want to configure the same local password on.
(Optional) Check the switches that you want to configure the same local password on.
Step 5![]() Select the switch WNN and fill in the Password field.
Select the switch WNN and fill in the Password field.
Step 6![]() Click Create to save the updated password.
Click Create to save the updated password.
About Password Configuration for Remote Devices
You can configure passwords in the local authentication database for other devices in a fabric. The other devices are identified by their device name, which is also known as the switch WWN or device WWN. The password is restricted to 64 characters and can be specified in clear text (0) or in encrypted text (7).

Note![]() The switch WWN identifies the physical switch. This WWN is used to authenticate the switch and is different from the VSAN node WWN.
The switch WWN identifies the physical switch. This WWN is used to authenticate the switch and is different from the VSAN node WWN.
Configuring DHCHAP Passwords for Remote Devices
To locally configure the remote DHCHAP password for another switch in the fabric, follow these steps:
About DHCHAP Timeout Value
During the DHCHAP protocol exchange, if the MDS switch does not receive the expected DHCHAP message within a specified time interval, authentication failure is assumed. The time ranges from 20 (no authentication is performed) to 1000 seconds. The default is 30 seconds.
When changing the timeout value, consider the following factors:
Configuring the DHCHAP Timeout Value
To configure the DHCHAP timeout value, follow these steps:
|
|
|
|
|---|---|---|
Configuring DHCHAP AAA Authentication
You can individually set authentication options. If authentication is not configured, local authentication is used by default.
To configure the AAA authentication refer to the Chapter4, “Configuring Security Features on an External AAA Server” Follow these steps:
Displaying Protocol Security Information
Use the show fcsp commands to display configurations for the local database (see Example 8-1 through 8-6 ).
Example 8-1 Displays DHCHAP Configurations in FC Interfaces
Example 8-2 Displays DHCHAP Statistics for an FC Interface
Example 8-3 Displays the FC-SP WWN of the Device Connected through a Specified Interface
Example 8-4 Displays Hash Algorithm and DHCHAP Groups Configured for the Local Switch
Example 8-5 Displays the DHCHAP Local Password Database
Example 8-6 Displays the ASCII Representation of the Device WWN

Tip![]() Use the ASCII representation of the device WWN (identified in bold in Example 8-6) to configure the switch information on RADIUS and TACACS+ servers.
Use the ASCII representation of the device WWN (identified in bold in Example 8-6) to configure the switch information on RADIUS and TACACS+ servers.
Sample Configuration
This section provides the steps to configure the example illustrated in Figure 8-2.
Figure 8-2 Sample DHCHAP Authentication
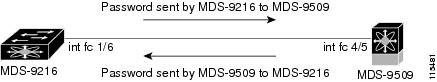
To configure the authentication setup shown in Figure 8-2, follow these steps:
Step 1![]() Obtain the device name of the MDS 9216 Switch in the fabric. The MDS 9216 Switch in the fabric is identified by the switch WWN.
Obtain the device name of the MDS 9216 Switch in the fabric. The MDS 9216 Switch in the fabric is identified by the switch WWN.
Step 2![]() Explicitly enable DHCHAP in this switch.
Explicitly enable DHCHAP in this switch.

Note![]() When you disable DHCHAP, all related configurations are automatically discarded.
When you disable DHCHAP, all related configurations are automatically discarded.
Step 3![]() Configure a clear text password for this switch. This password will be used by the connecting device.
Configure a clear text password for this switch. This password will be used by the connecting device.
Step 4![]() Configures a password for another switch in the fabric that is identified by the switch WWN device name.
Configures a password for another switch in the fabric that is identified by the switch WWN device name.
Step 5![]() Enable the DHCHAP mode for the required Fibre Channel interface.
Enable the DHCHAP mode for the required Fibre Channel interface.

Note![]() Whenever DHCHAP port mode is changed to a mode other than the Off mode, reauthentication is performed.
Whenever DHCHAP port mode is changed to a mode other than the Off mode, reauthentication is performed.
Step 6![]() Verify the protocol security information configured in this switch by displaying the DHCHAP local password database.
Verify the protocol security information configured in this switch by displaying the DHCHAP local password database.
Step 7![]() Display the DHCHAP configuration in the Fibre Channel interface.
Display the DHCHAP configuration in the Fibre Channel interface.
Step 8![]() Repeat these steps on the connecting MDS 9509 Switch.
Repeat these steps on the connecting MDS 9509 Switch.
You have now enabled and configured DHCHAP authentication for the sample setup in Figure 8-2.
Default Settings
Table 8-2 lists the default settings for all fabric security features in any switch.
|
|
|
|---|---|
A priority list of MD5 followed by SHA-1 for DHCHAP authentication |
|
 Feedback
Feedback