Email Security Monitor Overview
The Email Security Monitor feature collects data from every step in the email delivery process. The database identifies and records each email sender by IP address, while interfacing with the IP Reputation Service for real-time identity information. You can instantly report on any email sender’s local mail flow history and show a profile that includes the sender’s global record on the Internet. The Email Security Monitor feature allows your security team to “close the loop” on who is sending mail to your users, the amount of mail sent from and received by your users, and the effectiveness of your security policies.
This chapter explains how to:
- Access the Email Security Monitor feature to monitor inbound and outbound message flow.
- Make mail flow policy decisions (update allowed lists, blocked lists, and greylists) by querying for a sender’s IP Reputation Score. You can query on network owners, domains, and even individual IP addresses.
- Report on mail flow, system status, and mail sent to and from your network.
For any given email sender for incoming mail, the Email Security Monitor database captures critical parameters such as:
- Message volume
- Connection history
- Accepted vs. rejected connections
- Acceptance rates and throttle limits
- Sender reputation filter matches
- Number of anti-spam messages for suspected spam and positively identified spam
- Number of virus-positive message detected by anti-virus scanning
See Managing Spam and Graymail for more information on Anti-Spam scanning and Anti-Virus for more information on anti-virus scanning.
The Email Security Monitor feature also captures information on which content filter a particular message triggers, including the internal user (email recipient) to or from which the message was sent.
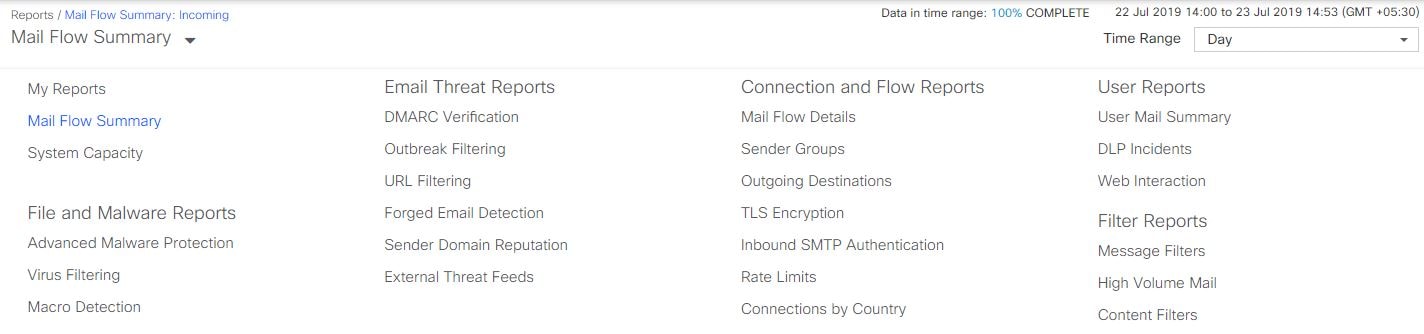
The Email Security Monitor feature is available in the GUI only, and provides a view into your email traffic and the status of your appliance (including quarantines, work queues, and outbreaks). The appliance identifies when a sender falls outside of the normal traffic profile. Senders that do are highlighted in the interface, allowing you to take corrective action by assigning that sender to a sender group or refining the access profile of the sender; or, you can let AsyncOS’s security services continue to react and respond. Outbound mail has a similar monitoring capability, providing you a view into the top domains in the mail queue and the status of receiving hosts (see Delivery Status Details Page).
 Note |
Information for messages present in the work queue when the appliance is rebooted is not reported by the Email Security Monitor feature. |
Related Topics
Email Security Monitor and Centralized Management
To view aggregated report data, deploy a Cisco Content Security Management appliance .
You cannot aggregate Email Security Monitor reports of clustered appliances. All reports are restricted to machine level. This means they cannot be run at the group or cluster levels — only on individual machines.
The same is true of the Archived Reports page — each machine in effect has its own archive. Thus, the “Generate Report” feature runs on the selected machine.
The Scheduled Reports page is not restricted to machine level; therefore, settings can be shared across multiple machines. Individual scheduled reports run at machine level just like interactive reports, so if you configure your scheduled reports at cluster level, every machine in the cluster will send its own report.
The “Preview This Report” button always runs against the login-host.

 in the top right corner of the required report module.
in the top right corner of the required report module.
 Feedback
Feedback