Introduction
This document introduces Cisco Umbrella (formerly OpenDNS) and provides general guidelines for its deployment. The purpose of this document is to:
-
Provide an overview of Cisco Umbrella WLAN feature
-
Highlight supported key features
-
Provide details on deploying and managing Cisco Umbrella on WLC
Pre–requisite
AireOS 8.4 or newer is required on the Cisco Wireless LAN Controller to support Cisco.
 Note |
In order to upgrade to AireOS 8.4, customers must have AireOS 8.0 or higher release |
Components Used
The information in this documentwas created from devices in a specificlab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Conventions
Refer to Cisco Technical Tips Conventions for more information on document conventions.
Feature Introduction
Cisco Umbrella is a Cloud delivered network security service, which gives insights to protect devices from malware and breach protection in real time. It uses evolving big data and data mining methods to proactively predict attacks also do category based filtering.
Terminology involved in the working of the feature:
-
API Token is issued from Cisco Umbrella Portal and is only used for device registration
-
Device Identity is a unique device identifier. Policy is enforced per identifier
-
EDNS is an Extension mechanism for DNS which carries tagged DNS packet
-
FQDN is Fully Qualified Domain Name
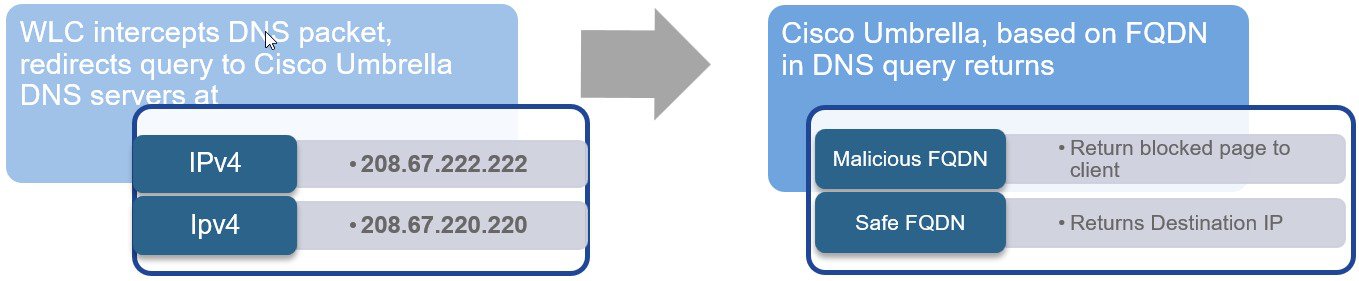
DNS request always precedes web request. Wireless Lan Controller intercepts DNS request from the client and redirects the query to Cisco Umbrella in the cloud (208.67.222.222, 208.67.220.220). Cisco Umbrella servers resolve the DNS query and enforces preconfigured security filtering rules on a per identity basis to mark the domain as either malicious which will return a blocked page to client or safe returning resolved IP address to client.
Cisco Umbrella General Work Flow
-
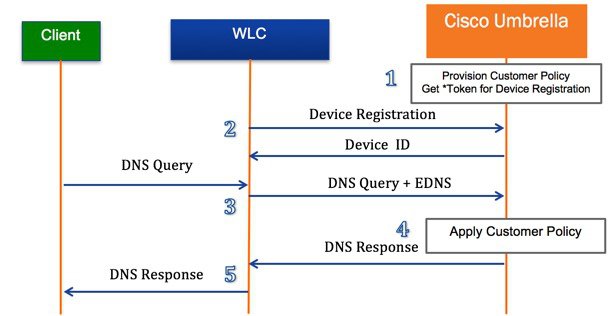
WLC registration with Cisco Umbrella server is a one-time process and happens over a secure HTTPS tunnel
-
Obtain API Token for device (WLC) registration from Cisco Umbrella dashboard
-
Apply the Token on Wireless Lan Controller. This should register the device to Cisco Umbrella account. Next, create Cisco Umbrella Profile/s on WLC. Profiles will automatically be pushed to the Cisco Umbrella as Identities and policy will be enforced on a per identity basis
-
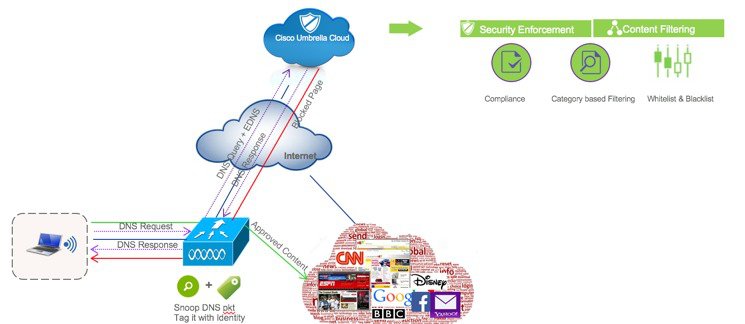
Wireless client traffic flow from to Cisco Umbrella server
-
A wireless client sends a DNS request to WLC
-
WLC snoops the DNS packet and tags it with a Cisco Umbrella Profile. Profile is the identity of the packet which also resides on Cisco Umbrella
-
This EDNS packet is redirected to the Cisco Umbrella cloud server for name resolution
-
Cisco Umbrella then enforces a policy on it depending on the identity and applies category based filtering rules to ensure organization compliance
-
Depending on the rules, it either returns a blocked page or resolved ip address to the client for the DNS request queried
Configuring the Cisco Umbrella Wireless LAN Controller Integration
Procedure
| Step 1 |
Cisco Umbrella provisioning involves creating a user account on Cisco Umbrella cloud. Subscription is per account and Cisco Umbrella offers14 day obligation free trial license. Permanent License is covered under CiscoOne Advanced Subscription. |
| Step 2 |
Next, enable Wireless Controller (GUI or CLI) for Cisco Umbrella . |
| Step 3 |
WLC registers to the cloud account over a secure HTTPS tunnel. |
| Step 4 |
Configure profiles (identities) on WLC. Profile can be mapped to either WLAN, AP group or incorporated into local policy. |
| Step 5 |
WLC redirects DNS packets to Cisco Umbrella cloud. |
| Step 6 |
Security policies on Cisco Umbrella are applied per Identity. Cisco Umbrella configuration steps on Wireless Controller involve enabling Cisco Umbrella function, configuring API Token, creating Profile/s and mapping the profile to either a WLAN, an AP group or a Local Policy. The policy priority order (starting from highest) is:
Cisco Umbrella profile when mapped to local policy allows for a granular differentiated user browsing experience based on dynamic evaluation of attributes (user role, device type etc). In rest of the document, we will discuss following two scenarios:
|
Scenario 1: Configuring Local Policies for Cisco Umbrella
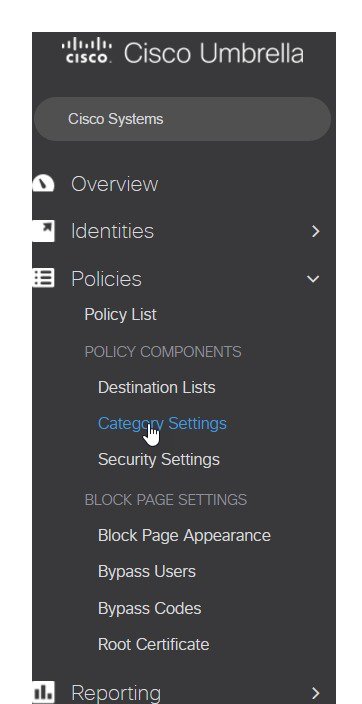
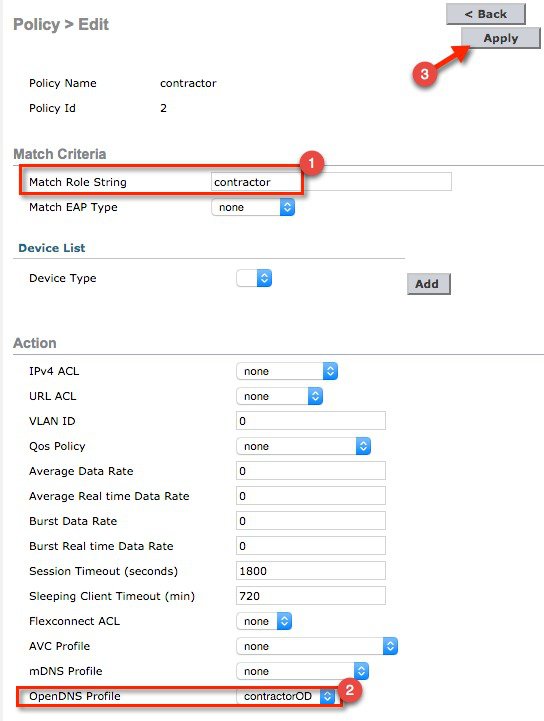
In an organization, our goal is to restrict internet access (for particular websites) to users based on their role types. For example, employees should be permitted full internet access barring sites such as adult, gambling, nudity and contractor access should be more rigid barring them access to social websites, sports, adult, gaming, nudity, etc.
-
On Cisco Umbrella Server: Create an account, generate API token for device (WLC) registration
-
On WLC: Enable Cisco Umbrella globally, apply API token and create Cisco Umbrella profiles for employee and contractor.
-
On Cisco Umbrella Server: Create Category definitions/rules and Policies for employee and contractor.
-
On WLC: Create Local policy each for employee and contractor tying the AAA returned role and Cisco Umbrella profile under each.
-
On WLC: Tie the two local policies to the dot1x WLAN
Procedure
| Step 1 |
Create your own 14 day trial account here https://signup.umbrella.com/  |
||
| Step 2 |
Login to your account at https://login.umbrella.com/ 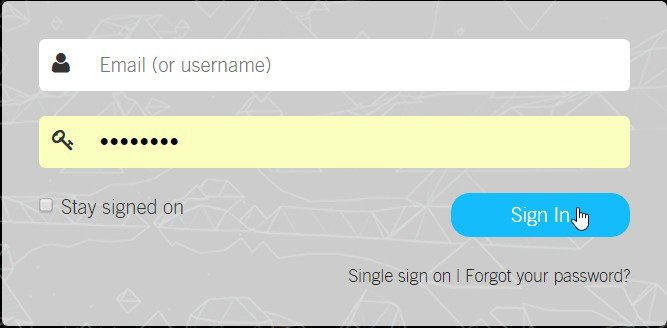 |
||
| Step 3 |
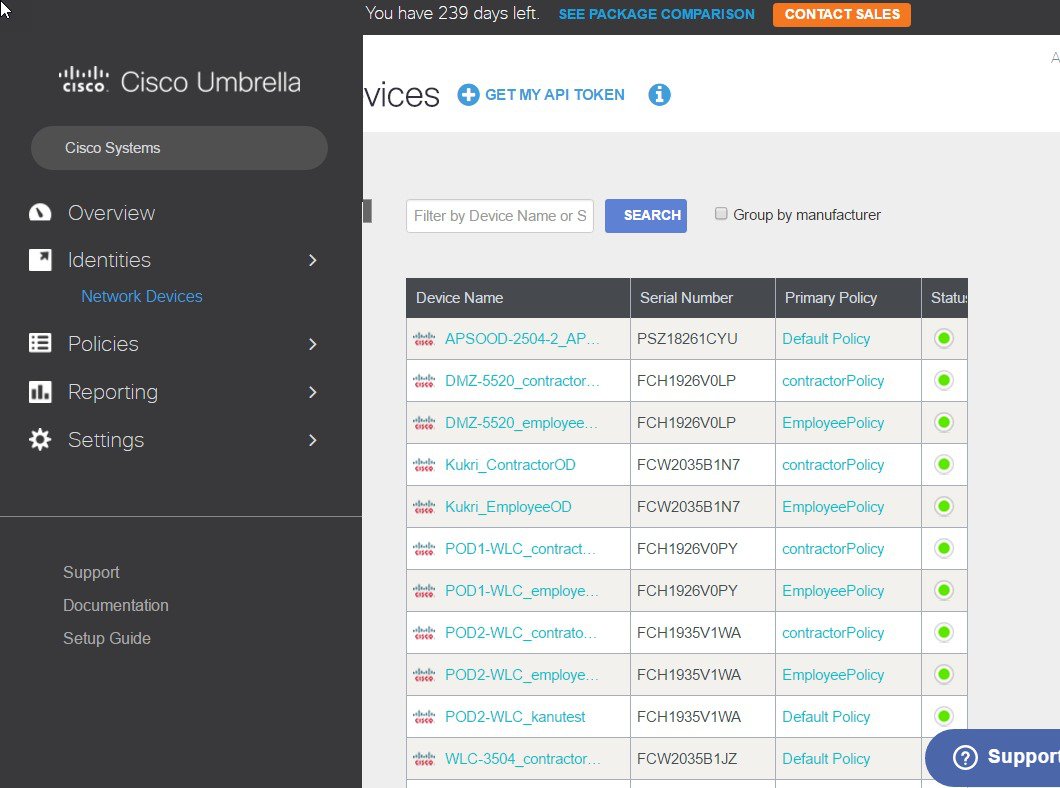
From Cisco Umbrella main dashboard landing page, click Identities from the side menu, then choose Network Devices. At the top of the page, click the + icon and click on GET MY API TOKEN as shown below. 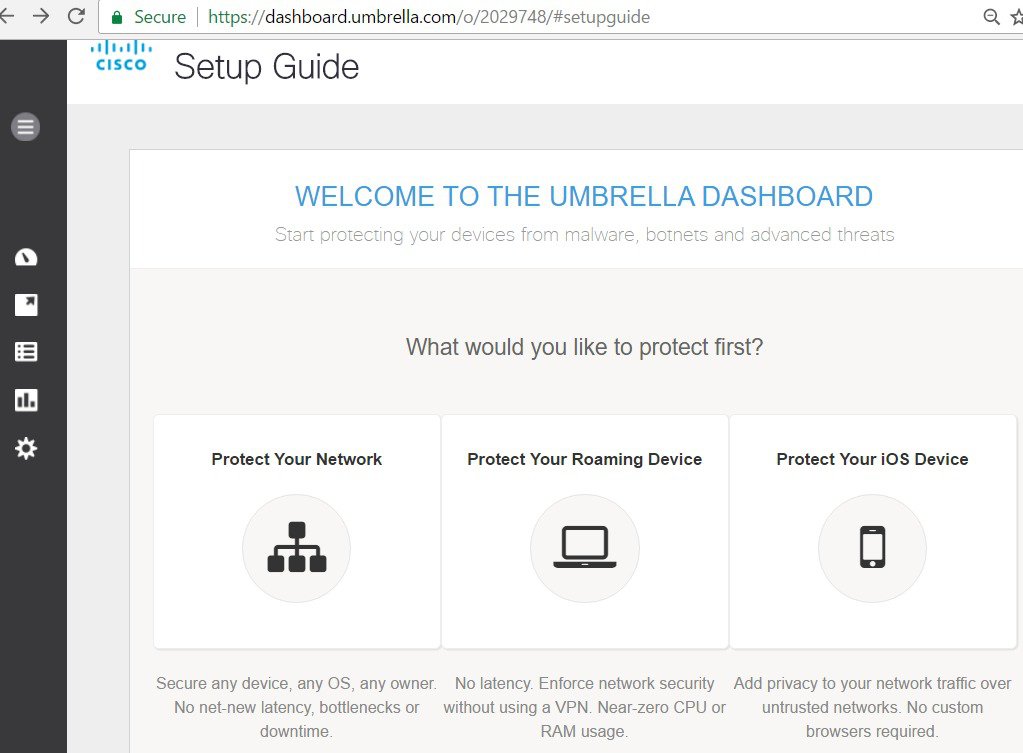 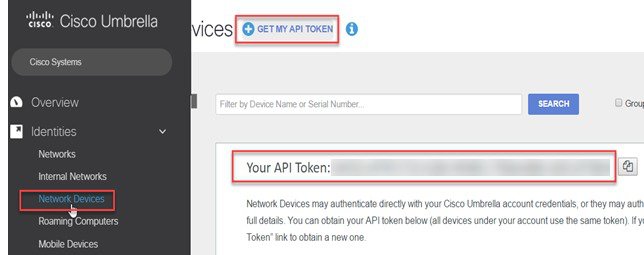 |
||
| Step 4 |
From WLC main menu, go to Controller > General and enter a DNS Server IP address that can resolve domains. This is needed for the first time before enabling Cisco Umbrella feature on the WLC. 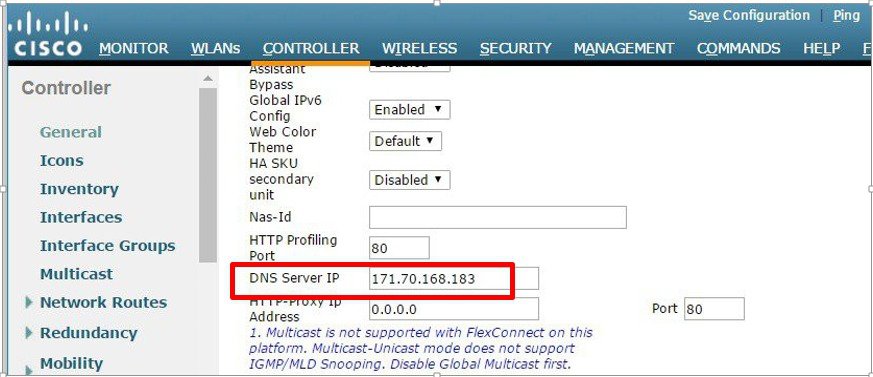 |
||
| Step 5 |
From WLC main menu, go to Security >OpenDNS > General> enable OpenDNS Global Status. 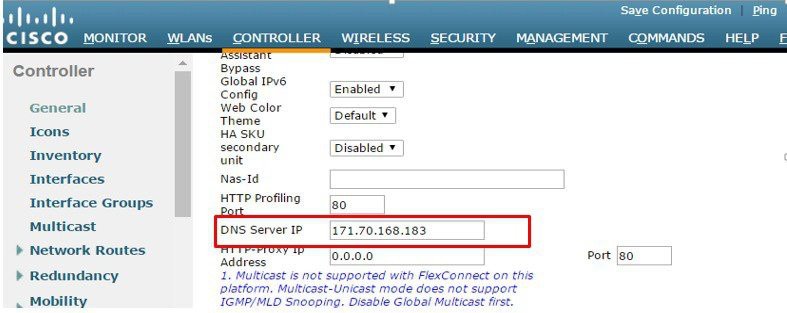 |
||
| Step 6 |
On the same WLC screen, configure API Token obtained from Umbrella dashboard earlier(Step 3)  |
||
| Step 7 |
From the same page, create OpenDNSProfiles Security > OpenDNS >General. 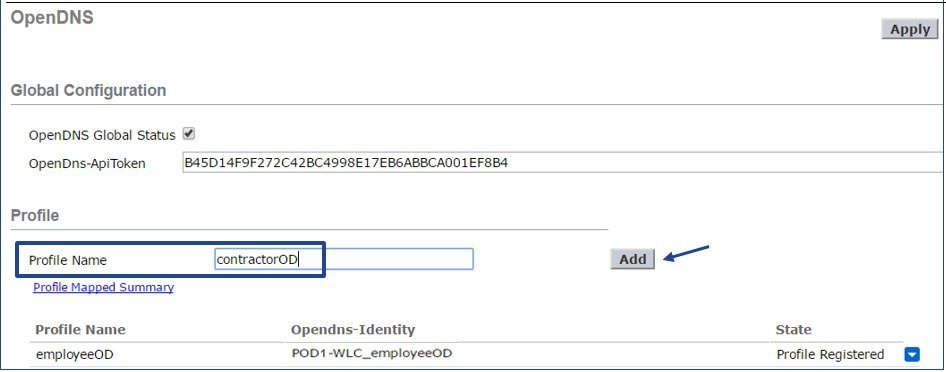 |
||
| Step 8 |
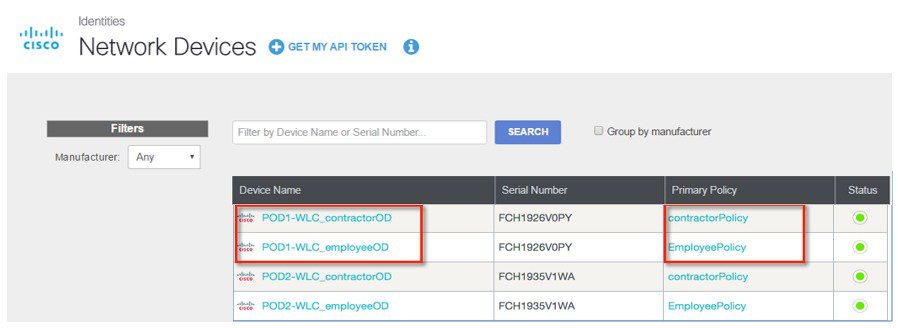
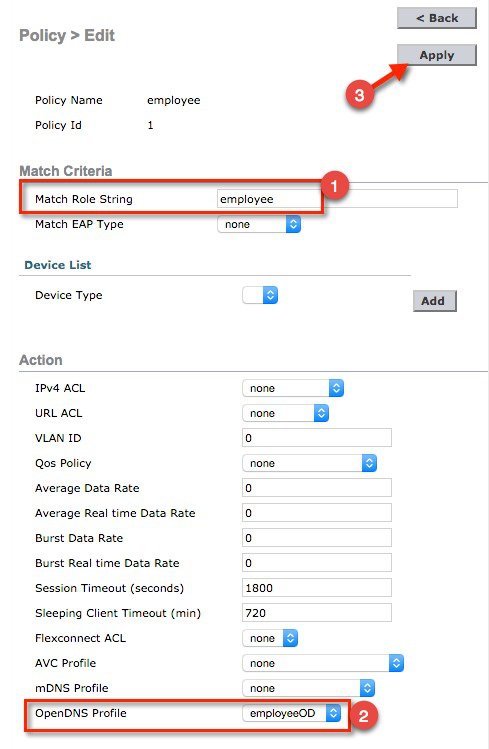
On WLC, create two OpenDNS profiles, one for employee(employeeOD) and anotherfor contractor (contractorOD) via CLI or GUI. These profiles shouldautomatically be pushed to your OpenDNS accountas Identitiesand you should see the State of the Profiles populated as Profile Registered. This is subject to a successful connection between the WLC and Umbrella server. 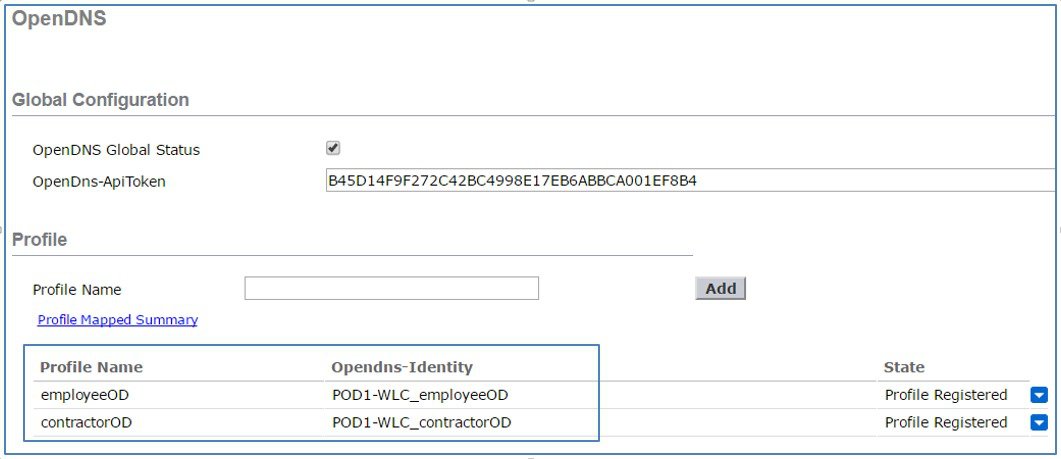 On CLI,
you can verify the two profiles as shown:
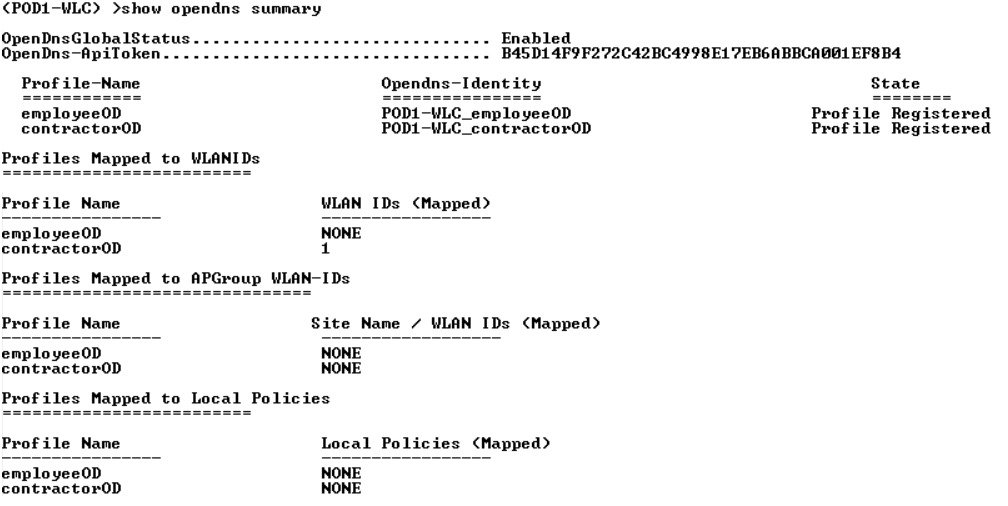
|
||
| Step 9 |
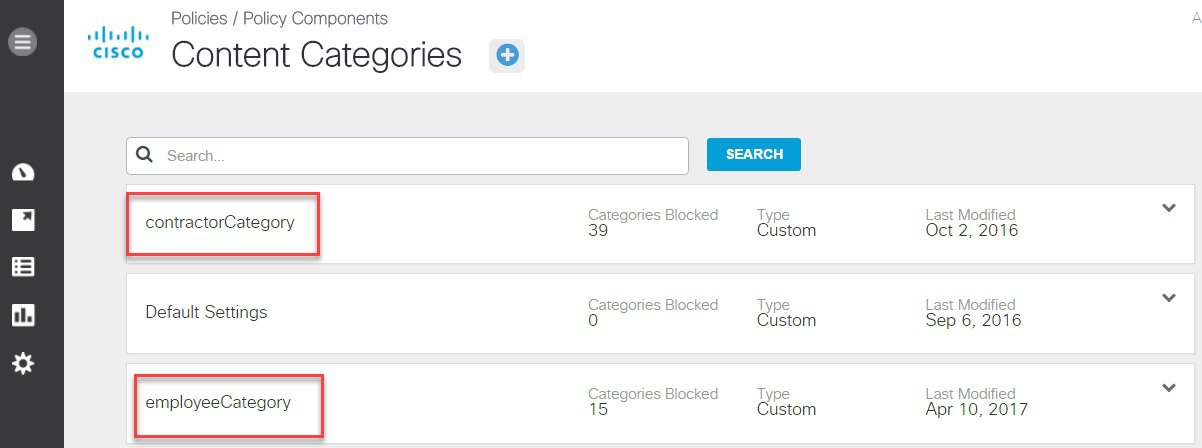
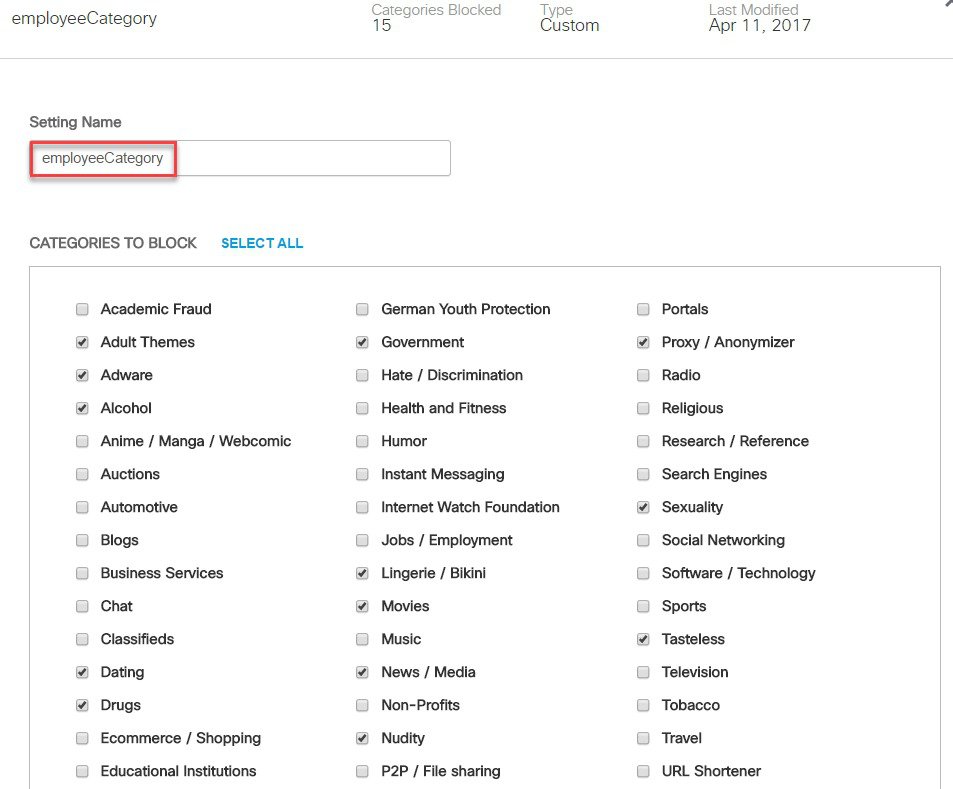
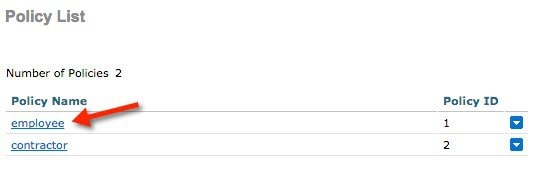
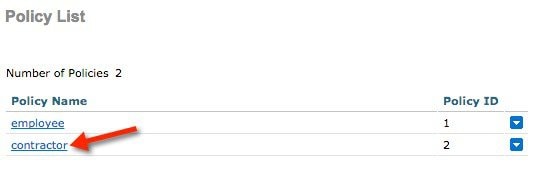
Finally, create and configure two Policies on the Cisco Umbrella server. From the left menu bar, browse to Policies > Policy List. 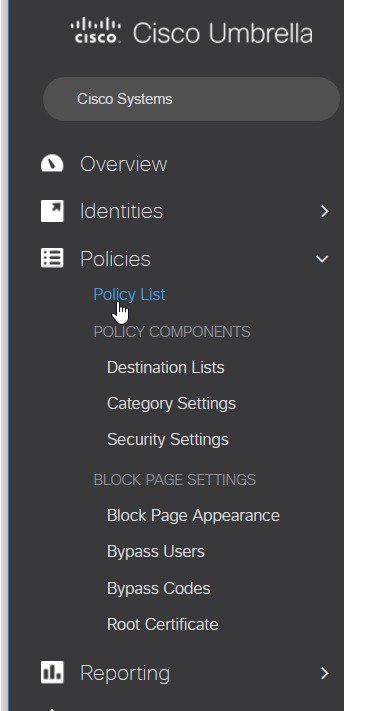 We have created these two policies:
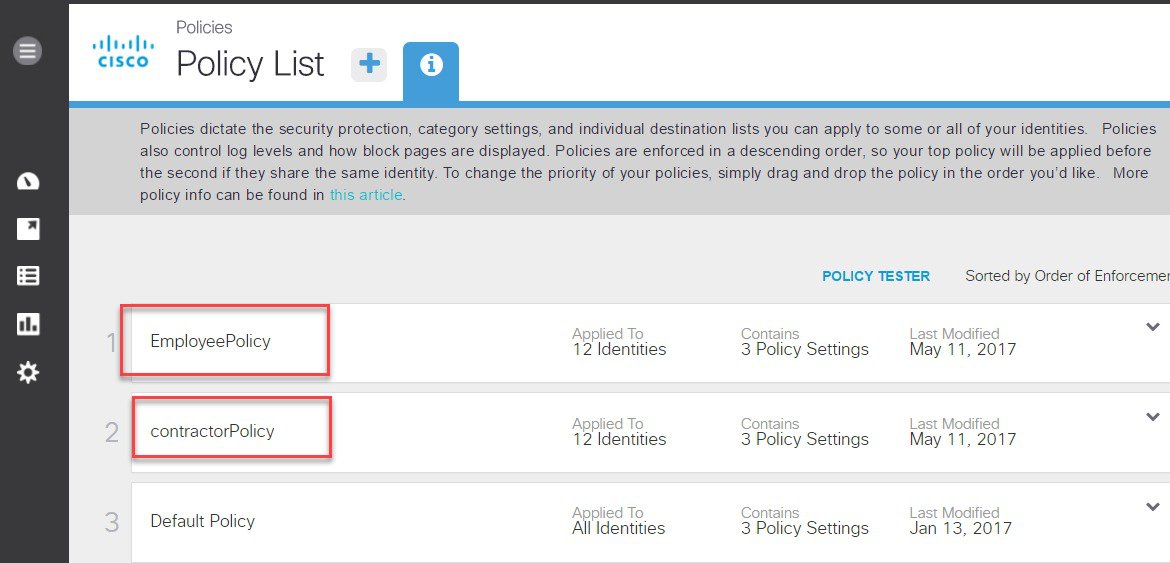 A Policy Wizard exists under each Policy screen showing Identities affected and the mapped category setting. Here, EmployeePolicy is assigned to employeeOD Identity and tied to a categoryemployeeCategory (created in the last step). Similarly, contractorPolicy is assigned to contractorOD Identity and tied to a custom category contractorCategory created earlier. 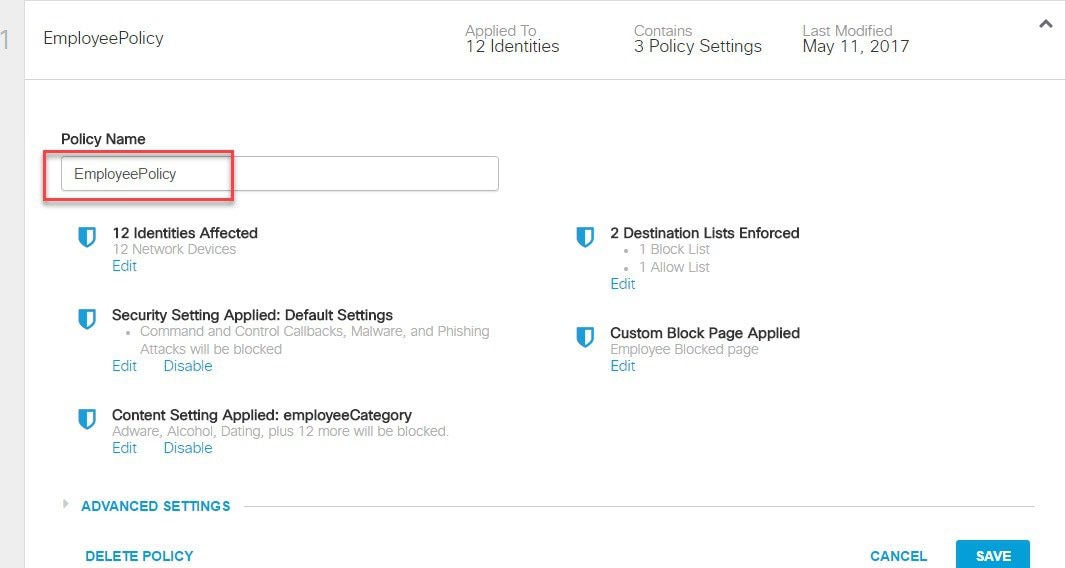 Click on Edit under Identities Affected to see all the identities/network devices (PodX-WLC_employeeOD) mapped to this Policy. 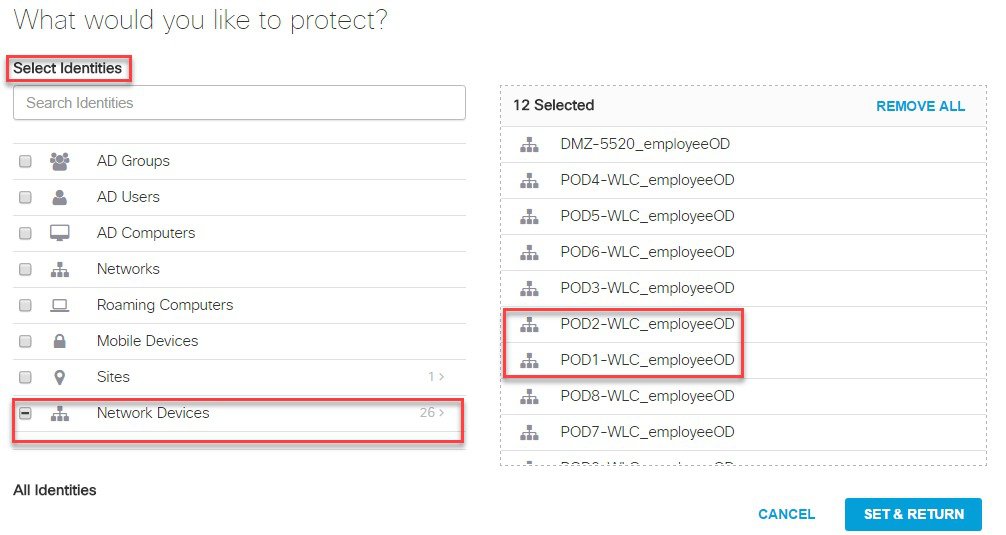 Click SET & RETURN and go to Content Setting Applied to verify category setting applied to this Policy as shown below. 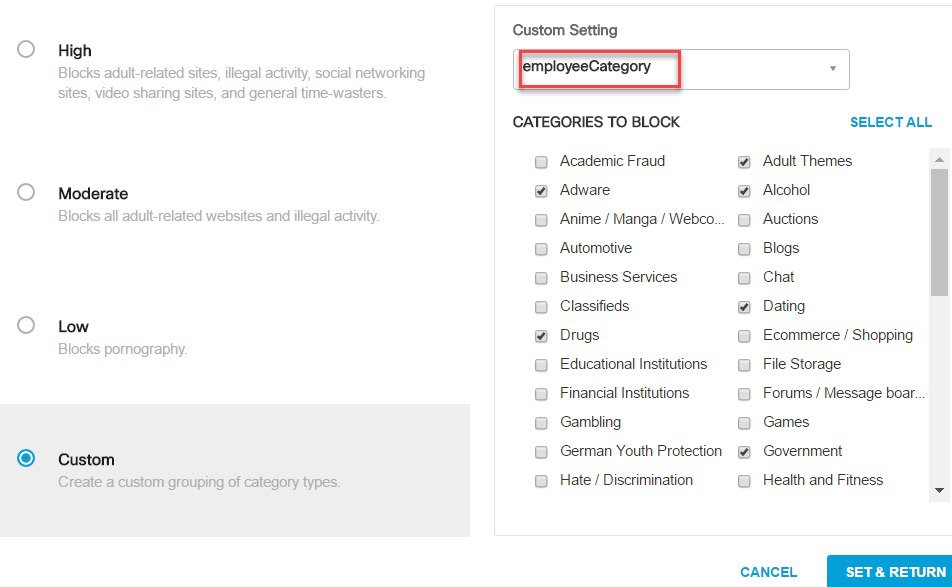 |
||
| Step 10 |
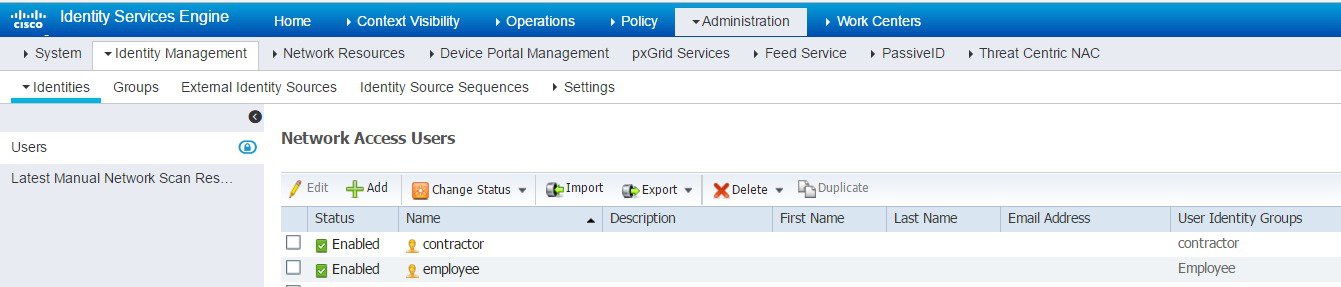
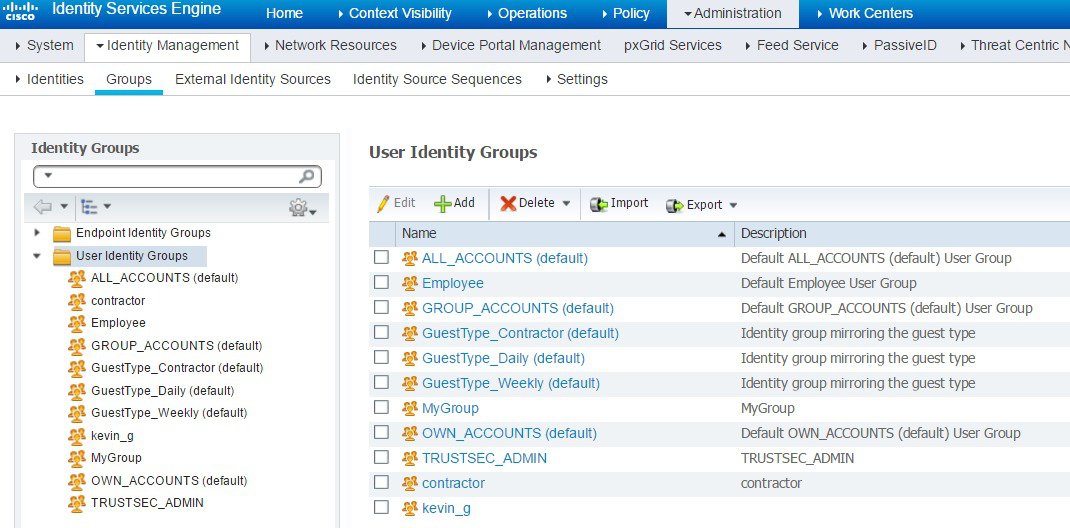
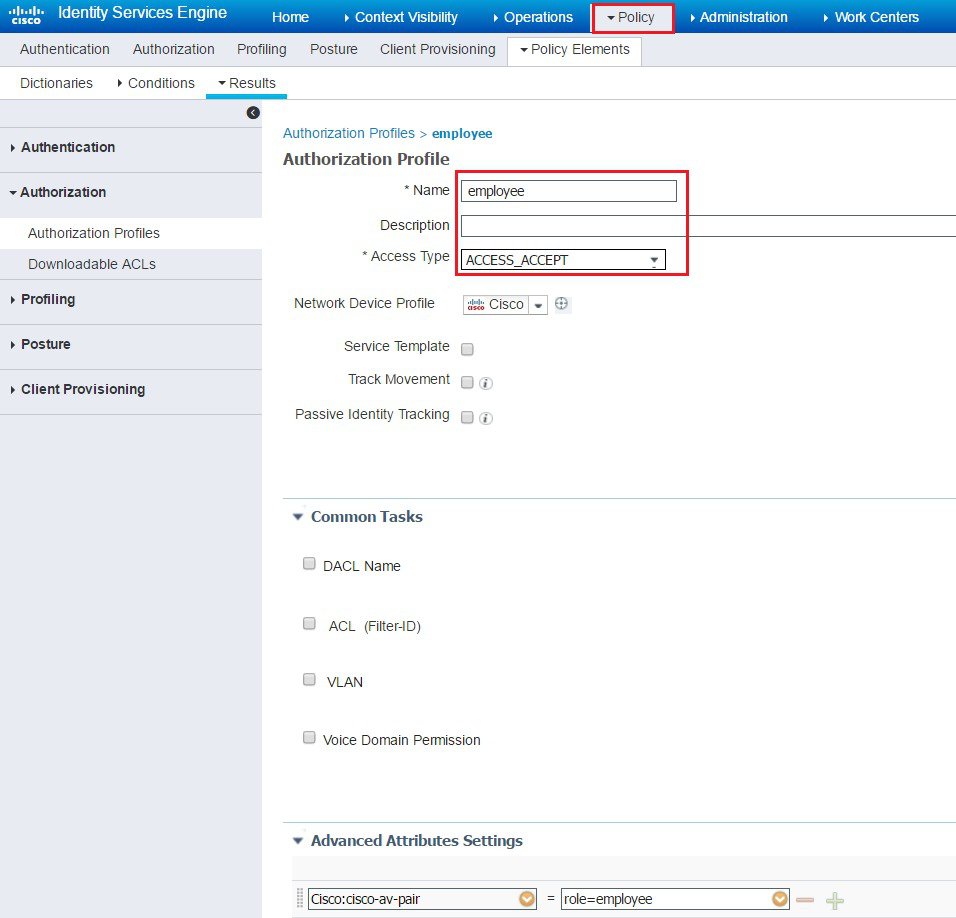
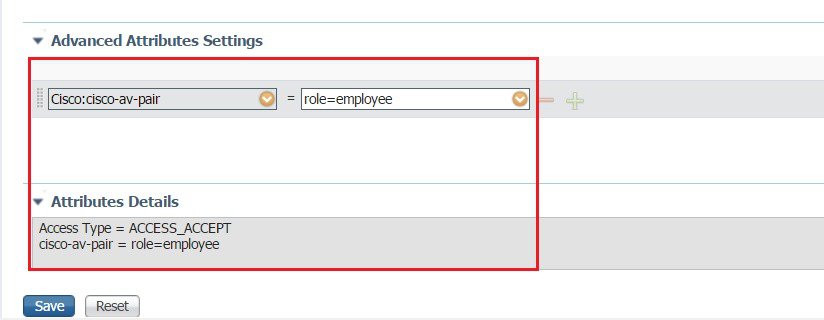
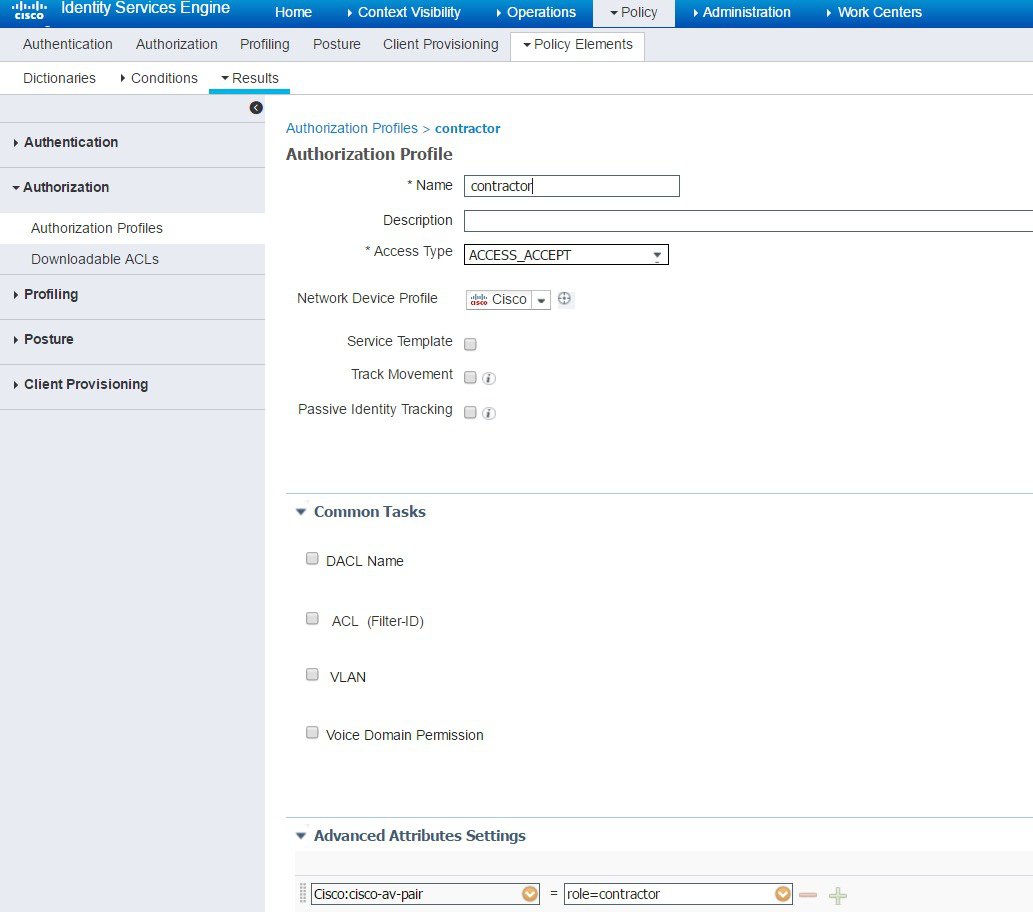
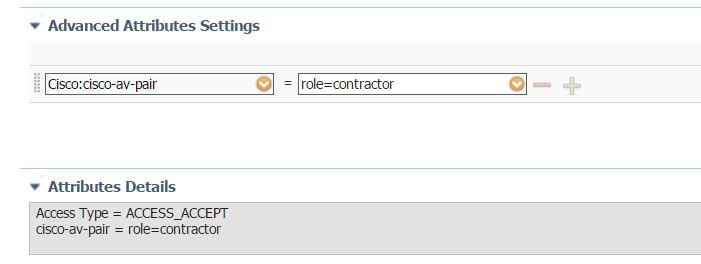
Configuring User Roles on ISE. |
||
| Step 11 |
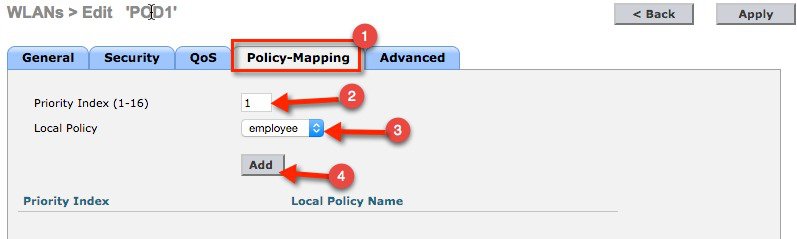
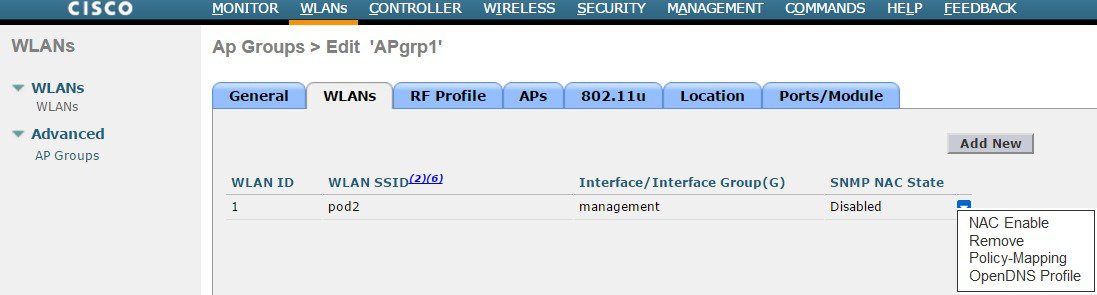
Configuring Local Policies for OpenDNS. User can now configure user role based Local Policy and tie the Cisco Umbrella profile to it. Finally, map the local policy to a particular WLAN. |
||
| Step 12 |
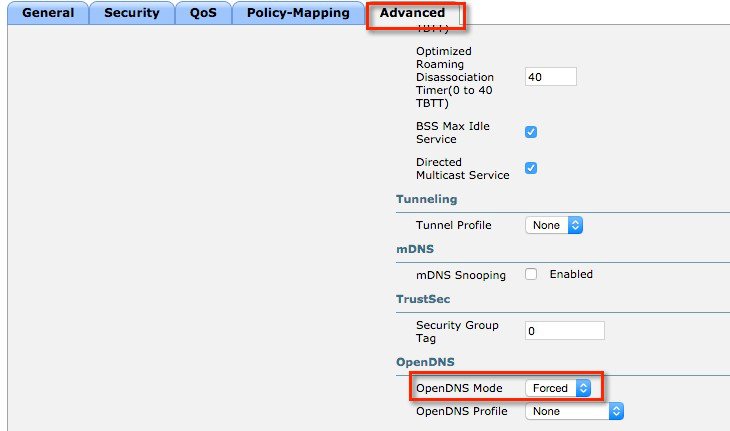
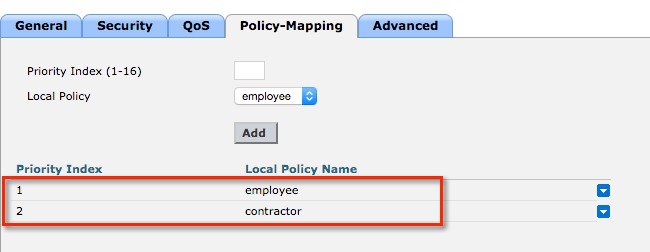
Configuring OpenDNS on WLAN. |
Scenario: 2 Configuring WLAN/AP Group for Cisco Umbrella
Similar to Local Policy, OpenDNS profile can be attached to a WLAN or to an AP group. Section below shows screenshots from GUI and CLI commands on how to tie OpenDNS profile to a WLAN and AP group. It is assumed that the Cisco Umbrella account is already created and API token is copied from the Umbrella dashboard.
Procedure
| Step 1 |
From WLC main menu, go to Controller >General and enter a DNS Server IP address that can resolve domains. This is needed for the first time before enabling Cisco Umbrella feature on the WLC. 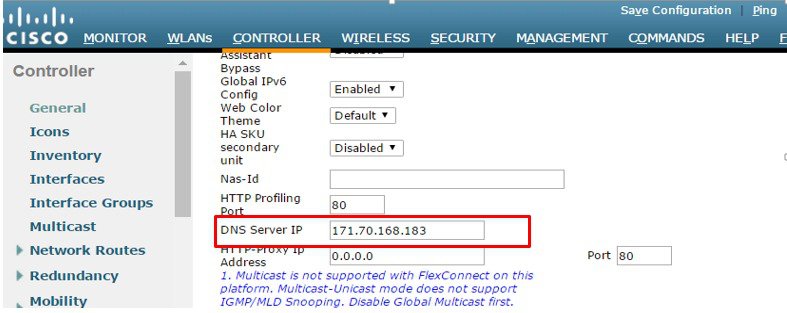 |
| Step 2 |
Enable openDNS globally on WLC by going to Security> OpenDNS >General. 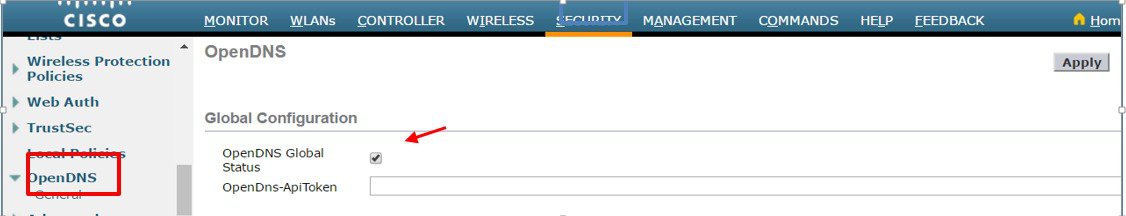 |
| Step 3 |
Configure API Token obtained from Cisco Umbrella account. 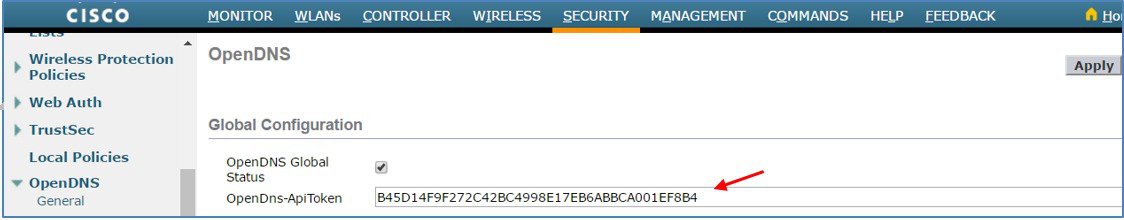 |
| Step 4 |
Create OpenDNS Profiles . 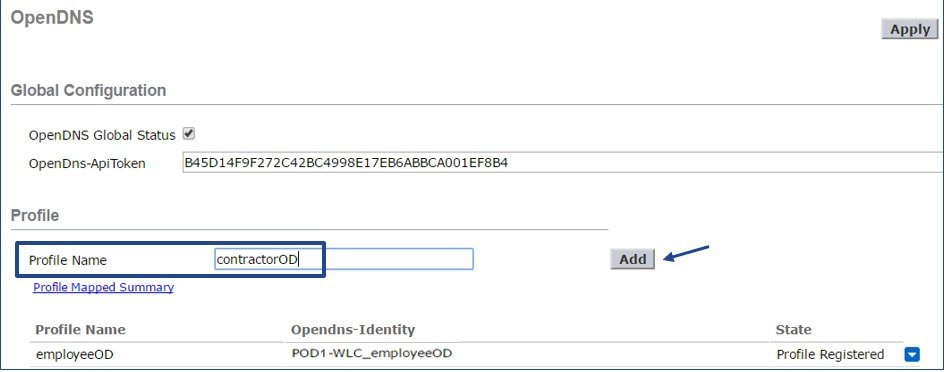 |
| Step 5 |
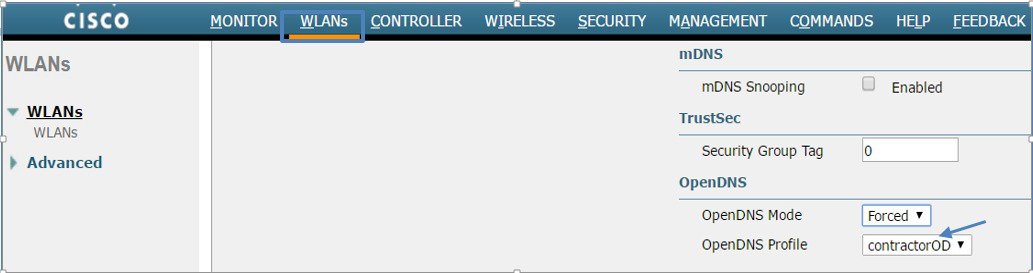
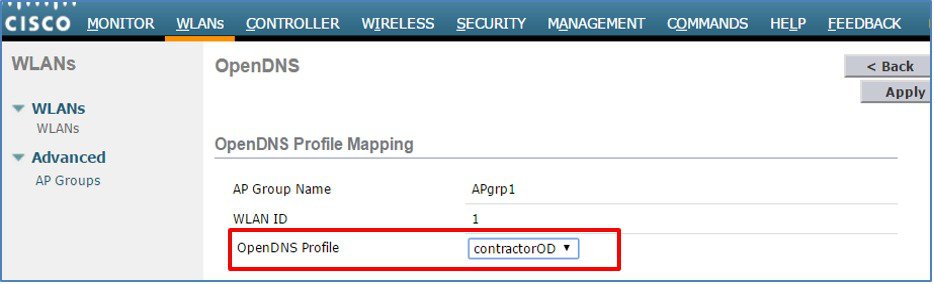
Map the Profile to WLAN or AP group. To view OpenDNS mapping, go to Security > OpenDNS > General and click on Profile Mapped Summary as shown: 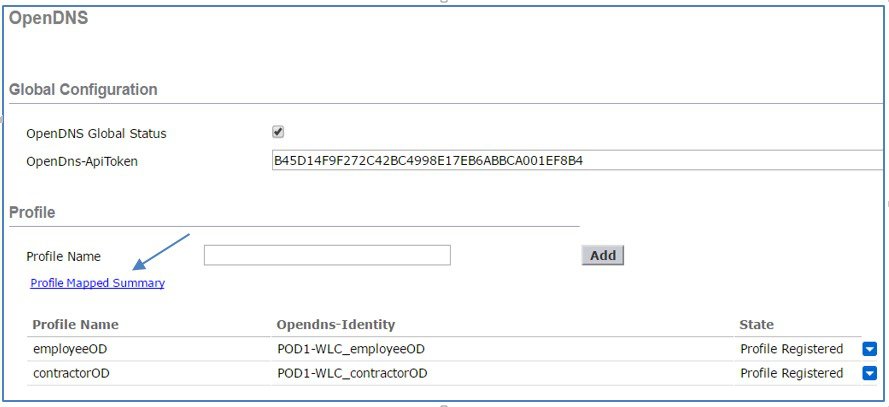 Here, the OpenDNS Profile contractorOD is mapped WLAN ID 1. 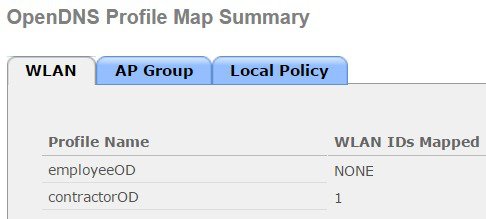 On the sameOpenDNS Profile Map Summary page, under AP Group, profile contractorOD is also mapped to AP Group APgrp1 as shown 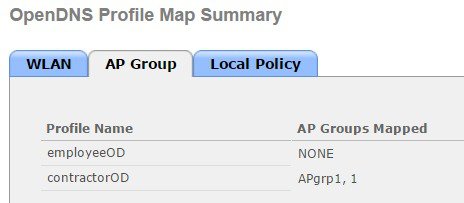 From CLI 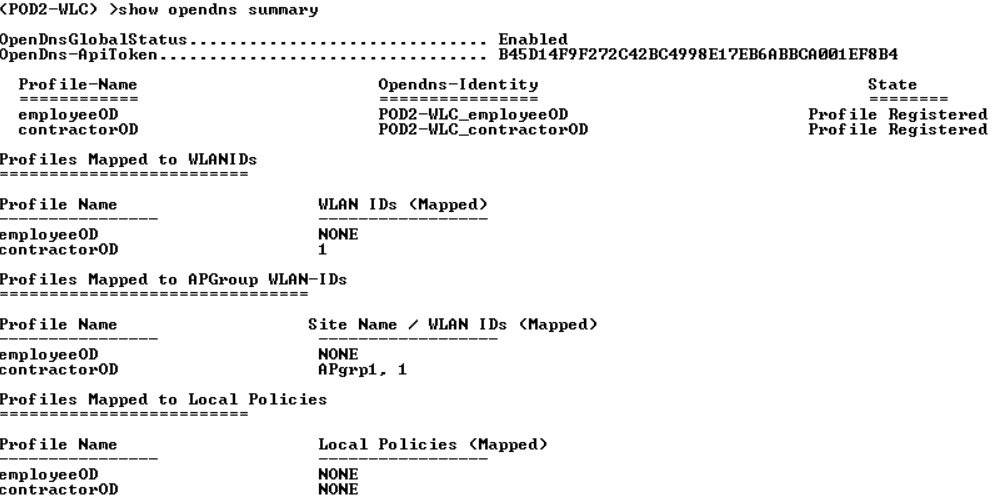 |
OpenDNS WLAN configuration modes
Administrator can configure OpenDNS on a WLAN in three modes under WLAN advanced tab.
-
DHCP Proxy for DNS override
Interface level config. Part of DHCP process to propagate OpenDNS ip address to all WLANs associated to Interface. Happens in the client join phase.
-
OpenDNS Force mode: (Enabled by default)
Enforced per WLAN, blocks intentional client activity after client has associated to WLAN.

Note
-
If the client device has DNS for any IP address other than opendns ip's this option will cause the client traffic to be blackholed.
-
WLC does not do a proxy in force mode but will simply re-direct all the DNS packets to OpenDNS only , so the reply to the client is received from opendns ip only. Client who do not have opendns ip as one of configured DNS IP can reject this causing connectivity issues.
Adding opendns as one of the DNS IP will help in some of these cases.
WLC does not do a proxy in force mode but will simply re-direct all the DNS packets to OpenDNS only , so the reply to the client is received from opendns ip only
If DNS ip change by user is to be allowed , we should use OpenDNS Ignore mode .
-
-
OpenDNS Ignore mode
WLC honors the DNS server used by the client; it could be Cisco Umbrella cloud servers or enterprise/ external DNS
-
OpenDNS Copy mode (not included in 8.4 release)
A copy of OpenDNS packets where all internet bound DNS traffic is forwarded to Cisco Umbrella cloud servers without any policy options (no block/redirect)
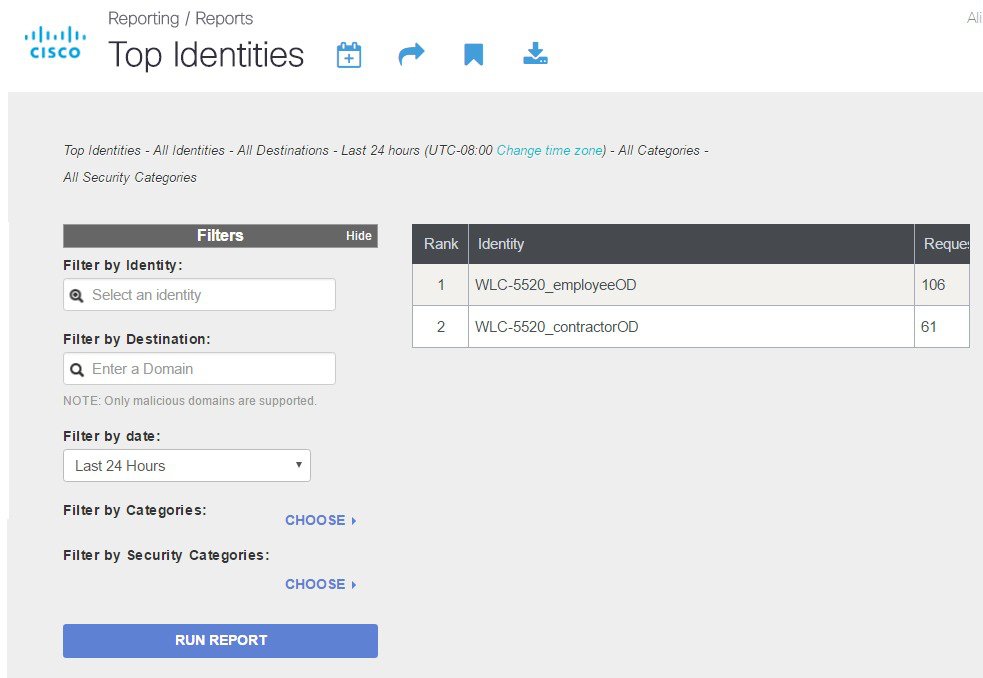
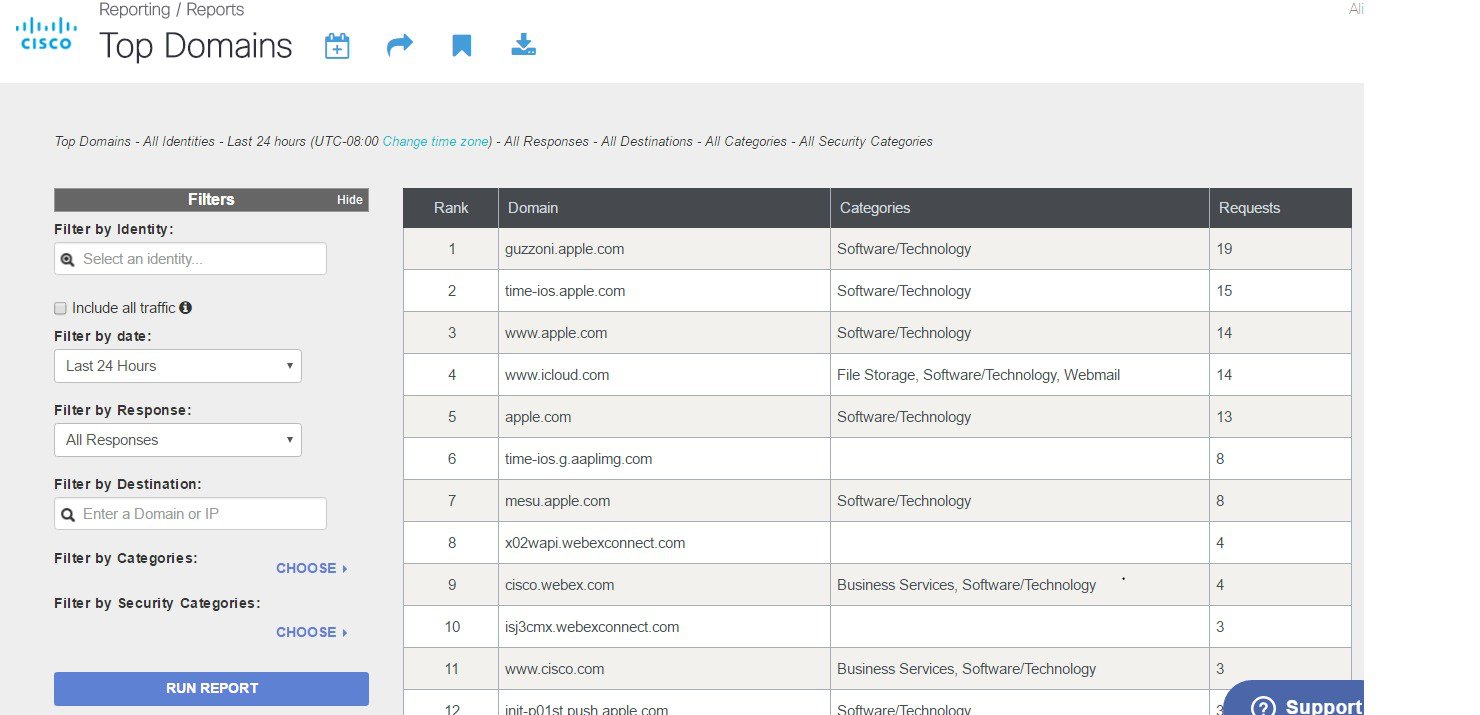
Cisco Umbrella Activity Reporting
Administrator can login to Cisco Umbrella server to view and generate reports regarding the clients activity, find the infected devices, targeted users trying to access forbidden sites. These reports can be filtered by client identity, destination and source IP. Reporting may take up to 2 hours to appear after a new identity is registered.
OpenDNS Support
-
WLC supported platform- 5508,5520,7500,8510,8540. ME, vWLC is not supported
-
AP mode supported–Local mode, Flex central switching.
-
10 different OpenDNS Profiles configurable on WLC
-
Guest (Foreign–Anchor) scenario, profile applies at Anchor WLC
OpenDNS Limitations
-
Client is connected to a web proxy and does not send DNS query to resolve the server address
-
Application or host uses IP address directly instead of DNS to query domains



 Feedback
Feedback