配置ASA 9.x EIGRP:示例
下載選項
無偏見用語
本產品的文件集力求使用無偏見用語。針對本文件集的目的,無偏見係定義為未根據年齡、身心障礙、性別、種族身分、民族身分、性別傾向、社會經濟地位及交織性表示歧視的用語。由於本產品軟體使用者介面中硬式編碼的語言、根據 RFP 文件使用的語言,或引用第三方產品的語言,因此本文件中可能會出現例外狀況。深入瞭解思科如何使用包容性用語。
關於此翻譯
思科已使用電腦和人工技術翻譯本文件,讓全世界的使用者能夠以自己的語言理解支援內容。請注意,即使是最佳機器翻譯,也不如專業譯者翻譯的內容準確。Cisco Systems, Inc. 對這些翻譯的準確度概不負責,並建議一律查看原始英文文件(提供連結)。
簡介
本文檔介紹如何配置Cisco ASA以透過增強型內部網關路由協定(EIGRP)獲知路由。
必要條件
需求
思科要求您在嘗試此組態之前,符合以下條件:
- Cisco ASA必須運行版本9.x或更高版本。
採用元件
本文中的資訊係根據以下軟體和硬體版本:
- Cisco ASA軟體版本9.2.1
- 思科調適型安全裝置管理員(ASDM)版本7.2.1
- 運行版本12.4的Cisco IOS®路由器
本文檔介紹如何配置Cisco自適應安全裝置(ASA),以便透過ASA軟體版本9.x及更高版本支援的增強型內部網關路由協定(EIGRP)獲知路由並執行身份驗證。
本文中的資訊是根據特定實驗室環境內的裝置所建立。文中使用到的所有裝置皆從已清除(預設)的組態來啟動。如果您的網路運作中,請確保您瞭解任何指令可能造成的影響。
背景資訊
準則和限制
- 單模式和多模式中每個情景支援一個EIGRP例項。
- 在多模式中,每個EIGRP例項的每個情景會建立兩個執行緒,並可使用show process進行檢視。
- 自動摘要預設為停用。
- 未以獨立介面模式在集群裝置之間建立鄰居關係。
- [<acl>]中的Default-information用於過濾傳入的候選預設路由中的External位。
- Default-information out [<acl>]用於過濾傳出候選預設路由中的External位。
EIGRP和故障切換
Cisco ASA代碼版本8.4.4.1及更高版本將動態路由從主用裝置同步到備用裝置。此外,刪除路由也會同步到STANDBY單元。但是,對等鄰接的狀態並不同步;只有活動裝置維護鄰居狀態並積極參與動態路由。有關詳細資訊,請參閱ASA常見問題:如果動態路由已同步,則在故障切換後會出現什麼情況?。
設定
本節介紹如何配置本文檔中介紹的功能。
注意:使用命令查詢工具(僅供註冊客戶使用)可獲取有關此部分中所用命令的更多資訊。
網路圖表
此文件使用以下網路設定:
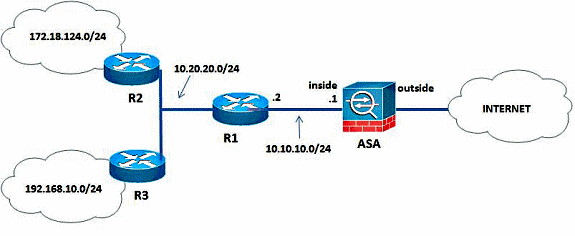
在圖示的網路拓撲中,Cisco ASA內部介面IP地址為10.10.10.1/24。目標是在Cisco ASA上配置EIGRP,以便透過相鄰路由器(R1)動態獲知到內部網路(10.20.20.0/24、172.18.124.0/24和192.168.10.0/24)的路由。R1透過另外兩台路由器(R2和R3)獲知到遠端內部網路的路由。
ASDM配置
ASDM是基於瀏覽器的應用,用於配置和監控安全裝置上的軟體。ASDM從安全裝置載入,然後用於配置、監控和管理裝置。您也可以使用ASDM Launcher以比Java Applet更快的速度啟動ASDM應用程式。本節介紹使用ASDM配置本文檔中介紹的功能所需的資訊。
要在Cisco ASA中配置EIGRP,請完成以下步驟。
- 使用ASDM登入到Cisco ASA。
- 導航到ASDM介面的Configuration > Device Setup > Routing > EIGRP區域,如此螢幕截圖所示。

- 在Setup > Process Instances 頁籤中,啟用EIGRP路由進程,如螢幕截圖所示。在本示例中,EIGRP進程是10。

- 您可以配置可選的高級EIGRP路由進程引數。按一下Setup > Process Instances頁籤上的Advanced。您可以將EIGRP路由進程配置為末節路由進程、停用自動路由彙總、定義重分發路由的預設度量、更改內部和外部EIGRP路由的管理距離、配置靜態路由器ID,以及啟用或停用鄰接更改的日誌記錄。在本示例中,EIGRP路由器ID使用內部介面的IP地址(10.10.10.1)進行靜態配置。此外,還停用了Auto-summary。所有其他選項均配置有它們的預設值。

- 完成前述步驟後,在Setup > Networks頁籤上定義EIGRP路由中涉及的網路和介面。按一下Add,如螢幕截圖所示。

- 出現此螢幕。在本示例中,您增加的唯一網路是內部網路(10.10.10.0/24),因為EIGRP僅在內部介面上啟用。

只有具有IP地址且屬於已定義網路的介面才會參與EIGRP路由進程。如果您不希望某介面參與EIGRP路由,但是該介面連線到了想要通告的網路,請在Setup > Networks頁籤上配置包含該介面連線的網路的網路項,然後將該介面配置為無源介面,這樣,該介面便無法傳送或接收EIGRP更新。
注意:配置為被動的介面不會傳送或接收EIGRP更新。
- 您可以選擇性地在Filter Rules窗格中定義路由過濾器。路由過濾可以更好地控制EIGRP更新中允許傳送或接收的路由。
- 可以選擇配置路由重分配。Cisco ASA可以將路由資訊協定(RIP)和開放最短路徑優先(OSPF)發現的路由重分配到EIGRP路由進程中。您還可以將靜態路由和已連線路由重分配到EIGRP路由進程中。如果靜態或已連線路由在Setup > Networks頁籤上配置的網路範圍內,則不需要對其重分配。在Redistribution窗格中定義路由重分配。
- EIGRP Hello資料包作為組播資料包傳送。如果EIGRP鄰居位於非廣播網路中,則必須手動定義該鄰居。當您手動定義EIGRP鄰居時,Hello資料包會作為單播消息傳送到該鄰居。為了定義靜態EIGRP鄰居,請轉到Static Neighbor窗格。
- 預設情況下,傳送和接受預設路由。為了限制或停用傳送和接收預設路由資訊,請打開Configuration > Device Setup > Routing > EIGRP > Default Information窗格。Default Information窗格顯示一個規則表,用於控制在EIGRP更新中傳送和接收預設路由資訊。
注意:每個EIGRP路由進程可以有一個「in」和一個「out」規則。(目前僅支援一個程式。)
配置EIGRP身份驗證
Cisco ASA支援對來自EIGRP路由協定的路由更新進行MD5身份驗證。每個EIGRP資料包中帶有MD5鍵的摘要可防止未經批准的來源引入未經授權或錯誤的路由消息。在EIGRP消息中增加身份驗證可確保您的路由器和Cisco ASA只接受來自配置了相同預共用金鑰的其他路由裝置的路由消息。如果沒有配置此身份驗證,如果有人將具有不同或相反路由資訊的另一台路由裝置引入網路,則路由器或Cisco ASA上的路由表可能會損壞,並隨後發生拒絕服務攻擊。當您在路由裝置(包括ASA)之間傳送的EIGRP消息中增加身份驗證時,可以防止在路由拓撲中未經授權增加EIGRP路由器。
EIGRP路由身份驗證是在每個介面上配置的。為EIGRP消息身份驗證配置的介面上的所有EIGRP鄰居必須使用相同的身份驗證模式和金鑰才能建立鄰接關係。
要在Cisco ASA上啟用EIGRP MD5身份驗證,請完成以下步驟。
- 在ASDM上,請按照所示步驟導航到Configuration > Device Setup > Routing > EIGRP > Interface。

- 在本例中,EIGRP在內部介面(GigabitEthernet 0/1)上啟用。選擇GigabitEthernet 0/1介面,然後按一下Edit。
- 在Authentication下,選擇Enable MD5 authentication。在此處增加有關身份驗證引數的更多資訊。在本示例中,預共用金鑰是cisco123,金鑰ID是1。

EIGRP路由過濾
使用EIGRP,您可以控制傳送和接收的路由更新。在本示例中,您將阻止ASA上位於R1後面的網路字首192.168.10.0/24的路由更新。對於路由過濾,只能使用標準ACL。
access-list eigrp standard deny 192.168.10.0 255.255.255.0
access-list eigrp standard permit any
router eigrp 10
distribute-list eigrp in
驗證
ASA(config)# show access-list eigrp
access-list eigrp; 2 elements; name hash: 0xd43d3adc
access-list eigrp line 1 standard deny 192.168.10.0 255.255.255.0 (hitcnt=3) 0xeb48ecd0
access-list eigrp line 2 standard permit any4 (hitcnt=12) 0x883fe5ac
組態
Cisco ASA CLI配置
這是Cisco ASA CLI配置。
!outside interface configuration
interface GigabitEthernet0/0
description outside interface connected to the Internet
nameif outside
security-level 0
ip address 198.51.100.120 255.255.255.0
!
!inside interface configuration
interface GigabitEthernet0/1
description interface connected to the internal network
nameif inside
security-level 100
ip address 10.10.10.1 255.255.255.0
!
!EIGRP authentication is configured on the inside interface
authentication key eigrp 10 cisco123 key-id 1
authentication mode eigrp 10 md5
!
!management interface configuration
interface Management0/0
nameif management
security-level 99
ip address 10.10.20.1 255.255.255.0 management-only
!
!
!EIGRP Configuration - the CLI configuration is very similar to the
!Cisco IOS router EIGRP configuration.
router eigrp 10
no auto-summary
eigrp router-id 10.10.10.1
network 10.10.10.0 255.255.255.0
!
!This is the static default gateway configuration
route outside 0.0.0.0 0.0.0.0 198.51.100.1 1
Cisco IOS路由器(R1) CLI配置
這是R1(內部路由器)的CLI配置。
!!Interface that connects to the Cisco ASA. Notice the EIGRP authentication
paramenters.
interface FastEthernet0/0
ip address 10.10.10.2 255.255.255.0
ip authentication mode eigrp 10 md5
ip authentication key-chain eigrp 10 MYCHAIN
!
!
! EIGRP Configuration
router eigrp 10
network 10.10.10.0 0.0.0.255
network 10.20.20.0 0.0.0.255
network 172.18.124.0 0.0.0.255
network 192.168.10.0
no auto-summary
驗證
完成以下步驟以驗證您的設定。
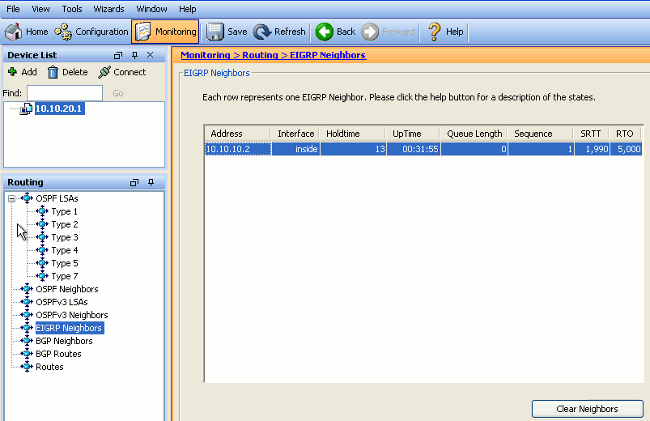
- 在ASDM上,可以導航到Monitoring > Routing > EIGRP Neighbor檢視每一個EIGRP鄰居。此螢幕截圖顯示內部路由器(R1)作為活動鄰居。您還可以看到此鄰居駐留的介面、保持時間以及鄰居關係已啟動的時間(UpTime)。
- 此外,如果導航到Monitoring > Routing > Routes,還可以驗證路由表。在此螢幕截圖中,可以看到192.168.10.0/24、172.18.124.0/24和10.20.20.0/24網路是透過R1 (10.10.10.2)獲知的。

從CLI中,可以使用show route命令獲得相同的輸出。
ciscoasa# show route
Codes: C - connected, S - static, I - IGRP, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, E - EGP
i - IS-IS, L1 - IS-IS level-1, L2 - IS-IS level-2, ia - IS-IS inter area
* - candidate default, U - per-user static route, o - ODR
P - periodic downloaded static route
Gateway of last resort is 100.10.10.2 to network 0.0.0.0
C 198.51.100.0 255.255.255.0 is directly connected, outside
D 192.168.10.0 255.255.255.0 [90/131072] via 10.10.10.2, 0:32:29, inside
D 172.18.124.0 255.255.255.0 [90/131072] via 10.10.10.2, 0:32:29, inside
C 127.0.0.0 255.255.0.0 is directly connected, cplane
D 10.20.20.0 255.255.255.0 [90/28672] via 10.10.10.2, 0:32:29, inside
C 10.10.10.0 255.255.255.0 is directly connected, inside
C 10.10.20.0 255.255.255.0 is directly connected, management
S* 0.0.0.0 0.0.0.0 [1/0] via 198.51.100.1, outside
對於ASA版本9.2.1及更高版本,可以使用show route eigrp命令只顯示EIGRP路由。
ciscoasa(config)# show route eigrp
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, + - replicated route
Gateway of last resort is not set
D 192.168.10.0 255.255.255.0 [90/131072] via 10.10.10.2, 0:32:29, inside
D 172.18.124.0 255.255.255.0 [90/131072] via 10.10.10.2, 0:32:29, inside
D 10.20.20.0 255.255.255.0 [90/28672] via 10.10.10.2, 0:32:29, inside - 也可以使用show eigrp topology命令獲得關於辨識的網路和EIGRP拓撲的資訊。
ciscoasa# show eigrp topology
EIGRP-IPv4 Topology Table for AS(10)/ID(10.10.10.1)
Codes: P - Passive, A - Active, U - Update, Q - Query, R - Reply,
r - reply Status, s - sia Status
P 10.20.20.0 255.255.255.0, 1 successors, FD is 28672
via 10.10.10.2 (28672/28416), GigabitEthernet0/1
P 10.10.10.0 255.255.255.0, 1 successors, FD is 2816
via Connected, GigabitEthernet0/1
P 192.168.10.0 255.255.255.0, 1 successors, FD is 131072
via 10.10.10.2 (131072/130816), GigabitEthernet0/1
P 172.18.124.0 255.255.255.0, 1 successors, FD is 131072
via 10.10.10.2 (131072/130816), GigabitEthernet0/1 - show eigrp neighbors命令在驗證活動鄰居和對應的資訊方面也很有用。本示例顯示的資訊與您在步驟1中從ASDM獲得的資訊相同。
ciscoasa# show eigrp neighbors
EIGRP-IPv4 neighbors for process 10
H Address Interface Hold Uptime SRTT RTO Q Seq (sec) (ms)Cnt Num
0 10.10.10.2 Gi0/1 12 00:39:12 107 642 0 1
封包流量
以下是封包流程。
- ASA在鏈路上啟動,並透過其所有配置了EIGRP的介面傳送mCast Hello資料包。
- R1收到Hello資料包並傳送mCast Hello資料包。

- ASA收到Hello資料包並傳送初始位設定的更新資料包,這表明這是初始化過程。
- R1收到Update資料包並傳送初始位元設定的Update資料包,這表明這是初始化過程。

- 在ASA和R1交換了Hello並建立了鄰居鄰接關係之後,ASA和R1都會回覆ACK資料包,這表示已收到更新資訊。
- ASA將其路由資訊以更新資料包形式傳送到R1。
- R1將更新資料包資訊插入其拓撲表中。拓撲表包含鄰居通告的所有目標。其組織方式如下:列出每個目的地,以及可前往目的地的所有鄰居及其相關測量結果。
- 然後,R1將更新資料包傳送到ASA。

- 收到更新資料包後,ASA會向R1傳送ACK資料包。在ASA和R1成功收到來自彼此的更新資料包後,它們準備在拓撲表中選擇後繼路由器(最佳)和可行後繼路由器(備份)路由,並為路由表提供後繼路由。
疑難排解
本部分包括有關debug和show命令的資訊,這些命令在排除EIGRP故障時非常有用。
疑難排解指令
輸出直譯器工具(僅供註冊客戶使用) (OIT)支援某些show指令。使用OIT可檢視對show命令輸出的分析。
附註:使用 debug 指令之前,請先參閱有關 Debug 指令的重要資訊。為了顯示關於擴散更新演算法(DUAL)有限狀態機的debug資訊,在特權EXEC模式下使用debug eigrp fsm命令。透過此命令,您可以觀察EIGRP可行後繼活動並確定路由更新是否由路由進程安裝和刪除。
以下是與R1成功對等過程中debug命令的輸出。您可以看到系統上成功安裝的每個不同路由。
EIGRP-IPv4(Default-IP-Routing-Table:10): Callback: route_adjust GigabitEthernet0/1
DUAL: dest(10.10.10.0 255.255.255.0) not active
DUAL: rcvupdate: 10.10.10.0 255.255.255.0 via Connected metric 2816/0 on topoid 0
DUAL: Find FS for dest 10.10.10.0 255.255.255.0. FD is 4294967295, RD is 4294967
295 on topoid 0 found
DUAL: RT installed 10.10.10.0 255.255.255.0 via 0.0.0.0
DUAL: Send update about 10.10.10.0 255.255.255.0. Reason: metric chg on topoid
0
DUAL: Send update about 10.10.10.0 255.255.255.0. Reason: new if on topoid 0
DUAL: dest(10.20.20.0 255.255.255.0) not active
DUAL: rcvupdate: 10.20.20.0 255.255.255.0 via 10.10.10.2 metric 28672/28416 on t
opoid 0
DUAL: Find FS for dest 10.20.20.0 255.255.255.0. FD is 4294967295, RD is 4294967
295 on topoid 0 found
EIGRP-IPv4(Default-IP-Routing-Table:10): route installed for 10.20.20.0 ()
DUAL: RT installed 10.20.20.0 255.255.255.0 via 10.10.10.2
DUAL: Send update about 10.20.20.0 255.255.255.0. Reason: metric chg on topoid
0
DUAL: Send update about 10.20.20.0 255.255.255.0. Reason: new if on topoid 0
DUAL: dest(172.18.124.0 255.255.255.0) not active
DUAL: rcvupdate: 172.18.124.0 255.255.255.0 via 10.10.10.2 metric 131072/130816
on topoid 0
DUAL: Find FS for dest 172.18.124.0 255.255.255.0. FD is 4294967295, RD is 42949
67295 on topoid 0 found
EIGRP-IPv4(Default-IP-Routing-Table:10): route installed for 172.18.124.0 ()
DUAL: RT installed 172.18.124.0 255.255.255.0 via 10.10.10.2
DUAL: Send update about 172.18.124.0 255.255.255.0. Reason: metric chg on topoi
d 0
DUAL: Send update about 172.18.124.0 255.255.255.0. Reason: new if on topoid 0
DUAL: dest(192.168.10.0 255.255.255.0) not active
DUAL: rcvupdate: 192.168.10.0 255.255.255.0 via 10.10.10.2 metric 131072/130816
on topoid 0
DUAL: Find FS for dest 192.168.10.0 255.255.255.0. FD is 4294967295, RD is 42949
67295 on topoid 0 found
EIGRP-IPv4(Default-IP-Routing-Table:10): route installed for 192.168.10.0 ()
DUAL: RT installed 192.168.10.0 255.255.255.0 via 10.10.10.2
DUAL: Send update about 192.168.10.0 255.255.255.0. Reason: metric chg on topoi
d 0
DUAL: Send update about 192.168.10.0 255.255.255.0. Reason: new if on topoid 0
您還可以使用debug eigrp neighbor命令。以下是Cisco ASA成功與R1建立新鄰居關係時此debug命令的輸出。
ciscoasa# EIGRP-IPv4(Default-IP-Routing-Table:10): Callback: route_adjust Gigabi
tEthernet0/1
EIGRP: New peer 10.10.10.2
EIGRP-IPv4(Default-IP-Routing-Table:10): route installed for 10.20.20.0 ()
EIGRP-IPv4(Default-IP-Routing-Table:10): route installed for 172.18.124.0 ()
EIGRP-IPv4(Default-IP-Routing-Table:10): route installed for 192.168.10.0 ()
您還可以使用debug EIGRP資料包在Cisco ASA及其對等體之間交換詳細的EIGRP消息資訊。在本例中,路由器(R1)上的身份驗證金鑰已更改,並且調試輸出顯示問題出在身份驗證不匹配。
ciscoasa# EIGRP: Sending HELLO on GigabitEthernet0/1
AS 655362, Flags 0x0, Seq 0/0 interfaceQ 1/1 iidbQ un/rely 0/0
EIGRP: pkt key id = 1, authentication mismatch
EIGRP: GigabitEthernet0/1: ignored packet from 10.10.10.2, opcode = 5
(invalid authentication)
EIGRP鄰居關係與Syslogs ASA-5-336010一起關閉
當EIGRP分發清單發生任何更改時,ASA會丟棄EIGRP鄰居關係。系統將顯示此系統日誌消息。
EIGRP Nieghborship Resets with syslogs ASA-5-336010: EIGRP-IPv4: PDM(314 10:
Neighbor 10.15.0.30 (GigabitEthernet0/0) is down: route configuration changed
使用此配置,每當新acl條目增加到ACL中,Eigrp-network-list EIGRP鄰居關係就會重置。
router eigrp 10
distribute-list Eigrp-network-list in
network 10.10.10.0 255.0.0.0
passive-interface default
no passive-interface inside
redistribute static
access-list Eigrp-network-list standard permit any
您可以觀察到,相鄰裝置的相鄰關係已啟動。
ciscoasa(config)# show eigrp neighbors
EIGRP-IPv4 neighbors for process 10
H Address Interface Hold Uptime SRTT RTO Q Seq
(sec) (ms) Cnt Num
0 10.10.10.2 Gi0/3 10 00:01:22 1 5000 0 5
ciscoasa(config)# show eigrp neighbors
EIGRP-IPv4 neighbors for process 10
H Address Interface Hold Uptime SRTT RTO Q Seq
(sec) (ms) Cnt Num
0 10.10.10.2 Gi0/3 13 00:01:29 1 5000 0 5
現在您可以增加access-list Eigrp-network-list standard deny 172.18.24.0 255.255.255.0。
%ASA-5-111010: User 'enable_15', running 'CLI' from IP 0.0.0.0, executed 'debug
eigrp fsm'
%ASA-7-111009: User 'enable_15' executed cmd: show access-list
%ASA-5-111008: User 'enable_15' executed the 'access-list Eigrp-network-list line
1 permit 172.18.24.0 255.255.255.0' command.
%ASA-5-111010: User 'enable_15', running 'CLI' from IP 0.0.0.0, executed 'access-list
Eigrp-network-list line 1 permit 172.18.24.0.0 255.255.255.0'
%ASA-7-111009: User 'enable_15' executed cmd: show eigrp neighbors
%ASA-5-336010: EIGRP-IPv4: PDM(599 10: Neighbor 10.10.10.2 (GigabitEthernet0/3) is
down: route configuration changed
%ASA-5-336010: EIGRP-IPv4: PDM(599 10: Neighbor 10.10.10.2 (GigabitEthernet0/3) is
up: new adjacency
這些日誌可以在debug eigrp fsm中看到。
IGRP2: linkdown: start - 10.10.10.2 via GigabitEthernet0/3
DUAL: Destination 10.10.10.0 255.255.255.0 for topoid 0
DUAL: linkdown: finish
在8.4和8.6到9.1的所有新ASA版本中,這是預期行為。運行12.4到15.1代碼系列的路由器上也存在相同的情況。 但是,在ASA版本8.2和更早的ASA軟體版本中不會觀察到此行為,因為對ACL所做的更改不會重置EIGRP鄰接關係。
由於EIGRP會在鄰居第一次啟動時將完整的拓撲表傳送給鄰居,然後只傳送更改,因此,如果配置具有EIGRP事件驅動性質的分散清單,則在未完全重置鄰居關係的情況下很難應用這些更改。路由器需要跟蹤從鄰居傳送和接收的每個路由,以便瞭解哪個路由已更改(即,將傳送/接受),以便應用當前分發清單規定的更改。簡單拆解和重新建立鄰居之間的鄰接關係要容易得多。
當鄰接關係被破壞並重新建立時,會忘記特定鄰居之間獲知的所有路由,並且重新執行鄰居之間的整個同步-即使用新的分發清單進行同步。
您用於排除Cisco IOS路由器故障的大多數EIGRP技術可以應用於Cisco ASA。為了對EIGRP進行故障排除,請使用主故障排除流程圖;從標籤為Main的框處開始。
常見問題
ASA影響EIGRP錯誤
- CSCun18948 ASA EIGRP路由在鄰居斷開連線後停滯不動。
- CSCum97632 RU:主/從裝置上「no nameif」之後的過時EIGRP彙總路由
- CSCuj30271 EIGRP:身份驗證金鑰命令已從ASA運行配置中刪除。
- CSCuj47104 活動ASA上的EIGRP路由在ASA故障切換後被刪除。
- CSCum93000 RU:主ASA上「no nameif」之後從屬裝置上的EIGRP路由過時。
- CSCup32973 ASA EIGRP在接收更新後不重置保持時間。
- CSCts93346 RIM:在ASA多情景模式下對EIGRP和OSPFv2的故障切換支援。
- CSCuc92292 ASA可能會由於版本問題而無法與路由器建立EIGRP鄰接關係。
- CSCuj13918 [RU:EIGRP]鄰居關係在配置靜態路由後關閉。
- CSCuj23967 EIGRP:來自具有預設候選EIGRP路由的ASA的流量失敗。
- CSCte01475 EIGRP:具有distribute-list的靜態路由重分配不起作用。
ASA EIGRP增強請求。
CSCug90292 ASA:EIGRP A/S不匹配無調試或Syslog輸出。
CSCtc43373 CSM:增強版-介紹ASA平台上的EIGRP配置支援。
修訂記錄
| 修訂 | 發佈日期 | 意見 |
|---|---|---|
1.0 |
02-Apr-2007
|
初始版本 |
由思科工程師貢獻
- Dinkar Sharma
- Magnus Mortensen
- Prashant Joshi
 意見
意見