Configure Network Exit
Geographic location is often an important issue for malware analysis. Some types of malware behave differently depending on geographic location, while other types may target a specific area. Similar in concept to VPN, the Network Exit setting makes any outgoing network that is generated during sample analysis appear to exit from that location.
The Network Exit setting is available in v2.4.3 or later, and replaces the tg-tunnel solution. Configuration files are automatically distributed and there is no need for suport staff to manually install or update them.
 Note |
If you were previously using tg-tunnel, you must allow outbound traffic to 4.14.36.142:21413 and 63.97.201.68:21413 before installing v2.4.3. Otherwise, that traffic only needs to be permitted before enabling remote exit use. |
Procedure
| Step 1 |
In the OpAdmin portal, click Configuration > Network Exit. 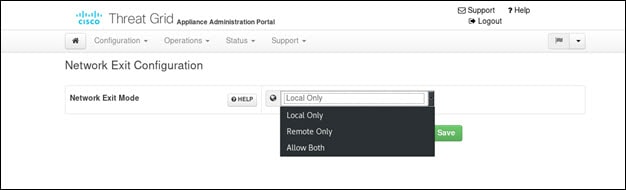
|
| Step 2 |
In the Network Exit Mode field, choose Local Only, Remote Only, or Allow Both. The selected option determines which Network Exit Localization options will be available in the application, such as when submitting samples in the UI. If you select Local Only or Remote Only, then the application will only make those options available to users. Accessing private networks, even for DNS lookup, is not allowed even for Network Exit Localization. All malware traffic comes out of the Dirty interface, using the Dirty DNS server configured. 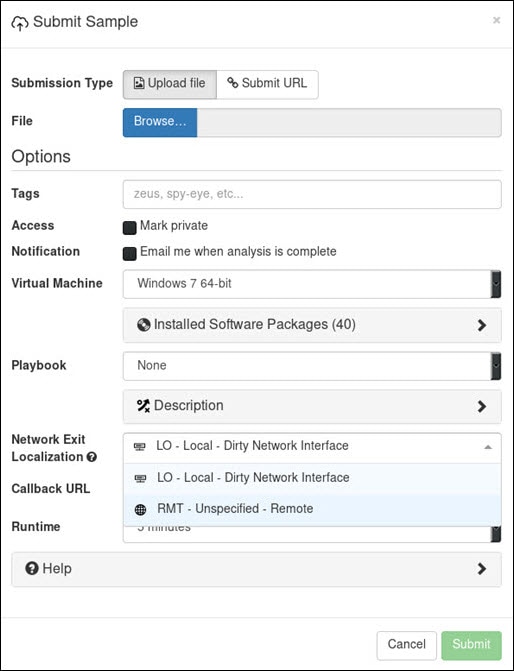
|
 Feedback
Feedback