Publishing a
Configuration Master overwrites existing policy information on the Web Security
appliances associated to that Configuration Master.
For information about
which settings you can configure using a Configuration Master, see
Determining the Correct Configuration Publishing Method.
All Publishing Jobs
If different features
are enabled on different Web Security appliances assigned to the same
Configuration Master, you must publish to each appliance separately, and verify
and enable features before each publish.
To identify
configuration mismatches encountered during publishing, see
Viewing Publish History
.
- Save a configuration file from each
target Web Security appliance before publishing, so that you can restore the
existing configuration in case of problems with the published configuration.
See the AsyncOS for Cisco Web Security Appliances User Guide for details.
- Any change that would cause a Web
proxy restart when committed on the Web Security appliance will also cause a
proxy restart when you publish it from the Security Management appliance. You
will receive a warning in these situations.
Web Proxy restarts temporarily interrupt web security services.
- When you publish any change to an
Identity/Identification Profile, all end-users must re-authenticate.
Special Situations
- If you have
reverted AsyncOS on the target Web Security appliance, you may need to
associate a different Configuration Master with that appliance.
- If you publish a
Configuration Master to a Web Security appliance that does not have a realm
configured with Transparent User Identification enabled, but you have selected
Transparent User Identification in an Identity /Identification Profile or SaaS
Policy:
- For
Identities/Identification Profiles, Transparent User Identification is disabled
and the Require Authentication option is selected instead.
- For SaaS
Policies, the Transparent User Identification option is disabled and the
default option (Always prompt SaaS users for proxy authentication) is selected
instead.
- When you publish
External DLP policies from a Security Management appliance to multiple Web
Security appliances that are not configured for RSA servers, the Security
Management appliance will send the following publish status warning:
“The Security Services display
settings configured for Configuration Master
<version> do not currently reflect the state of one or more Security
Services on Web Appliances associated with this publish request. The affected
appliances are: “<WSA Appliance
Names>”. This may indicate a misconfiguration of the Security Services
display settings for this particular Configuration Master. Go to the Web
Appliance Status page for each appliance provides a detailed view to
troubleshooting this issue. Do you want to continue publishing the
configuration now?”
If you decide to
continue to publish, the Web Security appliance that is not configured for the
RSA servers will receive the External DLP policies, but these policies will be
disabled.The Web Security appliance External DLP page will not show the
published policies if External DLP Server is not configured.
|
If the
Scheme in the Identity /Identification Profile in the Configuration Master Was:
|
Then the
Scheme in the Identity /Identification Profile on the Web Security Appliance
Becomes
|
|
Use
Kerberos
|
Use NTLMSSP
or Basic
|
|
Use
Kerberos or NTLMSSP
|
Use NTLMSSP
|
|
Use
Kerberos or NTLMSSP or Basic
|
Use NTLMSSP
or Basic
|
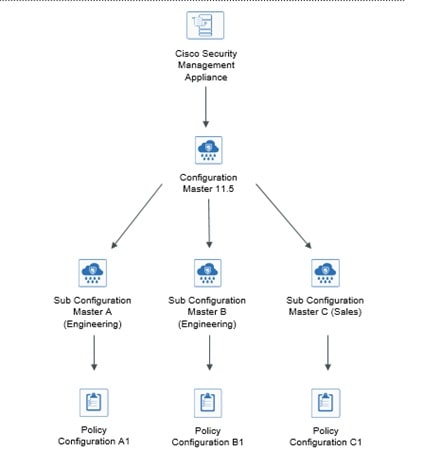
If you are an externally authenticated user, you can only view the list of all the Configuration Master that are assigned
to the Web Security appliance and publish the configuration that is currently initialized. If you want to publish a different
subset of the Configuration Master, contact your administrator.



 Feedback
Feedback