Limitations and Restrictions of Assurance
Assurance does not support devices that are connected through Network Address Translation (NAT).
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
Assurance does not support devices that are connected through Network Address Translation (NAT).
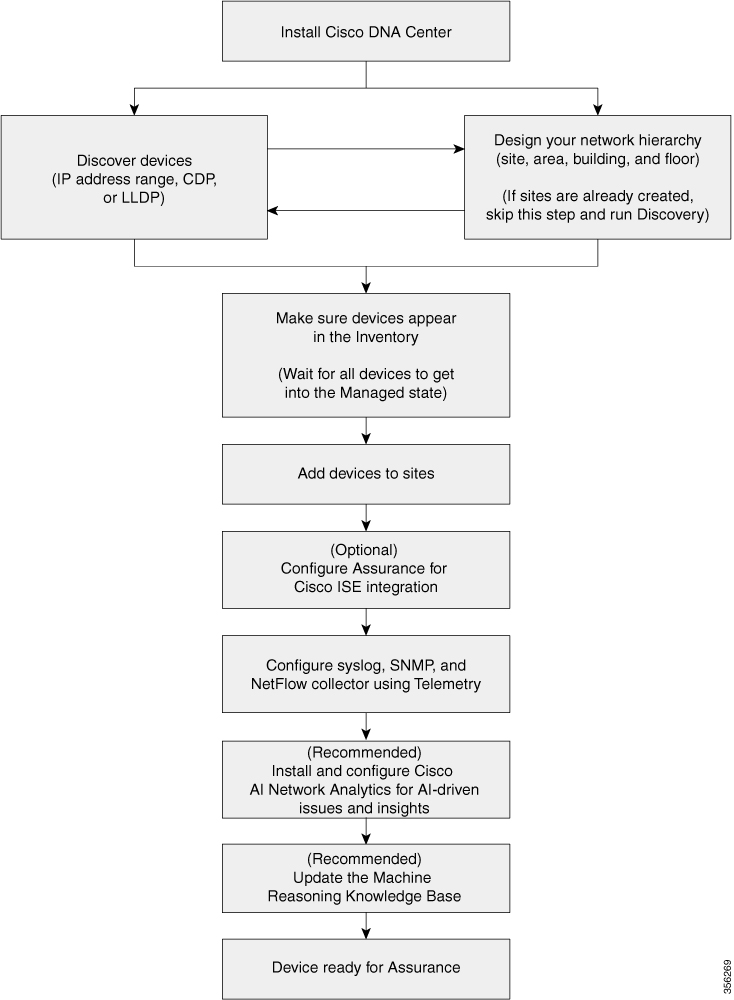
Before you begin using the Assurance application, you must set up Cisco DNA Center to use Assurance.
This chapter provides the basic tasks you must do to set up Assurance. Use this chapter in conjunction with the Cisco DNA Center User Guide.
See the following illustration and the procedure that follows to understand the basic workflow.
|
Step 1 |
Install Cisco DNA Center. See the Cisco DNA Center Installation Guide. |
||||
|
Step 2 |
Do the following in any order:
|
||||
|
Step 3 |
Make sure that the devices appear in the device Inventory. See Display Information About Your Inventory.
|
||||
|
Step 4 |
Add devices to sites. |
||||
|
Step 5 |
If you have APs, we recommend that you add them to a floor map. |
||||
|
Step 6 |
If your network uses Cisco Identity Services Engine (ISE) for user authentication, you can configure Assurance for Cisco ISE integration. This enables you to see more information about wired clients, such as the username and operating system, in Assurance. |
||||
|
Step 7 |
Configure the syslog, SNMP traps, and NetFlow Collector servers using Telemetry. |
||||
|
Step 8 |
(Recommended) To view AI-driven issues and gain network insights, configure Cisco AI Network Analytics data collection. |
||||
|
Step 9 |
(Recommended) To have access to the latest Machine Reasoning workflows, update the Machine Reasoning Knowledge Base. |
||||
|
Step 10 |
Start using the Assurance application. |
Use the Cisco DNA Center Discovery feature to scan the devices in your network.
The Discovery feature scans the devices in your network and sends the list of discovered devices to inventory.
The Discovery feature also works with the Device Controllability feature to configure the required network settings on devices, if these settings are not already present on the devices.
There are three ways for you to discover devices:
Use Cisco Discovery Protocol (CDP) and provide a seed IP address.
Specify a range of IP addresses. (A maximum range of 4096 devices is supported.)
Use Link Layer Discovery Protocol (LLDP) and provide a seed IP address.
When configuring the Discovery criteria, remember that there are settings that you can use to help reduce the amount of time it takes to discover your network:
CDP Level and LLDP Level: If you use CDP or LLDP as the Discovery method, you can set the CDP or LLDP level to indicate the number of hops from the seed device that you want to scan. The default, level 16, might take a long time on a large network. So, if fewer devices have to be discovered, you can set the level to a lower value.
Subnet Filters: If you use an IP address range, you can specify devices in specific IP subnets for Discovery to ignore.
Preferred Management IP: Whether you use CDP, LLDP, or an IP address range, you can specify whether you want Cisco DNA Center to add any of the device's IP addresses or only the device loopback address.
 Note |
For Cisco SD-Access Fabric and Cisco DNA Assurance, we recommend that you specify the device loopback address. |
Regardless of the method you use, you must be able to reach the device from Cisco DNA Center and configure specific credentials and protocols in Cisco DNA Center to discover your devices. These credentials can be configured and saved in the window or on a per-job basis in the Discovery window.
 Note |
If a device uses a first hop resolution protocol, such as Hot Standby Router Protocol (HSRP) or Virtual Router Redundancy Protocol (VRRP), the device might be discovered and added to the inventory along with its floating IP address. Later, if HSRP or VRRP fails, the IP address might be reassigned to a different device. This situation can cause issues with the data that Cisco DNA Center retrieves for analysis. |
Before you run Discovery, complete the following minimum prerequisites:
Understand what devices will be discovered by Cisco DNA Center by viewing the Cisco DNA Center Compatibility Matrix.
Understand that the preferred network latency between Cisco DNA Center and devices is 100 ms round-trip time (RTT). (The maximum latency is 200 ms RTT.)
Ensure that at least one SNMP credential is configured on your devices for use by Cisco DNA Center. At a minimum, this can be an SNMPv2C read credential.
Configure SSH credentials on the devices you want Cisco DNA Center to discover and manage. Cisco DNA Center discovers and adds a device to its inventory if at least one of the following criteria is met:
The account that is being used by Cisco DNA Center to SSH into your devices has privileged EXEC mode (level 15).
You configure the device’s enable password as part of the CLI credentials configured in the Discovery job. For more information, see Discovery Configuration Guidelines and Limitations.
When Cisco DNA Center discovers a device, it uses one of the device's IP addresses as the preferred management IP address. The IP address can be that of a built-in management interface of the device, another physical interface, or a logical interface such as Loopback0. You can configure Cisco DNA Center to use the device's loopback IP address as the preferred management IP address, provided the IP address is reachable from Cisco DNA Center.
When you choose Use Loopback IP as the preferred management IP address, Cisco DNA Center determines the preferred management IP address as follows:
If the device has one loopback interface, Cisco DNA Center uses that loopback interface IP address.
If the device has multiple loopback interfaces, Cisco DNA Center uses the loopback interface with the highest IP address.
If there are no loopback interfaces, Cisco DNA Center uses the Ethernet interface with the highest IP address. (Subinterface IP addresses are not considered.)
If there are no Ethernet interfaces, Cisco DNA Center uses the serial interface with the highest IP address.
After a device is discovered, you can update the management IP address from the Inventory window.
The following are the guidelines and limitations for Cisco DNA Center to discover your Cisco Catalyst 3000 Series Switches and Catalyst 6000 Series Switches:
Configure the CLI username and password with privileged EXEC mode (level 15). These credentials are the same CLI username and password that you configure in Cisco DNA Center for the Discovery function. Cisco DNA Center requires the highest access level to the device.
Explicitly specify the transport protocols allowed on individual interfaces for both incoming and outgoing connections. Use the transport input and transport output commands for this configuration. For information about these commands, see the command reference document for the specific device type.
Do not change the default login method for a device's console port and the VTY lines. If a device is already configured with a AAA (TACACS) login, make sure that the CLI credential defined in the Cisco DNA Center is the same as the TACACS credential defined in the TACACS server.
Cisco wireless controllers must be discovered using the management IP address instead of the service port IP address. If not, the related wireless controller 360 and AP 360 windows will not display any data.
Discovery credentials are the CLI, SNMPv2c, SNMPv3, HTTP(S), and NETCONF configuration values for the devices that you want to discover. You must specify the credentials based on the types of devices you are trying to discover:
Network devices: CLI and SNMP credentials.
 Note |
For NETCONF-enabled devices such as embedded wireless controllers, you must specify SSH credentials with admin privilege and select the NETCONF port. |
Compute devices (NFVIS): CLI, SNMP, and HTTP(S) credentials.
Because the various devices in a network can have different sets of credentials, you can configure multiple sets of credentials in Cisco DNA Center. The discovery process iterates through all sets of credentials that are configured for the Discovery job until it finds a set that works for the device.
If you use the same credential values for the majority of devices in your network, you can configure and save them to reuse in multiple Discovery jobs. To discover devices with unique credentials, you can add job-specific Discovery credentials when you run Discovery jobs. You can configure up to 10 global credentials for each credential type and define any five of them. If you need to define a job-specific credential, you can define five global credentials and one job-specific credential for each credential type.
To define credentials for a Discovery, click the menu icon ( ![]() ) and choose
. To continue, use the following procedures and discovery credential information:
) and choose
. To continue, use the following procedures and discovery credential information:
| Field | Description | ||
|---|---|---|---|
| Name/Description | Name or phrase that describes the CLI credentials. | ||
| Username | Name that is used to log in to the CLI of the devices in your network. | ||
| Password |
Password that is used to log in to the CLI of the devices in your network. For security reasons, re-enter the password as confirmation.
|
||
| Enable Password |
Password used to move to a higher privilege level in the CLI. Configure this password only if your network devices require it. For security reasons, re-enter the enable password.
|
|
Field |
Description |
||
|---|---|---|---|
|
Read |
|
||
|
Write |
|
|
Field |
Description |
||
|---|---|---|---|
|
Name/Description |
Name or description of the SNMPv3 settings that you are adding. |
||
| Username |
Name associated with the SNMPv3 settings. |
||
|
Mode |
Security level that an SNMP message requires. Choose one of the following modes:
|
||
|
Auth. Type |
Authentication type to be used. (Enabled if you select Authentication and Privacy or Authentication, No Privacy as Mode.) Choose one of the following authentication types:
|
||
|
Auth. Password |
SNMPv3 password used for gaining access to information from devices that use SNMPv3. These passwords (or passphrases) must be at least eight characters in length.
|
||
|
Privacy Type |
Privacy type. (Enabled if you select Authentication and Privacy as Mode.) Choose one of the following privacy types:
|
||
|
Privacy Password |
SNMPv3 privacy password that is used to generate the secret key for encrypting messages that are exchanged with devices that support encryption standards. Passwords (or passphrases) must be at least eight characters long.
|
| Field | Description |
|---|---|
| Retries | Number of times Cisco DNA Center tries to communicate with network devices using SNMP. |
| Timeout (in Seconds) | Amount of time, in seconds, between retries. |
|
Field |
Description |
|---|---|
|
Type |
Specifies the kind of HTTPS credentials you are configuring. Valid types are Read or Write. |
|
Read |
You can configure up to 10 HTTPS read credentials:
The password must contain between 7 and 128 characters, including at least one of the following:
The password cannot contain spaces or angle brackets (< >). Note that some Cisco IOS XE devices do not allow a question mark (?). |
|
Write |
You can configure up to 10 HTTPS write credentials:
The password must contain between 7 and 128 characters, including at least one of the following:
The password cannot contain spaces or angle brackets (< >). Note that some Cisco IOS XE devices do not allow a question mark (?). |
|
Field |
Description |
|---|---|
|
Port |
Port on the device. You can use one of the following ports:
|
You can discover devices using Cisco Discovery Protocol (CDP), an IP address range, or LLDP. This procedure shows you how to discover devices and hosts using CDP. For more information about the other discovery methods, see Discover Your Network Using an IP Address Range and Discover Your Network Using LLDP.
 Note |
|
Enable CDP on your network devices.
Configure your network devices, as described in Discovery Prerequisites.
Configure your network device's host IP address as the client IP address. (A host is an end-user device, such as a laptop computer or mobile device.)
|
Step 1 |
Click the menu icon ( |
||
|
Step 2 |
In the Discovery window, click |
||
|
Step 3 |
In the New Discovery window, enter a name in the Discovery Name field. |
||
|
Step 4 |
Expand the IP Address/Range area if it is not already visible, and configure the following fields: |
||
|
Step 5 |
Expand the Credentials area and choose any of the global credentials that have already been created or configure your own. If you want to use existing credentials, make sure that to select them. If you don't want to use a credential, deselect it. |
||
|
Step 6 |
To configure your own credentials, click Add Credentials. You must configure CLI and SNMP v2c credentials. All other credentials are optional. For field information, see Discovery Credentials. To save credentials for only the current job, click Save. To save them for the current job and future jobs, check the Save as global settings check box and then click Save. |
||
|
Step 7 |
To configure the protocols to be used to connect with devices, expand the Advanced area and do the following tasks: |
||
|
Step 8 |
Click Start.
The Discoveries window displays the results of your scan. The Discovery Details pane shows the status (active or inactive) and the Discovery configuration. The Discovery Devices pane displays the host names, IP addresses, and status of the discovered devices. |
You can discover devices using an IP address range, CDP, or LLDP. This procedure shows you how to discover devices and hosts using an IP address range. For more information about the other Discovery methods, see Discover Your Network Using CDP and Discover Your Network Using LLDP.
Your devices must have the required device configurations, as described in Discovery Prerequisites.
|
Step 1 |
Click the menu icon ( |
||
|
Step 2 |
Click |
||
|
Step 3 |
In the Discovery Name field, enter a name. |
||
|
Step 4 |
Expand the IP Address/Ranges area, if it is not already visible, and configure the following fields: |
||
|
Step 5 |
Expand the Credentials area and choose any of the global credentials that have already been created or configure your own. If you want to use existing credentials, make sure that to select them. If you don't want to use a credential, deselect it. |
||
|
Step 6 |
To configure your own credentials, click Add Credentials. You must configure CLI and SNMP v2c credentials. All other credentials are optional. For field information, see Discovery Credentials. To save credentials for only the current job, click Save. To save them for the current job and future jobs, check the Save as global settings check box and then click Save. |
||
|
Step 7 |
(Optional) To configure the protocols that are to be used to connect with devices, expand the Advanced area and do the following tasks: |
||
|
Step 8 |
Click Start.
The Discoveries window displays the results of your scan. The Discovery Details pane shows the status (active or inactive) and the Discovery configuration. The Discovery Devices pane displays the host names, IP addresses, and status of the discovered devices. |
You can discover devices using Link Layer Discovery Protocol (LLDP), CDP, or an IP address range. This procedure shows you how to discover devices and hosts using LLDP. For more information about the other discovery methods, see Discover Your Network Using CDP and Discover Your Network Using an IP Address Range.
 Note |
|
Enable LLDP on your network devices.
Configure your network devices, as described in Discovery Prerequisites.
Configure your network device's host IP address as the client IP address. (A host is an end-user device, such as a laptop computer or mobile device.)
|
Step 1 |
Click the menu icon ( |
||
|
Step 2 |
Click |
||
|
Step 3 |
In the Discovery Name field, enter a name. |
||
|
Step 4 |
Expand the IP Address/Range area if it is not already visible, and configure the following fields: |
||
|
Step 5 |
Expand the Credentials area and choose any of the global credentials that have already been created or configure your own. If you want to use existing credentials, make sure that to select them. If you don't want to use a credential, deselect it. |
||
|
Step 6 |
To configure your own credentials, click Add Credentials. You must configure CLI and SNMP v2c credentials. All other credentials are optional. For field information, see Discovery Credentials. To save credentials for only the current job, click Save. To save them for the current job and future jobs, check the Save as global settings check box and then click Save. |
||
|
Step 7 |
(Optional) To configure the protocols to be used to connect with devices, expand the Advanced area and do the following tasks:
|
||
|
Step 8 |
Click Start.
The Discoveries window displays the results of your scan. The Discovery Details pane shows the status (active or inactive) and the Discovery configuration. The Discovery Devices pane displays the host names, IP addresses, and status of the discovered devices. |
The following sections provide information about how to manage the Discovery jobs.
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
In the Discovery window, click View All Discoveries. |
|
Step 3 |
To stop an active Discovery job, perform these steps:
|
|
Step 4 |
To restart an inactive Discovery job, perform these steps:
|
You can clone a Discovery job and retain all the information defined for that job.
You should have run at least one Discovery job.
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
In the Discovery window, click View All Discoveries. |
|
Step 3 |
In the left pane, click a Discovery job. |
|
Step 4 |
In the bottom pane, click Copy & Edit. Cisco DNA Center creates a copy of the Discovery job, named Clone of Discovery_Job . |
|
Step 5 |
(Optional) To change the name of the Discovery job, replace the default name in the Discovery Name field with a new name. |
|
Step 6 |
Define or update the parameters for the new Discovery job. |
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
In the Discovery window, click View All Discoveries. |
|
Step 3 |
In the left pane, click the Discovery job that you want to delete. |
|
Step 4 |
In the bottom pane, click Delete. |
|
Step 5 |
Click OK to confirm. |
You can view information about a Discovery job, such as the settings and credentials that were used. You also can view the historical information about each Discovery job that was run, including information about the specific devices that were discovered or that failed to be discovered.
Run at least one Discovery job.
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
In the Discovery window, click All discoveries page from previous release. |
|
Step 3 |
In the left Discoveries pane, select the Discovery job. Alternatively, use the Search function to find a Discovery job by device IP address or name. |
|
Step 4 |
Click the down arrow next to one of the following areas for more information:
|
You can create a network hierarchy that represents your network's geographical locations. The hierarchical organization enables you to easily apply design settings or configurations to a specific hierarchical element. For example, you can apply design settings to an entire area or to only a floor.
You can name hierarchical elements to help you identify where to apply design settings later.
The hierarchical elements that you can create have rules that dictate under which elements they can reside and which elements can reside under them.
Global: Default element under which all other hierarchical elements reside. are the only elements that can reside directly under Global.
Areas and Sites: Areas and sites reside under Global or under other areas or sites. They do not have a physical address. As the largest element, they identify a geographic region. They provide a way to group areas and sites.
Buildings: Buildings reside under areas or sites. When you create a building, you need to specify a physical address or latitude and longitude coordinates. Buildings can't contain areas. However, they can contain floors.
Floors: Floors reside under buildings. You can add floors to buildings with or without maps that contain various building components, like walls and windows. If you decide to use floor maps, you can manually create them or import them from files, such as DXF, DWG, JPG, GIF, PNG, or PDF file types. Then you can position your wireless devices on the floor maps to visualize your wireless network coverage.
You can change the site hierarchy for unprovisioned devices while preserving AP locations on floor maps. Note, however, that you can't move an existing floor to a different building.
To get started, build your network hierarchy using one of the following methods:
Create a new network hierarchy. For more information, see Create a New Network Hierarchy.
Import an existing network hierarchy from Cisco Prime Infrastructure or Ekahau Pro. For more information, see the Cisco DNA Center User Guide.Use an Existing Cisco Network Hierarchy or Use an Existing Ekahau Network Hierarchy.
Create a new network hierarchy by creating new sites (or areas), building, and floors.
Cisco DNA Center allows you to easily define physical sites and then specify common resources for those sites. The Design area uses a hierarchical format for intuitive use, while eliminating the need to redefine the same resource in multiple places when provisioning devices. By default, there is one site called Global. You can add more sites, buildings, and areas to your network hierarchy. You must create at least one site before you can use the provision features.
|
Step 1 |
Click the menu icon ( A world map appears in the right pane. |
||||||||
|
Step 2 |
From this window, you can add, edit, and delete sites. See the following table for details.
|
|
Step 1 |
Click the menu icon ( |
||||||||
|
Step 2 |
From this window, you can add, edit, and delete a building. See the following table for details.
|
After you add a building, you can add floors to it. You can add a basic floor that doesn't have a floor map and add the floor map later, or you can add a floor and include a floor map at the same time.
To add a basic floor to a building, use this procedure.
To add a floor and a floor map at the same time, see the Cisco DNA Center User Guide.:
|
Step 1 |
Click the menu icon ( |
||||||||
|
Step 2 |
From this window, you can add, edit, and delete a floor. See the following table for details.
|
If you have an existing network hierarchy in Cisco Prime Infrastructure, you can export it and then import it into Cisco DNA Center, saving time and effort spent in creating a new network hierarchy.
The following information is available for you to re-create your network hierarchy:
Site Hierarchy: Your existing site hierarchy is downloaded in a CSV file format. The CSV file contains details such as site names, parent hierarchy, number of floors, location, and site address.
Map Archive: Map information is downloaded as a map archive in a TAR file format. The map archive file contains data such as the date and time, number of floors, and APs. Depending on what you choose to download, the map archive can also include map information, such as floor dimensions (length, width, and height) and details about the APs and overlay objects that have been placed on the floor maps. You can also choose to download calibration information, such as the RF attenuation model that has been applied to each floor.
You can choose to base the map archive on the global hierarchy or the hierarchy of a single site, building, or floor, as follows:
Site: The chosen site and all of its subsites, buildings, and floors are exported.
Building: The chosen building and all of its floors are exported.
Floor: The chosen floor is exported.
 Note |
Cisco DNA Center supports the United States' Federal Information Processing Standards (FIPS). FIPS is an optional mode that can be enabled when installing the Cisco DNA Center image. By default, FIPS mode is disabled. |
FIPS mode has the following impact on the export and import of map archives.
If FIPS mode is enabled:
Exported map archives are unencrypted.
Only unencrypted map archives can be imported.
If FIPS mode is disabled:
Exported map archives are encrypted.
Both encrypted and unencrypted map archives can be imported.
For details, see the Cisco DNA Center User Guide.
You can export your site hierarchy from Cisco Prime Infrastructure in a CSV file format. The CSV file contains details such as site names, parent hierarchy, number of floors, location, and site address.
Site hierarchy export is supported in Cisco Prime Infrastructure, Release 3.2 and later.
|
Step 1 |
In Cisco Prime Infrastructure, choose . |
|
Step 2 |
In the Device Groups window, click Export Groups. |
|
Step 3 |
In the Export Groups dialog box, click the APIC-EM radio button. |
|
Step 4 |
To download the CSV file, click OK. |
You can export map archive files from Cisco Prime Infrastructure and import them into Cisco DNA Center. Map archives contain map information, such as floor dimensions, and calibration information, such as the Radio Frequency (RF) attenuation model that has been applied to each floor in Cisco Prime Infrastructure.
|
Step 1 |
From the Cisco Prime Infrastructure GUI, choose . |
|
Step 2 |
From the Export drop-down list, choose Map Archive. The Export Map Archive window opens, and the Select Sites window opens by default. |
|
Step 3 |
Check the check box adjacent to a specific site, campus, building, or floor that you want to export. Alternatively, check the Select All check box to export all the maps. |
|
Step 4 |
Select at least one of the following options:
|
|
Step 5 |
Click Generate Map Archive. The following message shows the progress of the operation: Exporting data is in progressA TAR file is created and is saved to your local machine. |
|
Step 6 |
Click Done. |
You can import a site hierarchy that you exported from Cisco Prime Infrastructure as a CSV file. For information about exporting the site hierarchy, see the Cisco DNA Center User Guide.
Make sure that you have Cisco Wireless Controllers and APs in your Cisco DNA Center inventory. If not, discover them using the Discovery feature.
Add and position APs on a floor map.
If you manually created sites in Cisco DNA Center that are present in Cisco Prime Infrastructure, you must remove them from Cisco DNA Center before you can import them.
|
Step 1 |
Click the menu icon ( |
||
|
Step 2 |
From the map tool bar, click Import and choose Import Sites. |
||
|
Step 3 |
In the dialog box, click one of the following radio buttons:
|
||
|
Step 4 |
In the dialog box, drag and drop your CSV file into the download area. Alternatively, you can click Choose a file and navigate to where your CSV file is located, then click Upload.
|
You can import a map archive TAR file into Cisco DNA Center. For example, you can upload the TAR file that you exported from Cisco Prime Infrastructure.
 Note |
Cisco DNA Center supports the United States' Federal Information Processing Standards (FIPS). FIPS is an optional mode that can be enabled when installing the Cisco DNA Center image. By default, FIPS mode is disabled. |
For information about exporting site hierarchy, see Export Your Map Archive from Cisco Prime Infrastructure.
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
From the map toolbar, click Import and choose Import Maps. |
|
Step 3 |
In the Import Maps dialog box, drag and drop the map archive file. |
|
Step 4 |
Click Import. The map archive file is imported. |
The Ekahau Pro tool allows you to create a complete network plan for your enterprise, including floor layout, AP locations, and obstacles. After creating the floor layout, you can export the simulated network plan as an Ekahau project file. You can also export the real-world site survey data into a format that Cisco DNA Center can use.
You can export your network hierarchy from Ekahau Pro and import it into Cisco DNA Center for further planning.
Cisco DNA Center supports Ekahau Pro tool version 10.2.
|
Step 1 |
In the Ekahau Pro tool, plan the floor layout:
|
|
Step 2 |
Deploy the planned APs at locations designed on the floor layout.
|
|
Step 3 |
In Cisco DNA Center, configure the Cisco Wireless Controller .
|
|
Step 4 |
Import the Ekahau project into Cisco DNA Center. |
|
Step 5 |
Map the planned APs to real APs in Cisco DNA Center. |
|
Step 1 |
Click the menu icon ( |
||
|
Step 2 |
Design your network hierarchy by adding sites, buildings, and floors.
|
||
|
Step 3 |
In the left pane, hover your cursor over the ellipsis The Import Ekahau Project dialog box appears. |
||
|
Step 4 |
Drag and drop the ESX file into the boxed area in the Import Ekahau Project dialog box, or click the click to select link and browse to the ESX file.
|
||
|
Step 5 |
If an AP is not found in the inventory and remains unmapped, the planned AP is retained on the floor. To see the reason for the mismatch, hover your cursor over the planned AP icon on the floor map, and click Import History. The following attempts are made to map the planned APs to real APs:
|
||
|
Step 6 |
To manually assign the planned AP to a real AP, hover your cursor over the planned AP icon on the floor map, and click . The Assign Planned APs panel appears. |
||
|
Step 7 |
In the Assign Planned APs panel, map the planned AP to a real AP by AP name, AP type, or All APs. |
||
|
Step 8 |
Click the radio button next to the AP Name, and click Assign to manually assign the planned AP. |
||
|
Step 9 |
Click Save. |
You can upload an Ekahau site survey to create the buildings and floors in your network hierarchy. The site survey includes information about wireless devices, including the site, building, and floor to which it is assigned and its position on the floor map. However, it doesn't include the AP antenna information. So, you need to upload this information separately using a CSV file.
Cisco DNA Center includes a CSV template file that you can download and edit to define the required AP antenna information.
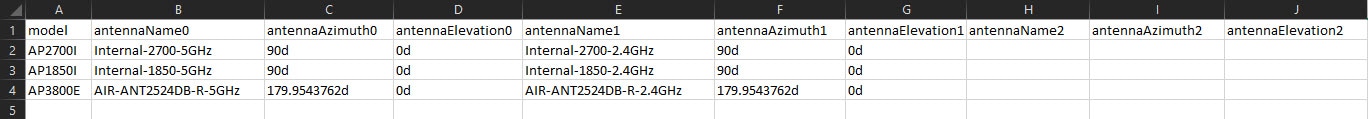
If an AP isn't in the Cisco DNA Center device inventory, it's imported as a planned AP. However, you can use a naming convention so that when you add an AP to the device inventory, Cisco DNA Center can automatically convert it to an actual AP.
The naming convention is AP, followed by the last four digits of the AP's MAC address, for example, AP-c4:e0. Using this information, Cisco DNA Center attempts to match the provided digits with the last four digits of an AP's Ethernet MAC or radio MAC address. If this information isn't available or a match is unsuccessful, Cisco DNA Center attempts to match AP names.
|
Step 1 |
Click the menu icon ( |
||
|
Step 2 |
Click Add Site > Add Area. Alternatively, you can hover your cursor over the ellipsis |
||
|
Step 3 |
In the left pane, hover your cursor over the ellipsis |
||
|
Step 4 |
In the Import Ekahau Survey dialog box, drag and drop the Ekahau Survey file into the Ekahau Survey boxed area, or click the Choose a file link and browse to the ESX file. |
||
|
Step 5 |
Drag and drop the CSV file into the AP Mapping CSV boxed area, or click the Choose a file link and browse to the CSV file.
|
||
|
Step 6 |
Click Import. After the files are successfully downloaded, a success message is displayed. |
||
|
Step 7 |
Click View Hierarchy and navigate to the floors to verify that the devices have been imported and positioned properly. Hover the cursor over a device to view its details. |
In 2D maps, you can configure devices and overlay objects on your floor maps. The Cisco DNA Assurance User Guide provides basic guidance on working with 2D maps. In addition to 2D maps, Cisco DNA Center supports 3D maps with more capabilities. For a full description of both 2D and 3D map features, see the Cisco DNA Center User Guide.
APs: An access point (AP) serves as the connection point between wireless and wired networks or as the center point of a stand-alone wireless network. In 2D maps, an AP represents an actual, installed device. For a list of APs that Cisco DNA Center supports, see the Cisco DNA Center Compatibility Matrix.
Planned APs: Planned APs are representations of APs that have not been installed yet. By placing planned APs on a map, you can envision your wireless network RF coverage and make changes before you actually install the APs.
Sensors: A sensor is a dedicated Cisco Aironet 1800S Active Sensor that gets bootstrapped using Cisco PnP. After it obtains the Assurance server reachability details, it communicates directly with the Assurance server. For more details, including information about sensor tests, see the Manage Sensors and Sensor-Driven Tests.
Coverage Areas: By default, any area defined as part of a floor map is considered as a wireless coverage area. However, if you have a building that is nonrectangular or you want to mark a nonrectangular or polygon-shaped area on a floor, you can use the Coverage Areas drawing tool to create a coverage area.
Openings: An opening, also called an atrium, is an open-air or skylight-covered area within a building. An opening can extend through multiple floors and can affect wireless signal coverage areas.
Location Regions: Location regions define areas that are included in or excluded from the computation of heatmaps. Inclusion areas are included in the calculations. and exclusion areas are not included. For example, you might want to exclude areas such as openings, atriums, or stairwells within a building, but include a work area, such as cubicles, labs, or manufacturing floors.
Walls: Walls are exterior or interior vertical structures in a building and can be made of different materials and thicknesses. As such, they affect how heatmaps are calculated.
Shelving Units: Shelving units are obstacles that affects signal attenuation. An example of a location with shelving units would be a high-ceiling warehouse.
Markers: A marker identifies a location on a map. When you create a marker, you can name it and position it to help you identify it later.
GPS Markers: When integrated with Cisco DNA Center, location services, such as Cisco DNA Spaces or Cisco Connected Mobile Experiences (CMX), use GPS markers to calculate the approximate geographical location of clients.
Align Points: Align points are markers that are used to position multiple floors that have different physical shapes. In 3D maps, floors are aligned at the top-left corner of the map (point 0,0). If you manage each floor independently, the misalignment is not a problem. However, to use some of the features of 3D maps, the floors need to be aligned as they are in reality. To compensate this misalignment, you can insert one or more align points on two or more floors, so that the floors align properly one on top of the other in a 3D map.
|
Step 1 |
Click the menu icon ( |
||||||||||
|
Step 2 |
In the left hierarchy tree, choose a floor. |
||||||||||
|
Step 3 |
From the map toolbar, click . |
||||||||||
|
Step 4 |
From this window, you can add, position, edit, and remove APs. See the following table for details.
|
Make sure you have the Cisco AP 1800S sensor in your inventory. The Cisco Aironet 1800s Active Sensor must be provisioned using Plug and Play for it to show up in the Inventory.
|
Step 1 |
Click the menu icon ( |
||||||
|
Step 2 |
From the left hierarchy tree, choose a floor. |
||||||
|
Step 3 |
From the map toolbar, click . |
||||||
|
Step 4 |
From this window, you can add, position, edit, and remove sensors. See the following table for details.
|
This procedure shows you how to mark a nonrectangular or polygon-shaped area as a coverage area on a floor map.
For more information about coverage areas, see Configure 2D Floor Map Devices and Overlay Objects.
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
From the left hierarchy tree, choose a floor. |
|
Step 3 |
In the map toolbar, click . |
|
Step 4 |
To add a coverage area, do the following: |
|
Step 5 |
To edit a coverage area, do the following:
|
|
Step 6 |
To delete a coverage area, do the following:
|
|
Step 7 |
In the map toolbar, click Save. |
Creating an opening is similar to creating an open space or atrium on a floor. On multifloor buildings, typically the opening extends vertically through multiple floors. This procedure shows you how to add, edit, and remove openings on a floor map. It also shows you how to copy openings to other floors.
For more information about openings, see Configure 2D Floor Map Devices and Overlay Objects.
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
From the left hierarchy tree, choose a floor. |
|
Step 3 |
In the map toolbar, click . |
|
Step 4 |
To add an opening, do the following: |
|
Step 5 |
To edit an opening, do the following:
|
|
Step 6 |
To copy an opening from one floor to another, do the following:
|
|
Step 7 |
To remove an opening, do the following:
|
|
Step 8 |
In the map toolbar, click Save. |
Location regions are areas on the map that are either included in or excluded from the heatmap calculation. The following topics show you how to add, edit, and remove location regions.
This procedure shows you how to add, edit, and remove an inclusion region. Use the following guidelines to define an inclusion region on a floor map:
Inclusion regions can be any polygon-shaped area and must have at least three points.
You can only define one inclusion region on a floor. By default, an inclusion region is defined for each floor area when it is created. The inclusion region is indicated by a solid aqua line, and generally outlines the entire floor area.
For more information about inclusion regions, see Configure 2D Floor Map Devices and Overlay Objects.
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
From the left hierarchy tree, choose a floor. |
|
Step 3 |
In the map toolbar, click . |
|
Step 4 |
In the left pane of the map, click the Inclusion icon. |
|
Step 5 |
To create an inclusion region, use the drawing tool: |
|
Step 6 |
To edit the location of an inclusion region, drag and drop the shape to the new location. |
|
Step 7 |
To remove an inclusion region, right-click the shape and choose Remove. |
|
Step 8 |
In the map toolbar, click Save. |
This procedure shows you how to add, edit, and remove an exclusion region. Use the following guidelines to define exclusion regions on a floor map:
Exclusion regions can be any polygon-shaped area and must have at least three points.
Exclusion regions are defined within the borders of an inclusion region.
You can define multiple exclusion regions on a floor map.
For more information about exclusion regions, see Configure 2D Floor Map Devices and Overlay Objects.
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
From the left hierarchy tree, choose a floor. |
|
Step 3 |
In the map toolbar, click . |
|
Step 4 |
From the left pane of the map, click the Exclusion icon. |
|
Step 5 |
To create an exclusion region, use the drawing tool: |
|
Step 6 |
To edit the location of an exclusion region, drag and drop the shape to the new location. |
|
Step 7 |
To remove an exclusion region, right-click the shape and choose Remove. |
|
Step 8 |
In the map toolbar, click Save. |
This procedure shows you how to add, edit, move, and remove walls on a floor map.
For more information about walls, see Configure 2D Floor Map Devices and Overlay Objects.
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
From the left hierarchy tree, choose a floor. |
|
Step 3 |
In the map toolbar, click . |
|
Step 4 |
To add walls, do the following: |
|
Step 5 |
To change a wall type, and depending on the wall type also configure its parameters, do the following: |
|
Step 6 |
To move a wall, do the following: |
|
Step 7 |
To remove a wall, right-click the wall and choose Remove. |
|
Step 8 |
In the map toolbar, click Save. |
This procedure shows you how to add, copy, edit, and remove shelving units on a floor map.
For information about shelving units, see Configure 2D Floor Map Devices and Overlay Objects.
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
From the left hierarchy tree, choose a floor. |
|
Step 3 |
In the map toolbar, click . |
|
Step 4 |
To add shelving units, do the following: |
|
Step 5 |
To create a copy or an array of a shelving unit, do one of the following:
|
|
Step 6 |
To edit the name, dimensions, orientation, and whether it is two-sided, right-click the shelving unit and choose Edit. |
|
Step 7 |
To remove a shelving unit, right-click the shelving unit and choose Remove. |
|
Step 8 |
In the map toolbar, click Save. |
The following procedure shows you how to add, edit, and remove markers.
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
From the left hierarchy tree, choose a floor. |
|
Step 3 |
In the map toolbar, click . |
|
Step 4 |
In the left pane of the map, click the Markers icon. |
|
Step 5 |
In the Place Markers dialog box, enter the name for the marker, and click Add Marker. |
|
Step 6 |
To place the marker, click the map where you want to place the marker. |
|
Step 7 |
To move a marker, hover your cursor over the marker until it turns blue. Then drag and drop it in the new location. |
|
Step 8 |
To edit a marker, right-click the marker and choose Edit. |
|
Step 9 |
To remove a marker, right-click the marker and choose Remove. |
|
Step 10 |
In the map toolbar, click Save. |
This procedure shows you how to add, edit, and remove GPS markers. For more information about GPS markers, see Configure 2D Floor Map Devices and Overlay Objects.
 Note |
The GPS marker is an attribute of the building. You can apply it to all the floors of the building. |
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
From the left hierarchy tree, choose a floor. |
|
Step 3 |
In the map toolbar, click . |
|
Step 4 |
To add a GPS marker, do the following: |
|
Step 5 |
To edit a GPS marker, right-click the GPS marker and choose Edit. |
|
Step 6 |
To remove a GPS marker, right-click the GPS marker and choose Remove. |
|
Step 7 |
In the map toolbar, click Save. |
This procedure shows you how to add, edit, and remove align points. For more information about align points, see Configure 2D Floor Map Devices and Overlay Objects.
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
From the left hierarchy tree, choose a floor. |
|
Step 3 |
In the map toolbar, click . |
|
Step 4 |
To add an alignment point, do the following:
|
|
Step 5 |
To edit the name of an alignment point, do the following:
|
|
Step 6 |
To change the location of an alignment point, do the following:
|
|
Step 7 |
To remove an alignment point, right-click the alignment point and choose Remove. |
|
Step 8 |
In the map toolbar, click Save. |
The Inventory function retrieves and saves details, such as host IP addresses, MAC addresses, and network attachment points about devices in its database.
The Inventory function retrieves and saves details, such as host IP addresses, MAC addresses, and network attachment points about devices in its database.
The Inventory feature can also work with the Device Controllability feature to configure the required network settings on devices, if these settings are not already present on the device.
Inventory uses the following protocols, as required:
Link Layer Discovery Protocol (LLDP).
IP Device Tracking (IPDT) or Switch Integrated Security Features (SISF). (IPDT or SISF must be enabled on the device.)
LLDP Media Endpoint Discovery. (This protocol is used to discover IP phones and some servers.)
Network Configuration Protocol (NETCONF). For a list of devices, see Discovery Prerequisites.
After the initial discovery, Cisco DNA Center maintains the inventory by polling the devices at regular intervals. The default interval is every 24 hours. However, you can change this interval as required for your network environment. For more information, see Update the Device Polling Interval. Also, a configuration change in the device triggers an SNMP trap, which in turn triggers device resynchronization. Polling occurs for each device, link, host, and interface. Only the devices that have been active for less than one day are displayed. This prevents stale device data, if any, from being displayed. On average, polling 500 devices takes approximately 20 minutes.
You can update the polling interval at the global level for all devices by choosing or at the device level for a specific device by choosing Device Inventory. When you set the polling interval using the Network Resync Interval, that value takes precedence over the Device Inventory polling interval value.
If you do not want a device to be polled, you can disable polling.
Make sure that you have devices in your inventory. If not, discover devices using the Discovery feature.
|
Step 1 |
Click the menu icon ( |
||
|
Step 2 |
Select the devices that you want to update. |
||
|
Step 3 |
From the Actions drop-down list, choose . |
||
|
Step 4 |
In the Edit Device slide-in pane, click Resync Interval. |
||
|
Step 5 |
Select the resync type.
|
||
|
Step 6 |
In the Resync Interval (in Mins) field, enter the time interval (in minutes) between successive polling cycles. |
||
|
Step 7 |
Click Update. |
The Inventory table displays information for each discovered device. Click the column header to sort the rows in ascending order. Click the column header again to sort the rows in descending order.
To choose which columns to display or to hide in the table, click ![]() . Note that the column selection does not persist across sessions.
. Note that the column selection does not persist across sessions.
When you select devices and choose a different view from the Focus drop-down list, your selection persists in each new view.
If you choose the Default view from the Focus drop-down list, the Inventory table displays only the Device Name, IP Address, Device Family, and MAC Address of the listed devices.
By default, 25 entries are shown in the Inventory table. Click Show More to view more entries. You can view up to 500 entries in the Inventory table.
If there are more than 25 entries in the Inventory table and you choose a different view from the Focus drop-down list, the same number of entries is displayed in each new view.
Make sure that you have devices in your inventory. If not, discover devices using the Discovery feature.
|
Click the menu icon (
|
You can delete devices from the Cisco DNA Center database, as long as they have not already been added to a site.
When you remove a wireless sensor from the inventory, the sensor is reset to the factory defaults so that when it rejoins, it gets the current configuration.
You must have administrator (ROLE_ADMIN) permissions and access to all devices (RBAC Scope set to ALL) to perform this procedure.
|
Step 1 |
Click the menu icon ( |
||
|
Step 2 |
Check the check box next to the device or devices that you want to delete.
|
||
|
Step 3 |
From the Actions drop-down list, choose . |
||
|
Step 4 |
In the Warning window, check the Config Clean-Up check box to remove the network settings and telemetry configuration from the selected device. |
||
|
Step 5 |
Confirm the action by clicking OK. |
|
Step 1 |
Click the menu icon ( |
||||
|
Step 2 |
Check the check box for the devices that you want to assign to a site. |
||||
|
Step 3 |
From the Actions menu, choose . |
||||
|
Step 4 |
In the Assign Device to Site slide-in pane, click the link next to the |
||||
|
Step 5 |
In the Choose a floor slide-in pane, select the floor to assign to the device and click Save. |
||||
|
Step 6 |
(Optional) If you select multiple devices to add to the same location, check the Apply to All check box for the first device to assign its location to the rest of the devices and click Next. |
||||
|
Step 7 |
Check Application and Endpoint Visibility is enabled on all applicable devices. Check this to skip enabling it on all devices check box.
|
||||
|
Step 8 |
Review summery settings and click Next. |
||||
|
Step 9 |
In the Task Name name field, enter a task name of your choice. |
||||
|
Step 10 |
Choose whether you want to assign the device to a site Now or schedule it for later. |
||||
|
Step 11 |
Click Assign. |
||||
|
Step 12 |
To preview the CLI configuration, click the Generate Configuration Preview radio button and do the following:
|
||||
|
Step 13 |
When assigning devices to a site, if Device Controllability is enabled, a workflow is automatically triggered to push the device configuration from the site to the devices. |
If your network uses Cisco ISE for user authentication, you can configure Cisco DNA Center for Cisco ISE integration. This enables you to see more information about wired clients, such as the username and operating system.
Cisco ISE configuration is centralized within NCP (Network Control Platform), which enables you to configure Cisco ISE at one GUI location. The workflow for configuring Cisco ISE is as follows:
Click the menu icon (![]() ) and choose , and enter the Cisco ISE server details.
) and choose , and enter the Cisco ISE server details.
After the Cisco ISE server is successfully added, NCP establishes a connection with NDP (Network Data Platform) and sends the details of the pxGrid nodes, keystore, and truststore files.
NDP uses the configuration received from NCP to establish a pxGrid session.
NCP automatically detects pxGrid node failovers, persona moves, and communicates it to NDP.
If there are ISE deployment changes, NDP starts a new pxGrid session with a new pxGrid ACTIVE node.
Cisco DNA Center uses AAA servers for user authentication and Cisco ISE for both user authentication and access control. Use this procedure to configure AAA servers, including Cisco ISE.
If you are using Cisco ISE to perform both policy and AAA functions, make sure that Cisco DNA Center and Cisco ISE are integrated.
If you are using another product (not Cisco ISE) to perform AAA functions, make sure to do the following:
Register Cisco DNA Center with the AAA server, including defining the shared secret on both the AAA server and Cisco DNA Center.
Define an attribute name for Cisco DNA Center on the AAA server.
For a Cisco DNA Center multihost cluster configuration, define all individual host IP addresses and the virtual IP address for the multihost cluster on the AAA server.
Before you configure Cisco ISE, confirm that:
You have deployed Cisco ISE on your network. For information on supported Cisco ISE versions, see the Cisco DNA Center Compatibility Matrix. For information on installing Cisco ISE, see the Cisco Identity Services Engine Install and Upgrade guides.
If you have a standalone ISE deployment, you must integrate Cisco DNA Center with the Cisco ISE node and enable the pxGrid service and External RESTful Services (ERS) on that node.
 Note |
Although pxGrid 2.0 allows up to four pxGrid nodes in the Cisco ISE deployment, Cisco DNA Center releases earlier than 2.2.1.x do not support more than two pxGrid nodes. |
If you have a distributed Cisco ISE deployment:
You must integrate Cisco DNA Center with the primary policy administration node (PAN), and enable ERS on the PAN.
 Note |
We recommend that you use ERS through the PAN. However, for backup, you can enable ERS on the PSNs. |
You must enable the pxGrid service on one of the Cisco ISE nodes within the distributed deployment. Although you can choose to do so, you do not have to enable pxGrid on the PAN. You can enable pxGrid on any Cisco ISE node in your distributed deployment.
The PSNs that you configure in Cisco ISE to handle TrustSec or SD Access content and PACs must also be defined in . For more information, see the Cisco Identity Services Engine Administrator Guide.
You must enable communication between Cisco DNA Center and Cisco ISE on the following ports: 443, 5222, 8910, and 9060.
The Cisco ISE host on which pxGrid is enabled must be reachable from Cisco DNA Center on the IP address of the Cisco ISE eth0 interface.
The Cisco ISE node can reach the fabric underlay network via the appliance's NIC.
The Cisco ISE admin node certificate must contain the Cisco ISE IP address or FQDN in either the certificate subject name or the Subject Alternative Name (SAN).
The Cisco DNA Center system certificate must list both the Cisco DNA Center appliance IP address and FQDN in the SAN field.
 Note |
For Cisco ISE 2.4 Patch 13, 2.6 Patch 7, and 2.7 Patch 3, if you are using the Cisco ISE default self-signed certificate as the pxGrid certificate, Cisco ISE might reject that certificate after applying those patches. This is because the older versions of that certificate have the Netscape Cert Type extension specified as the SSL server, which now fails (because a client certificate is required). This issue does not occur in Cisco ISE 3.0 and later. For more information, see the Cisco ISE Release Notes. |
|
Step 1 |
Click the menu icon ( |
||||
|
Step 2 |
From the Add drop-down list, choose AAA or ISE. |
||||
|
Step 3 |
To configure the primary AAA server, enter the following information:
|
||||
|
Step 4 |
To configure a Cisco ISE server, enter the following details:
|
||||
|
Step 5 |
Click Advanced Settings and configure the settings:
|
||||
|
Step 6 |
Click Add. |
||||
|
Step 7 |
To add a secondary server, repeat the preceding steps. |
With Cisco DNA Center, you can configure global network settings when devices are assigned to a specific site. Telemetry polls network devices and collects telemetry data according to the settings in the SNMP server, syslog server, NetFlow Collector, or wired client.
Create a site and assign a device to the site. See Create, Edit and Delete a Site.
|
Step 1 |
Click the menu icon ( |
||
|
Step 2 |
In the SNMP Traps area, do one of the following:
|
||
|
Step 3 |
In the Syslogs area, do one of the following:
|
||
|
Step 4 |
In the NetFlow area, do one of the following:
|
||
|
Step 5 |
In the Wired Endpoint Data Collection area, click the Enable Cisco DNA Center Wired Endpoint Data Collection At This Site radio button to turn on IP Device Tracking (IPDT) on the access devices of the site. If you don't want to enable IPDT for the site, click the Disable radio button (the default).
|
||
|
Step 6 |
In the Wireless Controller, Access Point and Wireless Clients Health area, check the Enable Wireless Telemetry check box to monitor the health of the wireless controllers, APs, and wireless clients in your network. |
||
|
Step 7 |
Click Save. |
Use this procedure to enable the Cisco AI Analytics features to exports network event data from network devices as well as inventory, site hierarchy, and topology data to the Cisco AI Cloud.
Make sure that you have the Cisco DNA Advantage software license for Cisco DNA Center. The AI Network Analytics application is part of the Cisco DNA Advantage software license.
Make sure that the latest version of the AI Network Analytics application is installed. See the "Download and Install Packages and Updates" topic in the Cisco Digital Network Architecture Center Administrator Guide.
Make sure that your network or HTTP proxy is configured to allow outbound HTTPS (TCP 443) access to the following cloud hosts:
api.use1.prd.kairos.ciscolabs.com (US East Region)
api.euc1.prd.kairos.ciscolabs.com (EU Central Region)
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
Scroll down to External Services and choose Cisco AI Analytics. 
|
|
Step 3 |
Do one of the following:
|
|
Step 4 |
In the Success dialog box, click Okay. |
|
Step 5 |
(Recommended) In the AI Network Analytics window, click Download Configuration file. |
To disable Cisco AI Network Analytics data collection, you must disable the AI Network Analytics feature, as follows:
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
Scroll down to External Services and choose Cisco AI Analytics. |
|
Step 3 |
In the AI Network Analytics area, click the Enable AI Network Analytics toggle button so that it is unchecked ( |
|
Step 4 |
Click Update. |
|
Step 5 |
To delete your network data from the Cisco AI Network Analytics cloud, contact the Cisco Technical Response Center (TAC) and open a support request. |
|
Step 6 |
(Optional) If you have misplaced your previous configuration, click Download configuration file. |
Machine Reasoning knowledge packs are step-by-step workflows that are used by the Machine Reasoning Engine (MRE) to identify security issues and improve automated root cause analysis. These knowledge packs are continuously updated as more information is received. The Machine Reasoning Knowledge Base is a repository of these knowledge packs (workflows). To have access to the latest knowledge packs, you can either configure Cisco DNA Center to automatically update the Machine Reasoning Knowledge Base on a daily basis, or you can perform a manual update.
|
Step 1 |
Click the menu icon ( |
|
Step 2 |
Scroll down to External Services and choose Machine Reasoning Knowledge Base.
When there is a new update to the Machine Reasoning Knowledge Base, the AVAILABLE UPDATE area appears in the Machine Reasoning Knowledge Base window, which provides the Version and Details about the update.
|
|
Step 3 |
(Recommended) Check the AUTO UPDATE check box to automatically update the Machine Reasoning Knowledge Base. You can perform an automatic update only if Cisco DNA Center is successfully connected to the Machine Reasoning Engine in the cloud. |
|
Step 4 |
To manually update the Machine Reasoning Knowledge Base in Cisco DNA Center, do one of the following:
|
|
Step 5 |
Check the CISCO CX CLOUD SERVICE FOR NETWORK BUG IDENTIFIER AND SECURITY ADVISORY check box to enable Cisco CX Cloud connection with network bug identifier and security advisory. |
|
Step 6 |
In the Security Advisories Settings area click the RECURRING SCAN toggle button to enable or disable the weekly recurring scan. |
|
Step 7 |
Click the CISCO CX CLOUD toggle button to enable or disable the Cisco CX cloud. |
You can view the Cisco DNA Center GUI windows in English (the default), Chinese, Japanese, or Korean.
To change the default language, perform the following task:
|
Step 1 |
In your browser, change the locale to one of the supported languages: Chinese, Japanese, or Korean.
|
|
Step 2 |
Log in to Cisco DNA Center. The GUI is shown in the selected language. |