- Required Tools and Information
- Choosing a Physical Location for the Cisco 3350
- Unpacking the Mobility Services Engine
Installation and Initial Configuration
This chapter describes how to initially install and configure your Cisco 3350 Mobility Services Engine.
This chapter contains these sections:
- Required Tools and Information
- Choosing a Physical Location for the Cisco 3350
- Unpacking the Mobility Services Engine
- Mounting the Cisco 3350 in a Rack
- Front and Rear Panel
- Connecting and Using the CLI Console
- Powering On the Mobility Services Engine
- Configuring the Mobility Services Engine
- Configuring an NTP Server
- Launching the Mobility Services Engine
- Verifying the Mobility Services Engine Software State
- Manually Stopping Mobility Services Engine Software
- Updating Mobility Services Engine Software
- Recovering a Lost Root Password

Note For configuration details beyond initial installation, refer to the appropriate mobility services configuration guide at:
http://www.cisco.com/en/US/products/ps9742/tsd_products_support_series_home.html
Required Tools and Information
This section lists the required hardware, software and other information that you need to install and setup the mobility services engine.
Required Hardware
You need this equipment to install a mobility services engine in an EIA rack:
- A mobility services engine
- Network cables
- One rack unit (RU) in an EIA-standard rack
- Rack mounting kit (included in shipment)

Note![]() If you are installing this unit in a threaded-hole rack, you must supply screws that fit the threaded-hole rack and the appropriate screwdriver or Torx driver for those screws.
If you are installing this unit in a threaded-hole rack, you must supply screws that fit the threaded-hole rack and the appropriate screwdriver or Torx driver for those screws.
CLI Console Requirements
You need this equipment to connect to the mobility services engine console:

Note![]() A null modem serial cable that provides a connection to the laptop, desktop, or palmtop is shipped with the mobility services engine.
A null modem serial cable that provides a connection to the laptop, desktop, or palmtop is shipped with the mobility services engine.

Note![]() Please refer to the latest Release Notes for Cisco 3300 Series Mobility Services Engine for compatibility by release between the mobility services engine and Cisco WCS and controller releases at: http://www.cisco.com/en/US/products/ps9742/prod_release_notes_list.html
Please refer to the latest Release Notes for Cisco 3300 Series Mobility Services Engine for compatibility by release between the mobility services engine and Cisco WCS and controller releases at: http://www.cisco.com/en/US/products/ps9742/prod_release_notes_list.html
System Configuration Parameters
Obtain these parameters from your network administrator:
- A host name for the mobility services engine
- An IP address for the Ethernet-0 (eth0) port (mobility services engine back panel)
- A net mask for the eth0 IP address
- An IP address for the eth0 default gateway
- An IP address for the Ethernet-1 (eth1) port (mobility services engine back panel) (installation optional)
- A net mask for the eth1 IP address (only required if eth1 is installed)
- An IP address for the eth1 default gateway (only required if eth1 is installed)

Note![]() Either the Ethernet-0 or Ethernet-1 port can be used to transmit location updates to Cisco WCS. However, the Ethernet-0 port is generally configured to communicate with Cisco WCS and the Ethernet-1 port is generally used for out-of-band management. Both ports are configured as part of the installation script described in the “Configuring the Mobility Services Engine” section.
Either the Ethernet-0 or Ethernet-1 port can be used to transmit location updates to Cisco WCS. However, the Ethernet-0 port is generally configured to communicate with Cisco WCS and the Ethernet-1 port is generally used for out-of-band management. Both ports are configured as part of the installation script described in the “Configuring the Mobility Services Engine” section.
Choosing a Physical Location for the Cisco 3350
For maximum safety and reliability, mount the mobility services engine using the following guidelines.
General Precautions
To reduce the risk of personal injury or damage to the mobility services engine:
- Place the product away from radiators, heat registers, stoves, amplifiers, or other products that produce heat.
- Never use the product in a wet location.
- Avoid inserting foreign objects through openings in the product.
- To reduce risk of injury from electric shock hazards, do not open the product enclosure.
Laser Devices
Laser devices are used within the DVD of the mobility services engine. The DVD has no defined use on the customer site.
Space and Airflow Requirements
Install the mobility services engine in a EIA-standard rack. One rack unit is required for each mobility services engine.
Ensure that you can reach the mobility services engine and all cables.
- Ensure that the mobility services engine is within 328 ft (100 m) equivalent distance to any equipment connected to the 10/100/1000BASE-T ports.
- Ensure that the power cord can reach a 110 or 220 VAC grounded electrical outlet.
Ensure that there is sufficient room at the back of the mobility services engine for all cables and connectors.
- Leave a minimum clearance of 63.5 cm (25 in.) in front of the rack.
- Leave a minimum clearance of 76.2 cm (30 in.) behind the rack.
- Leave a minimum clearance of 121.9 cm (48 in.) from the back of the rack to the back of another rack or row of racks



Temperature Requirements
To ensure continued safe and reliable equipment operation, install or position the system in a well ventilated, climate-controlled environment.
Ensure that the ambient operating temperature remains between 0 and 40° C (32 and 104° F), taking into account the elevated temperatures that occur when equipment is installed in a rack.

Power Requirements
Installation of this equipment must comply with local and regional electrical regulations governing the installation of information technology equipment by licensed electricians. This equipment is designed to operate in installations covered by NFPA 70, 1999 Edition (National Electric Code) and NFPA-75, 1992 (code for Protection of Electronic Computer/Data Processing Equipment). For electrical power ratings on options, refer to the product rating label or the user documentation supplied with that option.

When installing more than one mobility services engine, you may need to use additional power distribution devices (PDUs) to safely provide power to all devices. Observe the following guidelines:
- Balance the mobility services engine power load between available AC supply branch circuits.
- Do not allow the overall system AC current load to exceed 80 percent of the branch circuit AC current rating.
- Do not use common power outlet strips for this equipment.
- Provide a separate electrical circuit for the mobility services engine.
Power Supplies on the Mobility Services Engine
The mobility services engine has two power supplies.

Warning![]() This unit might have more than one power supply connection. All connections must be removed to de-energize the unit. Statement 1028
This unit might have more than one power supply connection. All connections must be removed to de-energize the unit. Statement 1028

Batteries
The mobility services engine might include a real-time clock battery or coin cell battery that might contain perchlorate and might require special handling when recycled or disposed of in California.
Refer to the following link for disposal information.
http://www.dtsc.ca.gov/hazardouswaste/perchlorate

Electrical Grounding Requirements
The mobility services engine must be grounded properly for proper operation and safety. In the United States, you must install the equipment in accordance with NFPA 70, 1999 Edition (National Electric Code), Article 250, as well as any local and regional building codes. In Canada, you must install the equipment in accordance with Canadian Standards Association, CSA C22.1, Canadian Electrical Code. In all other countries, you must install the equipment in accordance with any regional or national electrical wiring codes, such as the International Electrotechnical Commission (IEC) Code 364, parts 1 through 7.
Furthermore, you must verify that all power distribution devices used in the installation, such as branch wiring and receptacles, are listed or certified grounding-type devices. Because of the high ground-leakage currents associated with multiple systems connected to the same power source, Cisco recommends the use of a PDU that is either permanently wired to the building’s branch circuit or includes a nondetachable cord that is wired to an industrial-style plug. NEMA locking-style plugs or those complying with IEC 60309 are considered suitable for this purpose. Using common power outlet strips for the mobility services engine is not recommended.
Rack Warnings

Warning![]() To prevent bodily injury when mounting or servicing this unit in a rack, you must take special precautions to ensure that the system remains stable. The following guidelines are provided to ensure your safety: (1) This unit should be mounted at the bottom of the rack if it is the only unit in the rack. (2) When mounting this unit in a partially filled rack, load the rack from the bottom to the top with the heaviest component at the bottom of the rack. (3) If the rack is provided with stabilizing devices, install the stabilizers before mounting or servicing the unit in the rack. Statement 1006.
To prevent bodily injury when mounting or servicing this unit in a rack, you must take special precautions to ensure that the system remains stable. The following guidelines are provided to ensure your safety: (1) This unit should be mounted at the bottom of the rack if it is the only unit in the rack. (2) When mounting this unit in a partially filled rack, load the rack from the bottom to the top with the heaviest component at the bottom of the rack. (3) If the rack is provided with stabilizing devices, install the stabilizers before mounting or servicing the unit in the rack. Statement 1006.


Unpacking the Mobility Services Engine
Follow these steps to unpack the mobility services engine.
Step 1![]() Open the shipping container and carefully remove the contents.
Open the shipping container and carefully remove the contents.
Step 2![]() Return all packing materials to the shipping container and save it.
Return all packing materials to the shipping container and save it.
Step 3![]() Ensure that all items listed in the “Package Contents” section are included in the shipment.
Ensure that all items listed in the “Package Contents” section are included in the shipment.
Step 4![]() Check each item for damage. If any item is damaged or missing, notify your authorized Cisco sales representative.
Check each item for damage. If any item is damaged or missing, notify your authorized Cisco sales representative.
Package Contents
Each mobility services engine package contains the following items:
Mounting the Cisco 3350 in a Rack

Warning![]() Only trained and qualified personnel should be allowed to install, replace, or service this equipment. Statement 1030
Only trained and qualified personnel should be allowed to install, replace, or service this equipment. Statement 1030

To reduce the risk of personal injury or damage to the equipment:
- Observe local occupational health and safety requirements and guidelines for manual material handling.
- Get help to lift and stabilize the mobility services engine during installation or removal is recommended, especially when the system is not fastened to the rails.
- Use caution when installing the mobility services engine in or removing it from the rack; it is unstable when not fastened to the rails.
- Always plan the rack installation so that the heaviest item is on the bottom of the rack. Install the heaviest item first, and continue to populate the rack from the bottom to the top.

Note ●![]() The mobility services engine comes with a rack mount rail kit that can be installed in a square-hole rack, round-hole rack, or a threaded-hole rack.
The mobility services engine comes with a rack mount rail kit that can be installed in a square-hole rack, round-hole rack, or a threaded-hole rack.
- You must provide the threaded-hole screws to secure the mounting rails to the rack. Threaded-hole screws are not shipped with the system.
Installing the Rail Kit Into a Threaded-Hole, Square-Hole or Round-Hole Rack
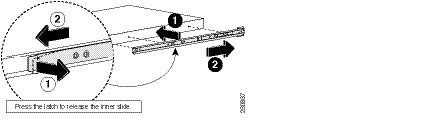
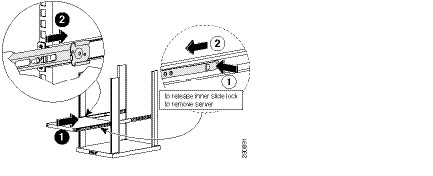
Step 1![]() Release the inner slide of the mounting rail and attach it to the side of the mobility services engine (Figure 2-1). The numbers within the illustrations indicate the order of the action.
Release the inner slide of the mounting rail and attach it to the side of the mobility services engine (Figure 2-1). The numbers within the illustrations indicate the order of the action.
Figure 2-1 Attach Inner Sliding Rail to Mobility Services Engine
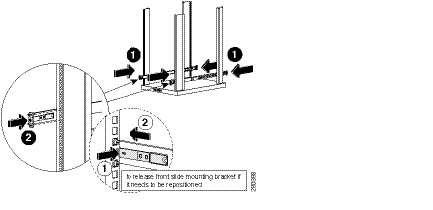
Step 2![]() Attach the outside rail to the front of the rack structure where the mobility services engine is going to be installed (Figure 2-2). The numbers within the illustrations indicate the order of the action.
Attach the outside rail to the front of the rack structure where the mobility services engine is going to be installed (Figure 2-2). The numbers within the illustrations indicate the order of the action.
Figure 2-2 Attach Outer Rail to Front of Rack
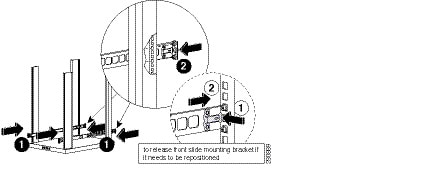
Step 3![]() Attach the outside rail to the back of the rack structure where the mobility services engine is going to be installed (Figure 2-3). The numbers within the illustrations indicate the order of the action.
Attach the outside rail to the back of the rack structure where the mobility services engine is going to be installed (Figure 2-3). The numbers within the illustrations indicate the order of the action.
Figure 2-3 Attach Outer Rail to Back of Rack
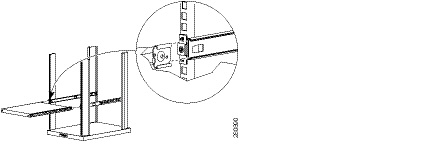
Step 4![]() Attach inner slide rail with mobility service engine to the outside rail that is mounted on the rack (Figure 2-4).
Attach inner slide rail with mobility service engine to the outside rail that is mounted on the rack (Figure 2-4).
Figure 2-4 Attach Inner Rail to Outer Rail
Step 5![]() Slide the attached inner rail and the mobility services engine to the rear of the rack (Figure 2-5). The numbers within the illustrations indicate the order of the action.
Slide the attached inner rail and the mobility services engine to the rear of the rack (Figure 2-5). The numbers within the illustrations indicate the order of the action.
Figure 2-5 Slide System and Inner Rail to Rear of Rack
Front and Rear Panel
Front Panel
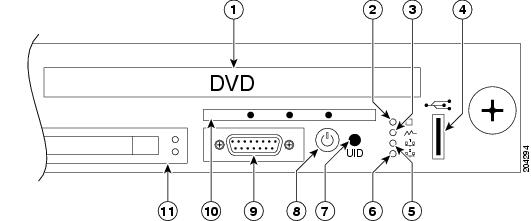
Figure 2-6 shows a full view of the front panel of the Cisco 3350 Mobility Services Engine.
Figure 2-7 shows a detailed section of the Cisco 3350 front panel.
Table 2-1 identifies Cisco 3350 front panel components and their function.
Figure 2-6 Cisco 3350 Front Panel

Figure 2-7 Close Up of Cisco 3350 Front Panel
|
|
|
|
|---|---|---|
No customer use. All system software is downloaded using Cisco WCS. |
||
Amber means that system health is degraded. For specific system information, pull out the diagnostic card from the front panel. Refer to the “Diagnostic Card” section. |
||
Red means that system health is critical. To identify the component in a critical state, pull out the diagnostic card from the front panel. Refer to the “Diagnostic Card” section. |
||
Off means that system health is normal (when in standby mode). |
||
Off means that power supply health is normal when in standby mode. |
||
Green means that a network link exists. Note NIC1 is identified as Ethernet-0 during the automatic installation script. |
||
Off means that no link to the network exists. Note If power is off, the front panel LED is not active. Check the NIC1 LED on the rear panel. Refer to the “Rear Panel” section. |
||
Green means that a network link exists. Note NIC2 is identified as Ethernet-1 during the automatic installation script. |
||
Blinking green means that a network link and activity exist. |
||
Off means that no link to the network exists. Note If power is off, the front panel LED is not active. Check the NIC2 LED on the rear panel. Refer to the “Rear Panel” section. |
||
Flashing blue means that the system is being remotely managed. |
||
Amber means that the system is shut down, but power is still applied. |
||
Off means that the power cord is not attached, power supply failure has occurred, no power supplies are installed, facility power is not available, or power button cable is disconnected. |
||
Serial connection is recommended. Do not connect any equipment to this port. |
||
Provides status on the power supplies, internal processors, DIMMS, memory, temperature and alarms. Refer to the “Diagnostic Card” section for details. |
||
Do not remove a hard drive unless it is malfunctioning and you are directed by Cisco technical support to do so. |
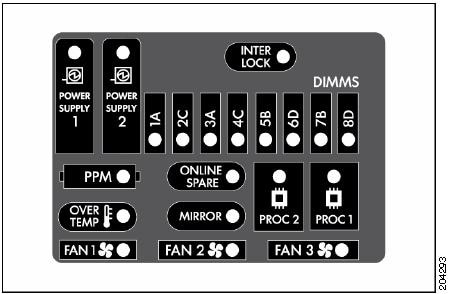
Diagnostic Card
Figure 2-8 shows details of the diagnostic card found on the front panel.
Table 2-2 summarizes the internal components of the mobility services engine that are tracked by the diagnostic card. Definitions of each of the LED states for those components are also summarized.

Note![]() This information is not currently summarized within Cisco WCS.
This information is not currently summarized within Cisco WCS.
Rear Panel
Figure 2-9 shows details of the rear panel for the Cisco 3350 Mobility Services Engine.
Table 2-3 identifies Cisco 3350 back panel components and their function.
Table 2-4 summarizes pin assignment for the DB9 cable.

Note![]() Items not labeled in Figure 2-9 are not currently assigned an active role on the system.
Items not labeled in Figure 2-9 are not currently assigned an active role on the system.
Figure 2-9 Cisco 3350 Mobility Services Engine Rear Panel

|
|
|
|---|---|
DB9 serial connector for console. See pinouts in Table 2-4 . |
|


|
|


|
|
|
|
|
|---|---|---|
Connecting and Using the CLI Console
For initial system configuration, use the command-line interface (CLI) console. The CLI console connects to the mobility services engine back-panel DB9 console port. Figure 2-9 shows the console port on the back panel of the mobility services engine. Back panel components are described in Table 2-3 . Console port pinouts are shown in Table 2-4 .

Note![]() Use either a Crossover serial cable or Null modem cable to connect the console ports.
Use either a Crossover serial cable or Null modem cable to connect the console ports.
Use these terminal emulator settings for the CLI console session:
Powering On the Mobility Services Engine
When you apply AC power to a mobility services engine, the bootup script initializes the operating system and its stored configurations. You are prompted to enter a user ID and password and enter key configuration details.
Follow these steps to power up the mobility services engine.
Step 1![]() Plug an AC power cord into the back of the power supplies of the mobility services engine (Figure 2-9), and connect the other end to a grounded 100 to 240 VAC 50/60 Hz electrical outlet.
Plug an AC power cord into the back of the power supplies of the mobility services engine (Figure 2-9), and connect the other end to a grounded 100 to 240 VAC 50/60 Hz electrical outlet.
The end of the power cord that plugs into the mobility services engine conforms with the IEC 320 standard.
Step 2![]() Use the front-panel Power On/Standby button to turn the mobility services engine on (Figure 2-7).
Use the front-panel Power On/Standby button to turn the mobility services engine on (Figure 2-7).
Step 3![]() At the login prompt, enter the mobility services engine operating user ID and password. The default user ID is root and the default password is password.
At the login prompt, enter the mobility services engine operating user ID and password. The default user ID is root and the default password is password.
The user ID and password are case sensitive.
You are now logged into the mobility services engine operating system.
Continue to the “Configuring the Mobility Services Engine” section.
Configuring the Mobility Services Engine
Minimal configuration is done for the mobility services engine as part of installation using the console. All configuration beyond the initial setup using the automatic installation can be done with Cisco WCS. For details on automatic installation refer to the “Automatic Installation Script” section.

Note You must change the default root password during initial configuration of the mobility services engine to ensure optimum network security.
- You are prompted to change the password during the automatic setup script.
- You can also change the password using the Linux command, passwd.
Automatic Installation Script

Note![]() It is highly recommended that all relevant items be configured during initial setup to ensure optimum operation of the mobility services engine in your network. The hostname and either the Ethernet-0 (eth0) or the Ethernet-1 (eth1) port MUST always be configured during the automatic installation.
It is highly recommended that all relevant items be configured during initial setup to ensure optimum operation of the mobility services engine in your network. The hostname and either the Ethernet-0 (eth0) or the Ethernet-1 (eth1) port MUST always be configured during the automatic installation.

Note![]() You can rerun the automatic installation script at any time to add or change parameters. There is no need to reenter values that you do not want changed during one of these updates.
You can rerun the automatic installation script at any time to add or change parameters. There is no need to reenter values that you do not want changed during one of these updates.

Note![]() If you do not want to configure an item, enter skip and you are prompted for the next configuration step. Any setting skipped is retained and not modified.
If you do not want to configure an item, enter skip and you are prompted for the next configuration step. Any setting skipped is retained and not modified.
The automatic installation script that displays to the screen is shown below along with descriptive text.
Example text: Indicates the installation script that displays to the console.
Body text: Provides additional information to the user about steps within the script.
Enter yes if you want to use the setup wizard or No if you want to manually set the parameters. Only experienced Linux system administrators should opt to configure the system using the setup script. The option in square brackets is the default. You can press Enter to choose that default.
When you enter Yes the following displays on the console.
enter ^ to go back to the previous prompt. You may exit at
any time by typing <Ctrl+C>.
parameter, skip it, or reset it to its initial default value.
Skipping a parameter will leave it unchanged from its current
value.
information is entered and verified.
The host name should be a unique name that can identify the device on the network. The hostname should start with a letter, end with a letter or number, and contain only letters, numbers, and dashes.
Enter a domain name for the network domain to which this device belongs. The domain name should start with a letter, and it should end with a valid domain name suffix such as .com. It must contain only letters, numbers, dashes, and dots.
Current eth0 netmask=[255.255.255.224]
Current gateway address=[209.165.201.1]

Note![]() A network administrator can provide you with the IP address, network mask, and default gateway address for the prompts that follow.
A network administrator can provide you with the IP address, network mask, and default gateway address for the prompts that follow.
Enter Yes if you want to provide information for a second ethernet (eth1) interface.

Note![]() Entry of a second ethernet interface (eth1) can be skipped by entering skip.
Entry of a second ethernet interface (eth1) can be skipped by entering skip.
Enter the network mask for the IP address you specified.

Note![]() If you entered an IP address and mask for the second interface (eth1) of this machine, you are given the opportunity to define up to two static routing entries for that interface. Static routes are typically used in lab environments to mimic out-of-band networks and are not recommended for implementation within your network unless you have extensive experience in their use.
If you entered an IP address and mask for the second interface (eth1) of this machine, you are given the opportunity to define up to two static routing entries for that interface. Static routes are typically used in lab environments to mimic out-of-band networks and are not recommended for implementation within your network unless you have extensive experience in their use.

Note![]() If you do not want to configure any static routes, enter none at the network address prompt seen below. You will not be prompted for the network mask and gateway address.
If you do not want to configure any static routes, enter none at the network address prompt seen below. You will not be prompted for the network mask and gateway address.

Note![]() If you want to configure only one route, you can enter none when you are prompted for the second network address.You will not be prompted for the network mask and gateway address for the second route.
If you want to configure only one route, you can enter none when you are prompted for the second network address.You will not be prompted for the network mask and gateway address for the second route.
Enter the network mask for the network address you entered above.
Enter a gateway address for the network address and network mask you provided.
Enter backup DNS server IP address (or none) [none]:

Note![]() Communications between the mobility services engine, Cisco WCS and the controller are in universal time code (UTC). Local time zones are configured on the mobility services engine to assist network operations center personnel in locating events within logs. Configuring NTP on each system provides devices with the UTC time.
Communications between the mobility services engine, Cisco WCS and the controller are in universal time code (UTC). Local time zones are configured on the mobility services engine to assist network operations center personnel in locating events within logs. Configuring NTP on each system provides devices with the UTC time.
Configure timezone? (Y)es/(S)kip/(U)se default [Skip]:

Note![]() The mobility services engine and its associated controllers must be mapped to the same NTP server and the same Cisco WCS server. An NTP server is required to automatically synchronize time between the controller, Cisco WCS and the mobility services engine.
The mobility services engine and its associated controllers must be mapped to the same NTP server and the same Cisco WCS server. An NTP server is required to automatically synchronize time between the controller, Cisco WCS and the mobility services engine.
A login banner appears when a user logs in through the console or SSH. This example shows the default banner. You can change the text that appears in this banner in the steps below. The banner is usually used to warn users that they are entering a private system.
Enter Y in the step below to configure and enable remote root login (access) from the console.

Note![]() If you enable remote root access, serial and SSH connections are supported. Local monitor and keyboard access is denied.
If you enable remote root access, serial and SSH connections are supported. Local monitor and keyboard access is denied.

Note![]() If you disable remote root access, then both the local monitor and keyboard work along with the serial connection. SSH access is disabled.
If you disable remote root access, then both the local monitor and keyboard work along with the serial connection. SSH access is disabled.
remote root login via secure shell for this machine.
Configure ssh access for root (Y)es/(S)kip/(U)se default [Skip]: N
root login. If you disable this option, only console
root login will be possible.
Enter yes (below) to allow remote login through SSH v2 (ssh root login) in addition to console login. Choose no to allow root login only from the console.

Note![]() If you forget the ssh root login password, you can enter into single user mode and change the password. To prevent unauthorized access, a password for the single user mode can be defined.
If you forget the ssh root login password, you can enter into single user mode and change the password. To prevent unauthorized access, a password for the single user mode can be defined.
operations. For example, when the root password is
forgotten, you can log into single user mode and reset
the root password.
!!WARNING!!
-----------
If single user mode password check is enabled and
the root password is forgotten, the appliance
will be unusable as it cannot be logged into
successfully. Do not enable this option unless it
is required. (Press ^ to go back to previous step.)

Enter the desired value for each of the password parameters or hit Enter to accept the default parameter value.

Note![]() These parameter settings apply to ALL passwords that you enable and set during the installation script.
These parameter settings apply to ALL passwords that you enable and set during the installation script.
Maximum number of days a password may be used : 60
Minimum number of days allowed between password changes : 1
Minimum acceptable password length : 9
Login delay after failed login : 5
Checking for strong passwords is currently enabled.
Minimum number of days a password may be used(0-99999, 0 means no minimum) [1]:
Minimum acceptable password length(8-10) [9]:
Login delay in seconds after failed login(0-15) [5]
Enable strong password checking? [yes/no] [yes]:
Enter Y to enable and define a root (superuser) password. Press Enter to skip this step.
Enter a password for the superuser and confirm it by typing it again. Your typing is not visible.
Confirm root password:
You can also configure a strong (GRand Unified Bootloader (GRUB)) password. A strong password must have a minimum of 9 characters and must include: two lowercase letters, two digits and two special characters (such as $ and #). An error message displays if you enter an inadequate password.


Note![]() If a strong password is not enabled, a password can be of any length.
If a strong password is not enabled, a password can be of any length.

Note![]() Passwords defined before a strong password is set are not affected by the strong password setting. Only those passwords that are set after the strong password is set are affected. For example, strong passwords will be required for passwords set later in this script such as the Cisco WCS communication password (as noted in example below) and as passwords expire.
Passwords defined before a strong password is set are not affected by the strong password setting. Only those passwords that are set after the strong password is set are affected. For example, strong passwords will be required for passwords set later in this script such as the Cisco WCS communication password (as noted in example below) and as passwords expire.
Configure GRUB password (Y)es/(D)isable/(S)kip/(U)se default [Skip]: Y
the GRUB loader means that each time the appliance is
powered up, you will be prompted for the GRUB password
you configure here.
!!WARNING!!
-----------
If the GRUB password is forgotten, the appliance
will be unusable as it cannot be booted up
successfully. Do not configure this option unless it
is required. (Press ^ to go back to previous step.)
Verify GRUB Password:
Verify GRUB Password:
UP = 2, LO = 6, DIGIT = 3, PUNCT = 0
2 digits and 2 special characters. Try again.
Verify GRUB Password:
Enter Y to enable and define a Cisco WCS communication password.

Note![]() This password does not define an individual user password for access to the Cisco WCS GUI. This password is used for SOAP/XML authentication between systems (such as mobility services engines) and Cisco WCS.
This password does not define an individual user password for access to the Cisco WCS GUI. This password is used for SOAP/XML authentication between systems (such as mobility services engines) and Cisco WCS.
The admin user is used by the WCS and other northbound systems
to authenticate their SOAP/XML session with the server.
Once this password is updated, it must correspondingly be updated
on the WCS page for MSE General Parameters so that the WCS can
communicate with the MSE.
Enter a password for Cisco WCS communication and confirm it by typing it again. Your typing is not visible.
Confirm WCS communication password:

Note![]() It is recommended that you set a BIOS password to prevent unauthorized BIOS access.
It is recommended that you set a BIOS password to prevent unauthorized BIOS access.
All of the information that was entered into the install script appears on the screen.
Host name= mse-nyc
Domain=cisco.com
Eth0 IP address=209.165.201.25, Eth0 network mask=255.255.255.224
Default gateway=209.165.201.1
Enable DNS=yes, DNS servers=209.165.201.20
Enable NTP=yes, NTP servers=1.ntp.esl.cisco.com
Login banner =
Enable SSH root access=yes
Enable Single User Mode Password Check=no
Password/Login parameters :
Password min length=9
Password min days =1
Password max days =60
Failed login delay =5
Strong password checking=yes
Root password is changed.
GRUB password is changed.
WCS password is changed.
---------------------------------------------------------------------------
more changes, or "^" to go back to the previous step.
Generating /etc/hosts
Running hostname mse-nyc.cisco.com
Generating /etc/sysconfig/network
Updating /proc/sys/kernel/hostname
Applying eth0 related parameters...
Generating /etc/sysconfig/network-scripts/ifcfg-eth0
Applying DNS related parameters...
Generating /etc/resolv.conf
Restarting network services with new settings.
Shutting down interface eth0:
Shutting down loopback interface:
Setting network parameters:
Bringing up loopback interface:
Bringing up interface eth0:
Applying NTP related parameters...
Generating /etc/ntp.conf and /etc/ntp/step-tickers
Setting system clock from NTP.
11 Apr 15:56:59 ntpdate[15176]: step time server 209.165.201.22 offset -37.556823 sec
Synchronizing hardware clock
Generating /etc/sysconfig/clock
Applying remote root login related parameters...
Disabling single user mode login password check...
Setting password/login parameters....
Setting root password.
Changing password for user root.
passwd: all authentication tokens updated successfully.
Setting wcs password.
***Configuration successful***
Reboot now? (yes/no) [yes]: yes
Exiting setup script...
After the script configuration appears on the screen, you are asked to verify all the setup information you provided. You can enter Yes to proceed with the configuration, No to make more changes, or ^ to go back to the previous step.
If you enter yes, the configuration information is applied. Cisco recommends that you reboot the system when prompted to ensure that the changes are applied.

Note![]() The message “***Configuration successful*** appears on the screen when the configuration is complete.
The message “***Configuration successful*** appears on the screen when the configuration is complete.
The next time you log in using root, only the Linux shell prompt appears and not the setup script. You can rerun the setup script at any time to change settings by logging in as root and running /opt/mse/setup/setup.sh.
The setup script generates a log file that can be found at /opt/mse/setup/setup.log .
Configuring an NTP Server
You can configure NTP servers to set up the time and date of the mobility services engine.

Note![]() You are automatically prompted to enable NTP and enter NTP server IP addresses as part of the automatic installation script. For more details on the automatic installation script, refer to the “Configuring the Mobility Services Engine” section.
You are automatically prompted to enable NTP and enter NTP server IP addresses as part of the automatic installation script. For more details on the automatic installation script, refer to the “Configuring the Mobility Services Engine” section.

Note![]() If you need to add or change an NTP server installation after a mobility services engine install, rerun the automatic installation script. You can configure the NTP server without adjusting the other values by just tabbing through the script. To rerun the automatic script, log in as root and run /opt/mse/setup/setup.sh.
If you need to add or change an NTP server installation after a mobility services engine install, rerun the automatic installation script. You can configure the NTP server without adjusting the other values by just tabbing through the script. To rerun the automatic script, log in as root and run /opt/mse/setup/setup.sh.

Note![]() For more information on the NTP configuration, consult the Linux configuration guide.
For more information on the NTP configuration, consult the Linux configuration guide.
Launching the Mobility Services Engine
To configure a mobility services engine to automatically launch after bootup enter:
Verifying the Mobility Services Engine Software State
You can verify the mobility services engine software state at any time. In the mobility services engine CLI interface, enter: /etc/init.d/msed status
If the mobility services engine is running, the command output looks like this example:
Server Config
-------------
Product name: Cisco Mobility Service Engine
Version: x.x.x.x
Hw Version: none
Hw Product Identifier: none
Hw Serial Number: none
Use HTTPS: true
HTTPS Port: 443
Use HTTP: false
HTTP Port: 80
Legacy HTTPS: false
Legacy Port: 8001
Session timeout in mins: 30
DB backup in days: 0
--------------
Server Monitor
--------------
Start time: Wed Sept 30 15:24:36 EDT 2008
Server current time: Fri May 30 19:08:15 EDT 2008
Server timezone: America/New_York
Server timezone offset: -18000000
--------------
Service Engine (1):
--------------
NAME: Location Service
VERSION: x.x.x.x
--------------
Location Service Monitor
--------------
Log Modules: 262143
Log Level: INFO
Days to keep events: 2
Keep absent data in mins: 1440
Restarts: 1
Used Memory (bytes): 129851856
Allocated Memory (bytes): 3087007744
Max Memory (bytes): 3087007744
DB virtual memory (kbytes): 0
DB virtual memory limit (bytes): 256000000
DB disk memory (bytes): 4128768
DB free size (kbytes): 2856
Active Elements: 0
Active Clients: 0
Active Tags: 0
Active Rogues: 0
Active Elements Limit: 18000
Active Sessions: 0
Clients Not Tracked due to the limiting: 0
Tags Not Tracked due to the limiting: 0
Rogues Not Tracked due to the limiting: 0
Total Elements Not Tracked due to the limiting: 0
If the mobility services engine is not running, the command output looks like this example:
Manually Stopping Mobility Services Engine Software
The mobility services engine software automatically runs after initial configuration and after each reboot.
Follow these steps to manually stop and restart the software:
Step 1![]() To stop the software, enter / etc/init.d/msed stop.
To stop the software, enter / etc/init.d/msed stop.
Step 2![]() To check status enter / etc/init.d/msed status.
To check status enter / etc/init.d/msed status.
Step 3![]() To start the software, enter: / etc/init.d/msed start.
To start the software, enter: / etc/init.d/msed start.
Updating Mobility Services Engine Software
You can update the mobility services engine using the Cisco WCS or manually download the software using a console port connected to the mobility services engine.

Note![]() For the latest Cisco WCS and mobility services engine compatibility and installation notes for a given release, refer to the appropriate release note at the following link: http://www.cisco.com/en/US/products/ps9742/tsd_products_support_series_home.html
For the latest Cisco WCS and mobility services engine compatibility and installation notes for a given release, refer to the appropriate release note at the following link: http://www.cisco.com/en/US/products/ps9742/tsd_products_support_series_home.html
Before downloading and updating software on the mobility services engine, note the following:
- The mobility services engine (server) image is compressed. The software image automatically decompresses during its download from Cisco WCS.
- Approximately 5 minutes is required for the newly loaded mobility services engine software version to appear on the Cisco WCS Mobility > Mobility Service Engines window.

Note![]() In release 6.0, the path is Services > Mobility Services.
In release 6.0, the path is Services > Mobility Services.

Note![]() Cisco WCS queries for mobility services engine connectivity and database updates every 5 minutes by default.
Cisco WCS queries for mobility services engine connectivity and database updates every 5 minutes by default.
Downloading Software Using Cisco WCS
To download software to a mobility services engine using Cisco WCS, follow these steps:
Step 1![]() Verify that you can ping the mobility services engine from Cisco WCS or an external FTP server, whichever you are going to use for the image download.
Verify that you can ping the mobility services engine from Cisco WCS or an external FTP server, whichever you are going to use for the image download.
Step 2![]() In Cisco WCS, choose Mobility > Mobility Service Engines.
In Cisco WCS, choose Mobility > Mobility Service Engines.

Note![]() In release 6.0, the path is Services > Mobility Services.
In release 6.0, the path is Services > Mobility Services.
Step 3![]() Click the name of the mobility services engine to which you want to download software.
Click the name of the mobility services engine to which you want to download software.
Step 4![]() Choose Maintenance (left panel).
Choose Maintenance (left panel).
Step 5![]() Choose Download Software.
Choose Download Software.
Step 6![]() To download software, do one of the following:
To download software, do one of the following:
- To download software listed in the Cisco WCS directory, select Select from uploaded images to transfer into the Server. Then, choose a binary image from the drop-down menu.
Cisco WCS downloads the binary images listed in the drop-down menu into the FTP server directory you have specified during the Cisco WCS installation.
- To use downloaded software available locally or over the network, select the Browse a new software image to transfer into the Server and click Browse. Locate the file and click Open.
Step 7![]() Enter the time in seconds (between 1 and1800) after which software download times out.
Enter the time in seconds (between 1 and1800) after which software download times out.

Note![]() This time out setting represents the total time allowed before a software download to a mobility services engine expires. It is not a FTP packet timeout setting.
This time out setting represents the total time allowed before a software download to a mobility services engine expires. It is not a FTP packet timeout setting.
Step 8![]() Click Download to send the software to the /opt/installers directory on the mobility services engine.
Click Download to send the software to the /opt/installers directory on the mobility services engine.
Step 9![]() After the image has been transferred to the mobility service engine, log in to the mobility services engine CLI and run the installer image from the /opt/installers directory by entering the ./image-name command.
After the image has been transferred to the mobility service engine, log in to the mobility services engine CLI and run the installer image from the /opt/installers directory by entering the ./image-name command.
Step 10![]() To run the software, enter /etc/init.d/msed start.
To run the software, enter /etc/init.d/msed start.
Step 11![]() To stop the software, enter /etc/init.d/msed stop and to check status enter /etc/init.d/msed status.
To stop the software, enter /etc/init.d/msed stop and to check status enter /etc/init.d/msed status.
Manually Downloading Software
If you do not want to automatically update the mobility services engine software using Cisco WCS, follow these steps to upgrade the software manually using a local (console) or remote (SSH) connection.
Step 1![]() Transfer the new mobility services engine image onto the hard drive.
Transfer the new mobility services engine image onto the hard drive.
a.![]() Log in as root, and use the binary setting to send the software image from an external FTP server root directory.
Log in as root, and use the binary setting to send the software image from an external FTP server root directory.
An example software image file name is CISCO-MSE-L-K9-x-x-x-x-64bit.bin.gz and it changes with each release.

Note![]() The mobility services engine image is compressed at this point.
The mobility services engine image is compressed at this point.

Note![]() The default login name for the FTP server is ftp-user.
The default login name for the FTP server is ftp-user.
# ftp <FTP Server IP address>
Name: <login>
Password: <password>
binary
get CISCO-MSE-L-K9-x-x-x-x-64bit.bin.gz
<CTRL-Z>
#
b.![]() Verify that the image ( CISCO-MSE-L-K9-x-x-x-x-64bit.bin.gz) is in the mobility services engine /opt/installers directory.
Verify that the image ( CISCO-MSE-L-K9-x-x-x-x-64bit.bin.gz) is in the mobility services engine /opt/installers directory.
c.![]() To decompress (unzip) the image file enter:
To decompress (unzip) the image file enter:
The decompression yields a bin file.
d.![]() Make sure that the CISCO-MSE-L-K9-x-x-x-x.bin file has execute permissions for the root user. If not, enter:
Make sure that the CISCO-MSE-L-K9-x-x-x-x.bin file has execute permissions for the root user. If not, enter:
chmod 755 CISCO-MSE-L-K9-x-x-x-x.bin
Step 2![]() To manually stop the mobility services engine, login as root and enter:
To manually stop the mobility services engine, login as root and enter:
Step 3![]() To install the new mobility services engine image, enter:
To install the new mobility services engine image, enter:
Step 4![]() To start the new mobility services software, by enter:
To start the new mobility services software, by enter:

Step 5![]() To uninstall the mobility services engine’s script files, enter:
To uninstall the mobility services engine’s script files, enter:
Recovering a Lost Root Password
If you lose or forget the root password for a mobility services engine, follow these steps:
Step 1![]() When the GRUB screen comes up, press Esc to enter the boot menu.
When the GRUB screen comes up, press Esc to enter the boot menu.


Note![]() The connection must be made over the console port, not by connecting a keyboard, mouse and monitor to the unit.
The connection must be made over the console port, not by connecting a keyboard, mouse and monitor to the unit.
Step 3![]() Navigate to the line beginning with "kernel," and press e.
Navigate to the line beginning with "kernel," and press e.
At the end of the line enter a space and the number one (1). Press Enter to save this change.
Step 4![]() Press b to begin boot sequence.
Press b to begin boot sequence.
At the end of the boot sequence, a shell prompt appears.

Note![]() The shell prompt does not appear if you have set up a single user mode password.
The shell prompt does not appear if you have set up a single user mode password.
Step 5![]() You can change the root password by entering the passwd command.
You can change the root password by entering the passwd command.
Step 6![]() Enter and confirm the new password.
Enter and confirm the new password.
 Feedback
Feedback