About Snort 3 Inspection
The Snort Intrusion Prevention System (IPS) analyzes network traffic in real time to provide deep packet inspection. Snort can detect and block traffic anomalies, and network probes and attacks. Snort 3 is the latest version of Snort. For more information, see https://snort.org/snort3.
Snort is designed for high performance and scalability. Snort includes a set of configurable plugins called inspectors. A Snort inspector can detect and analyze traffic for a certain type of network protocol or probe, normalize messages to enhance packet analysis, and inspect specific types of files embedded in a message. You configure the Snort inspectors in a Network Analysis Policy (NAP) and enable intrusion rules in an Intrusion policy.
Access Control Policies
Access control policies process traffic in several stages. The following diagram represents an example of a policy deployment. The elements addressed in this document are the Snort 3 inspectors and rule options used in intrusion rules, both highlighted in blue.
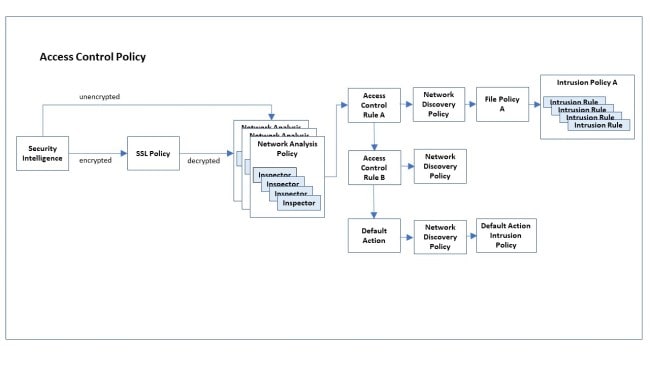
Network analysis policies enable you to configure Snort 3 inspectors to determine the traffic protocol and extract and normalize data. You can configure multiple network analysis policies, each using a uniquely configured collection of Snort 3 inspectors to normalize the data. Inspectors can alert when they detect irregularities in the data stream, but their main purpose is to prepare the data for the intrusion rules. The intrusion policies apply their configured intrusion rules to examine the data for signs of evasions, intrusions, or attacks.
Within a network analysis policy, you can customize inspection behavior for data using a
given protocol by setting configuration parameters specific to the inspector that
handles that protocol. For example, to configure inspection behavior for POP data, set
the configuration parameters for the pop inspector.
You can also customize the intrusion policy for some protocols by writing custom intrusion rules using rule options specific to those protocols.
If you establish a complex configuration using multiple network analysis policies and multiple intrusion policies, the system first chooses the network analysis policy to handle the data. After the network analysis policy has applied the appropriate inspectors to perform its analysis, the data does not automatically get handed off to the corresponding intrusion policy for that protocol. The access control policy performs additional tests to determine which intrusion policy gets the data. For this reason, when configuring your access control, network analysis, and intrusion policies, ensure that data is analyzed by the correct network analysis and intrusion policy pair. For more information, see the Cisco Secure Firewall Management Center Snort 3 Configuration Guide.
Intrusion Rule Updates
Cisco periodically issues intrusion rule updates in the form of Lightweight Security Packages (LSPs). These updates may change the default values of a Snort 3 inspector's configuration parameters and intrusion rule options.
Inspector Configuration
You can enable and disable Snort inspectors as well as view and change their configurations through the Secure Firewall Management Center web interface. The Secure Firewall Management Center web interface uses the JSON format to describe the inspector configurations. For more information, see the Cisco Secure Firewall Management Center Snort 3 Configuration Guide.
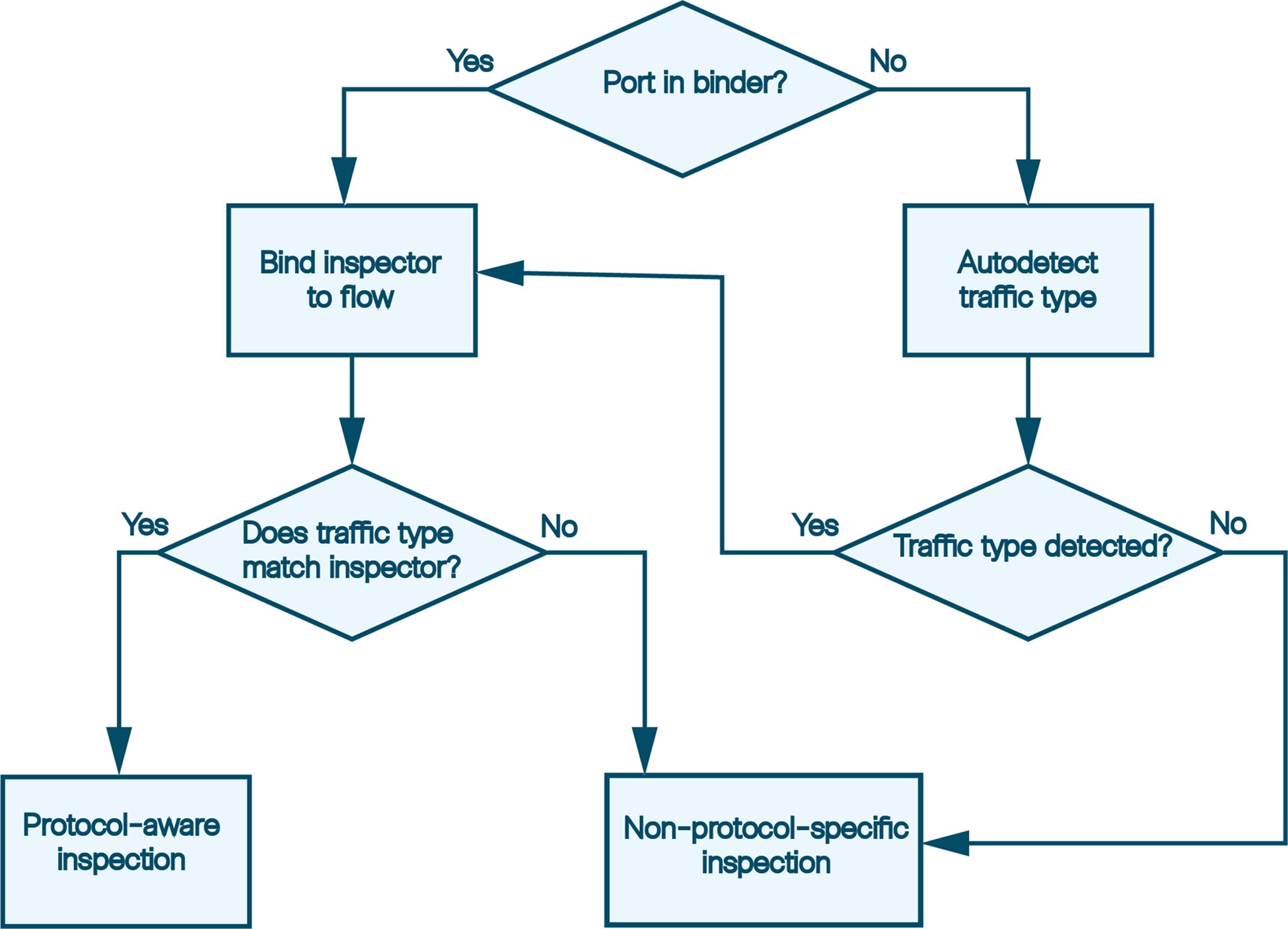
To use an inspector, you must enable it through the management center web interface. In addition, for service inspectors, you must configure an entry
for the service inspector in the binder inspector. For more information,
see Binder Inspector Overview.
The Snort 3 Inspector Reference reflects the default settings for Snort 3 inspector parameters and built-in intrusion rule options. Your system may use different defaults depending upon LSP updates, or the base network access policies provided with the system. To get the most accurate understanding of inspector settings for your network access policies, view the settings in the management center web interface.

 Feedback
Feedback