Set Up Directory Synchronization and Authentication
-
Synchronize with the directory server.
-
Authenticate with the directory server.
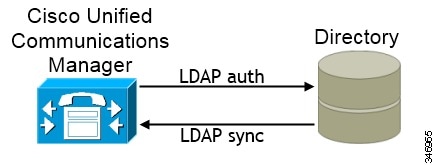
Synchronizing with the directory server replicates contact data from your directory to Cisco Unified Communications Manager.
Enabling authentication with the directory server lets Cisco Unified Communications Manager proxy authentication from the client to the directory server. In this way, users authenticate with the directory server, not with Cisco Unified Communications Manager or a presence server.
Synchronize with the Directory Server
Enable Synchronization
To ensure that contact data in your directory server is replicated to Cisco Unified Communications Manager, you must synchronize with the directory server. Before you can synchronize with the directory server, you must enable synchronization.
Procedure
| Step 1 |
Open the Cisco Unified CM Administration interface. |
| Step 2 |
Select . The LDAP System Configuration window opens. |
| Step 3 |
Locate the LDAP System Information section. |
| Step 4 |
Select Enable Synchronizing from LDAP Server. |
| Step 5 |
Select the type of directory server from which you are synchronizing data from the LDAP Server Type drop-down list. |
What to do next
Specify an LDAP attribute for the user ID.
Specify an LDAP Attribute for the User ID
When you synchronize from your directory source to Cisco Unified Communications Manager, you can populate the user ID from an attribute in the directory. The default attribute that holds the user ID is sAMAccountName.
Procedure
| Step 1 |
Locate the LDAP Attribute for User ID drop-down list on the LDAP System Configuration window. |
||
| Step 2 |
Specify an attribute for the user ID as appropriate and then select Save.
|
Perform Synchronization
After you add a directory server and specify the required parameters, you can synchronize Cisco Unified Communications Manager with the directory server.
Before you begin
-
Cisco Unified Presence — Cisco UP Sync Agent
-
Cisco Unified Communications Manager IM and Presence Service — Cisco Sync Agent
This service keeps data synchronized between the presence server and Cisco Unified Communications Manager. When you perform the synchronization with your directory server, Cisco Unified Communications Manager then synchronizes the data with the presence server. However, the Cisco Sync Agent service must be activated and started.
Procedure
| Step 1 |
Select . |
||
| Step 2 |
Select Add New. The LDAP Directory window opens. |
||
| Step 3 |
Specify the required details on the LDAP Directory window. See the Cisco Unified Communications Manager Administration Guide for more information about the values and formats you can specify. |
||
| Step 4 |
Create an LDAP Directory Synchronization Schedule to ensure that your information is synchronized regularly. |
||
| Step 5 |
Select Save. |
||
| Step 6 |
Select Perform Full Sync Now.
|
User data from your directory server is synchronized to the Cisco Unified Communications Manager database. Cisco Unified Communications Manager then synchronizes the user data to the presence server database.
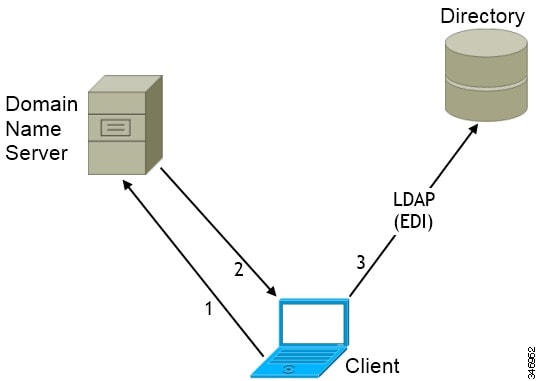
Authenticate with the LDAP Server
Perform this procedure if you want to enable LDAP authentication so that end user passwords are authenticated against the password that is assigned in the company LDAP directory. LDAP authentication gives system administrators the ability to assign an end user a single password for all company applications. This configuration applies to end user passwords only and does not apply to end user PINs or application user passwords. When users sign in to the client, the presence service routes that authentication to Cisco Unified Communications Manager. Cisco Unified Communications Manager then sends that authentication to the directory server.
Procedure
| Step 1 |
Open the Cisco Unified CM Administration interface. |
| Step 2 |
Select . |
| Step 3 |
Select Use LDAP Authentication for End Users. |
| Step 4 |
Specify LDAP credentials and a user search base as appropriate. See the Cisco Unified Communications Manager Administration Guide for information about the fields on the LDAP Authentication window. |
| Step 5 |
Select Save. |


 Feedback
Feedback