New Log4Shell Detections
We've added new threat detections to our portfolio, including these two types of detection related to the recently discovered Log4j vulnerability:
Malware Installation Through Log4Shell
This is a detection of the already successful Log4j exploitation. Log4j is a logging framework used by web applications. Its log4j2 library is vulnerable to remote code execution (RCE) through any protocol (TCP, HTTP). Once the attacker sends the malicious payload, it gets logged by the server and the vulnerability gets triggered. It leads the web server to connect to rogue infrastructure (T1583.004) through JNDI and inject a malicious Java class (T1620) file into a server process. The injected Java class starts the second stage of the attack and lets the attacker remotely execute code on the victim's server. Attackers use it to get full access to the victim's infrastructure and deploy additional malware and crypto-mining software, such as Mirai, Kinsing (S0599), and Tsunami.
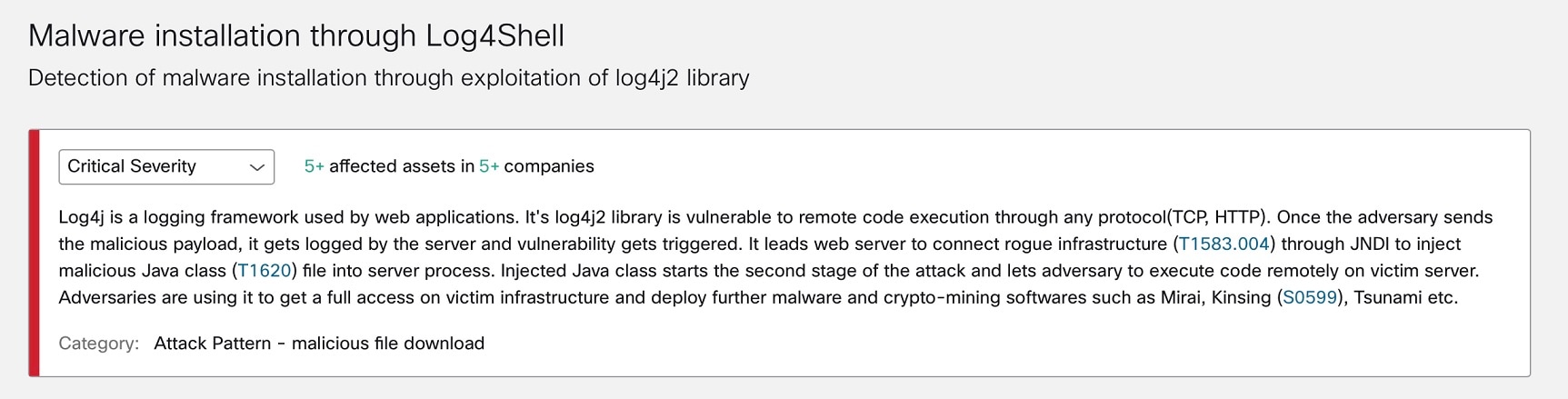
To see if Malware installation through Log4Shell has been detected in your environment, click Malware installation through Log4Shell to view its details in global threat alerts.
Log4Shell Vulnerability Scan
This is a detection of a device performing a scan of remote services (T1595.002) to identify and potentially exploit Log4Shell (CVE-2021-44228). The Log4Shell vulnerability in Apache Log4j, a popular Java logging framework, can lead to remote code execution (RCE) or disclosure of information. A triggered alert can indicate the presence of an unwanted application or malware performing the scan, as well as testing activities intended on penetration. To investigate, verify the associated anomalies against the intended behavior of the device.
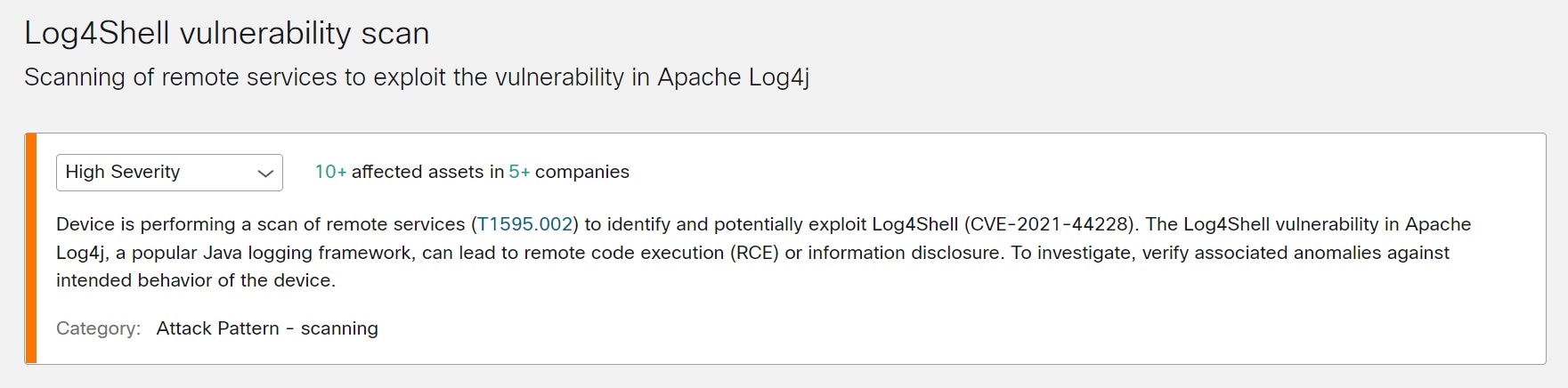
To see if Log4Shell vulnerability scan has been detected in your environment, click Log4Shell vulnerability scan to view its details in global threat alerts.

 Feedback
Feedback