Integrating Your Appliance with Cisco SecureX
Cisco SecureX is a security platform embedded with every Cisco security product. It is cloud-native with no new technology to deploy. Cisco SecureX simplifies the demands of threat protection by providing a platform that unifies visibility, enables automation, and strengthens your security across network, endpoints, cloud, and applications. By connecting technology in an integrated platform, Cisco SecureX delivers measurable insights, desirable outcomes, and unparalleled cross-team collaboration. Cisco SecureX enables you to expand your capabilities by connecting your security infrastructure.
Integrating the Appliance with Cisco SecureX contains the following sections:
You can integrate your appliance with Cisco SecureX, and perform the following actions in Cisco SecureX:
-
View and send the email data from multiple appliances in your organization.
-
Identify, investigate and remediate threats observed in the email reports, sender and target relationships, search for multiple email addresses and subject lines and message tracking.
-
Block compromised users or users violating outgoing email policies.
-
Resolve the identified threats rapidly and provide recommended actions to take against the identified threats.
-
Document the threats to save the investigation and enable collaboration of information among other devices.
-
Block malicious domains, track suspicious observances, initiate an approval workflow or to create an IT ticket to update email policy.
You can access Cisco SecureX using the following URL:
https://securex.us.security.cisco.com/login
Cisco Security Management Appliance (SMA) centralizes management and reporting functions across multiple Cisco email security appliances. For more information on observables that can be enriched by the SMA Email module, see https://securex.us.security.cisco.com/help/module-sma.
How to Integrate Your Appliance with Cisco SecureX
|
Do This |
More Info |
|
|---|---|---|
|
Step 1 |
Review the prerequisites. |
|
|
Step 2 |
On your Security Management appliance, enable the Cisco SecureX integration. |
Enable the SecureX integration on your Security Management Appliance |
|
Step 3 |
On Cisco SecureX, add your appliance as a device, register it, and generate a registration token. |
See Configure Security Services Exchange topic on https://securex.us.security.cisco.com/help/module-sma. |
|
Step 4 |
On your Security Management appliance, complete the Cisco SecureX registration. |
Register Cisco SecureX on your Security Management Appliance |
|
Step 5 |
Confirm whether the registration was successful. |
|
|
Step 6 |
On Cisco SecureX, add SMA Email Module. |
See Add SMA Email Module topic on https://securex.us.security.cisco.com/help/module-sma. |
Prerequisites
-
Make sure that you create a user account in Cisco SecureX with admin access rights. To create a new user account, go to Cisco SecureX login page using the URL https://securex.us.security.cisco.com/login and click Create a SecureX Sign-on Account in the login page. If you are unable to create a new user account, contact Cisco TAC for assistance.
-
[Only if you are not using a proxy server .] Make sure that you open HTTPS (In and Out) 443 port on the firewall for the following FQDNs to register your appliance with Cisco SecureX:
-
api-sse.cisco.com (applicable for NAM users only)
-
api.eu.sse.itd.cisco.com (applicable for European Union (EU) users only)
-
api.apj.sse.itd.cisco.com (applicable for APJC users only)
-
est.sco.cisco.com (applicable for APJC, EU, and NAM users)
For more information, see Firewall Information.
-
Enable the Cisco SecureX Integration on your Security Management Appliance
Procedure
| Step 1 |
Log in to your appliance. |
| Step 2 |
Select Networks > Cloud Service Settings. |
| Step 3 |
Click Edit Settings. |
| Step 4 |
Check the Enable check box. |
| Step 5 |
Choose the required Cisco SecureX server to connect your appliance to Cisco SecureX. |
| Step 6 |
Submit and commit your changes. |
| Step 7 |
Wait for few minutes, and check whether the Register button appears on your appliance. |
 Note |
To enable this integration using the CLI, use the threatresponseconfig command.
|
What to do next
Register your appliance on Cisco SecureX. For more information, see Configure Security Services Exchange topic on https://securex.us.security.cisco.com/help/module-sma.
Register Cisco SecureX on Your Security Management Appliance
Procedure
| Step 1 |
Go to Networks > Cloud Service Settings. |
| Step 2 |
In Cloud Services Settings, enter the registration token, and click Register. |
 Note |
To register Cisco SecureX using the CLI, use the cloudserviceconfig command.
|
What to do next
Confirm Whether the Registration was Successful
-
On Security Services Exchange, confirm successful registration by reviewing the status in Security Services Exchange.
-
On Cisco SecureX, navigate to the Devices page and view the SMA that has been registered with Security Services Exchange.
 Note |
If you want to switch to another Cisco SecureX server (for example, 'Europe - api.eu.sse.itd.cisco.com'), you must first deregister your appliance from Cisco SecureX and follow steps mentioned in How to Integrate Your Appliance with Cisco SecureX. After you have integrated your appliance with Cisco SecureX, you do not need to integrate your Email Security appliance with Cisco SecureX because the email and web reporting features are centralized. After successful registration of your appliance on Security Services Excange, add the SMA Email module on Cisco SecureX. For more information, see Add SMA Email Module topic on https://securex.us.security.cisco.com/help/module-sma. |
Performing Threat Analysis using Cisco SecureX Ribbon
 Note |
When you upgrade from Security Management Appliance 13.6.1 or earlier versions, Casebook will be part of the Cisco SecureX Ribbon. |
Cisco SecureX supports a distributed set of capabilities that unify visibility, enable automation, accelerate incident response workflows, and improve threat hunting. These distributed capabilities are presented in the form of applications (apps) and tools in the Cisco SecureX Ribbon.
This topic contains the following sections:
You will find the Cisco SecureX Ribbon at the bottom pane of the page, and it persists as you move between the dashboard and other security products in your environment. Cisco SecureX Ribbon consists of the following icons and elements:
-
Expand/Collapse Ribbon
-
Home
-
Casebook App
-
Incidents App
-
Orbital App
-
Enrichment Search Box
-
Find Observables
-
Settings
For more information on Cisco SecureX Ribbon, see https://securex.us.security.cisco.com/help/ribbon.
Accessing the Cisco SecureX Ribbon
Before you begin
 Note |
If you have already configured Casebook for Security Management Appliance 13.6.1 or earlier versions, you need not create a Client ID and Client Secret in Cisco Threat Response API client. You will be automatically logged into Cisco SecureX Ribbon. |
You can drag the Cisco SecureX Ribbon, positioned at the bottom pane of the page, from right using  button.
button.
Procedure
| Step 1 |
Log in to the new web interface of your appliance. For more information, see Accessing the Web Interface. |
||
| Step 2 |
Click the Cisco SecureX Ribbon. |
||
| Step 3 |
Create a Client ID and Client Secret in Threat Response API Client. For more information to generate API Client credentials, see Creating an API Client. While creating a client ID and client password, make sure that you choose the following scopes:
|
||
| Step 4 |
Enter the client ID and client password obtained in Step 3 in the Login to use SecureX Ribbon dialog box in your appliance. |
||
| Step 5 |
Select the required Cisco SecureX server in the Login to use SecureX Ribbon dialog box. |
||
| Step 6 |
Click Authenticate.
|
What to do next
Adding Observable to Casebook for Threat Analysis
Before you begin
Make sure that you obtain the client ID and client password to access the casebook and pivot menu widgets on your appliance. For more information, see Accessing the Cisco SecureX Ribbon.
Procedure
| Step 1 |
Log in to the new web interface of your appliance. For more information, see Accessing the Web Interface. |
||
| Step 2 |
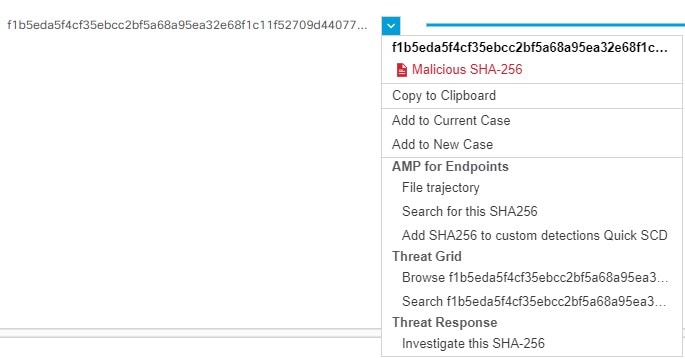
Navigate to the Email Reporting or Web Reporting page, click the pivot menu 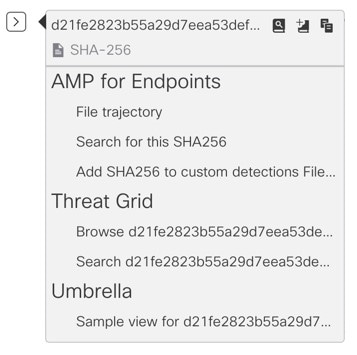 Perform the following:
|
||
| Step 3 |
Hover over |
||
| Step 4 |
(Optional) Click |
 Note |
You can search for observables for threat analysis in two different ways: |
-
Click the Enrichment
 search box from the Cisco SecureX Ribbon and search for the observables.
search box from the Cisco SecureX Ribbon and search for the observables.
-
Click the Casebook icon inside the Cisco SecureX Ribbon and search for the observables in the search
 field.
field.
For more information on Cisco SecureX Ribbon, see https://securex.us.security.cisco.com/help/ribbon.
 button next to the required observable (for example, bit.ly).
button next to the required observable (for example, bit.ly).
 button to add an observable to active case.
button to add an observable to active case.
 button to add the observable to new case.
button to add the observable to new case.
 icon and click
icon and click  button to open the
button to open the  button to add a title, description, or notes to the
button to add a title, description, or notes to the  button.
button.
 Feedback
Feedback