BPA使用手冊RBAC許可權v5.1
簡介
基於角色的訪問控制(RBAC)是一種根據使用者在企業中的角色來限制訪問的方法。預設角色可用,並且可以通過選擇首選許可權並將這些角色對映到使用者組來建立新角色。將角色對映到使用者組允許該使用者組中的所有使用者執行與該角色關聯的操作。
新許可權
本節介紹微服務如何定義其自己的RBAC許可權集。
定義靜態許可權
要定義靜態許可權,請執行以下操作:
- 建立JSON檔案,列出microservice/src/config/device-permissions-spec.json路徑中的所有許可權。
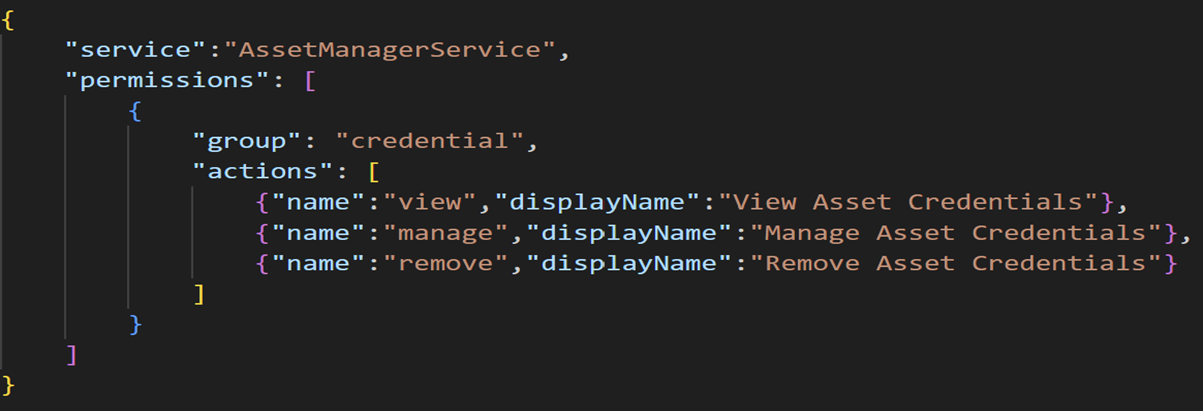
- 運行以下JSON代碼以列出許可權:
{
"service":"service-name",
"permissions": [
{
"group": "group-name",
"actions": [
{"name":"action-name","displayName":"Display name to be shown in roles page"}
]
}
]
}請參閱以下示例,在憑據組中建立檢視、管理和刪除許可權。
在BPA中註冊許可權
要註冊許可權,請執行以下操作:
- 從@cisco-bpa-platform/mw-util-common-app匯入rbacSpecProcessorHelper。
const { rbacHelper, rbacSpecProcessorHelper } = require('@cisco-bpa-platform/mw-util-common-app');- 運行以下命令以使用rbacSpecProcessorHelper處理JSON檔案中列出的許可權。
let resources = require('./config/asset-manager-permissions-spec');
let rbacSpecProcessorObj = rbacSpecProcessorHelper.getRbacSpecProcessorUtil();
rbacSpecProcessorObj.setSpec(resources);
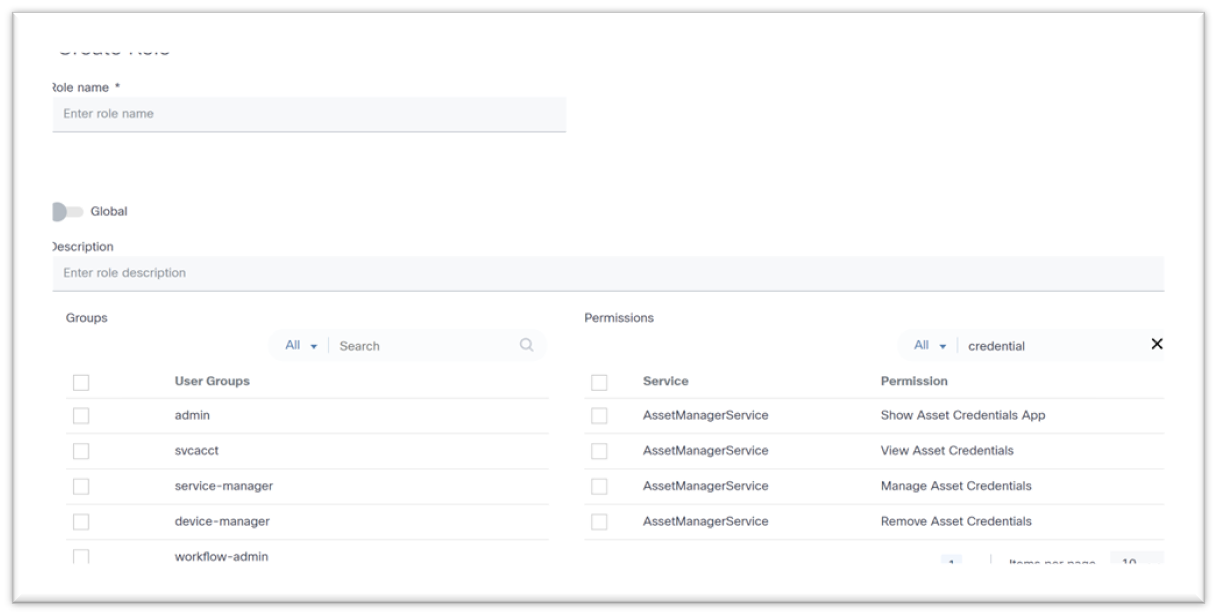
await rbacSpecProcessorObj.process();使用者可以在「建立角色」和「編輯角色」頁中檢視已註冊的許可權。
對映許可權
預設情況下,在上一節中建立的許可權可以對映到角色,也可以通過定義與角色的對映來對映。
定義許可權對映
要將定義的許可權對映到預設角色,請在microservice/src/config/device-role-permissions-mapping-spec.json路徑中建立新的JSON檔案。
在下面的示例中,三(3)個許可權對映到BPA超級管理員角色,兩(2)個許可權對映到Tenant Admin角色,一(1)個許可權對映到Network Operator角色。
{
"service": "AssetManagerService",
"roles": [
{
"name": "BPA Super Admin",
"permissions": [
{"name":"view","displayName":"View Asset Credentials","group": "credential"},
{"name":"remove","displayName":"Remove Asset Credentials","group": "credential"},
{"name":"manage","displayName":"Manage Asset Credentials Add, Update and Delete Asset Credentials","group": "credential"}
]
},
{
"name": "Tenant Admin",
"permissions": [
{"name":"view","displayName":"View Asset Credentials","group": "credential"},
{"name":"remove","displayName":"Remove Asset Credentials","group": "credential"}
]
},
{
"name": "Network Operator",
"permissions": [
{"name":"view","displayName”:"View Asset Credentials","group": "credential"}
]
}
]
}
更新許可權對映
要更新許可權對映,請執行以下操作:
- 從@cisco-bpa-platform/mw-util-common-app匯入rbacHelper、rbacPermissionMappingHelper。
const { rbacHelper, rbacPermissionMappingHelper } = require('@cisco-bpa-platform/mw-util-common-app');- 運行以下命令以更新與角色的許可權對映:
let rbacUtilObj = rbacHelper.getRbacUtilObj();
let registryDetails = await rbacUtilObj getRegistryByName({}, 'device-role-permissions-mapping-spec');
if (Array.isArray(registryDetails) && registryDetails.length === 0) {
let rbacPermissionMappingSpecProcessorObj = rbacPermissionMappingHelper.getRbacSpecProcessorUtil() ;
let rolePermissions = require('./config/device-role-permissions-mapping-spec');
rbacPermissionMappingSpecProcessorObj.setSpec(rolePermissions);
await rbacPermissionMappingSpecProcessorObj.process();
let rbacUtilObjRegister = rbacHelper.getRbacUtilObj();
await rbacUtilObjRegister addRegistry({}, 'device-role-permissions-mapping-spec');
}- 運行以下命令以處理檔案、建立許可權清單以及對映許可權與角色:
async function permissionsSpecProcessor() {
let resources = require('./config/device-permissions-spec');
let rbacSpecProcessorObj = rbacSpecProcessorHelper.getRbacSpecProcessorlltil();
rbacSpecProcessorObj.setSpec(resources);
await rbacSpecProcessorObj.process();
let rbacUtilObj = rbacHelper.getRbacUtilObj();
let registryDetails = await rbacUtilObj.getRegistryByName({} 'device-role-permissions-mapping-spec');
if (Array.isArray(registryDetails) && registryDetails.length === 0) {
let rbacPermissionMappingSpecProcessorObj = rbacPermissionMappingHelper.getRbacSpecProcessorUtil();
let rolePermissions = require('./config/device-role-permissions-mapping-spec');
rbacPermissionMappingSpecProcessorObj.setSpec(rolePermissions);
await rbacPermissionMappingSpecProcessorObj.process();
let rbacUtilObjRegister = rbacHelper.getRbacUtilObj();
await rbacUtilObjRegister.addRegistry({}, 'device-role-permissions-mapping-spec');
}
}修訂記錄
| 修訂 | 發佈日期 | 意見 |
|---|---|---|
1.0 |
23-Sep-2025
|
初始版本 |
 意見
意見