Supported Versions
|
FTD Device Package Version |
Platform |
FTD/FMC Version |
ACI/APIC Version |
|---|---|---|---|
|
1.0.3 |
Firepower-93xx |
6.2.3 |
2.3(1f) 3.0(1k) 3.2(1l) |
|
1.0.3 |
Firepower-41xx |
6.2.3 |
2.3(1f) 3.0(1k) 3.2(1l) |
|
1.0.3 |
Firepower-21xx |
6.2.3 |
2.3(1f) 3.0(1k) 3.2(1l) |
|
1.0.3 |
vFTD |
6.2.3 |
2.3(1f) 3.0(1k) 3.2(1l) |
Import the Device Package
Sign in on Cisco.com to download and install the device package software. For instructions, see the Cisco FTD for ACI Quick Start Guide.
New Features in Version 1.0(3)
-
IPv4 static route support
-
FTD clustering support
-
Ether-channel sub-interface support
IPv4 Static Route Support
The following fields are supported:
-
network (required)
-
gateway (required)
-
metric (optional)
-
isTunneled (optional)
 Note |
The SLA monitor option is not supported |
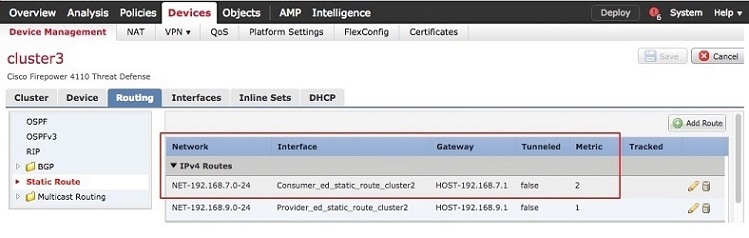
Example of an IPv4 static route configured on the APIC:
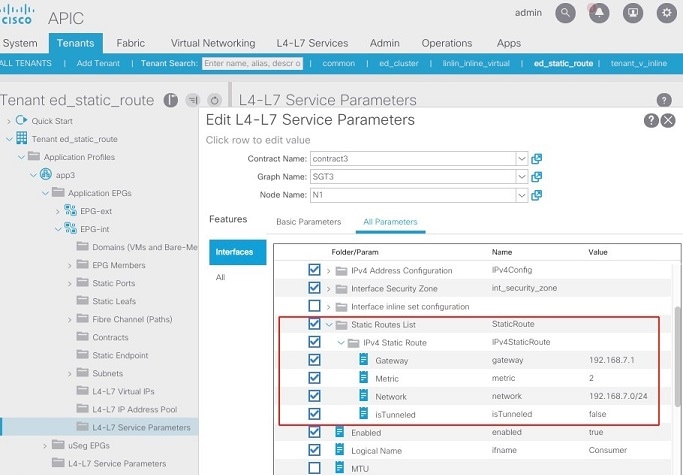
Example of the IPv4 static route pushed to the FMC by the FTD-DP:
FTD Clustering Support
FTD cluster must be pre-configured on the FMC. For example:
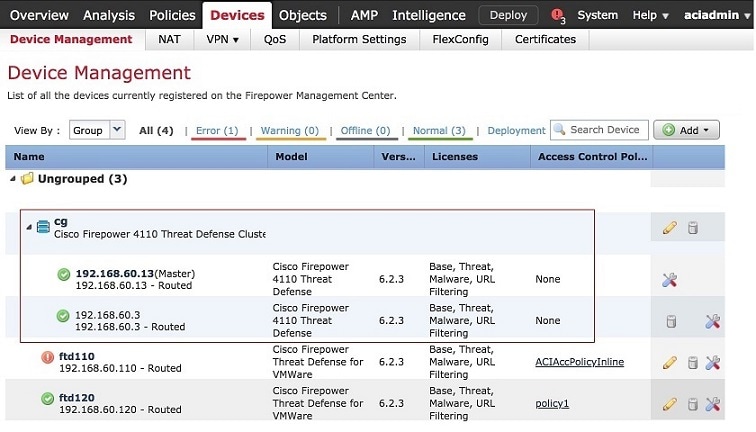
Register the FTD cluster on the APIC. For example:
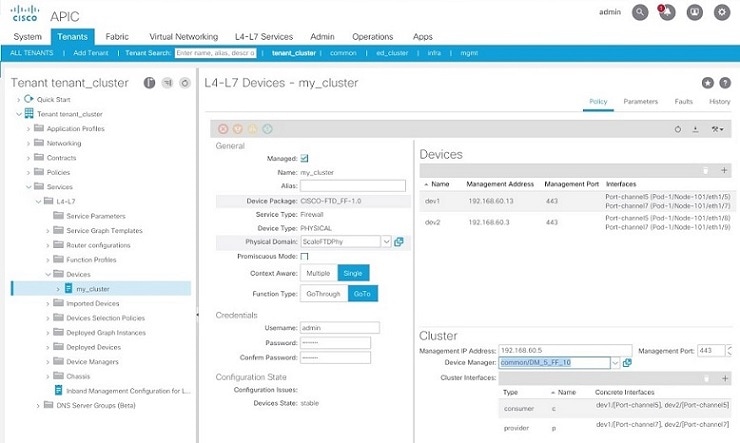
The logical cluster device is used the same way as a normal single device in the APIC.
When a serviceAudit is triggered on the APIC, such as Re-Query for Device Validation, or when a configuration is changed, such as the IP address of the externalInterface of the service graph, which causes a serviceModify, the FTD-DP can use the new FMC etherchannel REST API to push the corresponding configuration to the FMC, and ensure the changes are automatically deployed to the FTD cluster.
Existing Features From Version 1.0(2)
-
Virtual FTD VLAN trunking support
-
FTD High Availability (HA) support
-
Dynamic EPG update
-
Firepower 21xx support
-
Performance enhancements (FTD-DP scalability)
Existing Features From Version 1.0(1)
-
Create interface configuration for FTD
-
Configure enabled
-
Configure logical name
-
Configure MTU
-
Configure security zone
-
Configure inline set
-
Configure static IPv4 addresses
-
-
Create new bridge group interface for Transparent mode
-
Configure bridge group ID
-
Configure static IPv4 addresses
-
Configure interface reference
-
-
Create new inline set
-
Configure snort fail open down
-
Configure snort fail open busy
-
Configure MTU
-
FTD physical appliance with Inline Set requires a specially designed ACI service graph with the same VLAN ID on both interfaces
-
-
Create new or update existing access rule
-
Configure source and destination security zones
-
-
Create new or update existing access policy
-
Configure name
-
-
Create new security zone
-
Configure type
-
Resolved Enhancement Requests in Version 1.0(3)
|
Caveat |
Description |
|---|---|
|
CSCvh58404 |
Enhancement: add IPv4 static route support in FTD-DP |
|
CSCvh58431 |
Enhancement: add cluster support in FTD-DP (pre-configured) |
|
CSCvh58443 |
Enhancement: add etherchannel support in FTD-DP |
Resolved Caveats in Version 1.0(3)
|
Caveat |
Description |
|---|---|
|
CSCvg73120 |
Associated interfaces deleted if BVI interface ID changed |
Bug Search
As a registered Cisco.com user, sign in to view more information about each bug or caveat using the Cisco Bug Search Tool.
Features Not Supported in Version 1.0(3)
The APIC cannot configure the following features using the FTD device package:
-
Dynamic routing
-
Port-channels
-
Access control policy rule ports, IPs, or inspections
-
Network Address Translation (NAT)
 Note |
For any unsupported FTD feature, we recommended that you clean up the configuration manually before removing a service graph or deleting the tenant. |
Known Issues
This section describes known issues and their workarounds.
CSCvj29517
In some circumstances, the FMC may be too busy to complete a service call from the APIC, which causes the same request to be made to the FMC again and again. This may occur when:
-
Using the FTD device package, version 1.0.3
-
Clustering deployment with Inline mode
Workaround
You can use the Cisco-provided Python script (attached to CSCvj29517) to access the APIC REST API and modify the timeout values:
-
Run the script to change the timeout value to its maximum number:
set_timeout.py <APIC_IP> <USERNAME> <PASSWORD> maximum -
Monitor the debug.log from the APIC to verify that the service call has completed. Or check the the FMC to verify that the intended changes have been pushed down to the FMC and the deployment to the FTD is complete.
-
Run the script again to change the timeout value back to its default number. Otherwise, unexpected behavior may occur.
set_timeout.py <APIC_IP> <USERNAME> <PASSWORD> default
CSCvf88494
When deleting a tenant with a large configuration, the device package process is killed before it can finish the service call, resulting in a configuration that may not be completely cleaned up on the FMC. This may occur when:
-
Using the FTD device package, version 1.0.2
-
The tenant contains a device that has more than 50 service graphs deployed
-
Deleting the tenant directly before detaching the service graphs
Workaround
Detach the service graphs before deleting the tenant, or increase various timeout values on the APIC using its REST API. The REST payload is like this:
<polUni>
<infraInfra>
<vnsMDev vendor=CISCO model=FTD_FI version=1.0>
<vnsDevScript auditTimeout=10800 modifyTimeout=10800 watchdogTimeout=10800/>
</vnsMDev>
</infraInfra>
</polUni>
You can use the Cisco-provided Python script (attached to CSCvf88494) to access the APIC REST API and modify the timeout values:
-
Before deleting the tenant, run the script to change the timeout value to its maximum number:
set_timeout.py <APIC_IP> <USERNAME> <PASSWORD> maximum -
Delete the tenant from the APIC.
-
Monitor the debug.log from the APIC to verify that the service call has completed. Or check the FMC to verify that all relevant configuration data has been cleaned up (such as access rules, security zones, sub-interfaces, and inline sets).
-
Run the script again to change the timeout value back to its default number. Otherwise, unexpected behavior may occur.
set_timeout.py <APIC_IP> <USERNAME> <PASSWORD> default
 Note |
Note: If the “CISCO-FTD_FI-1.0” device package is not installed on the APIC, running the script results in a “Bad Request” error. This error message can be safely ignored, as the script is designed to affect this particular device package only. |
For more information, see CSCvg00515, opened to track this issue.
CSCvg06100
VLAN trunking fails in Transparent mode on a virtual FTD.
Workaround
Opened to track the FMC issue in CSCvf90086.
Enable the trunking port after creating the L4-L7 device. Then, apply the service graph.
If the deployment fails:
-
On the FMC:
-
Navigate to Devices, and select the FTD.
-
Delete the new BVI and the associated sub-interfaces. Click Save. Click Deploy.
-
Wait for the FMC to complete the deployment.
-
-
On the APIC:
-
In the node tree on the left, navigate to L4-L7 Devices, and select the device.
-
Verify that the Trunking Port check box is selected.
-
Right-click the device, and select Re-Query For Device Validation.
-
CSCvc46536
Multiple graph deployment needs a different parameter name for an access rule.
Workaround
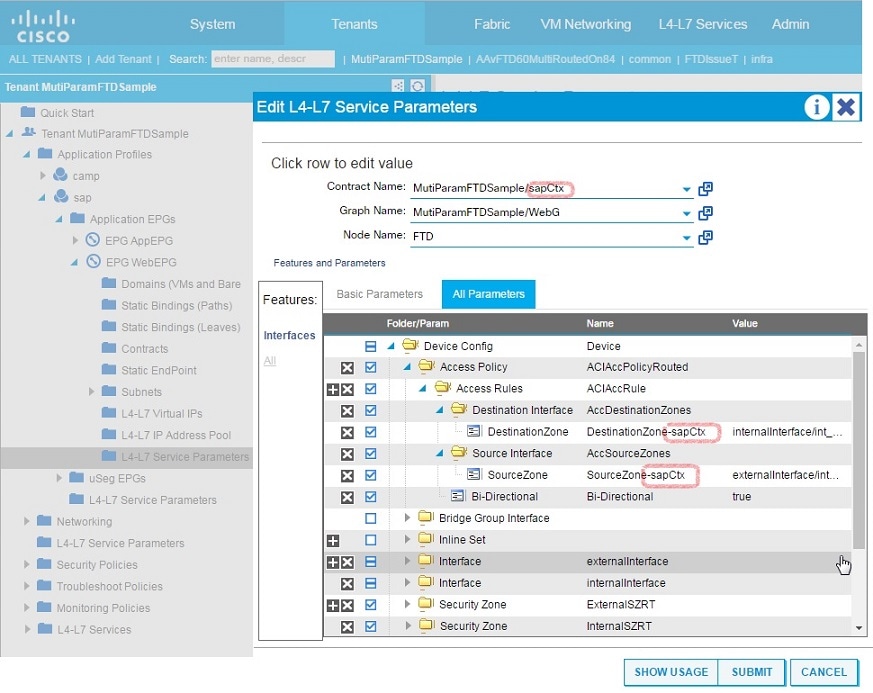
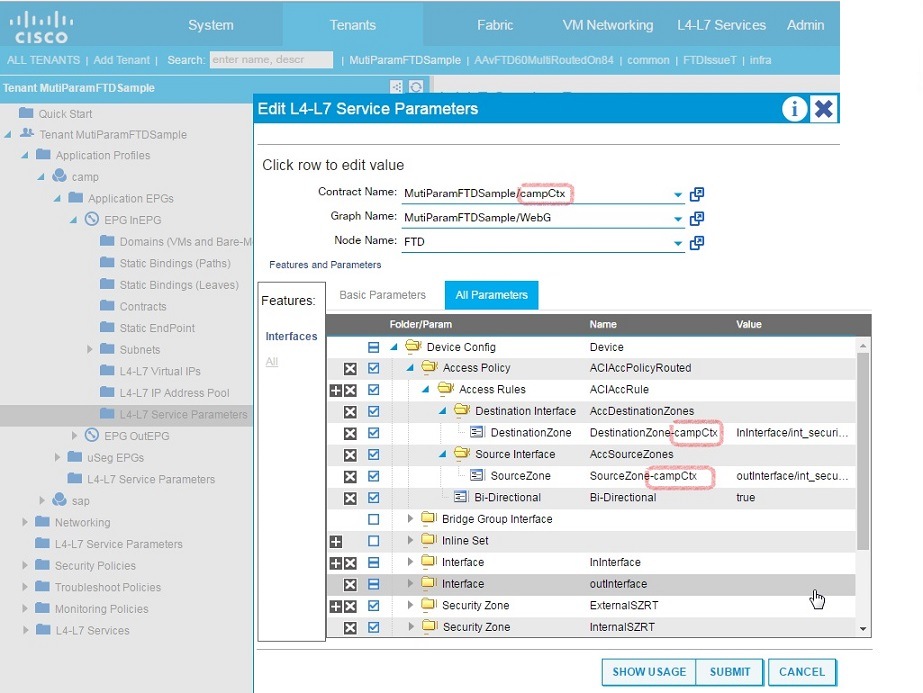
For instance, Access Rules is a common APIC configuration parameter that can be shared across multiple graph deployments on the same L4-L7 device. In order to attach each graph deployment's interface security zones to a common access rule, provide different names for the SourceZone and DestinationZone parameters. For example, append each parameter with a matching suffix name, such as SourceZone-campCtx and DestinationZone-campCtx in one case and SourceZone-sapCtx and DestinationZone-sapCtx in another.
For more information, see the FMC Configuration Guide in Related Documentation.
 Feedback
Feedback