backup
bandwidth
--The usage of NHOP and NNHOP backup tunnels to provide bandwidth protection for rerouted LSPs.
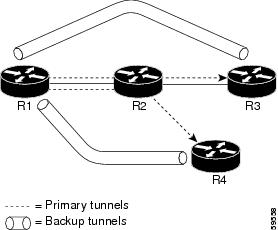
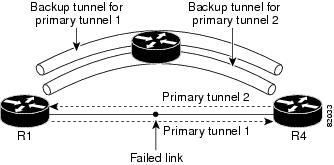
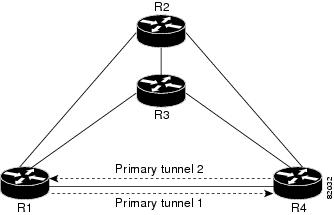
backup
tunnel
--An MPLS TE tunnel used to protect other (primary) tunnels’ traffic when a link or node failure occurs.
bandwidth
--The available traffic capacity of a link.
Cisco
Express
Forwarding
--A means for accelerating the forwarding of packets within a router, by storing route lookup.
enterprise
network
--A large and diverse network connecting most major points in a company or other organization.
Fast
Reroute
--Procedures that enable temporary routing around a failed link or node while a new LSP is being established at the head end.
Gigabit
Ethernet
--Standard for a high-speed Ethernet, approved by the IEEE (Institute of Electrical and Electronics Engineers) 802.3z standards
committee in 1996.
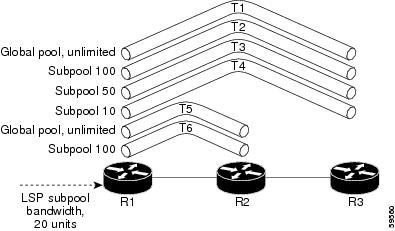
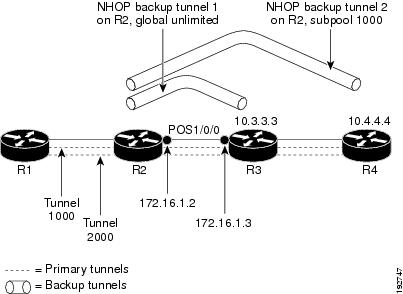
global
pool
--The total bandwidth allocated to an MPLS Traffic Engineering link or node.
headend
--The router that originates and maintains a given LSP. This is the first router in the LSP’s path.
hop
--Passage of a data packet between two network nodes (for example, between two routers).
instance
--A Hello instance implements the RSVP Hello extensions for a given router interface address and remote IP address. Active
Hello instances periodically send Hello Request messages, expecting Hello ACK messages in response. If the expected Ack message
is not received, the active Hello instance declares that the neighbor (remote IP address) is unreachable (that is, it is lost).
This can cause LSPs crossing this neighbor to be fast rerouted.
interface
--A network connection.
Intermediate
System-to-Intermediate
System
--IS-IS. Link-state hierarchical routing protocol that calls for intermediate system (IS) routers to exchange routing information
based on a single metric to determine network topology.
link
--A point-to-point connection between adjacent nodes. There can be more than one link between adjacent nodes. A network communications
channel consisting of a circuit or transmission path and all related equipment between a sender and a receiver. Sometimes
referred to as a line or a transmission link.
limited
backup
bandwidth
--Backup tunnels that provide bandwidth protection.
load
balancing
--A configuration technique that shifts traffic to an alternative link if a certain threshold is exceeded on the primary link.
Load balancing is similar to redundancy in that if an event causes traffic to shift directions, alternative equipment must
be present in the configuration. In load balancing, the alternative equipment is not necessarily redundant equipment that
only operates in the event of a failure.
LSP
--label switched path. A configured connection between two routers, in which label switching is used to carry the packets.
The purpose of an LSP is to carry data packets.
merge
point
--The backup tunnel’s tail.
MPLS
--Multiprotocol Label Switching. Packet-forwarding technology, used in the network core, that applies data link layer labels
to tell switching nodes how to forward data, resulting in faster and more scalable forwarding than network layer routing normally
can do.
MPLS
global
label
allocation
--There is one label space for all interfaces in the router. For example, label 100 coming in one interface is treated the
same as label 100 coming in a different interface.
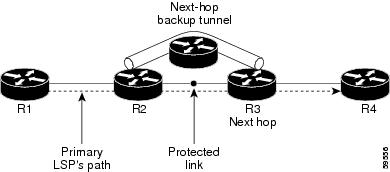
NHOP
--next hop. The next downstream node along an LSP’s path.
NHOP
backup
tunnel
--next-hop backup tunnel. Backup tunnel terminating at the LSP’s next hop beyond the point of failure, and originating at
the hop immediately upstream of the point of failure. It bypasses a failed link, and is used to protect primary LSPs that
were using this link before the failure.
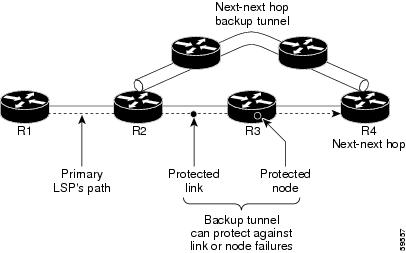
NNHOP
--next-next hop. The node after the next downstream node along an LSP’s path.
NNHOP
backup
tunnel
--next-next-hop backup tunnel. Backup tunnel terminating at the LSP’s next-next hop beyond the point of failure, and originating
at the hop immediately upstream of the point of failure. It bypasses a failed link or node, and is used to protect primary
LSPs that were using this link or node before the failure.
node
--Endpoint of a network connection or a junction common to two or more lines in a network. Nodes can be interconnected by
links, and serve as control points in the network. Computers on a network, or any endpoint or a junction common to two or
more lines in a network. Nodes can be processors, controllers, or workstations.
OSPF
--Open Shortest Path First. A link-state hierarchical Interior Gateway Protocol routing algorithm, derived from the IS-IS
protocol. OSPF features include least-cost routing, multipath routing, and load balancing.
primary
LSP
--The last LSP originally signaled over the protected interface before the failure. The LSP before the failure.
primary
tunnel
--Tunnel whose LSP may be fast rerouted if there is a failure. Backup tunnels cannot be primary tunnels.
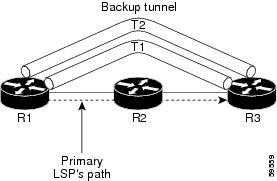
promotion
--Conditions, such as a new backup tunnel comes up, cause a reevaluation of a backup tunnel that was chosen for an LSP. If
the reevaluation is successful, it is called a promotion.
protected
interface
--An interface that has one or more backup tunnels associated with it.
redundancy
--The duplication of devices, services, or connections so that, in the event of a failure, the redundant devices, services,
or connections can perform the work of those that failed.
RSVP
--Resource Reservation Protocol. An IETF protocol used for signaling requests (setting up reservations) for Internet services
by a customer before that customer is permitted to transmit data over that portion of the network.
scalability
--An indicator showing how quickly some measure of resource usage increases as a network gets larger.
state
--Information that a router must maintain about each LSP. The information is used for rerouting tunnels.
subpool
--The more restrictive bandwidth in an MPLS Traffic Engineering link or node. The subpool is a portion of the link or node’s
overall global pool bandwidth.
tailend
--The router upon which an LSP is terminated. This is the last router in the LSP’s path.
topology
--The physical arrangement of network nodes and media within an enterprise networking structure.
tunnel
--Secure communications path between two peers, such as two routers.
unlimited
backup
bandwidth
--Backup tunnels that provide no bandwidth (best-effort) protection (that is, they provide best-effort protection).

 Feedback
Feedback