CA
--certification authority. CA is an entity that issues digital certificates (especially X.509 certificates) and vouches for
the binding between the data items in a certificate.
CLI
--command-line-interface. CLI is an interface that allows the user to interact with the operating system by entering commands
and optional arguments. The UNIX operating system and DOS provide CLIs.
client
--Corresponding IPsec IOS peer of the UUT in the Multi Protocol Label Switching (MPLS) network.
dead
peer
--IKE peer that is no longer reachable.
DN
--Distinguished Name. A DN is the global, authoritative name of an entry in the Open System Interconnection (OSI Directory
[X.500]).
FQDN
--fully qualified domain name. A FQDN is the full name of a system rather than just its host name. For example, aldebaran
is a host name, and aldebaran.interop.com is an FQDN.
FR
--Frame Relay. FR is an industry-standard, switch-data-link-layer protocol that handles multiple virtual circuits using high-level
data link (HDLC) encapsulation between connected devices. Frame Relay is more efficient than X.25, the protocol for which
it generally is considered a replacement.
FVRF
--Front Door Virtual Routing and Forwarding (VRF) repository. FVRF is the VRF used to route the encrypted packets to the peer.
IDB
--Interface descriptor block. An IDB subblock is an area of memory that is private to an application. This area stores private
information and states variables that an application wants to associate with an IDB or an interface. The application uses
the IDB to register a pointer to its subblock, not to the contents of the subblock itself.
IKE
--Internet Key Exchange. IKE establishes a shared security policy and authenticates keys for services (such as IPsec) that
require keys. Before any IPsec traffic can be passed, each router, firewall, and host must verify the identity of its peer.
This can be done by manually entering preshared keys into both hosts or by a CA service.
IKE
keepalive
--Bidirectional mechanism for determining the liveliness of an IKE peer.
IPsec
--Security protocol for IP.
IVRF
--Inside Virtual Routing and Forwarding. IVRF is the VRF of the plaintext packets.
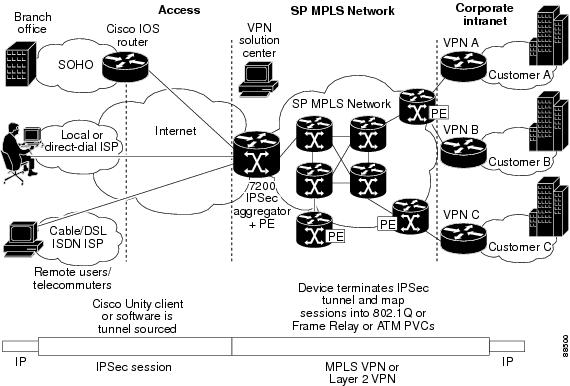
MPLS
--Multiprotocol Label Switching. MPLS is a switching method that forwards IP traffic using a label. This label instructs the
routers and the switches in the network where to forward the packets based on preestablished IP routing information.
RSA
--Rivest, Shamir, and Adelman are the inventors of the RSA technique. The RSA technique is a public-key cryptographic system
that can be used for encryption and authentication.
SA
--Security Association. SA is an instance of security policy and keying material applied to a data flow.
VPN
--Virtual Private Network. A VPN enables IP traffic to travel securely over a public TCP or IP network by encrypting all traffic
from one network to another. A VPN uses “tunneling” to encrypt all information at the IP level.
VRF
--Virtual Route Forwarding. VRF is A VPN routing and forwarding instance. A VRF consists of an IP routing table, a derived
forwarding table, a set of interfaces that use the forwarding table, and a set of rules and routing protocols that determine
what goes into the forwarding table. In general, a VRF includes the routing information that defines a customer VPN site that
is attached to a PE router.
XAUTH
--Extended authentication. XAUTH is an optional exchange between IKE Phase 1 and IKE Phase 2, in which the router demands
additional authentication information in an attempt to authenticate the actual user (as opposed to authenticating the peer).

 Feedback
Feedback