- Preface
- Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 Migration Overview
- Understanding the Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 Migration Tool
- Installing the Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 Migration Tool
- Using the Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 Migration Utility
- Installing the Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 Migration Tool
- Cisco Secure ACS 5.1/5.2 and Cisco ISE 1.0 Data Object Mapping
- Troubleshooting the Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 Migration Tool
- Glossary
Cisco Identity Services Engine Migration Guide for Cisco Secure ACS 5.1 and 5.2, Release 1.0
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- May 17, 2011
Chapter: Understanding the Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 Migration Tool
Understanding the Cisco ACS 5.1/5.2-ISE 1.0 Migration Tool
This chapter provides information about the Cisco ACS 5.1/5.2-ISE 1.0 Migration Tool that is used to migrate data from a Cisco Secure ACS 5.1/5.2 database to Cisco ISE Release 1.0 appliance. The following topics describe what you should know about the Cisco ACS 5.1/5.2-ISE 1.0 Migration Tool before using it to migrate data:
Overview: Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0
The Cisco ACS 5.1/5.2-ISE 1.0 Migration Tool is designed to provide users that have existing installed Cisco Secure ACS 5.1/5.2 database with a method for transporting that data to a Cisco ISE 1.0 appliance. The design of the tool addresses the inherent migration problems that result from differences in the underlying hardware platforms and systems, databases, and data schemes. The three steps in the migration process using the Cisco ACS 5.1/5.2-ISE 1.0 Migration Tool include:
- Exporting the Cisco Secure ACS 5.1/5.2 data from its database
- Persisting this data using the migration tool
- Importing the persisted data into the Cisco ISE 1.0 appliance
The Cisco ACS 5.1/5.2-ISE 1.0 Migration Tool supports the migration of only Cisco Secure ACS Release 5.1/5.2 data to a Cisco ISE 1.0 appliance, which requires a three-step process. For example, you can use the Cisco ACS 5.1/5.2-ISE 1.0 Migration Tool to perform the following data migration steps:
1.![]() Export the Cisco Secure ACS 5.1/5.2 data from the Cisco Secure ACS-1121 hardware appliance to a secure external server with a database.
Export the Cisco Secure ACS 5.1/5.2 data from the Cisco Secure ACS-1121 hardware appliance to a secure external server with a database.
2.![]() Reimage the Cisco Secure ACS-1121 hardware appliance, which is the same physical hardware as the Cisco ISE 3315 appliance, with the Cisco ISE 1.0 software.
Reimage the Cisco Secure ACS-1121 hardware appliance, which is the same physical hardware as the Cisco ISE 3315 appliance, with the Cisco ISE 1.0 software.
3.![]() Import the converted Cisco Secure ACS Release 5.1/5.2 data from the secure external server into the Cisco ISE 1.0 appliance.
Import the converted Cisco Secure ACS Release 5.1/5.2 data from the secure external server into the Cisco ISE 1.0 appliance.
The only supported direct migration process using the Cisco ACS 5.1/5.2-ISE 1.0 Migration Tool is from a Cisco Secure ACS Release 5.1/5.2 system to a Cisco ISE 1.0 appliance. However, you upgrade earlier versions of Cisco Secure ACS data to a Cisco Secure ACS 5.1/5.2 state by using the options listed in Table 2-1 .
The Cisco Secure ACS 5.1/5.2-ISE 1.0 Migration Tool migrates data from a Cisco Secure ACS 5.1/5.2 system to a Cisco ISE 1.0 appliance, which is a different process from an upgrade used for earlier versions of Cisco Secure ACS Release 3.x to 4.x.
|
|
|
|
|---|---|---|

Note![]() For information and documentation links about migrating Cisco Secure ACS Release 3.x and 4.x to 5.0 to Cisco Secure ACS 5.1/5.2, see Chapter5, “Migrating Data from Cisco Secure ACS 3.x and 4.x to ACS 5.1/5.2” Chapter 5 also provides information and documentation links about migrating Cisco Secure ACS 5.0 to Cisco Secure ACS 5.1/5.2.
For information and documentation links about migrating Cisco Secure ACS Release 3.x and 4.x to 5.0 to Cisco Secure ACS 5.1/5.2, see Chapter5, “Migrating Data from Cisco Secure ACS 3.x and 4.x to ACS 5.1/5.2” Chapter 5 also provides information and documentation links about migrating Cisco Secure ACS 5.0 to Cisco Secure ACS 5.1/5.2.
Cisco Secure ACS 5.1/5.2-ISE 1.0 Migration Tool
The Cisco Secure ACS 5.1/5.2-ISE 1.0 Migration Tool runs on Windows-based systems, and it works by importing the Cisco Secure ACS data files, analyzing the data, and making required data modifications necessary for importing the data into a format usable by the Cisco ISE 1.0 system.
The Cisco Secure ACS 5.1/5.2 and Cisco ISE 1.0 applications may or may not run on the same type physical hardware. So the Cisco Secure ACS 5.1/5.2-ISE 1.0 Migration Tool uses the Cisco Secure ACS Programmatic Interface (PI) and the Cisco ISE representational state transfer (REST) application programming interfaces (APIs). The Cisco Secure ACS PI and the Cisco ISE REST APIs allow the Cisco Secure ACS and ISE applications to run on any of the supported hardware platforms or VMware servers.
Because the Cisco Secure ACS is considered a closed appliance, running the migration tool directly on the Cisco Secure ACS-1121 appliance is not permitted. Instead the Cisco Secure ACS PI reads and returns the ACS configuration data in a normalized form. The Cisco ISE REST APIs perform validation and normalize the exported Cisco Secure ACS data to persist it in a form usable by Cisco ISE software.
Figure 2-1 explains the deployment scenario when Cisco Secure ACS and Cisco ISE are installed on different appliances (dual-appliance deployment).
Figure 2-1 Cisco Secure ACS and Cisco ISE Installed on Different Appliances
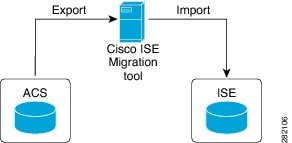
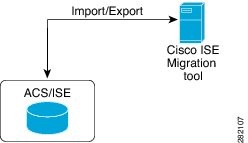
Figure 2-2 shows the deployment scenario when Cisco Secure ACS is installed on the same appliance upon which the Cisco ISE software will be installed (single-appliance deployment). In a single-appliance deployment, complete the following steps:
Step 1![]() Install the Cisco ACS 5.1/5.2-ISE 1.0 Migration Tool on a standalone Windows machine.
Install the Cisco ACS 5.1/5.2-ISE 1.0 Migration Tool on a standalone Windows machine.
Step 2![]() Export the Cisco Secure ACS 5.1/5.2 data from the Cisco Secure ACS appliance.
Export the Cisco Secure ACS 5.1/5.2 data from the Cisco Secure ACS appliance.
Step 3![]() Reimage the appliance with the Cisco ISE 1.0 software.
Reimage the appliance with the Cisco ISE 1.0 software.
Step 4![]() Import the Cisco Secure ACS 5.1/5.2 data into the Cisco ISE 1.0 appliance.
Import the Cisco Secure ACS 5.1/5.2 data into the Cisco ISE 1.0 appliance.

Note![]() When you are ready to start migrating Cisco Secure ACS 5.1/5.2 data to a Cisco ISE appliance, make sure that it is to a standalone Cisco ISE node. Only after migration has been successfully completed should you begin the any deployment configuration (such as setting up Administrator ISE and Policy Service ISE personas). It is a requirement that the migration import phase be performed on a “clean” new installation of the Cisco ISE software on a supported hardware appliance.
When you are ready to start migrating Cisco Secure ACS 5.1/5.2 data to a Cisco ISE appliance, make sure that it is to a standalone Cisco ISE node. Only after migration has been successfully completed should you begin the any deployment configuration (such as setting up Administrator ISE and Policy Service ISE personas). It is a requirement that the migration import phase be performed on a “clean” new installation of the Cisco ISE software on a supported hardware appliance.
Figure 2-2 Cisco Secure ACS and Cisco ISE Installed on a Single Appliance
Migration Tool Components
The migration application consists of the following components:
Data Configuration
A minimal set of configuration data is needed as input at the beginning of the migration process and the application then proceeds to migrate the full set of configuration items. You must enter the IP address (or hostname) of the primary Cisco Secure ACS server and the Cisco ISE server, along with the administrator credentials. After you have been authenticated, the Cisco Secure ACS 5.1/5.2-ISE 1.0 Migration Tool proceeds to migrate the full set of configured data items in a form similar to an upgrade.
Usually no additional operator intervention is required after the migration process starts. However, as the migration progresses, some data may not be mapped automatically between the two applications. The administrator handling the migration is notified of this type of data, which must be resolved before the migration is complete.
Status Reporting
As the migration proceeds, you can monitor the real-time migration status along with the progress of that activity. In case of troubleshooting, detailed logs are available and accessible within the migration tool.
Export and Import
You can perform import and export operations as discrete operations or in sequence. These steps may take a long time, depending upon the amount of data being migrated. So the migration tool periodically displays the checkpoints with the status of the activity being performed. These checkpoints allow you to restart the migration process from the checkpoint in case of any failure.
The export component is active during the migration phase when Cisco Secure ACS data is exported from the Cisco Secure ACS 5.1/5.2 database using the Cisco Secure ACS PI. You can start the export process after you connect with the Cisco Secure ACS system, request that data be exported, and are authenticated.
A direct upgrade from Cisco Secure ACS to Cisco ISE is not supported. The Cisco Secure ACS 5.1/5.2-ISE 1.0 Migration Tool assists you if you want to uninstall the Cisco Secure ACS5.1/5.2 software and reimage the physical hardware with the Cisco ISE 1.0 software. The migration tool persists the Cisco Secure ACS data while the reimage process is completing and before the import stage begins.
During the export phase, Cisco Secure ACS 5.1/5.2-ISE 1.0 Migration Tool reads and analyzes the data from the Cisco Secure ACS to confirm that it can be created correspondingly on the Cisco ISE appliance. The tool reports any issue with the data, which may require administrator intervention at the end of the export phase.
Data Items Migrated
All Cisco Secure ACS configuration data that is applicable to Cisco ISE is migrated. However, Cisco Secure ACS 5.1/5.2-ISE 1.0 Migration Tool performs an analysis to check the data to be migrated and filter out the unsupported data types. The objects for Security Group Access are also considered for migration.
The following factors are considered when the priority is assessed. A weight of 1-3 is assigned, except for the Required for Policy factor, which has a dominant weight of up to 5.
- Required for Policy—The prime objective of the migration tool is to migrate effortlessly the Cisco Secure ACS 5.1/5.2 operational policies to Cisco ISE 1.0. The policy may involve many types of configuration items. For example, identity stores contain attributes that may be used in policy, and likewise, network devices related to Network Device Groups may also be used similarly. The policy affects and defines the order of object migration. The items on which policy is dependent must be migrated before the policy itself.
- Data Set Size— The number of each type of data item is also considered. There may be thousands of users or devices which you cannot recreate manually. Alternatively, there are some objects of which there is only a single instance, such as global protocol settings or the default device.
- Manual Migration Complexity— This factor indicates how difficult it is to migrate the data manually. Configuration data with a small number of parameters would be easy to recreate manually, but complex data sets or data difficult to configure will be much harder to recreate.
There is also an Applicability weighting. This weighting is a boolean value of either 0 or 1 to exclude data that is not applicable to the Cisco ISE product.
Some items related to the Security Group Access are also migrated. This solution has a very limited deployment, so priority for migration of these items is reduced by giving a low weightage for Data Set Size.
For a complete list of data objects that are migrated and data information mapping that takes place during export, see Appendix A, “Cisco Secure ACS 5.1/5.2 and Cisco ISE 1.0 Data Structure Mapping” .
Data Structure Mapping
Data structure mapping from Cisco Secure ACS 5.1/5.2 to Cisco ISE 1.0 is the process by which each of the data objects are analyzed and validated during the export phase by the Cisco Secure ACS 5.1/5.2-ISE 1.0 Migration Tool. For a complete list of the data information mapping that takes place during export, see the table in Appendix A, “Cisco Secure ACS 5.1/5.2 and Cisco ISE 1.0 Data Structure Mapping” .
 Feedback
Feedback