- Preface
- Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 Migration Overview
- Understanding the Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 Migration Tool
- Installing the Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 Migration Tool
- Using the Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 Migration Utility
- Installing the Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 Migration Tool
- Cisco Secure ACS 5.1/5.2 and Cisco ISE 1.0 Data Object Mapping
- Troubleshooting the Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 Migration Tool
- Glossary
Cisco Identity Services Engine Migration Guide for Cisco Secure ACS 5.1 and 5.2, Release 1.0
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- May 17, 2011
Chapter: Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 Migration Overview
Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 Migration Overview
This chapter provides a brief overview of Cisco Identity Services Engine (ISE) and Cisco Secure Access Control System (ACS). The following topics are discussed in this chapter:
Overview
The Cisco ISE deployment model consists of one primary node with multiple secondary nodes. Each Cisco ISE node in a deployment can take any one or more of the following personas: Administration, Policy Service, and Monitoring.
After you install Cisco ISE, all the nodes will be in the standalone state. You must define one of your Cisco ISE nodes to be the primary (running as an Administration persona). After you have defined the primary node, you can configure other Cisco ISE node personas such as Policy Service and Monitoring for the network. You can then register other secondary nodes with the primary node and define specific roles for each of them.
When you register an Cisco ISE node as a secondary node, Cisco ISE immediately creates a database link from the primary to the secondary node and begins the process of replication. All configuration changes are made on the primary Administration ISE node and are replicated to the secondary nodes. The Monitoring ISE node acts as the log collector.
Cisco Secure Access Control System (ACS) deployment model consists of a single primary and multiple secondary Cisco Secure ACS servers, where configuration changes are made on the primary Cisco Secure ACS server. These configurations are replicated to the secondary Cisco Secure ACS servers.
All primary and secondary Cisco Secure ACS servers can process AAA requests. The primary Cisco Secure ACS server is also the default log collector for the Monitoring and Report Viewer, although you can configure any Cisco Secure ACS server to be the log collector.
Cisco Secure ACS and Cisco ISE may exist on different hardware platforms and have different operating system, database, and information model. Therefore, you cannot perform a standard upgrade from Cisco Secure ACS to Cisco ISE.
Instead, a migration tool and procedure is available that reads the data from Cisco Secure ACS and creates corresponding data in Cisco ISE. You can also use this migration procedure in cases where Cisco Secure ACS and Cisco ISE use the same hardware; the CSACS-1121 appliance. The Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 migration process requires minimum user interaction and the full set of configuration data is migrated from Cisco Secure ACS to Cisco ISE.
Supported Migration from Cisco Secure ACS to Cisco ISE
Cisco ISE supports data migration from Cisco Secure ACS 5.1 and 5.2 using the Cisco Secure ACS-ISE 1.0 Migration Tool. If you are running Cisco Secure ACS 3.x or Cisco Secure ACS 4.x, you must first upgrade to Cisco Secure ACS 5.0.
After you reach the Cisco Secure ACS 5.0 level, you can then upgrade to Cisco Secure ACS 5.1 or 5.2. At this point, you can then migrate to Cisco ISE 1.0 using the Cisco Secure ACS-ISE 1.0 Migration Tool.

Note![]() A direct upgrade is available from Cisco Secure ACS 5.0 to Cisco Secure ACS 5.1/5.2. You must first complete upgrading all previous Cisco Secure ACS releases to Cisco Secure ACS 5.1/5.2 before you attempt to migrate any Cisco Secure ACS data to Cisco ISE.
A direct upgrade is available from Cisco Secure ACS 5.0 to Cisco Secure ACS 5.1/5.2. You must first complete upgrading all previous Cisco Secure ACS releases to Cisco Secure ACS 5.1/5.2 before you attempt to migrate any Cisco Secure ACS data to Cisco ISE.
For information on migrating data from Cisco Secure ACS 3.x or 4.x to Cisco Secure ACS 5.0, see Migrating Data from Cisco Secure ACS 3.x and 4.x to ACS 5.1/5.2 .
Software Requirements
The Cisco ACS 5.1/5.2-ISE 1.0 Migration Tool runs on a Windows machine. The machine should have JAVA installed on it.
The minimum disk space required is 512 megabytes (MB). This space is required not only for the installation of the migration tool, but also because the migration tool will store the migrated data and will generate reports and logs.
The minimum RAM required is 1 GB. If you have about 300,000 users, 50,000 hosts, 50,000 network devices, then we recommend that you have a minimum of 2 GB RAM.
Before running the Cisco ACS 5.1/5.2-ISE 1.0 Migration Tool, make sure that you have installed the latest patches for ACS 5.1 and 5.2.
Functional Description
The migration tool is responsible for transferring Cisco Secure ACS data into Cisco ISE and there are three major steps:
1.![]() Export data from Cisco Secure ACS.
Export data from Cisco Secure ACS.
2.![]() Persist data in the migration tool.
Persist data in the migration tool.
3.![]() Import data into Cisco ISE 1.0.
Import data into Cisco ISE 1.0.
The following are the major features of the Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 migration process:
Export
The first stage in the migration process is to export ACS data using the Cisco Secure ACS Programmatic Interface (PI). You have to provide the credentials to connect with Cisco Secure ACS and request to export Cisco Secure ACS data into the migration application. During this time the exported data must be validated to verify if it can be imported into a Cisco ISE 1.0 appliance successfully. In cases where the data is invalid, this status is logged in the migration report.
Data Persistency
Cisco ISE does not support an upgrade from Cisco Secure ACS to Cisco ISE 1.0. Therefore, if you want to upgrade your Cisco Secure ACS appliance to Cisco ISE, you have to uninstall Cisco Secure ACS and reimage the appliance with the Cisco ISE 1.0 image. The migration tool persists Cisco Secure ACS data before the reimage takes place and before the next stage (import) begins. The persisted data is in an encrypted format.
Import
At the import stage, the migration tool contains information from Cisco Secure ACS and is ready to import the data into Cisco ISE 1.0. At this point, you have to reimage the Cisco Secure ACS machine with the Cisco ISE 1.0 image and start the import operation. You can view the import progress through the Cisco ACS 5.1/5.2-ISE 1.0 Migration Tool user interface. You can see the object types that are being transferred and how many objects are pending for delivery. Any errors during this process are logged in the migration report.
Scalability
The migration application supports object scale as described in Table 1-1 .
|
|
|
|
|
|---|---|---|---|
DACLs3 (each contain 1,600 entries) |
|||
|
1.AD is an acronym for Active Directory (see AD in the ). 2.LDAP is an acronym for Lightweight Directory Access Protocol (see LDAP in the ). 3.DACL is an acronym downloadable access control list (see DACLin the ). |
High Availability
The Cisco ACS 5.1/5.2-ISE 1.0 Migration Tool maintains the state at each stage of the import or export operation. This means that if the process of importing or exporting fails at any point, you need not start from the beginning, but from the last checkpoint before the failure occurred.
If the migration process fails during the import or export phase, the migration tool terminates the process. If you restart the migration tool after a failure, a dialog box is displayed.
You can either choose to resume the previous import/export or discard the previous process and start a new migration process. If you choose to resume the previous process, the migration process resumes from the last object type. Resuming from a failure also resumes the report to run from the previous process.
Reporting
Two Cisco ISE reports are available while migrating Cisco Secure ACS 5.1/5.2 data to the Cisco ISE appliance using the Cisco Secure ACS 5.1/5.2-ISE 1.0 Migration Tool. The two types of reports (export and import) indicate specific information or errors that are encountered during the export of data from the Cisco Secure ACS database or during the import of data into the Cisco ISE appliance.
The export report includes error information for objects that are exported but will not be imported. It contains a data analysis section at the end of the report, which describes the functional gap analysis in the data between Cisco Secure ACS and Cisco ISE.
Table 1-2 describes the report type, the message type, and message contents in these import or export reports.
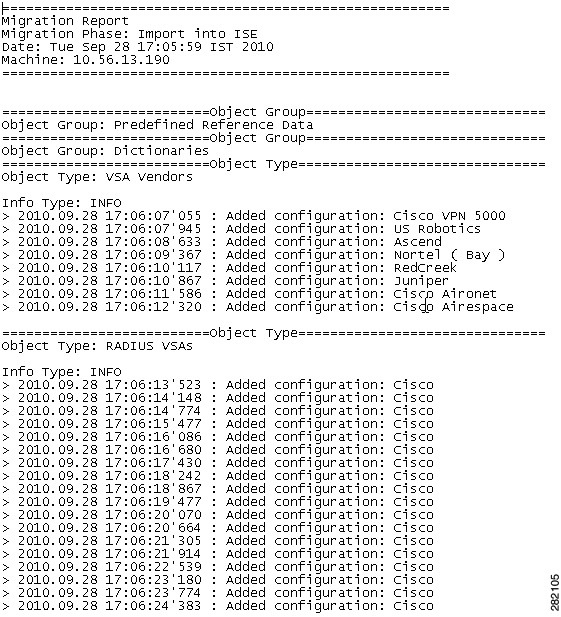
Figure 1-1 and Figure 1-2 are examples of the export and import reports, respectively.
Figure 1-1 Example of Export Report
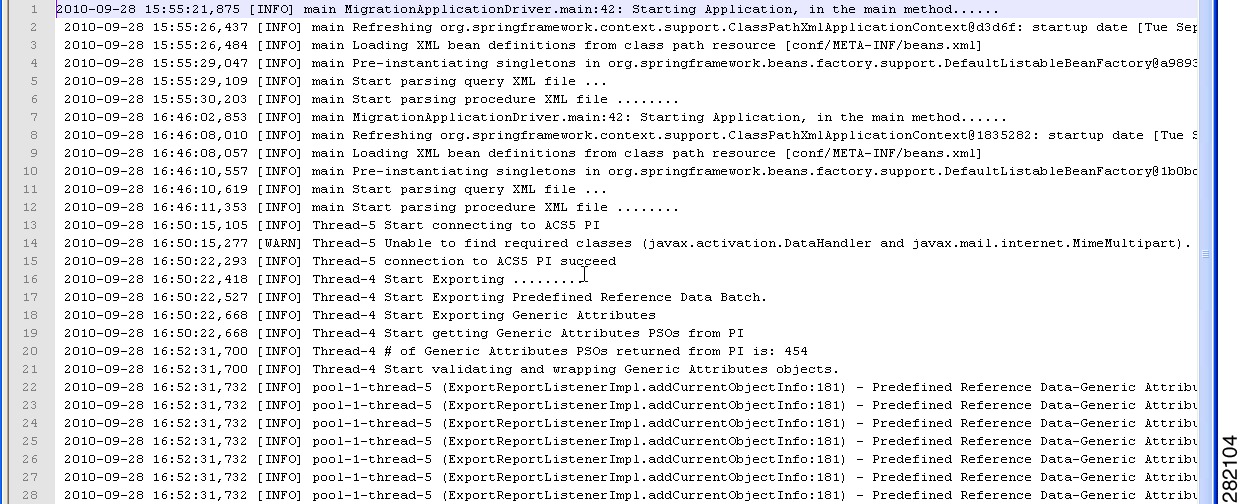
Figure 1-2 Example of Import Report
Migration Considerations
The only currently supported browser for downloading the migration tool files is Firefox version 3.6.x. Microsoft Windows Internet Explorer (IE8 and IE7) browsers are not currently supported in this release.
 Feedback
Feedback