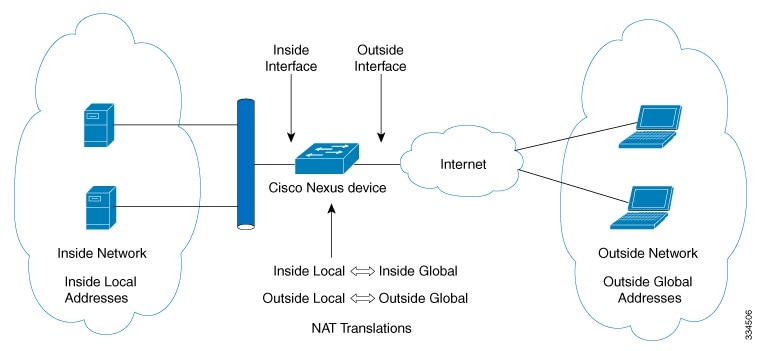
Dynamic Network
Address Translation (NAT) translates a group of real IP addresses into mapped
IP addresses that are routable on a destination network. Dynamic NAT
establishes a one-to-one mapping between unregistered and registered IP
addresses; however, the mapping can vary depending on the registered IP address
that is available at the time of communication.
A dynamic NAT
configuration automatically creates a firewall between your internal network
and outside networks or the Internet. Dynamic NAT allows only connections that
originate inside the stub domain—a device on an external network cannot connect
to devices in your network, unless your device has initiated the contact.
Dynamic NAT
translations do not exist in the NAT translation table until a device receives
traffic that requires translation. Dynamic translations are cleared or timed
out when not in use to make space for new entries. Usually, NAT translation
entries are cleared when the ternary content addressable memory (TCAM) entries
are limited. The default minimum timeout for dynamic NAT translations is 30
minutes.

Note
|
For Cisco NX-OS 7.0(3)I2(3) and earlier releases, the minimum value of the sampling-timeout in the ip nat translation sampling-timeout command was reduced from 30 minutes to 15 minutes.
|

Note
|
For Cisco NX-OS 7.0(3)I3(1) and later releases , the ip nat translation sampling-timeout command is not supported. Statistics are collected every 60 seconds for the installed NAT policies. These statistics are
used to determine if the flow is active or not.
|
For Cisco NX-OS 7.0(3)I2(3) and earlier releases, the timeout of a dynamic NAT translation involves both the sampling-timeout
value and the TCP or UDP timeout value. The sampling-timeout specifies the time after which the device checks for dynamic
translation activity. It has a default value of 12 hours. All the other timeouts start only after the sample-timeout times
out. After the sampling-timeout, the device inspects the packets that are hitting this translation. The checking happens for
the TCP or UDP timeout period. If there are no packets for the TCP or UDP timeout period, the translation is cleared. If activity
is detected on the translation, then the checking is stopped immediately and a sampling-timeout period begins.
For Cisco NX-OS 7.0(3)I2(3) and earlier releases, after waiting for this new sampling-timeout period, the device checks for
dynamic translation activity again. During an activity check the TCAM sends a copy of the packet that matches the dynamic
NAT translation to the CPU. If the Control Plane Policing (CoPP) is configured at a low threshold, the TCP or UDP packets
might not reach the CPU, and the CPU considers this as inactivity of the NAT translation.
Dynamic NAT supports
Port Address Translation (PAT) and access control lists (ACLs). PAT, also known
as overloading, is a form of dynamic NAT that maps multiple unregistered IP
addresses to a single registered IP address by using different ports. Your NAT
configuration can have multiple dynamic NAT translations with same or different
ACLs. However, for a given ACL, only one interface can be specified.

 Feedback
Feedback