Policy Sets
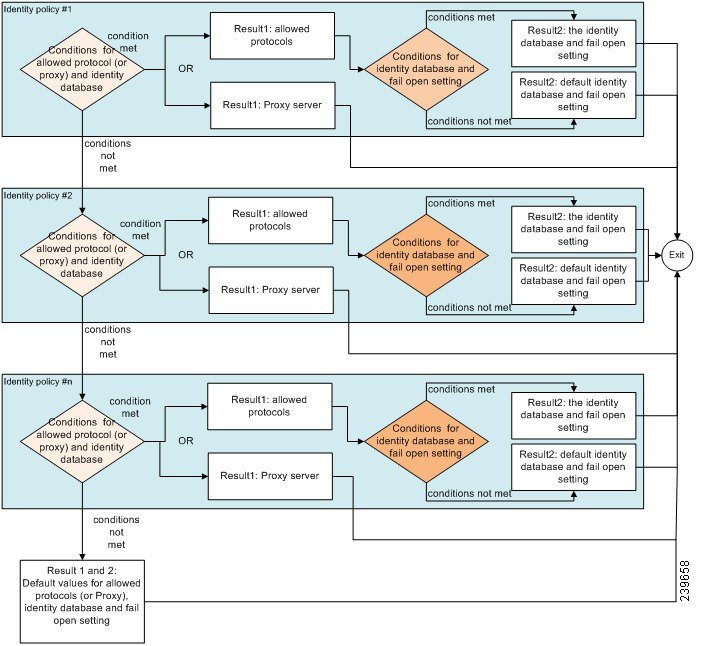
Cisco ISE is a policy-based, network-access-control solution, which offers network access policy sets, allowing you to manage several different network access use cases such as wireless, wired, guest, and client provisioning. Policy sets (both network access and device administration sets) enable you to logically group authentication and authorization policies within the same set. You can have several policy sets based on an area, such as policy sets based on location, access type, and similar parameters. When you install Cisco ISE, there is always one policy set defined, which is the default policy set, and the default policy set contains within it, predefined and default authentication, authorization and exception policy rules.
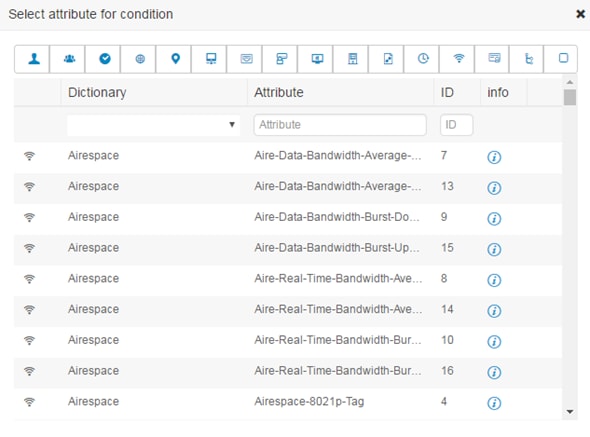
When creating policy sets, you can configure these rules (configured with conditions and results) in order to choose the network access services on the policy set level, the identity sources on the authentication policy level, and network permissions on the authorization policy levels. You can define one or more conditions using any of the attributes from the Cisco ISE-supported dictionaries for different vendors. Cisco ISE allows you to create conditions as individual resuable policy elements.
The network access service to be used per policy set to communicate with the network devices is defined at the top level of that policy set. Network access services include:
-
Allowed protocols—the protocols configured to handle the initial request and protocol negotiation.
-
A proxy service—sends requests to an external RADIUS server for processing.
 Note |
From the , you can also select a relevant TACACS server sequence for your policy set. Use the TACACS server sequence to configure a sequence of TACACS proxy servers for processing. |
Policy sets are configured hierarchically, where the rule on the top level of the policy set, which can be viewed from the Policy Set table, applies to the entire set and is matched before the rules for the rest of the policies and exceptions. Thereafter, rules of the set are applied in this order:
-
Authentication policy rules
-
Local policy exceptions
-
Global policy exceptions
-
Authorization policy rules
 Note |
Policy Sets functionality is identical for network access and for device administration policies. All processes described in this chapter can be applied when working with both the Network Access and the Device Administration work centers. This chapter specifically discusses the Network Access work center policy sets. Choose . |
|
For information about using RADIUS results from a WLC, see WLC Called-Station-ID (Radius Authentication and Accounting Config) . |
 from the Actions column to view and select different actions:
from the Actions column to view and select different actions:
 from the View column in the Policy Sets table, in order to access all of the policy set details and to create authentication
and authorization policies as well as policy exceptions.
from the View column in the Policy Sets table, in order to access all of the policy set details and to create authentication
and authorization policies as well as policy exceptions.
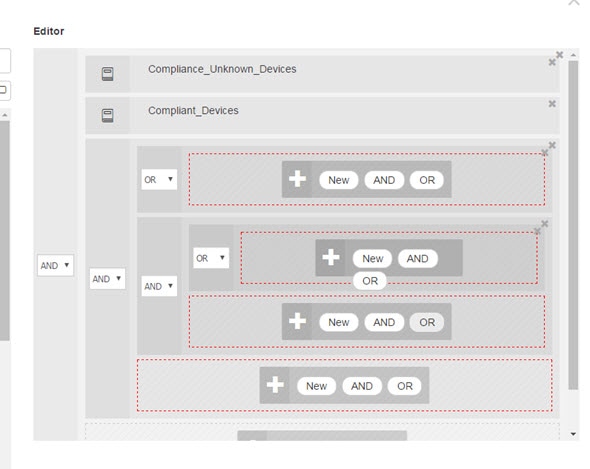
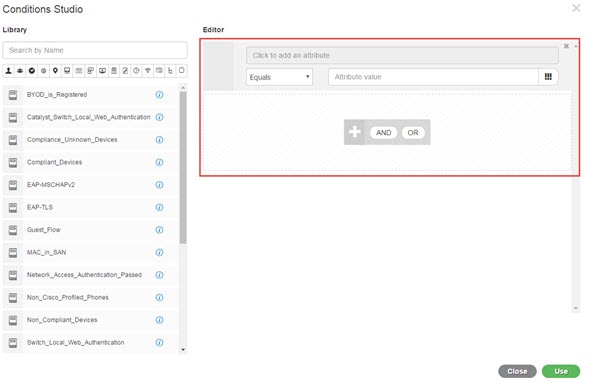
 . The Conditions Studio opens. For more information, see
. The Conditions Studio opens. For more information, see  , choose
, choose 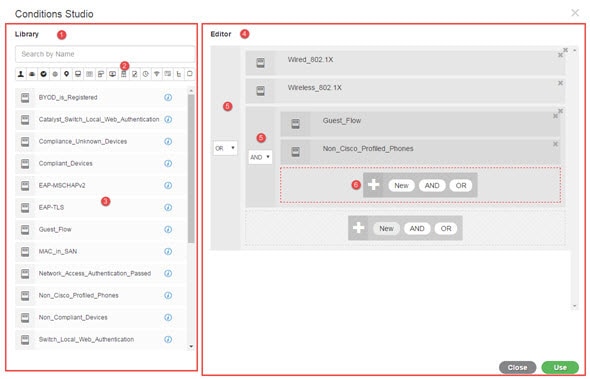
 , because conditions can be associated with more than one category.
, because conditions can be associated with more than one category.
 Feedback
Feedback