- About this Guide
-
- Information About Cisco Unified Communications Features
- Using the Cisco Unified Communication Wizard
- Configuring the Cisco Phone Proxy
- Configuring the TLS Proxy for Encrypted Voice Inspection
- Configuring Cisco Mobility Advantage
- Configuring Cisco Unified Presence
- Configuring Cisco Unified Communications Intercompany Media Engine
- Index
CLI Book 2: Cisco ASA Series Firewall CLI Configuration Guide, 9.1
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- August 14, 2014
Chapter: Configuring Connection Limits and Timeouts
Configuring Connection Settings
This chapter describes how to configure connection settings for connections that go through the ASA, or for management connections, that go to the ASA. Connection settings include:
Information About Connection Settings
This section describes why you might want to limit connections and includes the following topics:
- TCP Intercept and Limiting Embryonic Connections
- Disabling TCP Intercept for Management Packets for Clientless SSL Compatibility
- Dead Connection Detection (DCD)
- TCP Sequence Randomization
- TCP Normalization
- TCP State Bypass
TCP Intercept and Limiting Embryonic Connections
Limiting the number of embryonic connections protects you from a DoS attack. The ASA uses the per-client limits and the embryonic connection limit to trigger TCP Intercept, which protects inside systems from a DoS attack perpetrated by flooding an interface with TCP SYN packets. An embryonic connection is a connection request that has not finished the necessary handshake between source and destination. TCP Intercept uses the SYN cookies algorithm to prevent TCP SYN-flooding attacks. A SYN-flooding attack consists of a series of SYN packets usually originating from spoofed IP addresses. The constant flood of SYN packets keeps the server SYN queue full, which prevents it from servicing connection requests. When the embryonic connection threshold of a connection is crossed, the ASA acts as a proxy for the server and generates a SYN-ACK response to the client SYN request. When the ASA receives an ACK back from the client, it can then authenticate the client and allow the connection to the server.

Note When you use TCP SYN cookie protection to protect servers from SYN attacks, you must set the embryonic connection limit lower than the TCP SYN backlog queue on the server that you want to protect. Otherwise, valid clients can nolonger access the server during a SYN attack.
To view TCP Intercept statistics, including the top 10 servers under attack, see Chapter27, “Configuring Threat Detection”
Disabling TCP Intercept for Management Packets for Clientless SSL Compatibility
By default, TCP management connections have TCP Intercept always enabled. When TCP Intercept is enabled, it intercepts the 3-way TCP connection establishment handshake packets and thus deprives the ASA from processing the packets for clientless SSL. Clientless SSL requires the ability to process the 3-way handshake packets to provide selective ACK and other TCP options for clientless SSL connections. To disable TCP Intercept for management traffic, you can set the embryonic connection limit; only after the embryonic connection limit is reached is TCP Intercept enabled.
Dead Connection Detection (DCD)
DCD detects a dead connection and allows it to expire, without expiring connections that can still handle traffic. You configure DCD when you want idle, but valid connections to persist.
When you enable DCD, idle timeout behavior changes. With idle timeout, DCD probes are sent to each of the two end-hosts to determine the validity of the connection. If an end-host fails to respond after probes are sent at the configured intervals, the connection is freed, and reset values, if configured, are sent to each of the end-hosts. If both end-hosts respond that the connection is valid, the activity timeout is updated to the current time and the idle timeout is rescheduled accordingly.
Enabling DCD changes the behavior of idle-timeout handling in the TCP normalizer. DCD probing resets the idle timeout on the connections seen in the show conn command. To determine when a connection that has exceeded the configured timeout value in the timeout command but is kept alive due to DCD probing, the show service-policy command includes counters to show the amount of activity from DCD.
TCP Sequence Randomization
Each TCP connection has two ISNs: one generated by the client and one generated by the server. The ASA randomizes the ISN of the TCP SYN passing in both the inbound and outbound directions.
Randomizing the ISN of the protected host prevents an attacker from predecting the next ISN for a new connection and potentially hijacking the new session.
TCP initial sequence number randomization can be disabled if required. For example:
- If another in-line firewall is also randomizing the initial sequence numbers, there is no need for both firewalls to be performing this action, even though this action does not affect the traffic.
- If you use eBGP multi-hop through the ASA, and the eBGP peers are using MD5. Randomization breaks the MD5 checksum.
- You use a WAAS device that requires the ASA not to randomize the sequence numbers of connections.
TCP Normalization
The TCP normalization feature identifies abnormal packets that the ASA can act on when they are detected; for example, the ASA can allow, drop, or clear the packets. TCP normalization helps protect the ASA from attacks. TCP normalization is always enabled, but you can customize how some features behave.
The TCP normalizer includes non-configurable actions and configurable actions. Typically, non-configurable actions that drop or clear connections apply to packets that are always bad. Configurable actions (as detailed in “Customizing the TCP Normalizer with a TCP Map” section) might need to be customized depending on your network needs.
TCP State Bypass
By default, all traffic that goes through the ASA is inspected using the Adaptive Security Algorithm and is either allowed through or dropped based on the security policy. The ASA maximizes the firewall performance by checking the state of each packet (is this a new connection or an established connection?) and assigning it to either the session management path (a new connection SYN packet), the fast path (an established connection), or the control plane path (advanced inspection). See the “Stateful Inspection Overview” section in the general operations configuration guide for more detailed information about the stateful firewall.
TCP packets that match existing connections in the fast path can pass through the ASA without rechecking every aspect of the security policy. This feature maximizes performance. However, the method of establishing the session in the fast path using the SYN packet, and the checks that occur in the fast path (such as TCP sequence number), can stand in the way of asymmetrical routing solutions: both the outbound and inbound flow of a connection must pass through the same ASA.
For example, a new connection goes to ASA 1. The SYN packet goes through the session management path, and an entry for the connection is added to the fast path table. If subsequent packets of this connection go through ASA 1, then the packets will match the entry in the fast path, and are passed through. But if subsequent packets go to ASA 2, where there was not a SYN packet that went through the session management path, then there is no entry in the fast path for the connection, and the packets are dropped. Figure 22-1 shows an asymmetric routing example where the outbound traffic goes through a different ASA than the inbound traffic:
Figure 22-1 Asymmetric Routing
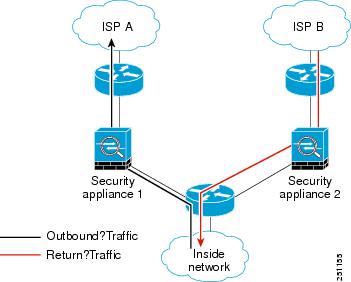
If you have asymmetric routing configured on upstream routers, and traffic alternates between two ASAs, then you can configure TCP state bypass for specific traffic. TCP state bypass alters the way sessions are established in the fast path and disables the fast path checks. This feature treats TCP traffic much as it treats a UDP connection: when a non-SYN packet matching the specified networks enters the ASA, and there is not an fast path entry, then the packet goes through the session management path to establish the connection in the fast path. Once in the fast path, the traffic bypasses the fast path checks.
Guidelines and Limitations
Supported in single and multiple context mode.
Supported in routed and transparent mode.
TCP State Bypass Unsupported Features
The following features are not supported when you use TCP state bypass:
- Application inspection—Application inspection requires both inbound and outbound traffic to go through the same ASA, so application inspection is not supported with TCP state bypass.
- AAA authenticated sessions—When a user authenticates with one ASA, traffic returning via the other ASA will be denied because the user did not authenticate with that ASA.
- TCP Intercept, maximum embryonic connection limit, TCP sequence number randomization—The ASA does not keep track of the state of the connection, so these features are not applied.
- TCP normalization—The TCP normalizer is disabled.
- SSM and SSC functionality—You cannot use TCP state bypass and any application running on an SSM or SSC, such as IPS or CSC.
TCP State Bypass NAT Guidelines
Because the translation session is established separately for each ASA, be sure to configure static NAT on both ASAs for TCP state bypass traffic; if you use dynamic NAT, the address chosen for the session on ASA 1 will differ from the address chosen for the session on ASA 2.
Maximum Concurrent and Embryonic Connection Guidelines
Depending on the number of CPU cores on your ASA model, the maximum concurrent and embryonic connections may exceed the configured numbers due to the way each core manages connections. In the worst case scenario, the ASA allows up to n -1 extra connections and embryonic connections, where n is the number of cores. For example, if your model has 4 cores, if you configure 6 concurrent connections and 4 embryonic connections, you could have an additional 3 of each type. To determine the number of cores for your model, enter the show cpu core command.
Configuring Connection Settings
This section includes the following topics:
Task Flow For Configuring Connection Settings
Step 1 For TCP normalization customization, create a TCP map according to the “Customizing the TCP Normalizer with a TCP Map” section.
Step 2 For all connection settings, configure a service policy according to Chapter1, “Configuring a Service Policy Using the Modular Policy Framework”
Step 3 Configure connection settings according to the “Configuring Connection Settings” section.
Customizing the TCP Normalizer with a TCP Map
To customize the TCP normalizer, first define the settings using a TCP map.
Detailed Steps
Step 1 To specify the TCP normalization criteria that you want to look for, create a TCP map by entering the following command:
For each TCP map, you can customize one or more settings.
Step 2 (Optional) Configure the TCP map criteria by entering one or more of the following commands (see Table 22-1 ). If you want to customize some settings, then the defaults are used for any commands you do not enter.
Detailed Steps
Creates a class map to identify the traffic for which you want to disable stateful firewall inspection. |
||
Specifies the traffic in the class map. See the “Identifying Traffic (Layer 3/4 Class Maps)” section for more information. |
||
Adds or edits a policy map that sets the actions to take with the class map traffic. |
||
Identifies the class map created in Step 1 |
||
set connection {[ conn-max n ] [ embryonic-conn-max n ] [ per-client-embryonic-max n ] [ per-client-max n ] [ random-sequence-number { enable | disable }]} ciscoasa(config-pmap-c)# set connection conn-max 256 random-sequence-number disable |
Sets maximum connection limits or whether TCP sequence randomization is enabled. The conn-max n argument sets the maximum number of simultaneous TCP and/or UDP connections that are allowed, between 0 and 2000000. The default is 0, which allows unlimited connections. If two servers are configured to allow simultaneous TCP and/or UDP connections, the connection limit is applied to each configured server separately. When configured under a class, this argument restricts the maximum number of simultaneous connections that are allowed for the entire class. In this case, one attack host can consume all the connections and leave none of the rest of the hosts matched in the ACL under the class. The embryonic-conn-max n argument sets the maximum number of simultaneous embryonic connections allowed, between 0 and 2000000. The default is 0, which allows unlimited connections. The per-client-embryonic-max n argument sets the maximum number of simultaneous embryonic connections allowed per client, between 0 and 2000000. The default is 0, which allows unlimited connections. The per-client-max n argument sets the maximum number of simultaneous connections allowed per client, between 0 and 2000000. The default is 0, which allows unlimited connections. When configured under a class, this argument restricts the maximum number of simultaneous connections that are allowed for each host that is matched through an ACL under the class. The random-sequence-number { enable | disable } keyword enables or disables TCP sequence number randomization. See the “TCP Sequence Randomization” section section for more information. You can enter this command all on one line (in any order), or you can enter each attribute as a separate command. The ASA combines the command into one line in the running configuration. 
Note For management traffic, you can only set the conn-max and embryonic-conn-max keywords. |
|
set connection timeout {[ embryonic hh : mm : ss] { idle hh : mm : ss [ reset ]] [ half-closed hh : mm : ss] [dcd hh : mm : ss [ max_retries ]]} ciscoasa(config-pmap-c)# set connection timeout idle 2:0:0 embryonic 0:40:0 half-closed 0:20:0 dcd |
Sets connection timeouts. For global timeouts, see the timout command in the command reference. The embryonic hh : mm : ss keyword sets the timeout period until a TCP embryonic (half-open) connection is closed, between 0:0:5 and 1193:00:00. The default is 0:0:30. You can also set this value to 0, which means the connection never times out. The idle hh : mm : ss keyword sets the idle timeout period after which an established connection of any protocol closes, between 0:0:1 and 1193:0:0. The default is 1:0:0. You can also set this value to 0, which means the connection never times out. For TCP traffic, the reset keyword sends a reset to TCP endpoints when the connection times out. The half-closed hh : mm : ss keyword sets the idle timeout period until a half-closed connection is closed, between 0:5:0 (for 9.1(1) and earlier) or 0:0:30 (for 9.1(2) and later) and 1193:0:0. The default is 0:10:0. Half-closed connections are not affected by DCD. Also, the ASA does not send a reset when taking down half-closed connections. The dcd keyword enables DCD. DCD detects a dead connection and allows it to expire, without expiring connections that can still handle traffic. You configure DCD when you want idle, but valid connections to persist. After a TCP connection times out, the ASA sends DCD probes to the end hosts to determine the validity of the connection. If one of the end hosts fails to respond after the maximum retries are exhausted, the ASA frees the connection. If both end hosts respond that the connection is valid, the ASA updates the activity timeout to the current time and reschedules the idle timeout accordingly. The retry-interval sets the time duration in hh : mm : ss format to wait after each unresponsive DCD probe before sending another probe, between 0:0:1 and 24:0:0. The default is 0:0:15. The max-retries sets the number of consecutive failed retries for DCD before declaring the connection as dead. The minimum value is 1 and the maximum value is 255. The default is 5. The default tcp idle timeout is 1 hour. The default udp idle timeout is 2 minutes. The default icmp idle timeout is 2 seconds. The default esp and ha idle timeout is 30 seconds. For all other protocols, the default idle timeout is 2 minutes. To never time out, enter 0:0:0. You can enter this command all on one line (in any order), or you can enter each attribute as a separate command. The command is combined onto one line in the running configuration. 
Note This command is not available for management traffic. |
|
set connection advanced-options tcp-map-name ciscoasa(config-pmap-c)# set connection advanced-options tcp_map1 |
Customizes the TCP normalizer. See the “Customizing the TCP Normalizer with a TCP Map” section to create a TCP map. |
|
set connection advanced-options tcp-state-bypass ciscoasa(config-pmap-c)# set connection advanced-options tcp-state-bypass |
||
service-policy policymap_name {global | interface interface_name } |
Activates the policy map on one or more interfaces. global applies the policy map to all interfaces, and interface applies the policy to one interface. Only one global policy is allowed. You can override the global policy on an interface by applying a service policy to that interface. You can only apply one policy map to each interface. |
|
Configuration Examples for Connection Settings
This section includes the following topics:
- Configuration Examples for Connection Limits and Timeouts
- Configuration Examples for TCP State Bypass
- Configuration Examples for TCP Normalization
Configuration Examples for Connection Limits and Timeouts
The following example sets the connection limits and timeouts for all traffic:
You can enter set connection commands with multiple parameters or you can enter each parameter as a separate command. The ASA combines the commands into one line in the running configuration. For example, if you entered the following two commands in class configuration mode:
the output of the show running-config policy-map command would display the result of the two commands in a single, combined command:
Configuration Examples for TCP State Bypass
The following is a sample configuration for TCP state bypass:
Feature History for Connection Settings
Table 22-2 lists each feature change and the platform release in which it was implemented.
 Feedback
Feedback