-
- IP Access List Features Roadmap
- IP Access List Overview
- Creating an IP Access List and Applying It to an Interface
- Creating an IP Access List to Filter IP Options TCP Flags Noncontiguous Ports or TTL Values
- Refining an IP Access List
- Displaying and Clearing IP Access List Data Using ACL Manageability
- Controlling Access to a Virtual Terminal Line
- Access List-Based RBSCP
- ACL IP Options Selective Drop
- ACL Authentication of Incoming rsh and rcp Requests
- Configuring Lock-and-Key Security for Dynamic Access Lists
- Configuring IP Session Filtering of Reflexive Access Lists
- Configuring TCP Intercept and Preventing Denial-of-Service Attacks
-
- Configuring Context-based Access Control
- Application Firewall - Instant Message Traffic Enforcement
- Cisco IOS Firewall MIB
- Cisco IOS Firewall Performance Improvements
- Cisco IOS Firewall Stateful Failover
- Cisco IOS Firewall Support for TRP
- Email Inspection Engine
- ESMTP Support for Cisco IOS Firewall
- Firewall ACL Bypass
- Firewall N2H2 Support
- Firewall Stateful Inspection of ICMP
- Firewall Support for SIP
- Firewall Support of Skinny Client Control Protocol
- Firewall Websense URL Filtering
- Granular Protocol Inspection
- HTTP Inspection Engine
- Inspection of Router-Generated Traffic
- TCP Out-of-Order Packet Support for Cisco IOS Firewall and Cisco IOS IPS
- Transparent Cisco IOS Firewall
- Virtual Fragmentation Reassembly
- VRF Aware Cisco IOS Firewall
- Configuring Port to Application Mapping
- Configuring Cisco IOS Intrusion Prevention System (IPS)
- Configuring IP Security Options
- Finding Feature Information
- Contents
- Prerequisites for Stateful Failover
- Restrictions for Stateful Failover
- Information About Stateful Failover
Cisco IOS Firewall Stateful Failover
Stateful failover for the Cisco IOS firewall enables a router to continue processing and forwarding firewall session packets after a planned or unplanned outage occurs. You employ a backup (secondary) router that automatically takes over the tasks of the active (primary) router if the active router loses connectivity for any reason. This process is transparent and does not require adjustment or reconfiguration of any remote peer.
Stateful failover for the Cisco IOS firewall is designed to work in conjunction with stateful switchover (SSO) and Hot Standby Routing Protocol (HSRP). HSRP provides network redundancy for IP networks, ensuring that user traffic immediately and transparently recovers from failures in network edge devices or access circuits. That is, HSRP monitors both the inside and outside interfaces so that if either interface goes down, the whole router is deemed to be down and ownership of firewall sessions is passed to the standby router (which transitions to the HSRP active state). SSO allows the active and standby routers to share firewall session state information so that each router has enough information to become the active router at any time. To configure stateful failover for the Cisco IOS firewall, a network administrator should enable HSRP, assign a virtual IP address, and enable the SSO protocol.
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest feature information and caveats, see the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the "Feature Information for Cisco IOS Firewall Stateful Failover" section.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Contents
•![]() Prerequisites for Stateful Failover
Prerequisites for Stateful Failover
•![]() Restrictions for Stateful Failover
Restrictions for Stateful Failover
•![]() Information About Stateful Failover
Information About Stateful Failover
•![]() How to Configure Stateful Failover for Cisco IOS Firewalls
How to Configure Stateful Failover for Cisco IOS Firewalls
•![]() Maintaining Firewall Stateful Failover
Maintaining Firewall Stateful Failover
•![]() Feature Information for Cisco IOS Firewall Stateful Failover
Feature Information for Cisco IOS Firewall Stateful Failover
Prerequisites for Stateful Failover
Complete, Duplicate Cisco IOS Firewall Configuration on the Active and Standby Devices
This document assumes that you have a complete Cisco IOS firewall configuration.
The Cisco IOS firewall configuration that is set up on the active device must be duplicated on the standby device. That is, firewall protocols inspected, the interface ACL's, the global firewall settings and the interface firewall configuration.

Note ![]() None of the configuration information between the active and standby device is automatically transferred; the user is responsible for ensuring that the Cisco IOS firewall configurations match on both devices. If the Cisco IOS firewall configurations on both devices do not match, failover from the active device to the standby device will not be successful.
None of the configuration information between the active and standby device is automatically transferred; the user is responsible for ensuring that the Cisco IOS firewall configurations match on both devices. If the Cisco IOS firewall configurations on both devices do not match, failover from the active device to the standby device will not be successful.
Device Requirements
•![]() The active and standby Cisco IOS routers must be running the same Cisco IOS software,
The active and standby Cisco IOS routers must be running the same Cisco IOS software,
Release 12.4(6)T or later.
•![]() Stateful failover for the Cisco IOS firewall requires that your network contains two identical routers that are available to be either the primary or secondary device. Both routers should be the same type of device, have the same CPU and memory.
Stateful failover for the Cisco IOS firewall requires that your network contains two identical routers that are available to be either the primary or secondary device. Both routers should be the same type of device, have the same CPU and memory.
•![]() This feature is currently supported only on a limited number of platforms. To check the latest platform support, go to Cisco Feature Navigator at http://www.cisco.com/go/fn.
This feature is currently supported only on a limited number of platforms. To check the latest platform support, go to Cisco Feature Navigator at http://www.cisco.com/go/fn.
Restrictions for Stateful Failover
When configuring redundancy for a Cisco IOS firewall, the following restrictions exist:
•![]() Both the active and standby devices must run the identical version of the Cisco IOS software, and both the active and standby devices must be connected via hub or switch.
Both the active and standby devices must run the identical version of the Cisco IOS software, and both the active and standby devices must be connected via hub or switch.
•![]() HSRP requires the inside interface to be connected via LANs.
HSRP requires the inside interface to be connected via LANs.
•![]() Load balancing is not supported; that is, no more than one device in a redundancy group can be active at any given time.
Load balancing is not supported; that is, no more than one device in a redundancy group can be active at any given time.
•![]() Any restrictions that exist for intradevice SSO will also exist for the firewall High Availability (HA). The behavior of intra-device active where the Active device re-boots when the SSO state changes from Active to anything will be the same with firewall HA.
Any restrictions that exist for intradevice SSO will also exist for the firewall High Availability (HA). The behavior of intra-device active where the Active device re-boots when the SSO state changes from Active to anything will be the same with firewall HA.
•![]() No support for configuration synchronization and In-Service Software Upgrade (ISSU) which are not yet available for intra-box failover in Cisco IOS T releases.
No support for configuration synchronization and In-Service Software Upgrade (ISSU) which are not yet available for intra-box failover in Cisco IOS T releases.
•![]() Stateful failover of the Cisco IOS firewall is not supported with Zone-Based Policy firewall configuration.
Stateful failover of the Cisco IOS firewall is not supported with Zone-Based Policy firewall configuration.
•![]() This phase of the feature will not provide support for asymmetric routing and it is the responsibility of the user to configure the network to avoid this.
This phase of the feature will not provide support for asymmetric routing and it is the responsibility of the user to configure the network to avoid this.
•![]() The stateful failover feature does not synchronize any statistics or mib firewall information between the active and standby devices.
The stateful failover feature does not synchronize any statistics or mib firewall information between the active and standby devices.
•![]() The stateful failover feature does not support rate-limiting of firewall sessions on the standby router for the failed over sessions.
The stateful failover feature does not support rate-limiting of firewall sessions on the standby router for the failed over sessions.
•![]() Currently only Layer 4 TCP and UDP protocol failover is supported. Therefore, all TCP only sessions, UDP only sessions, and single channel granular protocols sessions for which L7 inspection is not supported are failed over.
Currently only Layer 4 TCP and UDP protocol failover is supported. Therefore, all TCP only sessions, UDP only sessions, and single channel granular protocols sessions for which L7 inspection is not supported are failed over.
•![]() Layer 4 ICMP session will not be failed over to the standby
Layer 4 ICMP session will not be failed over to the standby
•![]() Any session configured for Layer 7 inspection will NOT be failed over.
Any session configured for Layer 7 inspection will NOT be failed over.
•![]() CiscoIntrusion Prevention Services (IPS)/Intrusion Detection Services (IDS) feature will not be made HA aware in this release.
CiscoIntrusion Prevention Services (IPS)/Intrusion Detection Services (IDS) feature will not be made HA aware in this release.
Information About Stateful Failover
•![]() Supported Deployment Scenarios: Stateful Failover for the Cisco IOS Firewall
Supported Deployment Scenarios: Stateful Failover for the Cisco IOS Firewall
•![]() Stateful Failover Architecture
Stateful Failover Architecture
Supported Deployment Scenarios: Stateful Failover for the Cisco IOS Firewall
It is recommended that you implement stateful failover in one of the following recommended deployment scenarios:
•![]() Dual LAN Interface
Dual LAN Interface
•![]() LAN WAN Interface
LAN WAN Interface
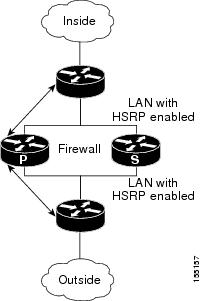
In a dual LAN interface scenario, the active and standby routers running the firewall are connected to each other via LAN interface on both the inside and the outside (see Figure 1). HSRP is configured on both the inside and outside interface. The next hop routers in this scenario talk to the HA pair via the virtual IP address. In this scenario there are two virtual IP address, one on the inside and the other on the outside. Virtual IP addresses cannot be advertised using routing protocols. You need to create static routes on the next hops to get to the virtual IP address.
You need to configue HSRP tracking in order to track multiple pairs of interfaces. If you run HSRP on only one pair of interfaces, or run on both without mutual tracking of the pairs, each pair functions independently of each other and are unaware of each other's state changes. For example, if HSRP is run on only the two outside interfaces (as shown in Figure 1), this could cause HSRP to failover on the outside interfaces, whilst the inside interfaces are unchanged. This causes the black holing of traffic, which continues to be directed to the primary from the inside. This introduces the possibility of problems arising from one interface on a primary router failing and triggering a move to the secondary, while the other interface on the ex-primary remains active. Mutual tracking means that if the outside interface does fail, the inside interface on the same router will also be deemed down allowing for complete router failover to the secondary.
Figure 1 Dual Interface Network Topology
In a LAN WAN scenario, the inside interface of the Active Standby pair running the firewall are connected via LAN interface on the inside and WAN interface on the outside (see Figure 2). HSRP is configured on the inside interface. The inside network communicates with the HA pair using the inside virtual IP address.
HSRP tracking should be configured on the inside LAN interfaces to track the state of the outside WAN interface. If the outside WAN interface goes down on the active the LAN interface that is tracking it reduces the HSRP priority and initiates a failover to the standby. Traffic from the outside flowing into the HSRP pair should now be directed to the new active device.
In the scenario where the LAN interfaces track the WAN interfaces, the failover to the standby happens immediately. However, for traffic to start flowing on the new active router, routing convergence needs to happen. The net failover time is dictated by the routing protocol.
In this scenario the traffic flows from the inside to the outside through the Active due to the HSRP configuration on the inside LAN interfaces. The traffic from the outside to the inside should also flow through the active device. The configuration of the network so that the traffic always flows through the active is beyond the scope of this document. In this scenario, the network administrator is responsible to ensure that the traffic always flows through the active device.
Figure 2

LAN WAN Network Topology
Stateful Failover Architecture
Firewall stateful failover is a client of Cisco IOS SSO. SSO is a method of providing redundancy and synchronization for Cisco IOS applications and features.
State Synchronization
The synchronization manager will be responsible for checking firewall to determine the state of the active device, which must be check pointed to the redundant peers and update that state on the firewall on standby devices.
Periodic updates are sent from the active to the standby for all HA sessions. This information enables the standby to take over the sessions and process the sessions if there is a failover.
The stateful failover feature supports deterministic updates. This means that the updates for a session get sent every N seconds, where N is configurable. Default value for N is 10 sec.
Bulk Synchronization
Bulk synchronization happens at boot time or when you use the clear ip inspect ha sessions all command on the standby device. If the standby device is configured after the active device already has sessions, then only new ha sessions established on the active device are synchronized to the standby device through dynamic synchronization. If you want all the current sessions synchronized from the active to the standby, you must specifically issue the clear ip inspect ha sessions all command on the standby device. A single request message is sent from the standby device to the active device which result in add_session messages from active to standby for all sessions open on the active at that time.
How to Configure Stateful Failover for Cisco IOS Firewalls
•![]() Enabling HSRP: IP Redundancy and a Virtual IP Address
Enabling HSRP: IP Redundancy and a Virtual IP Address
•![]() Enabling Stateful Failover for a Cisco IOS Firewall
Enabling Stateful Failover for a Cisco IOS Firewall
•![]() Configuring the Cisco IOS Firewall HA Update Interval
Configuring the Cisco IOS Firewall HA Update Interval
•![]() Troubleshooting Stateful Failover
Troubleshooting Stateful Failover
•![]() Maintaining Firewall Stateful Failover
Maintaining Firewall Stateful Failover
•![]() Displaying Firewall Stateful Failover Information
Displaying Firewall Stateful Failover Information
Enabling HSRP: IP Redundancy and a Virtual IP Address
HSRP provides two services—IP redundancy and a Virtual IP (VIP) address. Each HSRP group may provide either or both of these services. Cisco IOS firewall stateful failover uses the IP redundancy services from only one HSRP standby group. It can use the VIP address from one or more HSRP groups. Use the following task to configure HSRP on the outside and inside interfaces of the router.

Note ![]() Perform this task on both routers (active and standby) and on both interfaces of each router.
Perform this task on both routers (active and standby) and on both interfaces of each router.
Prerequisites for Spanning Tree Protocol and HSRP Stability
If a switch connects the active and standby routers, you must perform one of the following steps to ensure that the correct settings are configured on that switch:
•![]() Enable the spanning-tree portfast command on every switch port that connects to a HSRP-enabled router interface.
Enable the spanning-tree portfast command on every switch port that connects to a HSRP-enabled router interface.
•![]() Disable the Spanning Tree Protocol (STP) on the switch only if your switch does not connect to other switches. Disabling spanning tree in a multi-switch environment may cause network instability.
Disable the Spanning Tree Protocol (STP) on the switch only if your switch does not connect to other switches. Disabling spanning tree in a multi-switch environment may cause network instability.
•![]() Enable the standby delay minimum [min-delay] reload [reload-delay] command if you do not have access to the switch. The reload-delay argument should be set to a value of at least 120 seconds. This command must be applied to all HSRP interfaces on both routers.
Enable the standby delay minimum [min-delay] reload [reload-delay] command if you do not have access to the switch. The reload-delay argument should be set to a value of at least 120 seconds. This command must be applied to all HSRP interfaces on both routers.
For more information on HSRP instability, see the document Avoiding HSRP Instability in a Switching Environment with Various Router Platforms.

Note ![]() You must perform at least one of these steps for correct HSRP operation.
You must perform at least one of these steps for correct HSRP operation.
Restrictions
•![]() Both the inside (private) interface and the outside (public) interface must belong to separate HSRP groups, but the HSRP group number can be the same.
Both the inside (private) interface and the outside (public) interface must belong to separate HSRP groups, but the HSRP group number can be the same.
•![]() The state of the inside interface and the outside interface must be the same—both interfaces must be in the active state or standby state; otherwise, the packets will not have a route out of the private network.
The state of the inside interface and the outside interface must be the same—both interfaces must be in the active state or standby state; otherwise, the packets will not have a route out of the private network.
•![]() Standby priorities should be equal on both active and standby routers. If the priorities are not equal, the higher priority router will unnecessarily take over as the active router, negatively affecting uptime.
Standby priorities should be equal on both active and standby routers. If the priorities are not equal, the higher priority router will unnecessarily take over as the active router, negatively affecting uptime.
•![]() The IP addresses on the HSRP-tracked interfaces of the standby and active routers should both be either lower or higher on one router than the other. In the case of equal priorities (an HA requirement), HSRP will assign the active state on the basis of the IP address. If an addressing scheme exists so that the public IP address of Router A is lower than the public IP address of Router B, but the opposite is true for their private interfaces, an active/standby-standby/active split condition could exist which will break connectivity.
The IP addresses on the HSRP-tracked interfaces of the standby and active routers should both be either lower or higher on one router than the other. In the case of equal priorities (an HA requirement), HSRP will assign the active state on the basis of the IP address. If an addressing scheme exists so that the public IP address of Router A is lower than the public IP address of Router B, but the opposite is true for their private interfaces, an active/standby-standby/active split condition could exist which will break connectivity.
•![]() Interface ACL should allow HSRP traffic to flow through.
Interface ACL should allow HSRP traffic to flow through.
•![]() Each time an active device relinquishes control to become the standby device, the active device will reload. This functionality ensures that the state of the new standby device synchronizes correctly with the new active device.
Each time an active device relinquishes control to become the standby device, the active device will reload. This functionality ensures that the state of the new standby device synchronizes correctly with the new active device.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() interface type number
interface type number
4. ![]() standby standby-group-number name standby-group-name
standby standby-group-number name standby-group-name
5. ![]() standby standby-group-number ip ip-address
standby standby-group-number ip ip-address
6. ![]() standby standby-group-number track interface-name
standby standby-group-number track interface-name
7. ![]() standby [group-number] preempt
standby [group-number] preempt
8. ![]() standby [group-number] timers [msec] hellotime [msec] holdtime
standby [group-number] timers [msec] hellotime [msec] holdtime
9. ![]() standby delay minimum [min-delay] reload [reload-delay]
standby delay minimum [min-delay] reload [reload-delay]
10. ![]() Repeat.
Repeat.
DETAILED STEPS
Troubleshooting Tips
To help troubleshoot possible HSRP-related configuration problems, issue any of the following HSRP-related debug commands—debug standby errors, debug standby events, and debug standby packets [terse].
Examples
The following example shows how to configure HSRP on a router:
interface Ethernet0/0
ip address 209.165.201.1 255.255.255.224
standby 1 ip 209.165.201.3
standby 1 preempt
standby 1 name HA-out
standby 1 track Ethernet1/0
standby delay minimum 120 reload 120
What to Do Next
After you have successfully configured HSRP on both the inside and outside interfaces, you should enable SSO as described in the section "Enabling SSO."
Enabling SSO
Use this task to enable SSO, which is used to transfer Cisco IOS firewall session state information between two routers.
SSO is a method of providing redundancy and synchronization for many Cisco IOS applications and features. SSO is necessary for the Cisco IOS firewall to learn about the redundancy state of the network and to synchronize their internal application state with their redundant peers.
Prerequisites
•![]() You should configure HSRP before enabling SSO.
You should configure HSRP before enabling SSO.
•![]() To avoid losing SCTP communication between peers, be sure to include the following commands to the local address section of the SCTP section of the IPC configuration:
To avoid losing SCTP communication between peers, be sure to include the following commands to the local address section of the SCTP section of the IPC configuration:
–![]() retransmit-timeout retran-min [msec] retra-max [msec]
retransmit-timeout retran-min [msec] retra-max [msec]
–![]() path-retransmit max-path-retries
path-retransmit max-path-retries
–![]() assoc-retransmit retries
assoc-retransmit retries
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() redundancy inter-device
redundancy inter-device
4. ![]() scheme standby standby-group-name
scheme standby standby-group-name
5. ![]() exit
exit
6. ![]() ipc zone default
ipc zone default
7. ![]() association 1
association 1
8. ![]() protocol sctp
protocol sctp
9. ![]() local-port local-port-number
local-port local-port-number
10. ![]() local-ip device-real-ip-address [device-real-ip-address2]
local-ip device-real-ip-address [device-real-ip-address2]
11. ![]() retransmit-timeout retran-min [msec] retran-max [msec]
retransmit-timeout retran-min [msec] retran-max [msec]
12. ![]() path-retransmit max-path-retries
path-retransmit max-path-retries
13. ![]() assoc-retransmit retries
assoc-retransmit retries
14. ![]() exit
exit
15. ![]() remote-port remote-port-number
remote-port remote-port-number
16. ![]() remote-ip peer-real-ip-address [peer-real-ip-address2]
remote-ip peer-real-ip-address [peer-real-ip-address2]
DETAILED STEPS
Troubleshooting Tips
To help troubleshoot possible SSO-related configuration problems, issue the debug redundancy command.
Examples
The following example shows how to enable SSO:
!
redundancy inter-device
scheme standby HA-in
!
!
ipc zone default
association 1
no shutdown
protocol sctp
local-port 5000
local-ip 10.0.0.1
retransmit-timeout 300 10000
path-retransmit 10
assoc-retransmit 10
remote-port 5000
remote-ip 10.0.0.2
!
What to Do Next
After you have enabled SSO, you should enable stateful failover for a firewall, as shown in the following section.
Enabling Stateful Failover for a Cisco IOS Firewall
Use this task to enabling Stateful Failover for the Cisco IOS firewall.
Prerequisites
Before performing this task, the Cisco IOS firewall inspect rule must be configured. Also, HSRP and SSO must be configured to enable box-to-box redundancy.
Restrictions
The inspect rules should not have ICMP or protocols for which Cisco IOS firewall supports Layer 7 inspection.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() interface [interface-name]
interface [interface-name]
4. ![]() ip inspect [rule] in | out redundancy stateful [hsrp-group-name]
ip inspect [rule] in | out redundancy stateful [hsrp-group-name]
5. ![]() exit
exit
DETAILED STEPS
Configuring the Cisco IOS Firewall HA Update Interval
Use this task to change the amount of time between each update to the standby. The default interval of 10 seconds.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() ip inspect redundancy update seconds [10-60]
ip inspect redundancy update seconds [10-60]
4. ![]() exit
exit
DETAILED STEPS
Troubleshooting Stateful Failover
The following commands may be used to display information about Stateful Failover messages or sessions. The debug commands may be used in any order or independent of the other debug commands.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() debug ip inspect ha [manager | update]
debug ip inspect ha [manager | update]
DETAILED STEPS
Maintaining Firewall Stateful Failover
The clear ip inspect ha command is used to clear all inspect ha sessions on the device. If the device is the standby device then it initiates a bulk sync of all session from the active. It is also used to clear the ha statistics on the device
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() clear ip inspect ha [sessions-all | statistics]
clear ip inspect ha [sessions-all | statistics]
DETAILED STEPS
Displaying Firewall Stateful Failover Information
Use the show ip inspect ha {sessions [detail] | statistics} [vrf vrf-name]}command to display firewall stateful failover information.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() show ip inspect ha {sessions [detail] | statistics} [vrf vrf-name]}
show ip inspect ha {sessions [detail] | statistics} [vrf vrf-name]}
DETAILED STEPS
The following tables provide examples of Stateful Failover error messages and alert message.
Table 1 contains the stateful failover HA error messages.
Table 1 Stateful Failover Error Messages
If audit trail is configured on the standby HA device the standard alerts that are shown when a session is added or deleted will be changed to reflect that the session is a standby session. Table 2 contains the stateful failover alert messages.
Table 2 Stateful Failover Alert Messages
Configuration Examples for Stateful Failover
Example: Stateful Failover
The following output example shows stateful failover that has been configured on a Cisco IOS router:
Router 1)
hostname ha-R1
!
boot-start-marker
boot-end-marker
!
!
redundancy inter-device
scheme standby HAin
!
!
redundancy
logging buffered 10000000 debugging
logging rate-limit console 10000
!
no aaa new-model
!
resource policy
!
!
ipc zone default
association 1
no shutdown
protocol sctp
local-port 5000
local-ip 10.0.0.1
remote-port 5000
remote-ip 10.0.0.2
!
!
ip inspect tcp idle-time 180
ip inspect name ha-protocols tcp
ip inspect name ha-protocols udp
ip inspect redundancy update seconds 60
!
!
!inside interface
interface Ethernet0/0
ip address 10.0.0.1 255.255.255.0
standby delay minimum 120 reload 120
standby 1 ip 10.0.0.3
standby 1 timers 1 10
standby 1 priority 60
standby 1 preempt
standby 1 name HAin
standby 1 track Ethernet1/0
!
!outside interface
interface Ethernet1/0
ip address 211.0.0.1 255.255.255.0
ip access-group fw-ha-acl in
!! The HSRP group used with the inspect config should be the inside HSRP group
ip inspect ha-protocols out redundancy stateful HAin
standby delay minimum 120 reload 120
standby 2 ip 211.0.0.3
standby 2 timers 1 10
standby 2 priority 60
standby 2 preempt
standby 2 name HAout
standby 2 track Ethernet0/0
!
!
!
! ACL on interface should permit HSRP, HA traffic from active to standby device
ip access-list extended fw-ha-acl
permit ip host 211.0.0.2 host 211.0.0.1
permit ip host 211.0.0.1 host 211.0.0.2
deny any any
!
!
!
!
line con 0
exec-timeout 0 0
line aux 0
##########################################################################
Router 2)
hostname ha-R2
!
boot-start-marker
boot-end-marker
!
!
redundancy inter-device
scheme standby HAin
!
!
redundancy
logging buffered 10000000 debugging
logging rate-limit console 10000
!
no aaa new-model
!
resource policy
!
!
ipc zone default
association 1
no shutdown
protocol sctp
local-port 5000
local-ip 10.0.0.2
remote-port 5000
remote-ip 10.0.0.1
!
!
ip inspect tcp idle-time 180
ip inspect name ha-protocols tcp
ip inspect name ha-protocols udp
ip inspect redundancy update seconds 60
!
!
!inside interface
interface Ethernet0/0
ip address 10.0.0.2 255.255.255.0
standby delay minimum 120 reload 120
standby 1 ip 10.0.0.3
standby 1 priority 60
standby 1 preempt
standby 1 name HAin
standby 1 track Ethernet1/0
!
!outside interface
interface Ethernet1/0
ip address 211.0.0.2 255.255.255.0
ip access-group fw-ha-acl in
!! The HSRP group used with the inspect config should be the inside HSRP group
ip inspect ha-protocols out redundancy stateful HAin
standby delay minimum 120 reload 120
standby 2 ip 211.0.0.3
standby 2 priority 60
standby 2 preempt
standby 2 name HAout
standby 2 track Ethernet0/0
!
!
!
! ACL on interface should permit HSRP, HA traffic from active to standby device
ip access-list extended fw-ha-acl
permit ip host 211.0.0.2 host 211.0.0.1
permit ip host 211.0.0.1 host 211.0.0.2
!
!
!
!
line con 0
exec-timeout 0 0
line aux 0
Additional References
Related Documents
|
|
|
|---|---|
Cisco IOS commands |
|
Configuring HSRP |
"Configuring HSRP" |
Standards
|
|
|
|---|---|
No new or modified standards are supported by this feature. |
— |
MIBs
RFCs
|
|
|
|---|---|
No new or modified RFCs are supported by this feature. |
— |
Technical Assistance
Feature Information for Cisco IOS Firewall Stateful Failover
Table 3 lists the features in this module and provides links to specific configuration information.
Use Cisco Feature Navigator to find information about platform support and software image support. Cisco Feature Navigator enables you to determine which software images support a specific software release, feature set, or platform. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.

Note ![]() Table 3 lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Table 3 lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Table 3
Feature Information for Cisco IOS Firewall Stateful Failover
Cisco and the Cisco Logo are trademarks of Cisco Systems, Inc. and/or its affiliates in the U.S. and other countries. A listing of Cisco's trademarks can be found at www.cisco.com/go/trademarks. Third party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1005R)
Any Internet Protocol (IP) addresses and phone numbers used in this document are not intended to be actual addresses and phone numbers. Any examples, command display output, network topology diagrams, and other figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses or phone numbers in illustrative content is unintentional and coincidental.
© 2007 Cisco Systems, Inc. All rights reserved.
 Feedback
Feedback