New Web Interface
During the Early Access phase, we refined our new web interface to bring it to you now as the main web interface of global threat alerts.
The new interface brings you:
Read more about it in a walk-through of the dashboard.
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
Updates released in September of 2022 to Cisco cloud-based machine learning global threat alerts:
During the Early Access phase, we refined our new web interface to bring it to you now as the main web interface of global threat alerts.
The new interface brings you:
Read more about it in a walk-through of the dashboard.
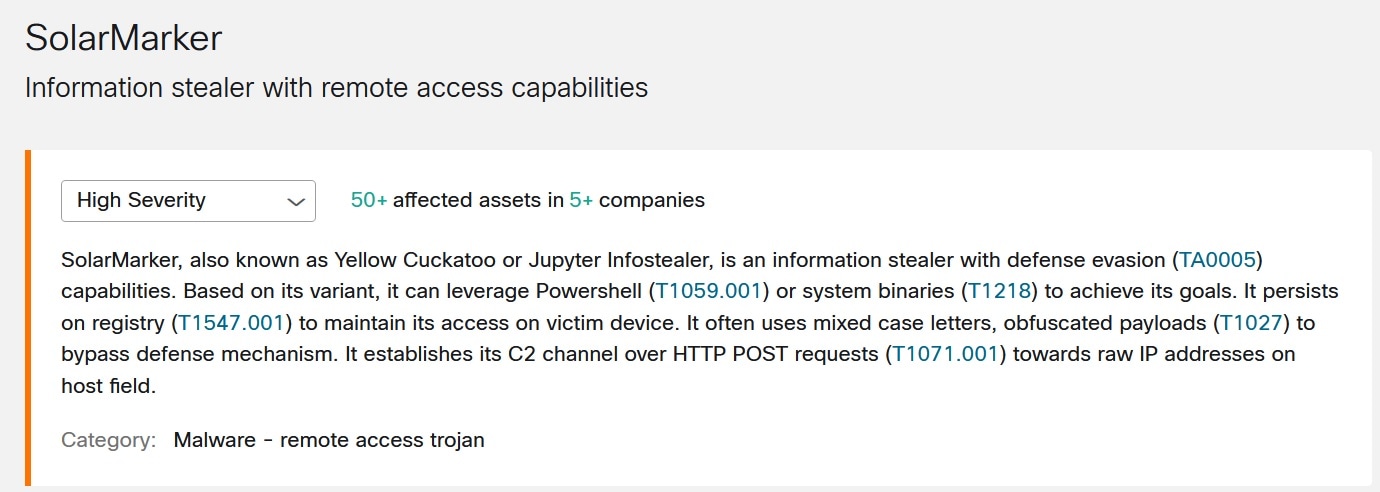
We've added a new threat detection, SolarMarker, to our portfolio. And we’ve updated indicators for our existing threat detections.
SolarMarker, also known as Yellow Cuckatoo or Jupyter Infostealer, is an information stealer capable of evading defenses (TA0005). Based on its variant, it can leverage Powershell (T1059.001) or system binaries (T1218) to achieve its goals. It persists in the registry (T1547.001) to maintain access to the victim's device. It often uses mixed-case letters and obfuscated payloads (T1027) to bypass defense mechanisms. It establishes its C2 channel over HTTP POST requests (T1071.001) towards raw IP addresses in the host field.
To see if SolarMarker has been detected in your environment, click SolarMarker Threat Detail to view its details in global threat alerts.