為vManage生成自簽名Web證書
簡介
本檔案介紹如何在自註冊vManage上現有自簽名Web證書過期時生成並安裝自簽名Web證書。
背景資訊
思科不會為此類部署簽署Web憑證。客戶必須由自己的憑證授權單位(CA)或某些第三方CA簽署。
問題
vManage Web證書即將過期或已過期。對圖形使用者介面(GUI)的訪問可能會丟失,或者您可以在GUI中看到有關證書過期的永久警報。
解決方案
如果您不關心自簽名證書使用的安全方面,並且只是希望避免出現警報消息以及由於證書過期而導致vManage GUI訪問可能存在的問題,則您可以將此解決方案與vManage上的自簽名Web證書配合使用。
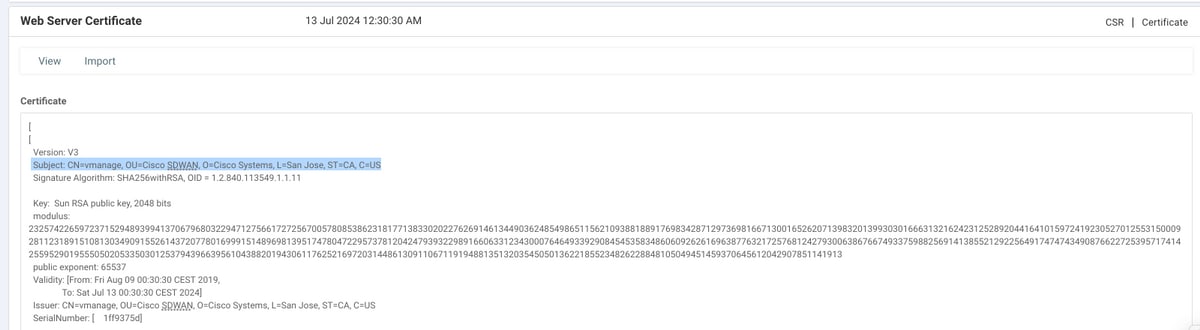
1.在vManage GUI中,導航到管理>設定> Web伺服器證書>證書,然後將此資訊儲存在有關證書主題的某個位置,例如主題:CN=vmanage、OU=Cisco SDWAN、O=Cisco Systems、L=San Jose、ST=CA、C=US。
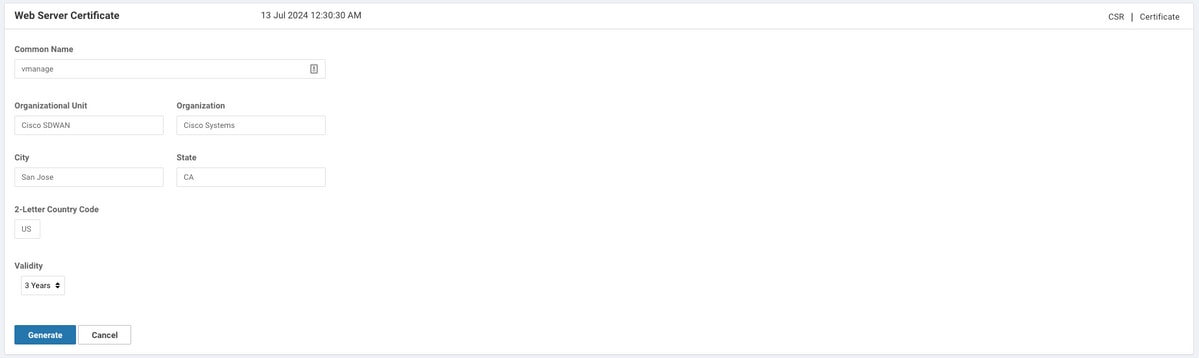
2.在vManage GUI中,導覽至管理>設定> Web伺服器證書> CSR ,然後選擇生成以生成新的證書簽名請求(CSR)。 確保輸入在上一步捕獲的Subject中的值。
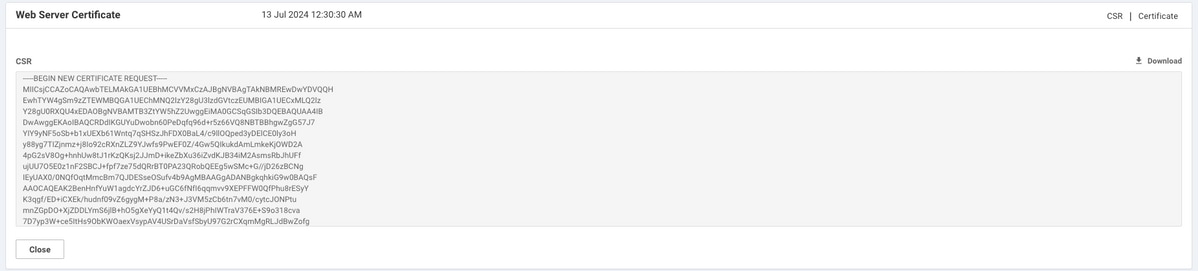
3.將新產生的CSR複製到複製貼上緩衝區,如下圖所示。
4.然後輸入vshell,並使用echo指令將具有CSR的緩衝區內容貼到vManage上的檔案中。
vmanage# vmanage# vshell vmanage:~$ mkdir web vmanage:~$ cd web vmanage:~/web$ echo "-----BEGIN NEW CERTIFICATE REQUEST----- > MIICsjCCAZoCAQAwbTELMAkGA1UEBhMCVVMxCzAJBgNVBAgTAkNBMREwDwYDVQQH > EwhTYW4gSm9zZTEWMBQGA1UEChMNQ2lzY28gU3lzdGVtczEUMBIGA1UECxMLQ2lz > Y28gU0RXQU4xEDAOBgNVBAMTB3ZtYW5hZ2UwggEiMA0GCSqGSIb3DQEBAQUAA4IB > DwAwggEKAoIBAQCRDdIKGUYuDwobn60PeDqfq96d+r5z66VQ8NBTBBhgwZgG57J7 > YIY9yNF5oSb+b1xUEXb61Wntq7qSHSzJhFDX0BaL4/c9llOQped3yDElCE0ly3oH > y88yg7TIZjnmz+j8Io92cRXnZLZ9YJwfs9PwEF0Z/4Gw5QIkukdAmLmkeKjOWD2A > 4pG2sV8Og+hnhUw8tJ1rKzQKsj2JJmD+ikeZbXu36iZvdKJB34iM2AsmsRbJhUFf > ujUU7O5E0z1nF2SBCJ+fpf7ze75dQRrBT0PA23QRobQEEg5wSMc+G//jD26zBCNg > IEyUAX0/0NQfOqtMmcBm7QJDESseOSufv4b9AgMBAAGgADANBgkqhkiG9w0BAQsF > AAOCAQEAK2BenHnfYuW1agdcYrZJD6+uGC6fNfI6qqmvv9XEPFFW0QfPhu8rESyY > K3qgf/ED+iCXEk/hudnf09vZ6gygM+P8a/zN3+J3VM5zCb6tn7vM0/cytcJONPtu > mnZGpDO+XjZDDLYmS6jlB+hO5gXeYyQ1t4Qv/s2H8jPhIWTraV376E+S9o318cva > 7D7yp3W+ce5ItHs9ObKWOaexVsypAV4USrDaVsfSbyU97G2rCXqmMgRLJdBwZofg > 04qsgrC8qG28aue1Q88XPa/HQtp0WB/Pxg7oe91s59Je/ETsMkR3vt7aglemyXAJ > nal67+T/QWgLSJB2pQuPHo51MbA55w== > -----END NEW CERTIFICATE REQUEST-----" > web_cert.csr
5.使用cat 指令確保正確儲存CSR。
vmanage:~/web$ cat web_cert.csr -----BEGIN NEW CERTIFICATE REQUEST----- MIICsjCCAZoCAQAwbTELMAkGA1UEBhMCVVMxCzAJBgNVBAgTAkNBMREwDwYDVQQH EwhTYW4gSm9zZTEWMBQGA1UEChMNQ2lzY28gU3lzdGVtczEUMBIGA1UECxMLQ2lz Y28gU0RXQU4xEDAOBgNVBAMTB3ZtYW5hZ2UwggEiMA0GCSqGSIb3DQEBAQUAA4IB DwAwggEKAoIBAQCRDdIKGUYuDwobn60PeDqfq96d+r5z66VQ8NBTBBhgwZgG57J7 YIY9yNF5oSb+b1xUEXb61Wntq7qSHSzJhFDX0BaL4/c9llOQped3yDElCE0ly3oH y88yg7TIZjnmz+j8Io92cRXnZLZ9YJwfs9PwEF0Z/4Gw5QIkukdAmLmkeKjOWD2A 4pG2sV8Og+hnhUw8tJ1rKzQKsj2JJmD+ikeZbXu36iZvdKJB34iM2AsmsRbJhUFf ujUU7O5E0z1nF2SBCJ+fpf7ze75dQRrBT0PA23QRobQEEg5wSMc+G//jD26zBCNg IEyUAX0/0NQfOqtMmcBm7QJDESseOSufv4b9AgMBAAGgADANBgkqhkiG9w0BAQsF AAOCAQEAK2BenHnfYuW1agdcYrZJD6+uGC6fNfI6qqmvv9XEPFFW0QfPhu8rESyY K3qgf/ED+iCXEk/hudnf09vZ6gygM+P8a/zN3+J3VM5zCb6tn7vM0/cytcJONPtu mnZGpDO+XjZDDLYmS6jlB+hO5gXeYyQ1t4Qv/s2H8jPhIWTraV376E+S9o318cva 7D7yp3W+ce5ItHs9ObKWOaexVsypAV4USrDaVsfSbyU97G2rCXqmMgRLJdBwZofg 04qsgrC8qG28aue1Q88XPa/HQtp0WB/Pxg7oe91s59Je/ETsMkR3vt7aglemyXAJ nal67+T/QWgLSJB2pQuPHo51MbA55w== -----END NEW CERTIFICATE REQUEST----- vmanage:~/web$
6.在openssl的幫助下,為rootca.key根憑證產生金鑰。
vmanage:~/web$ openssl genrsa -out rootca.key 2048 Generating RSA private key, 2048 bit long modulus .. .......... e is 65537 (0x10001) vmanage:~/web$ ls rootca.key web_cert.csr vmanage:~/web$
7.生成名為rootca.pem的根CA證書,並使用上一步生成的rootca.key對其進行簽名。
vmanage:~/web$ openssl req -x509 -new -nodes -key rootca.key -sha256 -days 4000 -out rootca.pem You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [AU]:US State or Province Name (full name) [Some-State]:CA Locality Name (eg, city) []:San Jose Organization Name (eg, company) [Internet Widgits Pty Ltd]:Cisco Systems Organizational Unit Name (eg, section) []:Cisco SDWAN Common Name (e.g. server FQDN or YOUR name) []:vmanage Email Address []: vmanage:~/web$ ls rootca.key rootca.pem web_cert.csr vmanage:~/web$
8.使用根CA憑證和金鑰簽署CSR。
vmanage:~/web$ openssl x509 -req -in web_cert.csr -CA rootca.pem -CAkey rootca.key -CAcreateserial -out web_cert.crt -days 4000 -sha256 Signature ok subject=/C=US/ST=CA/L=San Jose/O=Cisco Systems/OU=Cisco SDWAN/CN=vmanage Getting CA Private Key vmanage:~/web$ ls rootca.key rootca.pem rootca.srl web_cert.crt web_cert.csr vmanage:~/web$
9.將新簽名證書復制到複製貼上緩衝區。您可以使用cat檢視簽名的憑證。
vmanage:~/web$ cat web_cert.crt -----BEGIN CERTIFICATE----- MIIDVjCCAj4CCQDXH8GlDhvL4DANBgkqhkiG9w0BAQsFADBtMQswCQYDVQQGEwJV UzELMAkGA1UECAwCQ0ExETAPBgNVBAcMCFNhbiBKb3NlMRYwFAYDVQQKDA1DaXNj byBTeXN0ZW1zMRQwEgYDVQQLDAtDaXNjbyBTRFdBTjEQMA4GA1UEAwwHdm1hbmFn ZTAeFw0xOTEwMjIwODU0MzdaFw0zMDEwMDQwODU0MzdaMG0xCzAJBgNVBAYTAlVT MQswCQYDVQQIEwJDQTERMA8GA1UEBxMIU2FuIEpvc2UxFjAUBgNVBAoTDUNpc2Nv IFN5c3RlbXMxFDASBgNVBAsTC0Npc2NvIFNEV0FOMRAwDgYDVQQDEwd2bWFuYWdl MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAkQ3SChlGLg8KG5+tD3g6 n6venfq+c+ulUPDQUwQYYMGYBueye2CGPcjReaEm/m9cVBF2+tVp7au6kh0syYRQ 19AWi+P3PZZTkKXnd8gxJQhNJct6B8vPMoO0yGY55s/o/CKPdnEV52S2fWCcH7PT 8BBdGf+BsOUCJLpHQJi5pHiozlg9gOKRtrFfDoPoZ4VMPLSdays0CrI9iSZg/opH mW17t+omb3SiQd+IjNgLJrEWyYVBX7o1FOzuRNM9ZxdkgQifn6X+83u+XUEawU9D wNt0EaG0BBIOcEjHPhv/4w9uswQjYCBMlAF9P9DUHzqrTJnAZu0CQxErHjkrn7+G /QIDAQABMA0GCSqGSIb3DQEBCwUAA4IBAQBZAIxV/GI/AP0aw54PA//+QMUs9t+b i6lhATUuTdyQwOuQSSfGjhWypDsqm3oh86GXmgoxIF1D/UmcOXHKVeK/MZrhZ/P9 USAAnPGyqOha/TqQvPbSMKALHj9cGc9389io2AAeDQqneEcDqie5uOs0M0vBth3V DXpq8mYgTjhqIUyab4txWZwXvQmZj+Hu2h2S4wj//us92KgE+XcljNeaky/GEZqZ jWNoWDgWeJdsm8hx2QteHHbDTahuArVJf1p45eLIcJR1k0lRL8TTroWaST1bZCJz 20aYK4S0K0nTkpscuVIrXHkwNN6Ka4q9/rVxnLzAflJ4E9DXojpD3qNH -----END CERTIFICATE-----
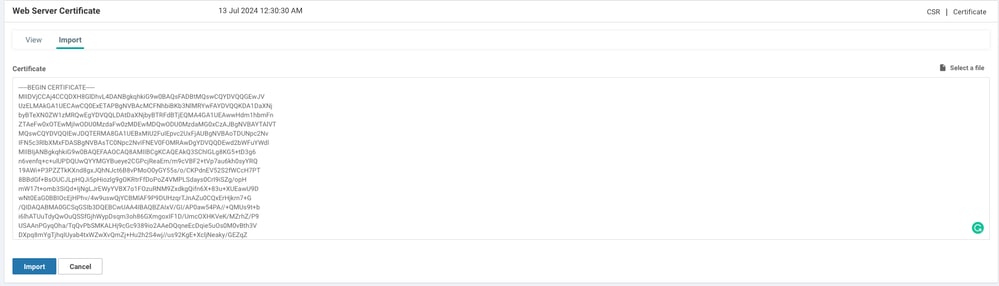
10.將證書匯入vManage。若要執行此操作,請導覽至Administration > Settings > Web Server Certificate > Import,然後貼上複製貼上緩衝區的內容,如下圖所示。
11.如果一切順利,vManage會顯示Certificate Installed Successfully,如下圖所示。
12.最後,檢查結果並確保證書有效日期更新成功,如下圖所示。

相關資訊
修訂記錄
| 修訂 | 發佈日期 | 意見 |
|---|---|---|
3.0 |
01-May-2026
|
更新的SEO和標題。 |
2.0 |
09-Sep-2024
|
已新增Alt文本。已更新標題、簡介和格式。 |
1.0 |
24-Dec-2019
|
初始版本 |
 意見
意見