Cisco Secure Workload Platform Data Sheet
Available Languages
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
Cisco Secure Workload (formerly Tetration) seamlessly delivers zero trust microsegmentation across any workload, environment, or location from a single console. With comprehensive visibility into every workload interaction and powerful AI/ML driven automation, Secure Workload reduces the attack surface by preventing lateral movement, identifies workload behavior anomalies, helps rapidly remediate threats, and continuously monitors compliance.
Traditionally in IT, we’ve had an infrastructure-centric view of the universe. Our most valuable data was contained in the data center, so our job was to let good traffic in and keep bad actors out. And our tool of choice was the firewall.
In today’s organizations, the center of gravity has shifted decidedly in favor of applications. Applications are critical to how you engage with customers, run your operations, and get paid. But the constant proliferation and dynamic nature of these applications have led to an unprecedented security challenge for IT professionals.
Applications are distributed. They’re deployed both on-premises and in the cloud, or across multiple clouds, and critical workloads are no longer tidily kept in the data center where they can be protected by a perimeter firewall. In some ways, there is no more perimeter. To respond to this app-centric world, you need a security solution that can bring security closer to the applications using a “new firewall or micro-perimeter” that surrounds each and every workload, allowing you to protect what matters most to you—your applications and - data.
With Secure Workload, you can secure your applications by creating micro-perimeters at the workload level across your entire infrastructure consistently, whether these are deployed on bare-metal servers, virtual machines, or containers.
Secure Workload delivers zero-trust microsegmentation to protect applications, reduce risk, and maintain compliance with:
● Automatically generated microsegmentation policies through comprehensive analysis of application communication patterns and dependencies.
● Dynamic attribute-based policy definition with a hierarchical policy model to deliver comprehensive controls across multiple user groups with role-based access control.
● Consistent policy enforcement at scale through distributed control of native host firewalls and infrastructure, including ADCs (Application Delivery Controllers) and firewalls.
● Near real-time compliance monitoring of all communications to identify and alert against policy violation or potential compromise.
● Workload behavior baselining and proactive anomaly detection.
● Common vulnerability detection with dynamic mitigation and threat-based quarantine.
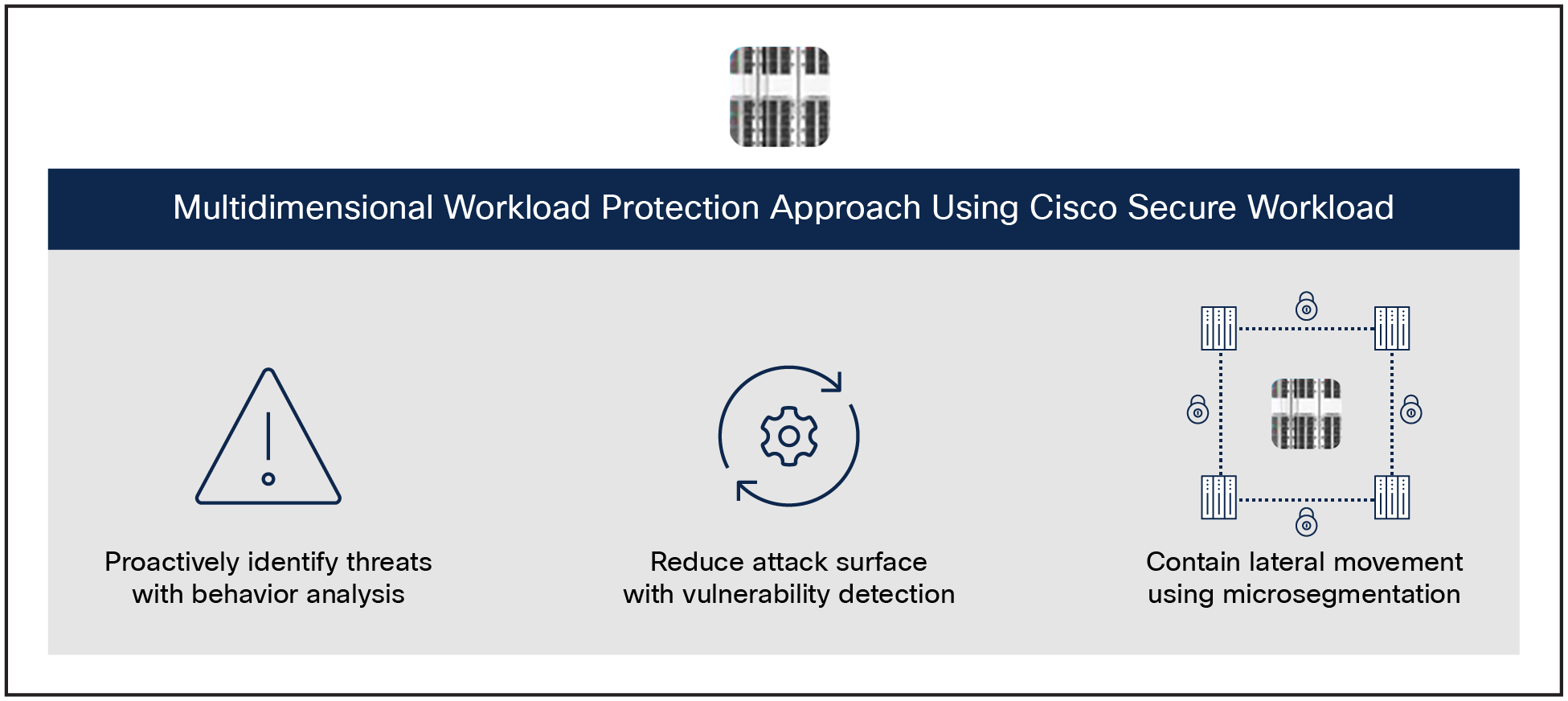
Multidimensional workload protection approach using Cisco Secure Workload
By using this multidimensional workload protection approach (Figure 1), Secure Workload significantly reduces the attack surface, minimizes lateral movement in case of security incidents, and quickly identifies anomalous behaviors within the data center.
To learn more about workload protection capabilities and use cases,
Refer to the Cisco Secure Workload for Workload Protection data sheet.
Features and benefits
Table 1 lists the main features and benefits of Cisco Secure Workload.
Table 1. Secure Workload primary features and benefits
| Feature |
Benefit |
| Achieve Zero-trust using microsegmentation |
● Make implementing microsegmentation within your environment a reality.
● Secure Workload’s automated approach helps accelerate deployment of microsegmentation.
● Secure hybrid multicloud workloads and contain lateral movement using microsegmentation.
|
| Extend policy definitions based on additional context |
● Eliminate time-consuming manual creation of resource lists to segment applications.
● Define microsegmentation default and absolute policies using asset tags.
● Quickly develop consistent policies for applications using real-time asset tagging:
● Associate rich business context with the servers.
● Define policies based on users and user groups that need access.
|
| One-click policy enforcement across a multicloud data center |
● Enforce the security framework using application segmentation and reduce the surface vulnerable to attack.
● Enforce policies with a single click. Use the mechanisms in Linux and Microsoft Windows environments to enforce security policy.
● Normalize the policy for each server, eliminating the need for manual intervention to identify policy for each of the servers.
|
| Detect policy noncompliance events |
● Track application policy compliance in real time.
● Enable alerts for compliance events that can then be integrated with SIEM systems for investigation and remediation.
|
| Identification of workload behavior deviations |
● Baseline the behavior or the workloads based on communication activities and processes on the workloads.
● Proactively detect anomalous behavior and identify indicators of compromise.
● Enable alerts for such events to be integrated with your SIEM systems for further security incident handling.
|
| Software vulnerability detection |
● Get a baseline software inventory and the version information installed on servers.
● Quickly identify if any of the package versions have known vulnerabilities or exposures, along with the severity.
● Get an accurate inventory of all the servers that have the vulnerable package.
● Tie this information to a policy that designates a specific action, such as quarantining a specific server.
|
| Flexible telemetry collection options |
Software agents:
● Capture communication and process activities along with software package information to baseline the workload behavior.
● Designed to operate within administrator-defined computing SLAs.
● Reside outside the data path and do not affect application performance.
● Support bare-metal servers, virtual machines, and containers.
Other options:
● ERSPAN sensors.
● Application Delivery Controller (ADC) sensors—F5, Citrix NetScaler.
● NetFlow sensors.
● AWS VPC flow logs.
● Azure VPC flow logs.
● Google VPC flow logs.
|
| Endpoint device and user context |
● Either collect telemetry from Cisco AnyConnect
® Network Visibility Module (NVM) running on endpoint devices such as laptops, desktops, smart phones, etc., or collect endpoint device information from a Cisco Identity Services Engine (ISE) or VDI environment using Cisco Secure Workload software agents.
● Correlate the user data with the user group within an organization.
● Define specific policies for segmentation, using user and user group information, that can be enforced on the workloads.
|
| Support for data center scalability |
● Collect telemetry data from tens of thousands of workloads across a multicloud data center.
● Offer microsegmentation and workload protection capability across all workloads.
● Flexible and scalable deployment options designed to support large and mega data centers.
|
The primary use case of the Data Backup and Recovery feature is to restore a cluster during an outage, to another cluster either at the same site or another site.
Table 2. Data Backup and Recovery Full backup mode and Lean mode comparison
| Platform Characteristics |
Full backup mode |
Lean Mode |
| Platforms supported |
● Cisco Secure Workload (large form factor) platform option.
● Cisco Secure Workload-M (small form factor).
|
Same as Full backup mode. |
| Supported Storage Type |
● Backup and Restore is supported from a customer managed object store with S3 interface that is compatible with S3V4 API since bulk of the data copied is immutable, flat and especially suited for object stores.
● DBR can work with a physical data store that’s racked up right next to the cluster or a cloud storage such as AWS S3 in the cloud or anywhere that can be reached with an IP address.
|
Same as Full backup mode. |
| Data Backed up |
All back-ups will be a point-in-time synchronous back up across all data stores. The following data is packaged as objects and backed up: A full backup copies every object in a checkpoint, even if it is already copied and the object has not changed. |
Lean Data Mode can be enabled to exclude the non-configuration data from being backed up. All data except the following is backed up:
● Flow database.
● Data required for automatic policy discovery.
● Enforcement policies.
● Data to help with forensics such as file hashes, data leak models.
● Data related to attack surface analysis.
● CVE databases.
|
| Storage Limits |
200TB of storage is recommended. |
1 TB is sufficient as this does not back up the flows. |
In order to activate Data Backup and Recovery, a license entitlement in the form of an activation key is required for the primary (active cluster). The activation key can be obtained by emailing ciscosecureworkload-licensing-support@cisco.com along with the cluster identification information.
Cisco Secure Workload offers both Software-as-a-Service (SaaS) and on-premises options allowing customers to choose the model that meets their business needs.
For on-premises deployments, customers can choose a hardware-based appliance model (small or large form factors). The platform selection will depend on scalability considerations including the number of workloads in the environment and the desired fidelity level of flow telemetry.
When configured for conversation-only flow telemetry across all workloads, each platform can scale vertically up to two times the default platform scale with detailed flow telemetry enabled. In addition, Secure Workload may be scaled horizontally to meet the demands of very large, geographically distributed enterprise environments through federation capability.
Secure Workload also offers Disaster Recovery (DR) capability, delivered through continuous backup and restore functionality that allows customers to restore data and operations to a standby cluster in case of major failure or disaster.
Cisco Secure Workload SaaS option
With the Secure Workload SaaS option, customers can get the benefits of workload protection capabilities without having to deploy and maintain the platform on-premises. With this option, Secure Workload software runs in the cloud, managed and operated by Cisco. The customer is responsible for purchasing the required software subscription licenses and deploying software agents on workloads.
This deployment option is well suited for SaaS-only or SaaS-first customers because it offers scale flexibility. You can start small and grow as your demand grows. Other benefits of the SaaS option include:
● Significant reduction in TCO (Total Cost of Ownership).
● Faster time to value.
Table 3 shows the verified and supported scale for the SaaS option.
Table 3. Cisco Secure Workload SaaS Scale.
| Platform characteristics |
Specification |
| Maximum number of IP Addresses that can be labeled per tenant (CMDB only) |
6,000 / 100 licenses (SaaS only) |
| Maximum number of subnets that can be labeled per tenant (CMDB only) |
120 / 100 licenses (SaaS only) |
| Number of flow events that can be processed per second |
5000 flows per second / 100 licenses |
Cisco Secure Workload-M (small form factor) option
Table 4 shows the verified and supported scale. Table 5 shows the power and cooling requirements for the Secure Workload-M platform.
Table 4. Cisco Secure Workload-M platform scale.
| Platform characteristics |
Specification |
| Number of concurrent workloads (virtual machine or bare metal or container host) from which telemetry data can be analyzed |
Up to 10,000 workloads in detailed mode. Up to 20,000 workloads in conversation mode. |
| Number of flow events that can be processed per second |
Up to 500,000 flows per second |
| Number of Tenants |
7 |
| Number of Child Scopes per Tenant |
1000 |
| Total number of Child Scopes across tenants |
7000 |
| Number of Workspaces per Tenant |
1000 |
| Total number of Workspaces across tenants |
5000 |
| Number of Inventory Filters per Tenant |
1000 |
| Total Number of Inventory Filters across Tenants |
7000 |
| Number of Roles per Child Scope |
6 |
| Maximum number of IP Addresses that can be labeled across all root scopes |
500,000 |
| Maximum number of subnets that can be labeled across all root scopes |
50,000 |
Table 5. Power and cooling specifications for Cisco Secure Workload-M
| Platform requirements |
Secure Workload M5 Appliance |
Secure Workload M6 Appliance |
| Max power |
5.5 kW |
6 kW |
| Maximum cooling requirement |
13,500 BTUs per hour |
14,171 BTUs per hour |
| Rack specification |
||
Cisco Secure Workload (large form factor) platform option
Table 6 shows the verified and supported scale. Table 7 shows the power and cooling requirements for the Secure Workload platform.
Table 6. Cisco Secure Workload large platform scale.
| Platform characteristics |
Specification |
| Number of concurrent workloads (virtual machine or bare metal or container host) from which telemetry data can be analyzed |
Up to 37,500 workloads in detailed mode. Up to 75,000 workloads in conversation-mode. |
| Number of flow events that can be processed per second |
Up to 2 million flows per second |
| Number of Tenants |
35 |
| Number of Child Scopes per Tenant |
5000 |
| Total number of Child Scopes across tenants |
35000 |
| Number of Workspaces per Tenant |
3500 |
| Total number of Workspaces across tenants |
20000 |
| Number of Inventory Filters per Tenant |
5000 |
| Total Number of Inventory Filters across Tenants |
35000 |
| Number of Roles per Child Scope |
6 |
| Maximum number of IP Addresses that can be labeled across all root scopes |
1,500,000 |
| Maximum number of subnets that can be labeled across all root scopes |
200,000 |
Table 7. Power and cooling specifications for large form factor
| Platform requirements |
Secure Workload M5 Appliance |
Secure Workload M6 Appliance |
| Peak power single-rack option* |
22.5 kW |
31.8 kW |
| Maximum cooling requirements single-rack option* |
50,000 BTUs per hour |
72117 BTUs per hour |
| Total weight single-rack option |
1800 lb (800 kg) |
1800 lb (800 kg) |
| Power Distribution Unit (PDU) and power supply single-rack option |
4 x 3-phase PDUs (current and voltage ratings vary by geography) |
4 x 3-phase PDUs (current and voltage ratings vary by geography) |
| Peak power dual-rack option |
11.25 kW per rack (22.5 kW total) |
15.9 kW |
| Maximum cooling requirement dual-rack option |
25,000 BTUs per hour per rack |
36.059 BTUs per hour per rack |
| Total weight for dual-rack option |
900 lb per rack (400 kg per rack) |
900 lb per rack (400 kg per rack) |
| PDU and power supply dual-rack option |
4 x single-phase PDUs per rack (current and voltage ratings vary by geography) |
4 x single-phase PDUs per rack (current and voltage ratings vary by geography) |
| Rack specification |
||
Cisco Secure Workload software is licensed based on the number of workload equivalents or devices (endpoints) depending on the agent or sensor type being used. Telemetry data can be collected using agents, supported by other supported sensors or collectors, in any combination. Policy enforcement is enabled through agents with enforcement capability with infrastructure enforcement delivered through Cisco Secure Firewall Integration, Application Delivery Controllers (ADCs), and Security Groups in public cloud infrastructure or orchestrated via streamed Kafka policy. Workload is defined as a virtual machine, bare-metal server, or container host and includes server and desktop operating systems.
There are two primary license types for Secure Workload (including SaaS and On-Premises deployment options):
● Secure Workload protection license: This license provides workload protection capabilities, including telemetry data collection, application insight, forensics, software vulnerability detections, policy recommendation, policy simulation, policy enforcement, and compliance tracking functions.
● Secure Workload endpoint license: This license provides the comprehensive telemetry data collection from a Cisco AnyConnect client installed in the endpoints (laptops, desktops, smartphones, etc), using an NVM module. This provides insights into user, device, group, process ID, process hierarchy, and OS as well as the domain names accessed from the endpoint. Additionally, this license provides rich context from user devices for any endpoint device managed through Cisco ISE via PxGrid integration. Customers must purchase the endpoint visibility license if they want to use the platform’s capability to collect, analyze, and define policies and provide visibility into endpoint device activities. This license can be independent of the workload protection licenses. This does not include any other licenses required to enable AnyConnect NVM or Cisco ISE (those licenses need to be purchased separately).
If a customer has multiple Secure Workload clusters, software licenses can be pooled across those clusters.
If a customer has Secure Workload SaaS licenses, they cannot be ported over to an on-premises license option or vice versa.
Secure Workload SaaS deployment:
The SaaS subscription is governed by the Secure Workload SaaS Offer Description and the Cisco Universal Cloud Agreement, located at www.cisco.com/go/uca (or similar terms existing between you and Cisco) (the “Agreement”), and any software that you install is licensed under the Cisco General Terms, located at www.cisco.com/go/eula (the “General Terms”).
On-premises deployment option:
Secure Workload on-premises subscriptions are governed by the Cisco General Terms (see www.cisco.com/go/eula). In addition, Cisco Secure Workload software is subject to the terms of the Cisco Supplemental End User License Agreement (SEULA; see www.cisco.com/c/dam/en_us/about/doing_business/legal/seula/cisco-secure-workload.pdf).
Support and compatibility
For detailed operating system support and compatibility information for Cisco Secure Workload, see Platform Support Information located at www.cisco.com/c/m/en_us/products/security/secure-workload-compatibility-matrix.html.
Ordering information
Table 8 provides subscription software bundle part numbers used for the Cisco Secure Workload SaaS deployment option.
Table 8. Software bundle for Cisco Secure Workload SaaS option.
| Bundle part number |
Part numbers included in bundle |
Description |
| C1-TAAS-SW-K9 |
|
Cisco Secure Workload bundle part number that includes the software subscription license for SaaS option. |
| C1-TAAS-WP-FND-K9 |
Bundle part number for the Cisco Secure Workload protection subscription license. Minimum quantity is 100 and increments of 1 after that. |
|
| C1-TAAS-ENDPT-K9 |
Cisco Secure Workload endpoint visibility software subscription license for endpoints. Choose a quantity between 1000 and 999,999. For example, a quantity of 5000 will provide license price for up to 5000 endpoint devices tracked through Cisco AnyConnect or Cisco ISE. |
Also note the following additional information about the software subscription license part number:
● You can select a 1-year, 3-year, or 5-year subscription term.
● The subscription price includes software support.
● You can select the annual billing option or a monthly or quarterly option, or prepay for the entire term.
● You can add more workload instance licenses through subscription modification.
● This software subscription license can be used only with a Cisco Secure Workload SaaS deployment.
Table 9 provides hardware and software bundle part numbers for the Cisco Secure Workload-M platform option.
Table 9. Hardware and subscription software bundle for Cisco Secure Workload-M option.
| Bundle part number |
Part numbers included in bundle |
Description |
| C1-TETRATION-M |
|
Cisco Secure Workload bundle part number that includes the hardware and software subscription license. |
| TA-CL-8U-M5-K9 |
Secure Workload Gen2 8RU Cluster. |
|
| TA-CL-8U-M6-K9 |
Cisco Secure Workload Gen3 8RU Cluster. |
|
| C1-TA-SW-K9 |
Bundle part number for the Cisco Secure Workload software subscription license; see Table 9 for details. |
Table 10 provides hardware and software bundle part numbers for the Cisco Secure Workload platform option.
Table 10. Hardware and subscription software bundle for Cisco Secure Workload option.
| Bundle part number |
Part numbers included in bundle |
Description |
| C1-TETRATION |
|
Cisco Secure Workload bundle part number that includes the hardware and software subscription license. |
| TA-CL-39U-M5-K9 |
Secure Workload Gen2 39RU Cluster. |
|
| TA-CL-39U-M6-K9 |
Cisco Secure Workload Gen3 39RU Cluster. |
|
| C1-TA-SW-K9 |
Bundle part number for the Cisco Secure Workload software subscription license; see Table 9 for details. |
Table 11 provides the software bundle part number for the Cisco Secure Workload software subscription license.
Table 11. Subscription software license for Cisco Secure Workload on-premises deployment options.
| Bundle part number |
Part numbers included in bundle |
Description |
| C1-TA-SW-K9 |
|
Bundle part number for the Cisco Secure Workload software subscription license |
| C1-TA-CWP-K9 |
Cisco Secure Workload on-premises subscription license for workload protection. Minimum quantity is 100 and increments of 1 after that. This license combines previous base and enforcement capabilities. For example, a quantity of 500 will provide the license for up to 500 workloads. |
|
| C1-TA-ENDPT-K9 |
Cisco Secure Workload endpoint visibility software subscription license is ordered in increments of 1 endpoint. Minimum quantity required is 1000. For example, a quantity of 1505 will provide license price for 1505 endpoint devices tracked through Cisco AnyConnect or Cisco ISE. |
Also note the following additional information about the software subscription license part numbers:
● You can select a 1-year, 3-year, or 5-year subscription term.
● The subscription price includes software support.
● The subscription tier is selected automatically based on the quantity entered.
● You can select the annual billing option or prepay for the entire term.
● You can add more workload instance licenses through subscription modification.
● This software subscription license can be used with both forms of Cisco Secure Workload hardware clusters.
Your license for Cisco Secure Workload endpoint software does not include AnyConnect or AnyConnect NVM licenses. You are responsible for acquiring those licenses separately.
Put Cisco expertise to work to accelerate adoption
Cisco provides professional and support services from Advisory, Implementation and Optimization to ongoing Solution Support, to help organizations get the most value from the Cisco Secure Workload platform. Cisco Services experts help integrate the platform into your production data center environment, define use cases relevant to your business objectives, tune machine learning, and validate policies and compliance to improve application and operation performance. Cisco Solution Support for Cisco Secure Workload provides hardware, software, and solution-level support. We offer a selection of custom and fixed-price, fixed-scope services for Cisco Secure Workload that help you experience faster time to value, comprehensive adoption in your environment, optimized policies and application performance, and solution wide support.
Cisco environmental sustainability
Information about Cisco’s environmental sustainability policies and initiatives for our products, solutions, operations, and extended operations or supply chain is provided in the “Environment Sustainability” section of Cisco’s Corporate Social Responsibility (CSR) Report.
Reference links to information about key environmental sustainability topics (mentioned in the “Environment Sustainability” section of the CSR Report) are provided in the following table:
| Sustainability topic |
Reference |
| Information on product material content laws and regulations |
|
| Information on electronic waste laws and regulations, including products, batteries, and packaging |
Cisco makes the packaging data available for informational purposes only. It may not reflect the most current legal developments, and Cisco does not represent, warrant, or guarantee that it is complete, accurate, or up to date. This information is subject to change without notice.
Flexible Payment Solutions to Help You Achieve Your Objectives
Cisco Capital makes it easier to get the right technology to achieve your objectives, enable business transformation and help you stay competitive. We can help you reduce the total cost of ownership, conserve capital, and accelerate growth. In more than 100 countries, our flexible payment solutions can help you acquire hardware, software, services and complementary third-party equipment in easy, predictable payments. Learn more.
For more information about the Cisco Secure Workload platform, please visit https://www.cisco.com/go/Secureworkload or contact your local Cisco account representative.
| New or revised topic |
Described In |
Date |
| Updated product overview, key features, and benefits and ordering information sections to include the updated content |
Product overview, key features and benefits, and ordering information |
January 30, 2019 |
| Updated supported operating systems for visibility and enforcement, and licensing terms |
Ordering information, licensing terms, and supported operating systems |
May 13, 2019 |
| Updated the document to include new features, subscription PID updates, and supported operating systems |
Features and benefits, ordering information, and supported operating systems |
July 20, 2019 |
| Updated the agent support matrix, hardware specifications for Secure Workload-V and included rack specifications for 39 RU and 8 RU form factors |
Supported operating systems, Cisco Secure Workload virtual option, Cisco Secure Workload large form factor option, and Cisco Secure Workload small form factor option |
February 24, 2020 |
| Updated document to rephrase terminologies and agent support matrix |
Product overview, key features and benefits and, supported operating systems |
June 16, 2020 |
| Updated product overview, key features and benefits, and agent support matrix |
Product overview, key features and benefits, and supported operating systems |
October 6, 2020 |
| Updated deployment options and scale, agent support matrix and orderability information |
Cisco Secure Workload large platform scale and Ordering information |
March 2, 2021 |
| Updated deployment scale for 39RU and SaaS offer description document URL |
Cisco Secure Workload large platform scale and Licensing terms
|
April 24, 2024 |