Security Configuration Guide: Unicast Reverse Path Forwarding Cisco IOS XE Release 3S
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- May 15, 2009
Chapter: Configuring Unicast Reverse Path Forwarding
- Finding Feature Information
- Contents
- Prerequisites for Unicast Reverse Path Forwarding
- Restrictions for Unicast Reverse Path Forwarding
- Information About Unicast Reverse Path Forwarding
Configuring Unicast Reverse Path Forwarding
This chapter describes the Unicast Reverse Path Forwarding (Unicast RPF) feature. The Unicast RPF feature helps to mitigate problems that are caused by malformed or forged IP source addresses that are passing through a router.
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest feature information and caveats, see the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the "Feature Information for Unicast Reverse Path Forwarding" section.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Contents
•![]() Prerequisites for Unicast Reverse Path Forwarding
Prerequisites for Unicast Reverse Path Forwarding
•![]() Restrictions for Unicast Reverse Path Forwarding
Restrictions for Unicast Reverse Path Forwarding
•![]() Information About Unicast Reverse Path Forwarding
Information About Unicast Reverse Path Forwarding
•![]() How to Configure Unicast Unicast Reverse Path Forwarding
How to Configure Unicast Unicast Reverse Path Forwarding
•![]() Configuration Examples for Unicast RPF
Configuration Examples for Unicast RPF
•![]() Feature Information for Unicast Reverse Path Forwarding
Feature Information for Unicast Reverse Path Forwarding
Prerequisites for Unicast Reverse Path Forwarding
Unicast RPF requires Cisco Express Forwarding to function properly on the router.
Prior to configuring Unicast RPF, configure ACLs:
•![]() Configure standard or extended ACLs to mitigate transmission of invalid IP addresses (perform egress filtering). Permit only valid source addresses to leave your network and get onto the Internet. Prevent all other source addresses from leaving your network for the Internet.
Configure standard or extended ACLs to mitigate transmission of invalid IP addresses (perform egress filtering). Permit only valid source addresses to leave your network and get onto the Internet. Prevent all other source addresses from leaving your network for the Internet.
•![]() Configure standard or extended ACLs entries to drop (deny) packets that have invalid source IP addresses (perform ingress filtering). Invalid source IP addresses include the following types:
Configure standard or extended ACLs entries to drop (deny) packets that have invalid source IP addresses (perform ingress filtering). Invalid source IP addresses include the following types:
–![]() Reserved addresses
Reserved addresses
–![]() Loopback addresses
Loopback addresses
–![]() Private addresses (RFC 1918, Address Allocation for Private Internets)
Private addresses (RFC 1918, Address Allocation for Private Internets)
–![]() Broadcast addresses (including multicast addresses)
Broadcast addresses (including multicast addresses)
–![]() Source addresses that fall outside the range of valid addresses associated with the protected network
Source addresses that fall outside the range of valid addresses associated with the protected network
•![]() Configure standard or extended ACL entries to forward (permit) packets that fail the Unicast RPF checks to allow specific traffic from known asymmetric routed sources.
Configure standard or extended ACL entries to forward (permit) packets that fail the Unicast RPF checks to allow specific traffic from known asymmetric routed sources.
Configure ACLs to track Unicast RPF events by adding the logging option into the ACL command. During network attacks, judicious logging of dropped or forwarded packets (suppressed drops) can provide additional information about network attacks.
Restrictions for Unicast Reverse Path Forwarding
There are some basic restrictions to applying Unicast RPF to multihomed clients:
•![]() Clients should not be multihomed to the same router because multihoming defeats the purpose of building a redundant service for the client.
Clients should not be multihomed to the same router because multihoming defeats the purpose of building a redundant service for the client.
•![]() Customers must ensure that the packets flowing up the link (out to the Internet) match the route advertised out the link. Otherwise, Unicast RPF filters those packets as malformed packets.
Customers must ensure that the packets flowing up the link (out to the Internet) match the route advertised out the link. Otherwise, Unicast RPF filters those packets as malformed packets.
•![]() Unicast RPF is available only for platform images that support Cisco Express Forwarding.
Unicast RPF is available only for platform images that support Cisco Express Forwarding.
Information About Unicast Reverse Path Forwarding
•![]() About Unicast Reverse Path Forwarding
About Unicast Reverse Path Forwarding
•![]() Unicast RPF Implementing Principles
Unicast RPF Implementing Principles
About Unicast Reverse Path Forwarding
The Unicast RPF feature helps to mitigate problems that are caused by the introduction of malformed or forged (spoofed) IP source addresses into a network by discarding IP packets that lack a verifiable IP source address. For example, a number of common types of denial-of-service (DoS) attacks, including Smurf and Tribal Flood Network (TFN), can take advantage of forged or rapidly changing source IP addresses to allow attackers to thwart efforts to locate or filter the attacks. For Internet service providers (ISPs) that provide public access, Unicast RPF deflects such attacks by forwarding only packets that have source addresses that are valid and consistent with the IP routing table. This action protects the network of the ISP, its customer, and the rest of the Internet.
How Unicast RPF Works
When Unicast RPF is enabled on an interface, the router examines all packets received as input on that interface to make sure that the source address and source interface appear in the routing table and match the interface on which the packet was received. This "look backwards" ability is available only when Cisco express forwarding is enabled on the router, because the lookup relies on the presence of the Forwarding Information Base (FIB). Cisco Express Forwarding generates the FIB as part of its operation.

Note ![]() Unicast RPF is an input function and is applied only on the input interface of a router at the upstream end of a connection.
Unicast RPF is an input function and is applied only on the input interface of a router at the upstream end of a connection.
Unicast RPF checks to see if any packet received at a router interface arrives on the best return path (return route) to the source of the packet. Unicast RPF does this by doing a reverse lookup in the Cisco Express Forwarding table. If the packet was received from one of the best reverse path routes, the packet is forwarded as normal. If there is no reverse path route on the same interface from which the packet was received, it might mean that the source address was modified. If Unicast RPF does not find a reverse path for the packet, the packet is dropped or forwarded, depending on whether an access control list (ACL) is specified in the ip verify unicast reverse-path interface configuration command.

Note ![]() With Unicast RPF, all equal-cost "best" return paths are considered valid. This means that Unicast RPF works in cases where multiple return paths exist, provided that each path is equal to the others in terms of the routing cost (number of hops, weights, and so on) and as long as the route is in the FIB. Unicast RPF also functions where EIGRP variants are being used and unequal candidate paths back to the source IP address exist.
With Unicast RPF, all equal-cost "best" return paths are considered valid. This means that Unicast RPF works in cases where multiple return paths exist, provided that each path is equal to the others in terms of the routing cost (number of hops, weights, and so on) and as long as the route is in the FIB. Unicast RPF also functions where EIGRP variants are being used and unequal candidate paths back to the source IP address exist.
When a packet is received at the interface where Unicast RPF and ACLs have been configured, the following actions occur:
Step 1 ![]() Input ACLs configured on the inbound interface are checked.
Input ACLs configured on the inbound interface are checked.
Step 2 ![]() Unicast RPF checks to see if the packet has arrived on the best return path to the source, which it does by doing a reverse lookup in the FIB table.
Unicast RPF checks to see if the packet has arrived on the best return path to the source, which it does by doing a reverse lookup in the FIB table.
Step 3 ![]() Cisco Express Forwarding table (FIB) lookup is carried out for packet forwarding.
Cisco Express Forwarding table (FIB) lookup is carried out for packet forwarding.
Step 4 ![]() Output ACLs are checked on the outbound interface.
Output ACLs are checked on the outbound interface.
Step 5 ![]() The packet is forwarded.
The packet is forwarded.
This section provides information about Unicast RPF enhancements:
•![]() Access Control Lists and Logging
Access Control Lists and Logging
Access Control Lists and Logging
If an ACL is specified in the command, then when (and only when) a packet fails the Unicast RPF check, the ACL is checked to see if the packet should be dropped (using a deny statement in the ACL) or forwarded (using a permit statement in the ACL). Whether a packet is dropped or forwarded, the packet is counted in the global IP traffic statistics for Unicast RPF drops and in the interface statistics for Unicast RPF.
If no ACL is specified in the Unicast RPF command, the router drops the forged or malformed packet immediately and no ACL logging occurs. The router and interface Unicast RPF counters are updated.
Unicast RPF events can be logged by specifying the logging option for the ACL entries used by the Unicast RPF command. Using the log information, administrators can see what source addresses are being used in the attack, the time the packets arrived at the interface, and so on.

Per-Interface Statistics
Each time a packet is dropped or forwarded at an interface, that information is counted two ways: globally on the router and at each interface where you have applied Unicast RPF. Global statistics on dropped packets provide information about potential attacks on the network; however, these global statistics do not help to specify which interface is the source of the attack.
Per-interface statistics allow network administrators to track two types of information about malformed packets: Unicast RPF drops and Unicast RPF suppressed drops. Statistics on the number of packets that Unicast RPF drops help to identify the interface that is the entry point of the attack. The Unicast RPF drop count tracks the number of drops at the interface. The Unicast RPF suppressed drop count tracks the number of packets that failed the Unicast RPF check but were forwarded because of the permit permission set up in the ACL. Using the drop count and suppressed drop count statistics, a network administrator can takes steps to isolate the attack at a specific interface.

Note ![]() Judicious use of ACL logging can further identify the address or addresses that are being dropped by Unicast RPF.
Judicious use of ACL logging can further identify the address or addresses that are being dropped by Unicast RPF.
Figure 1 illustrates how Unicast RPF and Cisco Express Forwarding work together to validate IP source addresses by verifying packet return paths. In this example, a customer has sent a packet having a source address of 192.168.1.1 from interface FDDI 2/0/0. Unicast RPF checks the FIB to see if 192.168.1.1 has a path to FDDI 2/0/0. If there is a matching path, the packet is forwarded. If there is no matching path, the packet is dropped.
Figure 1 Unicast RPF Validating IP Source Addresses
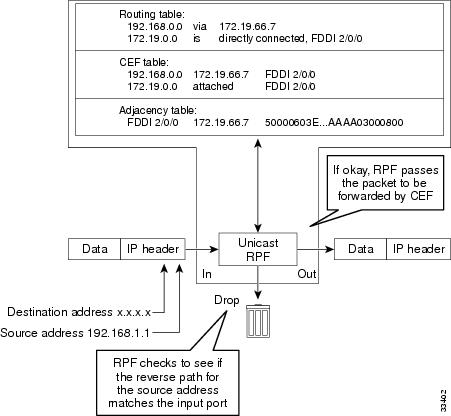
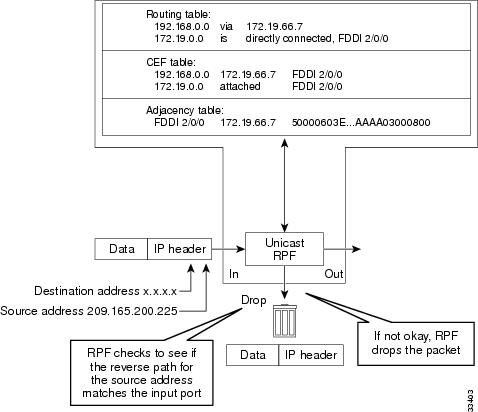
Figure 2 illustrates how Unicast RPF drops packets that fail validation. In this example, a customer has sent a packet having a source address of 209.165.200.225, which is received at interface FDDI 2/0/0. Unicast RPF checks the FIB to see if 209.165.200.225 has a return path to FDDI 2/0/0. If there is a matching path, the packet is forwarded. In this case, there is no reverse entry in the routing table that routes the customer packet back to source address 209.165.200.225 on interface FDDI 2/0/0, and so the packet is dropped.
Figure 2 Unicast RPF Dropping Packets That Fail Verification
Unicast RPF Implementing Principles
Unicast RPF has several key implementation principles:
•![]() The packet must be received at an interface that has the best return path (route) to the packet source (a process called symmetric routing). There must be a route in the FIB matching the route to the receiving interface. Adding a route in the FIB can be done via static route, network statement, or dynamic routing. (ACLs permit Unicast RPF to be used when packets are known to be arriving by specific, less optimal asymmetric input paths.)
The packet must be received at an interface that has the best return path (route) to the packet source (a process called symmetric routing). There must be a route in the FIB matching the route to the receiving interface. Adding a route in the FIB can be done via static route, network statement, or dynamic routing. (ACLs permit Unicast RPF to be used when packets are known to be arriving by specific, less optimal asymmetric input paths.)
•![]() IP source addresses at the receiving interface must match the routing entry for the interface.
IP source addresses at the receiving interface must match the routing entry for the interface.
•![]() Unicast RPF is an input function and is applied only on the input interface of a router at the upstream end of a connection.
Unicast RPF is an input function and is applied only on the input interface of a router at the upstream end of a connection.
Given these implementation principles, Unicast RPF becomes a tool that network administrators can use not only for their customers but also for their downstream network or ISP, even if the downstream network or ISP has other connections to the Internet.

This section provides information about the implementation of Unicast RPF:
•![]() Security Policy and Unicast RPF
Security Policy and Unicast RPF
•![]() Ingress and Egress Filtering Policy for Unicast RPF
Ingress and Egress Filtering Policy for Unicast RPF
•![]() Unicast RPF with BOOTP and DHCP
Unicast RPF with BOOTP and DHCP
Security Policy and Unicast RPF
Consider the following points in determining your policy for deploying Unicast RPF:
•![]() Unicast RPF must be applied at the interface downstream from the larger portion of the network, preferably at the edges of your network.
Unicast RPF must be applied at the interface downstream from the larger portion of the network, preferably at the edges of your network.
•![]() The further downstream you apply Unicast RPF, the finer the granularity you have in mitigating address spoofing and in identifying the sources of spoofed addresses. For example, applying Unicast RPF on an aggregation router helps mitigate attacks from many downstream networks or clients and is simple to administer, but it does not help identify the source of the attack. Applying Unicast RPF at the network access server helps limit the scope of the attack and trace the source of the attack; however, deploying Unicast RPF across many sites does add to the administration cost of operating the network.
The further downstream you apply Unicast RPF, the finer the granularity you have in mitigating address spoofing and in identifying the sources of spoofed addresses. For example, applying Unicast RPF on an aggregation router helps mitigate attacks from many downstream networks or clients and is simple to administer, but it does not help identify the source of the attack. Applying Unicast RPF at the network access server helps limit the scope of the attack and trace the source of the attack; however, deploying Unicast RPF across many sites does add to the administration cost of operating the network.
•![]() The more entities that deploy Unicast RPF across Internet, intranet, and extranet resources, the better the chances of mitigating large-scale network disruptions throughout the Internet community, and the better the chances of tracing the source of an attack.
The more entities that deploy Unicast RPF across Internet, intranet, and extranet resources, the better the chances of mitigating large-scale network disruptions throughout the Internet community, and the better the chances of tracing the source of an attack.
•![]() Unicast RPF will not inspect IP packets encapsulated in tunnels, such as GRE, LT2P, or PPTP. Unicast RPF must be configured at a home gateway so that Unicast RPF processes network traffic only after the tunneling and encryption layers have been stripped off the packets.
Unicast RPF will not inspect IP packets encapsulated in tunnels, such as GRE, LT2P, or PPTP. Unicast RPF must be configured at a home gateway so that Unicast RPF processes network traffic only after the tunneling and encryption layers have been stripped off the packets.
Ingress and Egress Filtering Policy for Unicast RPF
Unicast RPF can be more effective at mitigating spoofing attacks when combined with a policy of ingress and egress filtering using Cisco IOS XE access control lists (ACLs).
•![]() Ingress filtering applies filters to traffic received at a network interface from either internal or external networks. With ingress filtering, packets that arrive from other networks or the Internet and that have a source address that matches a local network, private, or broadcast address are dropped. In ISP environments, for example, ingress filtering can apply to traffic received at the router from either the client (customer) or the Internet.
Ingress filtering applies filters to traffic received at a network interface from either internal or external networks. With ingress filtering, packets that arrive from other networks or the Internet and that have a source address that matches a local network, private, or broadcast address are dropped. In ISP environments, for example, ingress filtering can apply to traffic received at the router from either the client (customer) or the Internet.
•![]() Egress filtering applies filters to traffic exiting a network interface (the sending interface). By filtering packets on routers that connect your network to the Internet or to other networks, you can permit only packets with valid source IP addresses to leave your network.
Egress filtering applies filters to traffic exiting a network interface (the sending interface). By filtering packets on routers that connect your network to the Internet or to other networks, you can permit only packets with valid source IP addresses to leave your network.
For more information on network filtering, refer to RFC 2267, Network Ingress Filtering: Defeating Denial of Service Attacks which employ IP Source Address Spoofing.
Where to Use Unicast RPF
Unicast RPF can be used in any "single-homed" environment where there is essentially only one access point out of the network; that is, one upstream connection. Networks having one access point offer the best example of symmetric routing, which means that the interface where a packet enters the network is also the best return path to the source of the IP packet. Unicast RPF is best used at the network perimeter for Internet, intranet, or extranet environments, or in ISP environments for customer network terminations.
The following sections provide a look at implementing Unicast RPF in two network environments:
•![]() Enterprise Networks with a Single Connection to an ISP
Enterprise Networks with a Single Connection to an ISP
•![]() Network Access Server Application (Applying Unicast RPF in PSTN/ISDN PoP Aggregation Routers)
Network Access Server Application (Applying Unicast RPF in PSTN/ISDN PoP Aggregation Routers)
Enterprise Networks with a Single Connection to an ISP
In enterprise networks, one objective of using Unicast RPF for filtering traffic at the input interface (a process called ingress filtering) is for protection from malformed packets arriving from the Internet. Traditionally, local networks that have one connection to the Internet would use ACLs at the receiving interface to prevent spoofed packets from the Internet from entering their local network.
ACLs work well for many single-homed customers; however, there are trade-offs when ACLs are used as ingress filters, including two commonly referenced limitations:
•![]() Packet per second (PPS) performance at very high packet rates
Packet per second (PPS) performance at very high packet rates
•![]() Maintenance of the ACL (whenever there are new addresses added to the network)
Maintenance of the ACL (whenever there are new addresses added to the network)
Unicast RPF is one tool that addresses both of these limitations. With Unicast RPF, ingress filtering is done at Cisco Express Forwarding PPS rates. This processing speed makes a difference when the link is more than 1 Mbps. Additionally, since Unicast RPF uses the FIB, no ACL maintenance is necessary, and thus the administration overhead of traditional ACLs is reduced. The following figure and example demonstrate how Unicast RPF is configured for ingress filtering.
Figure 3 illustrates an enterprise network that has a single link to an upstream ISP. In this example, Unicast RPF is applied at interface S0/1/0 on the enterprise router for protection from malformed packets arriving from the Internet. Unicast RPF is also applied at interface S2/0/0 on the ISP router for protection from malformed packets arriving from the enterprise network.
Figure 3 Enterprise Network Using Unicast RPF for Ingress Filtering
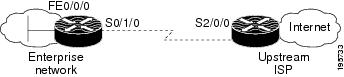
Using the topography in Figure 3, a typical configuration (assuming that Cisco Express Forwarding is turned on) on the ISP router would be as follows:
ip cef
interface loopback 0
description Loopback interface on Gateway Router 2
ip address 192.168.3.1 255.255.255.255
no ip redirects
no ip directed-broadcast
no ip proxy-arp
interface Serial 2/0/0
description 128K HDLC link to ExampleCorp WT50314E R5-0
bandwidth 128
ip unnumbered loopback 0
ip verify unicast reverse-path
no ip redirects
no ip directed-broadcast
no ip proxy-arp
ip route 192.168.10.0 255.255.252.0 Serial 2/0/0
The gateway router configuration of the enterprise network (assuming that Cisco Express Forwarding is turned on) would look similar to the following:
ip cef
interface FastEthernet 0/0/0
description ExampleCorp LAN
ip address 192.168.10.1 255.255.252.0
no ip redirects
no ip directed-broadcast
no ip proxy-arp
interface Serial 0/1/0
description 128K HDLC link to ExampleCorp Internet Inc WT50314E C0
bandwidth 128
ip unnumbered FastEthernet 0/0/0
ip verify unicast reverse-path
no ip redirects
no ip directed-broadcast
no ip proxy-arp
ip route 0.0.0.0 0.0.0.0 Serial 0/1/0
Notice that Unicast RPF works with a single default route. There are no additional routes or routing protocols. Network 192.168.10.0/22 is a connected network. Hence, packets coming from the Internet with a source address in the range 192.168.10.0/22 will be dropped by Unicast RPF.
Network Access Server Application (Applying Unicast RPF in PSTN/ISDN PoP Aggregation Routers)
Aggregation routers are ideal places to use Unicast RPF with single-homed clients. Unicast RPF works equally well on leased-line or PSTN/ISDN/xDSL customer connections into the Internet. In fact, dialup connections are reputed to be the greatest source of DoS attacks using forged IP addresses. As long as the network access server supports Cisco Express Forwarding, Unicast RPF will work. In this topology, the customer aggregation routers need not have the full Internet routing table. Aggregation routers need the routing prefixes information (IP address block); hence, information configured or redistributed in the Interior Gateway Protocol (IGP) or Internal Border Gateway Protocol (IBGP) (depending on the way that you add customer routes into your network) would be enough for Unicast RPF to do its job.
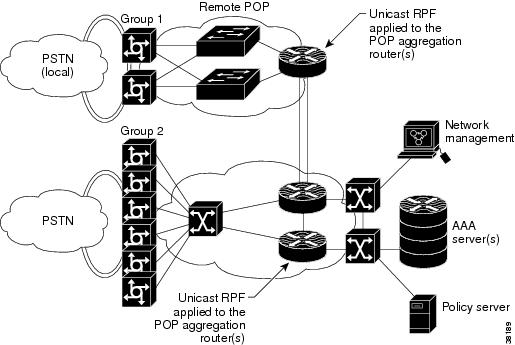
Figure 4 illustrates the application of Unicast RPF to the aggregation and access routers for an Internet service provider (ISP) point of presence (POP), with the ISP routers providing dialup customer connections. In this example, Unicast RPF is applied upstream from the customer dialup connection router on the receiving (input) interfaces of the ISP aggregation routers.
Figure 4 Unicast RPF Applied to PSTN/ISDN Customer Connections
Routing Table Requirements
To work correctly, Unicast RPF needs proper information in the Cisco Express Forwarding tables. This requirement does not mean that the router must have the entire Internet routing table. The amount of routing information needed in the Cisco Express Forwarding tables depends on where Unicast RPF is configured and what functions the router performs in the network. For example, in an ISP environment, a router that is a leased-line aggregation router for customers needs only the information based on the static routes redistributed into the IGP or IBGP (depending on which technique is used in the network). Unicast RPF would be configured on the customer interfaces—hence the requirement for minimal routing information. In another scenario, a single-homed ISP could place Unicast RPF on the gateway link to the Internet. The full Internet routing table would be required. Requiring the full routing table would help protect the ISP from external DoS attacks that use addresses that are not in the Internet routing table.
Where Not to Use Unicast RPF
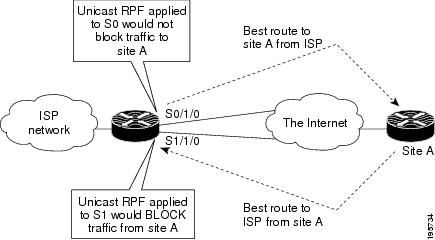
Unicast RPF should not be used on interfaces that are internal to the network. Internal interfaces are likely to have routing asymmetry (see Figure 5), meaning multiple routes to the source of a packet. Unicast RPF should be applied only where there is natural or configured symmetry. As long as administrators carefully plan which interfaces they activate Unicast RPF on, routing asymmetry is not a serious problem.
For example, routers at the edge of the network of an ISP are more likely to have symmetrical reverse paths than routers that are in the core of the ISP network. Routers that are in the core of the ISP network have no guarantee that the best forwarding path out of the router will be the path selected for packets returning to the router. Hence, it is not recommended that you apply Unicast RPF where there is a chance of asymmetric routing, unless you use ACLs to allow the router to accept incoming packets. ACLs permit Unicast RPF to be used when packets are known to be arriving by specific, less optimal asymmetric input paths. However, it is simplest to place Unicast RPF only at the edge of a network or, for an ISP, at the customer edge of the network.
Figure 5 illustrates how Unicast RPF can block legitimate traffic in an asymmetrical routing environment.
Figure 5 Unicast RPF Blocking Traffic in an Asymmetrical Routing Environment
Unicast RPF with BOOTP and DHCP
Unicast RPF will allow packets with 0.0.0.0 source and 255.255.255.255 destination to pass so that Bootstrap Protocol (BOOTP) and Dynamic Host Configuration Protocol (DHCP) functions work properly.
How to Configure Unicast Unicast Reverse Path Forwarding
•![]() Configuring Unicast RPF (required)
Configuring Unicast RPF (required)
•![]() Verifying Unicast RPF (optional)
Verifying Unicast RPF (optional)
•![]() Monitoring and Maintaining Unicast RPF (optional)
Monitoring and Maintaining Unicast RPF (optional)
Configuring Unicast RPF
To configure Unicast RPF, perform the following task.
Prerequisites for Configuring RPF
To use Unicast RPF, you must configure the router for Cisco Express Forwarding switching or Cisco Express Forwarding distributed switching. There is no need to configure the input interface for Cisco Express Forwarding switching because Unicast RPF has been implemented as a search through the FIB using the source IP address. As long as Cisco Express Forwarding is running on the router, individual interfaces can be configured with other switching modes. Unicast RPF is an input-side function that is enabled on an interface or subinterface that supports any type of encapsulation and operates on IP packets received by the router. It is very important that Cisco Express Forwarding be turned on globally in the router—Unicast RPF will not work without Cisco Express Forwarding.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() ip cef [distributed]
ip cef [distributed]
4. ![]() interface slot/subslot/port[.subinterface-number]
interface slot/subslot/port[.subinterface-number]
5. ![]() ip verify unicast reverse-path list
ip verify unicast reverse-path list
6. ![]() exit
exit
7. ![]() Repeat Steps 4 and 5 for each interface on which you want to apply Unicast RPF.
Repeat Steps 4 and 5 for each interface on which you want to apply Unicast RPF.
8. ![]() end
end
DETAILED STEPS
Verifying Unicast RPF
To verify that Unicast RPF is operational, use the show cef interface command. The following example shows that Unicast RPF is enabled at interface serial2/0/0.
Router# show cef interface serial 2/0/0
Serial2/0/0 is up (if_number 8)
Internet address is 192.168.10.2/30
ICMP redirects are never sent
Per packet loadbalancing is disabled
!The next line displays Unicast RPF packet dropping information.
IP unicast RPF check is enabled
Inbound access list is not set
Outbound access list is not set
Interface is marked as point to point interface
Packets switched to this interface on linecard are dropped to next slow path
Hardware idb is Serial2/0/0
Fast switching type 4, interface type 6
!The next line displays Unicast RPF packet dropping information.
IP Distributed CEF switching enabled
IP LES Feature Fast switching turbo vector
IP Feature CEF switching turbo vector
Input fast flags 0x40, Output fast flags 0x0, ifindex 7(7)
Slot 2 Slot unit 0 VC -1
Transmit limit accumulator 0x48001A02 (0x48001A02)
IP MTU 1500
Troubleshooting Tips
HSRP Failure
Failure to disable Unicast RPF before disabling Cisco Express Forwarding can cause Hot Standby Router Protocol (HSRP) failure. If you want to disable Cisco Express Forwarding on the router, you must first disable Unicast RPF. To disable Unicast RPF, see the section "Monitoring and Maintaining Unicast RPF."
Dropped Boot Requests
Unicast RPF can drop BOOTP request packets that have a source address of 0.0.0.0 due to source address verification at the interface. To enable boot requests to work on the interface, you must use ACLs instead of Unicast RPF.
Monitoring and Maintaining Unicast RPF
This section describes commands used to monitor and maintain Unicast RPF.

The show ip traffic command shows the total number (global count) of dropped or suppressed packets for all interfaces on the router. The Unicast RPF drop count is included in the IP statistics section. Unicast RPF counts the number of packets dropped or suppressed because of malformed or forged source addresses. Unicast RPF counts dropped or forwarded packets that include the following global and per-interface information:
•![]() Global Unicast RPF drops
Global Unicast RPF drops
•![]() Per-interface Unicast RPF drops
Per-interface Unicast RPF drops
•![]() Per-interface Unicast RPF suppressed drops
Per-interface Unicast RPF suppressed drops
Router# show ip traffic
IP statistics:
Rcvd: 1471590 total, 887368 local destination
0 format errors, 0 checksum errors, 301274 bad hop count
0 unknown protocol, 0 not a gateway
0 security failures, 0 bad options, 0 with options
Opts: 0 end, 0 nop, 0 basic security, 0 loose source route
0 timestamp, 0 extended security, 0 record route
0 stream ID, 0 strict source route, 0 alert, 0 other
Frags: 0 reassembled, 0 timeouts, 0 couldn't reassemble
0 fragmented, 0 couldn't fragment
Bcast: 205233 received, 0 sent
Mcast: 463292 received, 462118 sent
Sent: 990158 generated, 282938 forwarded
! The second line below ("0 unicast RPF") displays Unicast RPF packet dropping
information.
Drop: 3 encapsulation failed, 0 unresolved, 0 no adjacency
0 no route, 0 unicast RPF, 0 forced drop
The show ip interface command shows the total of dropped or suppressed packets at a specific interface. A nonzero value for the count of dropped or suppressed packets can mean one of two things:
•![]() Unicast RPF is dropping or suppressing packets that have a bad source address (normal operation).
Unicast RPF is dropping or suppressing packets that have a bad source address (normal operation).
•![]() Unicast RPF is dropping or suppressing legitimate packets because the route is misconfigured to use Unicast RPF in environments where asymmetric routing exists; that is, where multiple paths can exist as the best return path for a source address.
Unicast RPF is dropping or suppressing legitimate packets because the route is misconfigured to use Unicast RPF in environments where asymmetric routing exists; that is, where multiple paths can exist as the best return path for a source address.
If Unicast RPF is configured to use a specific ACL, that ACL information is displayed along with the drop statistics.
Router> show ip interface fastethernet0/1/1
Unicast RPF ACL 197
1 unicast RPF drop
1 unicast RPF suppressed drop
The show access-lists command displays the number of matches found for a specific entry in a specific access list.
Router> show access-lists
Extended IP access list 197
deny ip 192.168.201.0 0.0.0.63 any log-input (1 match)
permit ip 192.168.201.64 0.0.0.63 any log-input (1 match)
deny ip 192.168.201.128 0.0.0.63 any log-input
permit ip 192.168.201.192 0.0.0.63 any log-input
Configuration Examples for Unicast RPF
•![]() Example: Unicast RPF with Inbound and Outbound Filters
Example: Unicast RPF with Inbound and Outbound Filters
•![]() Example: Unicast RPF with ACLs and Logging
Example: Unicast RPF with ACLs and Logging
Example: Unicast RPF with Inbound and Outbound Filters
The following example uses a very simple single-homed ISP to demonstrate the concepts of ingress and egress filters used in conjunction with Unicast RPF. The example illustrates an ISP-allocated classless interdomain routing (CIDR) block 209.165.202.128/28 that has both inbound and outbound filters on the upstream interface. Be aware that ISPs are usually not single-homed. Hence, provisions for asymmetrical flows (when outbound traffic goes out one link and returns via a different link) need to be designed into the filters on the border routers of the ISP.
ip cef distributed
!
interface Serial 5/0/0
description Connection to Upstream ISP
ip address 209.165.200.225 255.255.255.252
no ip redirects
no ip directed-broadcast
no ip proxy-arp
ip verify unicast reverse-path
ip access-group 111 in
ip access-group 110 out
!
access-list 110 permit ip 209.165.202.128 0.0.0.31 any
access-list 110 deny ip any any log
access-list 111 deny ip host 0.0.0.0 any log
access-list 111 deny ip 127.0.0.0 0.255.255.255 any log
access-list 111 deny ip 10.0.0.0 0.255.255.255 any log
access-list 111 deny ip 172.16.0.0 0.15.255.255 any log
access-list 111 deny ip 192.168.0.0 0.0.255.255 any log
access-list 111 deny ip 209.165.202.128 0.0.0.31 any log
access-list 111 permit ip any any
Example: Unicast RPF with ACLs and Logging
The following example demonstrates the use of ACLs and logging with Unicast RPF. In this example, extended ACL 197 provides entries that deny or permit network traffic for specific address ranges. Unicast RPF is configured on interface FastEthernet0/1/1 to check packets arriving at that interface.
For example, packets with a source address of 192.168.201.10 arriving at interface FastEthernet0/1/1 are dropped because of the deny statement in ACL 197. In this case, the ACL information is logged (the logging option is turned on for the ACL entry) and dropped packets are counted per interface and globally. Packets with a source address of 192.168.201.100 arriving at interface FastEthernet0 /1/2 are forwarded because of the permit statement in ACL 197. ACL information about dropped or suppressed packets is logged (logging option turned on for the ACL entry) to the log server.
ip cef distributed
!
int fasteth0/1/1
ip address 192.168.200.1 255.255.255.0
ip verify unicast reverse-path 197
!
int fasteth0/1/2
ip address 192.168.201.1 255.255.255.0
!
access-list 197 deny ip 192.168.201.0 0.0.0.63 any log-input
access-list 197 permit ip 192.168.201.64 0.0.0.63 any log-input
access-list 197 deny ip 192.168.201.128 0.0.0.63 any log-input
access-list 197 permit ip 192.168.201.192 0.0.0.63 any log-input
access-list 197 deny ip host 0.0.0.0 any log
Additional References
Related Documents
|
|
|
|---|---|
Cisco IOS commands |
|
Unicast RPF command descriptions |
|
Cisco Express Forwarding concepts and tasks |
Standards
|
|
|
|---|---|
None |
— |
RFCs
|
|
|
|---|---|
RFC 1918 |
Address Allocation for Private Internets |
RFC 2267 |
Network Ingress Filtering: Defeating Denial of Service Attacks which employ IP Source Address Spoofing |
Technical Assistance
Feature Information for Unicast Reverse Path Forwarding
Table 1 lists the features in this module and provides links to specific configuration information.
Use Cisco Feature Navigator to find information about platform support and software image support. Cisco Feature Navigator enables you to determine which software images support a specific software release, feature set, or platform. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.

Note ![]() Table 1 lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Table 1 lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
|
|
|
|
|---|---|---|
Unicast Reverse Path Forwarding |
Cisco IOS XE Release 2.1 |
Unicast RPF helps to mitigate problems that are caused by malformed or forged IP source addresses that are passing through a router. The following sections provide information about this feature: • • No commands were introduced or modified for this feature. |
 Feedback
Feedback