- Preface
- Supplemental License Agreement
- Installing the Product Software
- Running the Setup Program
- Configuring Cisco IOS CNS Agents
- Setting Up a Multizone System
- Setting Up a Multihomed System
- Scalability Among Event Gateway Ports
- Cisco CNS Configuration Engine SSL Security
- Installing the VMware
- Index
Cisco Configuration Engine Installation and Configuration Guide 3.5.4
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- April 10, 2014
Chapter: Setting Up a Multizone System
Setting Up a Multizone System
The installation of the Cisco Configuration Engine software does not offer the multizone system setup by default. If you require a multizone system setup, you must enable the multizone feature during the system setup. To setup multiple IP addresses on the Cisco Configuration Engine server, you must manually customize the network parameters of the server to have multiple IP addresses. You can configure multiple IP addresses by using IP aliasing on a network interface card or by using multiple network interface cards where each card should have an IP address. This chapter provides a brief overview of the Cisco Configuration Engine multizone setup. It contains the following sections:
Setup Restrictions
Two network interfaces are installed in the Cisco Configuration Engine server: eth0 (Ethernet 0) and eth1 (Ethernet 1). Both interfaces can be configured and connected to networks. The Cisco Configuration Engine setup has the following restrictions:
1.![]() For both the eth0 and eth1 interfaces, the default gateway must be configured on the same network as eth0.
For both the eth0 and eth1 interfaces, the default gateway must be configured on the same network as eth0.
2.![]() The primary IP address and hostname should be assigned to eth0.
The primary IP address and hostname should be assigned to eth0.
3.![]() The prompt CNS Event Bus Network parameter in the setup of CNS Configuration Engine controls the location of the CNS Event Bus. It should be set as eth0 hostname.
The prompt CNS Event Bus Network parameter in the setup of CNS Configuration Engine controls the location of the CNS Event Bus. It should be set as eth0 hostname.
4.![]() Ethernet 0 is used to connect to the management network. The CPE resides in the management network.
Ethernet 0 is used to connect to the management network. The CPE resides in the management network.
Typical Deployment of the Multizone System
To deploy the Cisco Configuration Engine in a distributed architecture in different security zones, follow these steps:
- Zone 1: Deploy the Cisco Configuration Engine processes which communicate with the network elements through the public network.
- Zone 2: Deploy the Cisco Configuration Engine administrative interfaces, APIs, and the back-end services.
- Zone 3: Deploy the LDAP and the Network File System with the template files.
To deploy one instance of the Cisco Configuration Engine in a distributed architecture, the Cisco Configuration Engine should be in a Demilitarized Zone (DMZ). Figure 4-1 shows a typical deployment of Cisco Configuration Engine server with the Cisco Configuration Engine software in a multi-network environment: private network and public network.
- Private Network—The private network contains the Network Operations Center (NOC), where the provisioning applications connect to the Cisco Configuration Engine through the CNS Event Bus.
- Public Network—The public network is the entry to the management network where CPE connects to the Cisco Configuration Engine through TCP connections.
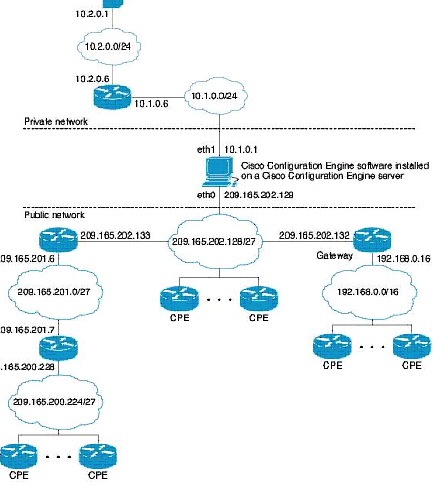
- In Figure 4-1, the public network represents Zone 1, private network represents Zone 3 and the Cisco Configuration Engine resides in Zone 2 of the DMZ.
- In Cisco Configuration Engine, the server can be configured to block all the administrative requests from the public network. This is done automatically during the setup. The setup program checks if multiple IP addresses are assigned to the Cisco Configuration Engine server. If so, it prompts the user to enable the multi-zone feature.
 Feedback
Feedback