Cisco Nexus 1000v Network Segmentation Manager Configuration Guide, Release 4.2(1)SV1(5.1)
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- January 31, 2012
Chapter: Overview
Overview
This chapter provides an overview of Network Segmentation Manager (NSM) and includes the following sections:
•![]() Information About vCloud Director
Information About vCloud Director
•![]() Information About Network Segmentation Manager
Information About Network Segmentation Manager
Information About vCloud Director
VMware's vCloud Director 1.5 provides an abstraction layer that enables cloud service providers to provide an infrastructure as a service (IaaS) to various tenant organizations. vCloud Director also allows the tenant organizations to manage resources such as virtual data centers (vDCs), vApps, networks, and network pools. See Figure 1-1.
Figure 1-1 vCloud Director
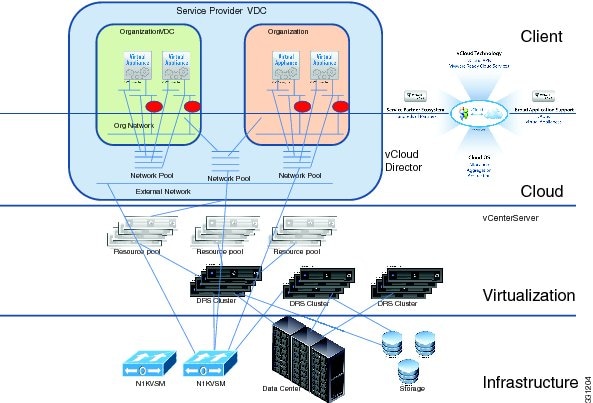
vCloud Director includes the following cloud resources:
•![]() Virtual data centers (vDCs)—Enables IT organizations to combine compute, storage, and networking resources to a vDC and deliver these resources to the users. There are two types of vDCs: provider vDCs and organization vDCs.
Virtual data centers (vDCs)—Enables IT organizations to combine compute, storage, and networking resources to a vDC and deliver these resources to the users. There are two types of vDCs: provider vDCs and organization vDCs.
•![]() Networks—Defines the boundaries and the respective service level for each function within a given cloud's network architecture. vCloud Director supports three types of networks: external networks, organization networks, and vApp networks. These networks are created as port profiles on the Cisco Nexus 1000V.
Networks—Defines the boundaries and the respective service level for each function within a given cloud's network architecture. vCloud Director supports three types of networks: external networks, organization networks, and vApp networks. These networks are created as port profiles on the Cisco Nexus 1000V.
•![]() Network pools—Provides a mechanism for dynamic provisioning of networks within an organization vDC. The three different types of network pools are VLAN-backed, network isolation-backed, and port group-backed. All the types of network pools can be backed by using the Cisco Nexus 1000V.
Network pools—Provides a mechanism for dynamic provisioning of networks within an organization vDC. The three different types of network pools are VLAN-backed, network isolation-backed, and port group-backed. All the types of network pools can be backed by using the Cisco Nexus 1000V.
See the VMware vCloud Director Administrator's Guide and vCloud Director User's Guide for more information.
Information About Network Segmentation Manager
Cisco Network Segmentation Manager (NSM) integrates VMware's vCloud Director 1.5 with Cisco Nexus 1000V for networking management. See Figure 1-2 and Figure 1-3. In this figure, NSM communicates with vShield Manager to integrate with the vCloud Director, enabling you to use the Cisco Nexus 1000V for backing all types of network pools (VLAN-backed, network isolation-backed, and port group-backed) supported by vCloud Director.
Figure 1-2 Integration of vCloud Director with Cisco Nexus 1000V

Figure 1-3 Cisco Nexus 1000V Topology Diagram with vCloud Director
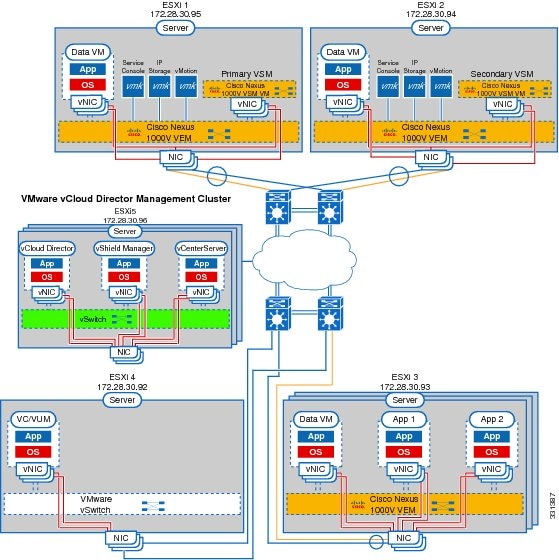
When a cloud administrator creates networks on demand within the vCloud Director, vShield Manager issues requests to NSM to create networks based on network pools in the vCloud Director. NSM exposes a set of APIs which enables vShield Manager to create a port profile on the Cisco Nexus 1000V.
The network administrator creates network segmentation policies that contain a tenant ID, backing type (Segmentation or VLAN), and a reference to port profiles that contain policies for features such as QoS, ACL, and so on. These network segmentation policies are inherited on a port profile as a result of a network that is created in the vCloud Director. For more information on network segmentation policies, see "Creating Network Segmentation Policies" section.
In the vCloud Director, the tenant ID determines how a network is assigned to a network segmentation policy. In a network segmentation policy, the policy type can be either VLAN or Segmentation. When vShield Manager issues requests to NSM to create networks, either a segmentation ID or VLAN is used depending on the policy type for the given tenant.
The vCloud Director creates the network from either a VLAN-backed or network isolation-backed network pool. The network pool type determines if a segmentation ID or VLAN is sent in the create network request to the NSM. Also, the network pool type that determines which type of network segmentation policy NSM uses
 Feedback
Feedback