- Preface
- Overview
- Before Installing Broadband Access Center
- Installation of Broadband Access Center on Solaris
- Installation of Broadband Access Center on Linux
- Post-Installation Activities
- Setting Up a Device Provisioning Engine
- Network Registrar Configuration File Example
- Installation Worksheet
- Index
Installation and Setup Guide for Cisco Broadband Access Center 4.1
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- October 21, 2010
Chapter: Before Installing Broadband Access Center
Before Installing Cisco Broadband Access Center
This chapter explains how to prepare for a successful installation of Cisco Broadband Access Center (Cisco BAC) and describes:
•![]() Installation and Startup Process
Installation and Startup Process
Cisco BAC Components
The Cisco BAC component installation program prompts you to install:
•![]() Regional Distribution Unit (RDU)
Regional Distribution Unit (RDU)
The RDU is the primary server in the Cisco BAC provisioning system. You should install the RDU on a server that fulfills the requirements that are described in Chapter 1 "Overview."
The RDU:
–![]() Manages the generation of device configurations.
Manages the generation of device configurations.
–![]() Processes application programming interface (API) requests for all Cisco BAC functions.
Processes application programming interface (API) requests for all Cisco BAC functions.
–![]() Manages the Cisco BAC system.
Manages the Cisco BAC system.
When you install the RDU, the installation program also installs the administrator user interface. The program also preloads required data into the RDU database, and starts the RDU daemon through the Cisco BAC process watchdog. The SNMP agent is also installed for the RDU. For details on configuring the SNMP agent, see the Cisco Broadband Access Center DPE CLI Reference 4.1. For information on the Cisco BAC process watchdog, see the Cisco Broadband Access Center Administrator Guide 4.1.
•![]() Device Provisioning Engine (DPE)
Device Provisioning Engine (DPE)
The DPE is the major component of the provisioning group, handling all device interactions with the RDU. You should install a DPE on a server that meets the requirements described in Chapter 1 "Overview."
The DPE:
–![]() Caches device configurations generated at the RDU.
Caches device configurations generated at the RDU.
–![]() Manages various CPE protocol services. These services obtain their operating instructions from the instruction cache.
Manages various CPE protocol services. These services obtain their operating instructions from the instruction cache.
The installation program installs a CLI on your system to help configure the DPE. The Cisco BAC process watchdog and the SNMP agent are installed for the DPE also. For information on configuring the DPE and configuring the SNMP agent, see the Cisco Broadband Access Center DPE CLI Reference 4.1.

Note ![]() The DPE is separately licensed and must be installed from the administrator user interface. For details on licensing in this Cisco BAC release and how to install your license, see Licensing Cisco BAC.
The DPE is separately licensed and must be installed from the administrator user interface. For details on licensing in this Cisco BAC release and how to install your license, see Licensing Cisco BAC.
•![]() CNR extensions
CNR extensions
The CNR extensions are the link between Cisco BAC and CNR. You should install this component on all CNR servers in your Cisco BAC environment. If you are deploying Cisco BAC in a failover environment, ensure that you install the extensions on the failover servers also.

Note ![]() You must install the Cisco BAC CNR extensions on a server running Network Registrar 7.1.2.1. If you do not want to install these extensions, you are not required to install CNR.
You must install the Cisco BAC CNR extensions on a server running Network Registrar 7.1.2.1. If you do not want to install these extensions, you are not required to install CNR.
•![]() Key Distribution Center (KDC)
Key Distribution Center (KDC)
The KDC, along with the DPE registration service, handles the authentication of all PacketCable voice technology MTAs. For performance reasons, install the KDC on a separate server that meets the requirements described in Chapter 1 "Overview."
The KDC requires service keys, which allow it to communicate with the DPE. For details, see the Cisco Broadband Access Center DPE CLI Reference 4.1 and the Cisco Broadband Access Center Administrator Guide 4.1.

Note ![]() The KDC requires a license, which continues to be proprietary, as in previous Cisco BAC releases, and is licensed during Cisco BAC installation. For information on installing a KDC license, see Installing Your KDC License.
The KDC requires a license, which continues to be proprietary, as in previous Cisco BAC releases, and is licensed during Cisco BAC installation. For information on installing a KDC license, see Installing Your KDC License.
Installation and Startup Process
To ensure a smooth installation and startup process:
Step 1 ![]() Determine the computers and servers on which you are installing the Cisco BAC components.
Determine the computers and servers on which you are installing the Cisco BAC components.
Step 2 ![]() Verify the file-system block size of the directory in which you intend to install the Cisco BAC database and the database transaction log files. See Database Requirements.
Verify the file-system block size of the directory in which you intend to install the Cisco BAC database and the database transaction log files. See Database Requirements.
Step 3 ![]() Review the installation checklist described in Table 2-1.
Review the installation checklist described in Table 2-1.
Step 4 ![]() Install the RDU. Ensure that you know the location for the:
Install the RDU. Ensure that you know the location for the:
•![]() Home directory
Home directory
•![]() Data directory
Data directory
•![]() Database logs directory
Database logs directory
Step 5 ![]() Install a DPE. Ensure that you know the location for the:
Install a DPE. Ensure that you know the location for the:
•![]() Home directory
Home directory
•![]() Data directory
Data directory
•![]() Database logs directory
Database logs directory
Step 6 ![]() After installing the RDU, ensure that you:
After installing the RDU, ensure that you:
a. ![]() Obtain a valid Cisco BAC license file to provision all technologies. For details on obtaining and installing your license file, see Obtaining a Permanent License.
Obtain a valid Cisco BAC license file to provision all technologies. For details on obtaining and installing your license file, see Obtaining a Permanent License.
You still require separate licenses—permanent or evaluation—for the following Cisco BAC components:
–![]() The DPE
The DPE
–![]() The KDC, if you configure your network to support voice technology
The KDC, if you configure your network to support voice technology
b. ![]() Verify that the RDU is running by starting the administrator user interface.
Verify that the RDU is running by starting the administrator user interface.
To launch the administrator user interface, enter the administrator's location from your web browser using:
http://machine_name:port_number/

Note ![]() To access the administrator user interface using HTTP over SSL, enter: https://machine_name:port_number/
To access the administrator user interface using HTTP over SSL, enter: https://machine_name:port_number/
•![]() machine_name—Identifies the computer on which the RDU is running.
machine_name—Identifies the computer on which the RDU is running.
•![]() port_number—Identifies the computer port on which the server side of the administrator application is running. By default, this port number is:
port_number—Identifies the computer port on which the server side of the administrator application is running. By default, this port number is:
–![]() 8100 for HTTP over TCP
8100 for HTTP over TCP
–![]() 8443 for HTTP over SSL
8443 for HTTP over SSL
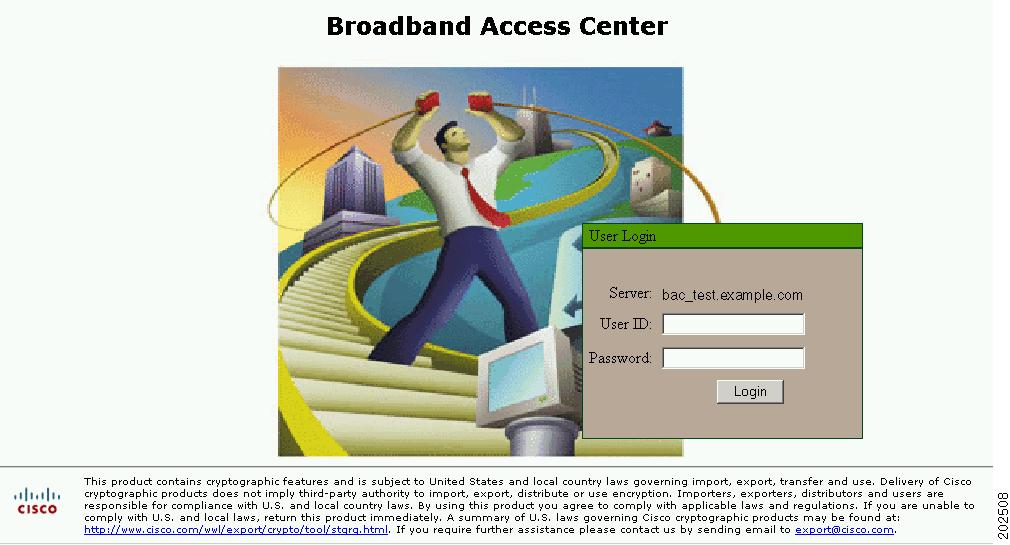
The main login screen, as shown in Figure 2-1, appears.
Figure 2-1 Login Screen
c. ![]() Change the Cisco BAC administrator's password.
Change the Cisco BAC administrator's password.
To change the password, enter the default username (admin) and password (changeme).
Click Login.
The Change Password screen appears.
Enter a new password; ensure that this password has at least 8 characters.
Click Login.
Step 7 ![]() Optionally, configure the syslog file for alerts. See Configuring the Syslog Utility to Receive Alerts from Cisco BAC. You can set up the syslog file on any Cisco BAC component server.
Optionally, configure the syslog file for alerts. See Configuring the Syslog Utility to Receive Alerts from Cisco BAC. You can set up the syslog file on any Cisco BAC component server.
Step 8 ![]() After installing the DPE, ensure that you:
After installing the DPE, ensure that you:
a. ![]() Change the DPE login password and the privileged password from the command-line interface (CLI).
Change the DPE login password and the privileged password from the command-line interface (CLI).
–![]() To change the login password, access the CLI in the privileged mode, and enter:
To change the login password, access the CLI in the privileged mode, and enter:
bac_dpe# password password
where password identifies the new DPE password.
–![]() To change the DPE privileged password, enter:
To change the DPE privileged password, enter:
bac_dpe# enable password password
where password identifies the local configured password currently in effect or, optionally, provides a new password. If this parameter is omitted, you are prompted for the password.
For more information, see the Cisco Broadband Access Center DPE CLI Reference 4.1.
b. ![]() Configure the DPE from the CLI as required. For configuration instructions, see the Cisco Broadband Access Center DPE CLI Reference 4.1.
Configure the DPE from the CLI as required. For configuration instructions, see the Cisco Broadband Access Center DPE CLI Reference 4.1.
Step 9 ![]() Install and configure CNR, if it is not already installed on your system. We recommend that you use CNR 7.1.2.1. For more information on installing CNR, see the Installation Guide for Cisco Network Registrar 7.1.
Install and configure CNR, if it is not already installed on your system. We recommend that you use CNR 7.1.2.1. For more information on installing CNR, see the Installation Guide for Cisco Network Registrar 7.1.
•![]() When you install the CNR Local Cluster (LCCM), ensure that you:
When you install the CNR Local Cluster (LCCM), ensure that you:
a. ![]() Obtain a valid CNR license file for the local cluster.
Obtain a valid CNR license file for the local cluster.
b. ![]() On all CNR local cluster servers, install Cisco BAC extensions. See
On all CNR local cluster servers, install Cisco BAC extensions. See
c. ![]() Configure CNR, including its extensions. Specifically, you need to configure scopes, policies, client classes, and selection tags. See
Configure CNR, including its extensions. Specifically, you need to configure scopes, policies, client classes, and selection tags. See
d. ![]() Configure the CNR syslog for alerts and debugging information. See Configuring the Syslog Utility to Receive Alerts from Cisco BAC.
Configure the CNR syslog for alerts and debugging information. See Configuring the Syslog Utility to Receive Alerts from Cisco BAC.
e. ![]() Validate the installation by connecting to the CNR web UI and viewing it.
Validate the installation by connecting to the CNR web UI and viewing it.
•![]() When you install CNR Regional Cluster (RCCM), ensure that you:
When you install CNR Regional Cluster (RCCM), ensure that you:
a. ![]() Identify the master server for CNR Regional Installation, which administers all the configured CNR local clusters. This server can be Solaris, Windows, or Linux. However, we recommend that you have the Solaris operating system on the CNR Regional Server.
Identify the master server for CNR Regional Installation, which administers all the configured CNR local clusters. This server can be Solaris, Windows, or Linux. However, we recommend that you have the Solaris operating system on the CNR Regional Server.
b. ![]() Obtain a valid central-cluster license file for the CNR Regional Server.
Obtain a valid central-cluster license file for the CNR Regional Server.
c. ![]() After you install the Cisco BAC extensions on all CNR local servers, replicate the local data into regional and pull the replica address space. For more information, see the User Guide for Cisco Network Registrar 7.1.
After you install the Cisco BAC extensions on all CNR local servers, replicate the local data into regional and pull the replica address space. For more information, see the User Guide for Cisco Network Registrar 7.1.
d. ![]() Alternatively, you can also create subnets, client classes, policies, and so on at RCCM and push them to the required LCCM DHCP server. For more information, see the User Guide for Cisco Network Registrar 7.1.
Alternatively, you can also create subnets, client classes, policies, and so on at RCCM and push them to the required LCCM DHCP server. For more information, see the User Guide for Cisco Network Registrar 7.1.
Step 10 ![]() Install and configure the KDC. When you install the KDC, ensure that you:
Install and configure the KDC. When you install the KDC, ensure that you:
•![]() Obtain a valid Cisco BAC license. The KDC license is proprietary and is licensed during Cisco BAC installation. For information on installing the KDC license, see Licensing Cisco BAC.
Obtain a valid Cisco BAC license. The KDC license is proprietary and is licensed during Cisco BAC installation. For information on installing the KDC license, see Licensing Cisco BAC.
•![]() Have the following information at hand:
Have the following information at hand:
–![]() KDC realm—Identified by a unique name, the KDC realm consists of a KDC and the clients and servers registered to that KDC.
KDC realm—Identified by a unique name, the KDC realm consists of a KDC and the clients and servers registered to that KDC.

Note ![]() The realm must match the certificate chain at the KDC.
The realm must match the certificate chain at the KDC.
–![]() KDC FQDN—Identifies the fully qualified domain name on which the KDC server is located.
KDC FQDN—Identifies the fully qualified domain name on which the KDC server is located.
–![]() KDC interface address—Identifies the interface (generally the IP address of the KDC server) on which the KDC listens for requests.
KDC interface address—Identifies the interface (generally the IP address of the KDC server) on which the KDC listens for requests.
Database Requirements
Before you install Cisco BAC, be aware of these database considerations:
•![]() File-system block size
File-system block size
•![]() Large file support
Large file support
File-System Block Size
For optimum performance and reliability of the Cisco BAC database, configure the file system or systems that contain the database files and database log files with an 8 KB or greater block size. If your system configuration does not support an 8-KB block size, then configure the block size in multiples of 8 KB; for example, 16 KB or 32 KB.

Note ![]() The block size cannot be changed once the Unix File System (UFS) is mounted with a value. The value has to be set during Solaris disk partition.
The block size cannot be changed once the Unix File System (UFS) is mounted with a value. The value has to be set during Solaris disk partition.
ZFS is a new file system in Solaris 10 OS which provides excellent data integrity and performance compared to other file systems. The benefit of using ZFS in a container is that the storage pool inside the container can then be given a particular amount of storage from the global storage pool and hence the global pool can be managed easily.
The steps required are:
•![]() Creating zone.
Creating zone.
•![]() Creating zpool, which is the actual storage pool.
Creating zpool, which is the actual storage pool.
•![]() Allocating a ZFS file system to the zone.
Allocating a ZFS file system to the zone.
In Cisco BAC, the RDU and DPE file system supports a blocksize of 8 KB to 64 KB. The DPE and RDU will restart if the block size configured is greater than 8 KB.
The installation program prompts you to specify a directory in which to install database files, and database transaction log files. These directories are identified in Cisco BAC with the system variables BPR_DATA, and BPR_DBLOG, respectively.
To verify that a directory resides on a file system with a minimum of 8-KB block size:
Step 1 ![]() Run the UNIX mount command without any parameters to determine on which file-system device the directory resides. The default directory is /var/CSCObac.
Run the UNIX mount command without any parameters to determine on which file-system device the directory resides. The default directory is /var/CSCObac.
For example:
# mount
/var on /dev/dsk/c0t0d0s4 read/write/setuid/intr/largefiles/logging/xattr/onerror=panic/ dev=2200004 on Thu Jun 15 16:58:21 2006
In this example, the file-system device is /dev/dsk/c0t0d0s4.
Step 2 ![]() To determine the file-system block size, use the df command.
To determine the file-system block size, use the df command.
For example:
# df -g /dev/dsk/c0t0d0s4
/var (/dev/dsk/c0t0d0s4): 8192 block size 1024 frag size
961240 total blocks 851210 free blocks 755086 available 243712 total files
239730 free files 35651588 filesys id
ufs fstype 0x00000004 flag 255 filename length
In this example, the block size is 8192 bytes, which is 8 KB. The block size of the selected directory, therefore, is correct.
Large File Support
Ensure that the file system in which you place database files is configured to support files larger than 2 GB. To verify large file support:
Step 1 ![]() Run the UNIX mount command without parameters.
Run the UNIX mount command without parameters.
Step 2 ![]() Note whether the intended file system contains the keyword largefiles.
Note whether the intended file system contains the keyword largefiles.
For example:
/var on /dev/dsk/c0t0d0s4 read/write/setuid/intr/largefiles/onerror=panic/dev=2200004 on Thu Jun 15 08:07:53
In this example, the output contains the keyword largefiles. This file system, therefore, can support files larger than 2 GB.
e. ![]()
 Feedback
Feedback