Where mayhem meets its match
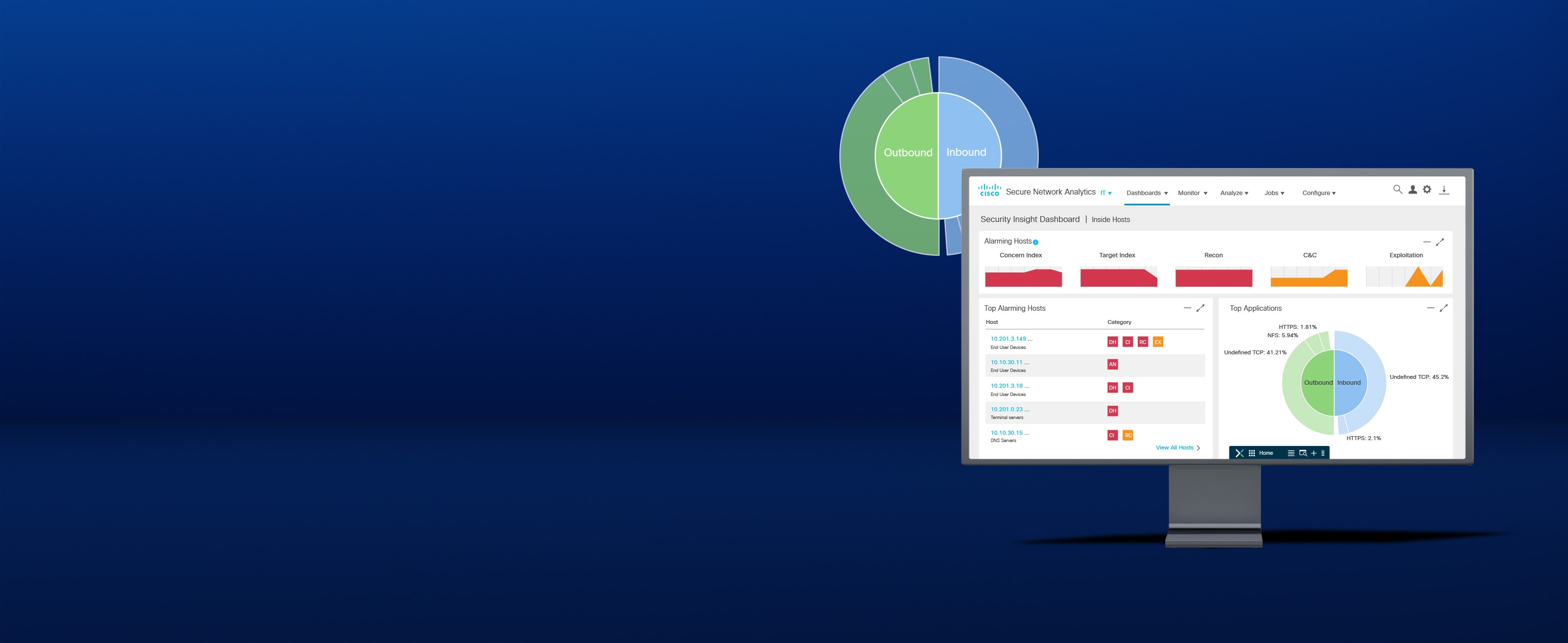
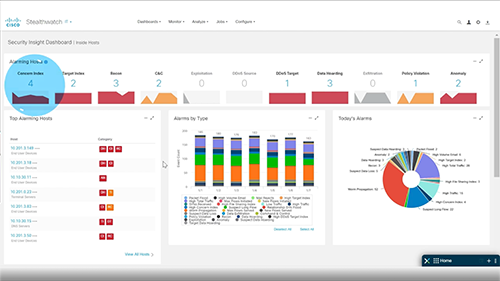
Analyze your existing network data to help detect threats that may have found a way to bypass your existing controls, before they can do serious damage.
Forewarned is forearmed
Detect attacks in real time across the dynamic network with high-fidelity alerts enriched with context, including user, device, location, timestamp, and application.
Reduce policy violations
Validate the efficacy of policies, adopt the right ones based on your environment's needs, and streamline policy violation investigations.
Reveal the unknown
Use advanced analytics to quickly detect unknown malware, insider threats like data exfiltration and policy violations, and other sophisticated attacks.
Analyze with ease
Identify and isolate threats in encrypted traffic without compromising privacy and data integrity.
Security that's even better than the sum of its parts
Where network nuances are never a problem
Use Secure Network Analytics with Identity Services Engine (ISE) to define smarter segmentation policies, create custom alerts to detect unauthorized access, and ensure compliance.
Unified threat detection across on-premises and clouds
Get SaaS-based visibility and threat detection across your on-premises network and all major public cloud platforms without software agents with Secure Cloud Analytics.
Where chaos meets calm
The Cisco SecureX platform combines the best of our integrated security technologies, including network analytics for threat detection and response.
Add value to security solutions
Cisco Security Enterprise Agreement
Instant savings
Experience security software buying flexibility with one easy-to-manage agreement.
Services for security
Let the experts secure your business.
Get more from your investments and enable constant vigilance to protect your organization.