Overview of Policies: Control Intercepted Internet Requests
When the user creates a web request the configured Web Security Appliance intercepts the requests and manages the process of which the request travels to get to its final outcome, be that accessing a particular web site, an email or even accessing an online application. In configuring the Web Security Appliance policies are created to define the criteria and actions of requests made by the user.
Policies are the means by which the Web Security Appliance identifies and controls web requests. When a client sends a web request to a server, the Web Proxy receives the request, evaluates it, and determines to which policy it belongs. Actions defined in the policy are then applied to the request.
The Web Security Appliance uses multiple policy types to manage different aspects of web requests. Policy types might fully manage transactions by themselves or pass transactions along to other policy types for additional processing. Policy types can be groups by the functions they perform, such as access, routing, or security.
AsyncOS evaluates transactions based on policies before it evaluates external dependencies to avoid unnecessary external communication from the appliance. For example, if a transaction is blocked based on a policy that blocks uncategorized URLs, the transaction will not fail based on a DNS error.
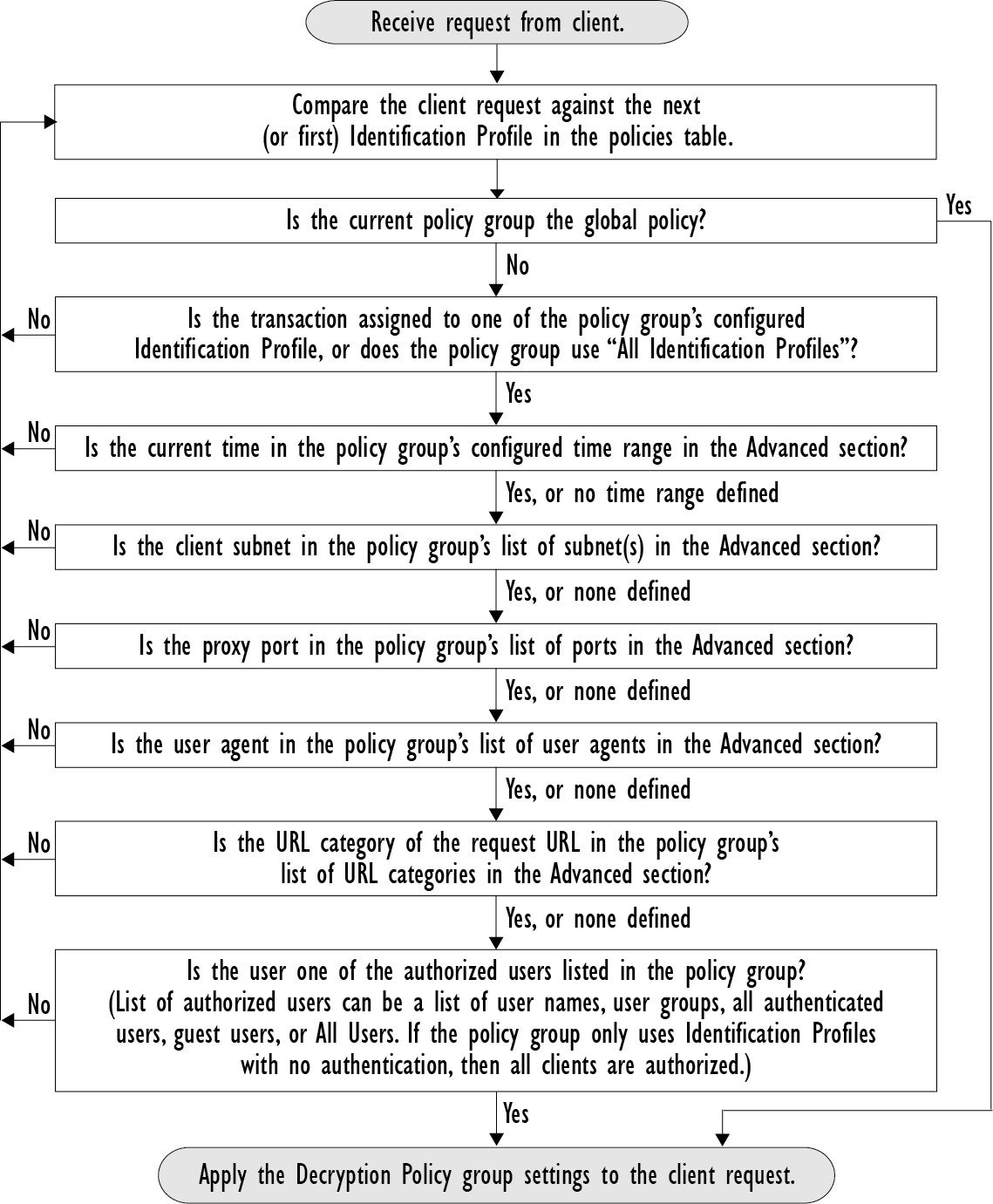
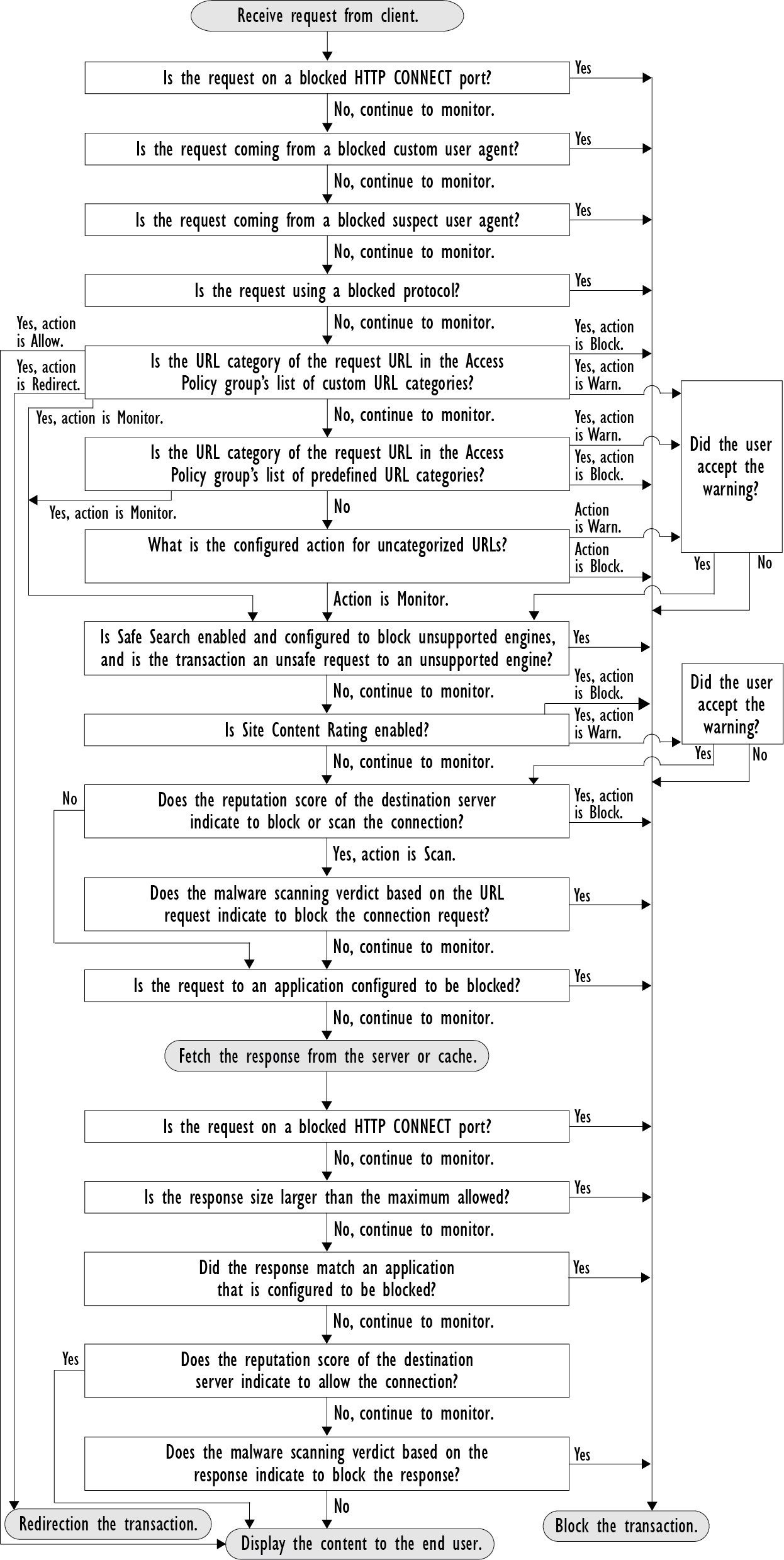
Intercepted HTTP/HTTPS Request Processing
The following diagram depicts the flow of an intercepted Web request as it is processed by the appliance.
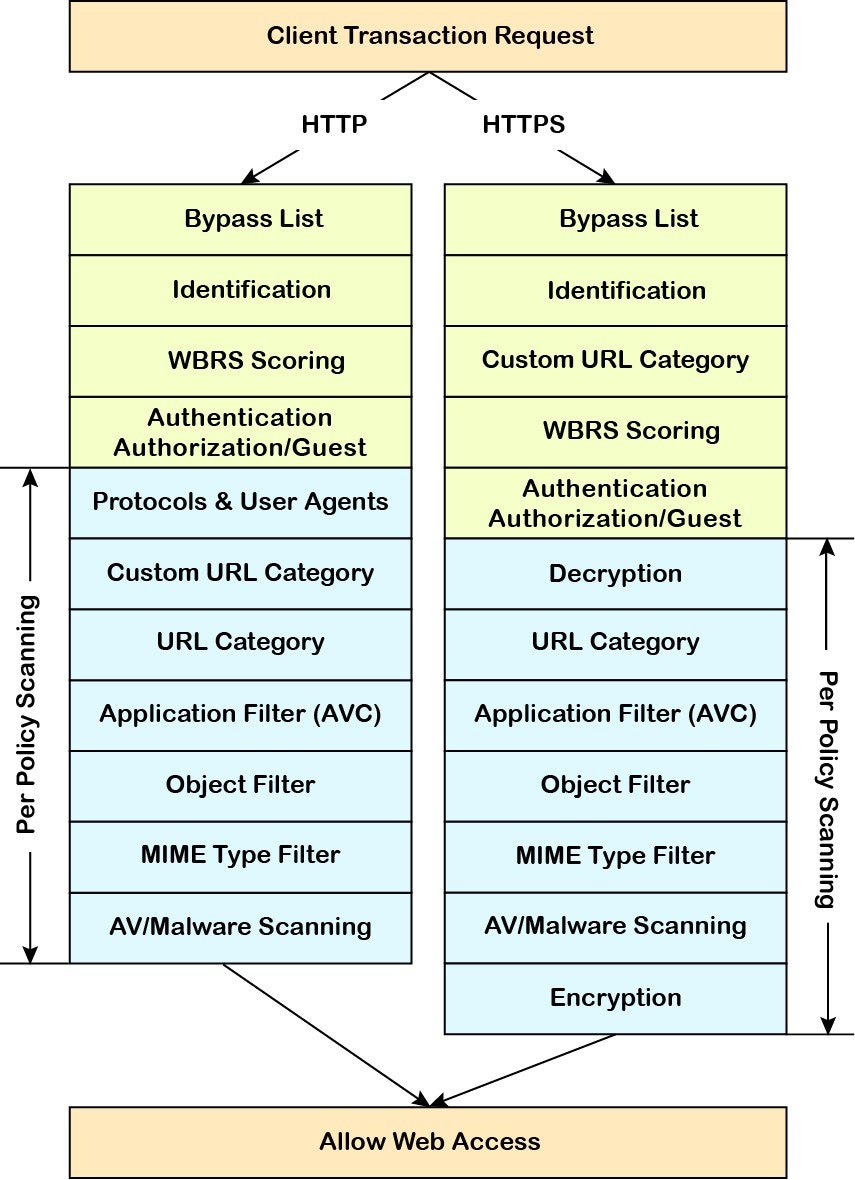
Also see the following diagrams depicting various transaction processing flows:

 Feedback
Feedback