BPA用户指南RBAC权限v5.1
简介
基于角色的访问控制(RBAC)是一种根据企业内用户的角色限制访问的方法。默认角色可用,通过选择首选权限并将这些角色映射到用户组可以创建新角色。将角色映射到用户组允许该用户组中的所有用户执行与该角色关联的操作。
新权限
本节介绍微服务如何定义自己的RBAC权限集。
定义静态权限
要定义静态权限,请执行以下操作:
- 在microservice/src/config/device-permissions-spec.json路径中创建列出所有权限的JSON文件。
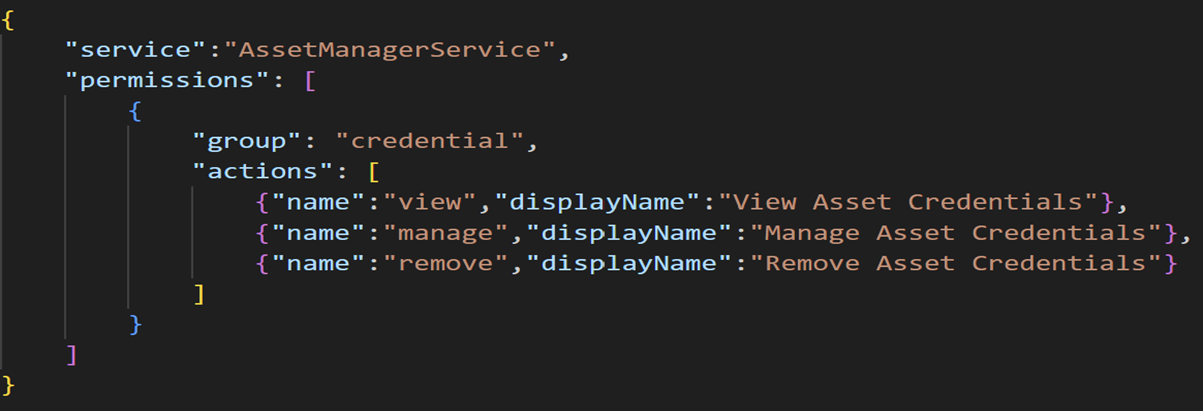
- 运行以下JSON代码以列出权限:
{
"service":"service-name",
"permissions": [
{
"group": "group-name",
"actions": [
{"name":"action-name","displayName":"Display name to be shown in roles page"}
]
}
]
}请参阅以下示例,在凭证组中创建查看、管理和删除权限。
在BPA中注册权限
要注册权限,请执行以下操作:
- 从@cisco-bpa-platform/mw-util-common-app导入rbacSpecProcessorHelper。
const { rbacHelper, rbacSpecProcessorHelper } = require('@cisco-bpa-platform/mw-util-common-app');- 运行以下命令以使用rbacSpecProcessorHelper处理JSON文件中列出的权限。
let resources = require('./config/asset-manager-permissions-spec');
let rbacSpecProcessorObj = rbacSpecProcessorHelper.getRbacSpecProcessorUtil();
rbacSpecProcessorObj.setSpec(resources);
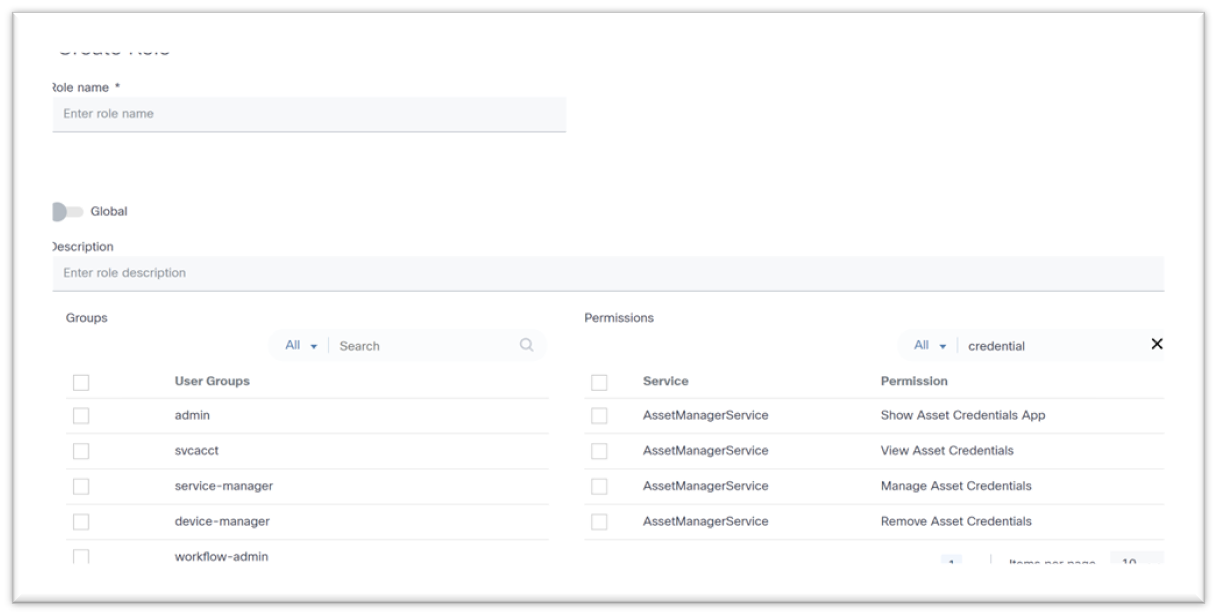
await rbacSpecProcessorObj.process();用户可以在“创建角色”和“编辑角色”页中查看已注册的权限。
映射权限
在上一节中创建的权限可以默认映射到角色,也可以通过定义角色映射来映射。
定义权限映射
要将定义的权限映射到默认角色,请在microservice/src/config/device-role-permissions-mapping-spec.json路径中创建新的JSON文件。
在下面的示例中,三(3)个权限映射到BPA超级管理员角色,两(2)个权限映射到Tenant Admin角色,一(1)个权限映射到Network Operator角色。
{
"service": "AssetManagerService",
"roles": [
{
"name": "BPA Super Admin",
"permissions": [
{"name":"view","displayName":"View Asset Credentials","group": "credential"},
{"name":"remove","displayName":"Remove Asset Credentials","group": "credential"},
{"name":"manage","displayName":"Manage Asset Credentials Add, Update and Delete Asset Credentials","group": "credential"}
]
},
{
"name": "Tenant Admin",
"permissions": [
{"name":"view","displayName":"View Asset Credentials","group": "credential"},
{"name":"remove","displayName":"Remove Asset Credentials","group": "credential"}
]
},
{
"name": "Network Operator",
"permissions": [
{"name":"view","displayName”:"View Asset Credentials","group": "credential"}
]
}
]
}
更新权限映射
要更新权限映射,请执行以下操作:
- 从@cisco-bpa-platform/mw-util-common-app导入rbacHelper和rbacPermissionMappingHelper。
const { rbacHelper, rbacPermissionMappingHelper } = require('@cisco-bpa-platform/mw-util-common-app');- 运行以下命令以更新角色权限映射:
let rbacUtilObj = rbacHelper.getRbacUtilObj();
let registryDetails = await rbacUtilObj getRegistryByName({}, 'device-role-permissions-mapping-spec');
if (Array.isArray(registryDetails) && registryDetails.length === 0) {
let rbacPermissionMappingSpecProcessorObj = rbacPermissionMappingHelper.getRbacSpecProcessorUtil() ;
let rolePermissions = require('./config/device-role-permissions-mapping-spec');
rbacPermissionMappingSpecProcessorObj.setSpec(rolePermissions);
await rbacPermissionMappingSpecProcessorObj.process();
let rbacUtilObjRegister = rbacHelper.getRbacUtilObj();
await rbacUtilObjRegister addRegistry({}, 'device-role-permissions-mapping-spec');
}- 运行以下命令以处理文件、创建权限列表并使用角色映射权限:
async function permissionsSpecProcessor() {
let resources = require('./config/device-permissions-spec');
let rbacSpecProcessorObj = rbacSpecProcessorHelper.getRbacSpecProcessorlltil();
rbacSpecProcessorObj.setSpec(resources);
await rbacSpecProcessorObj.process();
let rbacUtilObj = rbacHelper.getRbacUtilObj();
let registryDetails = await rbacUtilObj.getRegistryByName({} 'device-role-permissions-mapping-spec');
if (Array.isArray(registryDetails) && registryDetails.length === 0) {
let rbacPermissionMappingSpecProcessorObj = rbacPermissionMappingHelper.getRbacSpecProcessorUtil();
let rolePermissions = require('./config/device-role-permissions-mapping-spec');
rbacPermissionMappingSpecProcessorObj.setSpec(rolePermissions);
await rbacPermissionMappingSpecProcessorObj.process();
let rbacUtilObjRegister = rbacHelper.getRbacUtilObj();
await rbacUtilObjRegister.addRegistry({}, 'device-role-permissions-mapping-spec');
}
}修订历史记录
| 版本 | 发布日期 | 备注 |
|---|---|---|
1.0 |
23-Sep-2025
|
初始版本 |
 反馈
反馈