PPPoE Session Limit Per NAS Port
Available Languages
Table Of Contents
PPPoE Session Limit per NAS Port
Prerequisites for PPPoE Session Limit per NAS Port
Restrictions for PPPoE Session Limit per NAS Port
Information About PPPoE Session Limit per NAS Port
How PPPoE per-NAS-Port Session Limits Work
Relationship Between the per-NAS-Port Session Limit and Other Types of Session Limits
Benefits of PPPoE Session Limits per NAS Port
How to Configure PPPoE Session Limits per NAS Port
Enabling Subscriber Service Switch Preauthorization
Configuring the RADIUS User Profile for PPPoE Session Limit per NAS Port
Verifying PPPoE Session Limit per NAS Port
Configuration Examples for PPPoE Session Limit per NAS Port
Configuring the LAC for per-NAS-Port Session Limits for PPPoE over ATM: Example
Configuring the LAC for per-NAS-Port Session Limits for PPPoE over VLAN: Example
Configuring the User Profile for PPPoE Session Limit per NAS Port: Example
PPPoE Session Limit per NAS Port
First Published: March 17, 2003Last Updated: February 28, 2006The PPPoE Session Limit per NAS Port feature enables you to limit the number of PPP over Ethernet (PPPoE) sessions on a specific permanent virtual circuit (PVC) or VLAN configured on an L2TP access concentrator (LAC). The network access server (NAS) port is either an ATM PVC or a configured VLAN ID. PPPoE per-NAS-port session limits are maintained in a RADIUS server customer profile database and are downloaded during Subscriber Service Switch (SSS) preauthorization.
History for the PPPoE Session Limit per NAS Port Feature
Finding Support Information for Platforms and Cisco IOS Software Images
Use Cisco Feature Navigator to find information about platform support and Cisco IOS software image support. Access Cisco Feature Navigator at http://www.cisco.com/go/fn. You must have an account on Cisco.com. If you do not have an account or have forgotten your username or password, click Cancel at the login dialog box and follow the instructions that appear.
Contents
•
Prerequisites for PPPoE Session Limit per NAS Port
•
Restrictions for PPPoE Session Limit per NAS Port
•
Information About PPPoE Session Limit per NAS Port
•
How to Configure PPPoE Session Limits per NAS Port
•
Configuration Examples for PPPoE Session Limit per NAS Port
Prerequisites for PPPoE Session Limit per NAS Port
Both the LAC and the L2TP Network Server (LNS) must be running a Cisco IOS image that supports the PPPoE Session Limit Per NAS Port feature.
Restrictions for PPPoE Session Limit per NAS Port
•
Do not configure the PPPoE per-NAS-port session limit to zero.
•
PPPoE Session Limit per NAS Port does not support TACACS+.
•
PPPoE Session Limit per NAS Port applies only to PVCs and VLANs.
Information About PPPoE Session Limit per NAS Port
To configure per-NAS-port session limits for PPPoE, you should understand the following concepts:
•
How PPPoE per-NAS-Port Session Limits Work
•
Relationship Between the per-NAS-Port Session Limit and Other Types of Session Limits
•
Benefits of PPPoE Session Limits per NAS Port
How PPPoE per-NAS-Port Session Limits Work
The PPPoE Session Limit per NAS Port feature limits the number of PPPoE sessions on a specific PVC or VLAN configured on an LAC. The NAS port is either an ATM PVC or a configured VLAN ID.
The PPPoE per-NAS-port session limit is maintained in a RADIUS server customer profile database. This customer profile database is connected to a LAC and is separate from the RADIUS server that the LAC and LNS use for the authentication and authorization of incoming users. See Figure 1 for a sample network topology. When the customer profile database receives a preauthorization request from the LAC, it sends the PPPoE per-NAS-port session limit to the LAC.
The LAC sends a preauthorization request to the customer profile database when the LAC is configured for SSS preauthorization. When the LAC receives the PPPoE per-NAS-port session limit from the customer profile database, the LAC compares the PPPoE per-NAS-port session limit with the number of sessions currently on the NAS port. The LAC then decides whether to accept or reject the current call, depending upon the configured PPPoE per NAS port-session-limit and the number of calls currently on the NAS port.
Figure 1 PPPoE Session Limit per NAS Port Sample Topology
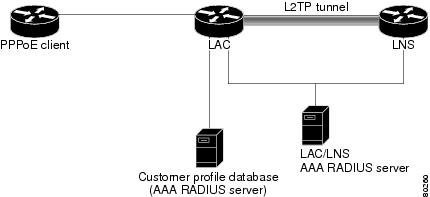
The customer profile database consists of user profiles for each user that is connected to the LAC. Each user profile contains the NAS-IP-Address (attribute 4) and the NAS-Port-ID (attribute 5.) When the LAC is configured for SSS preauthorization, it queries the customer profile database using the username. When a match is found in the customer profile database, the customer profile database sends the PPPoE per-NAS-port session limit in the user profile. The PPPoE per-NAS-port session limit is defined in the username as a Cisco AV-pair.
Relationship Between the per-NAS-Port Session Limit and Other Types of Session Limits
You can configure other types of session limits on the LAC, including session limit per VC, per VLAN, per MAC, and a global session limit for the LAC. When PPPoE Session Limit per NAS Port is enabled (that is, when you have enabled SSS preauthorization on the LAC), local configurations for session limit per VC and per VLAN are overwritten by the PPPoE per-NAS-port session limit downloaded from the customer profile database. Configured session limits per VC and per VLAN serve as backups in case of a download failure of the PPPoE per-NAS-port session limit. Global session limits and per-MAC session limits, if configured on the router, will take effect as other means of limiting PPPoE sessions.
Benefits of PPPoE Session Limits per NAS Port
The PPPoE Session Limit Per NAS Port feature provides flexibility and simplifies router configuration by allowing you to download the per-VC and per-VLAN session limits from a RADIUS server in addition to being able to configure them on the router.
How to Configure PPPoE Session Limits per NAS Port
This section contains the following procedures:
•
Enabling Subscriber Service Switch Preauthorization
•
Configuring the RADIUS User Profile for PPPoE Session Limit per NAS Port
•
Verifying PPPoE Session Limit per NAS Port
Enabling Subscriber Service Switch Preauthorization
When Subscriber Service Switch preauthorization is enabled on a LAC, local configurations for session limit per VC and per VLAN are overwritten by the per-NAS-port session limit downloaded from the server. To enable this preauthorization, perform the following steps:
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
subscriber access pppoe pre-authorize nas-port-id [aaa-method-list]
4.
exit
DETAILED STEPS
Configuring the RADIUS User Profile for PPPoE Session Limit per NAS Port
Table 1 lists the attributes to enable per-NAS-port PPPoE session limits in a RADIUS user profile for the customer profile database. Refer to the Cisco IOS Security Configuration Guide, for information about creating a RADIUS user profile.
Verifying PPPoE Session Limit per NAS Port
Perform this task to verify per-NAS-port session limit performance.
SUMMARY STEPS
1.
enable
2.
debug aaa authorization
3.
debug radius [brief | hex]
DETAILED STEPS
Configuration Examples for PPPoE Session Limit per NAS Port
•
Configuring the LAC for per-NAS-Port Session Limits for PPPoE over ATM: Example
•
Configuring the LAC for per-NAS-Port Session Limits for PPPoE over VLAN: Example
•
Configuring the User Profile for PPPoE Session Limit per NAS Port: Example
Configuring the LAC for per-NAS-Port Session Limits for PPPoE over ATM: Example
The following example shows how to configure per-NAS-port session limits for PPPoE over ATM on the LAC:
!username lac password 0 labusername lns password 0 labaaa new-model!aaa authentication ppp default group radius localaaa authentication ppp mlist_nasport group radiusaaa authorization network mlist_nasport group radiusaaa session-id commonip subnet-zero!no ip domain lookupip host abrick 192.168.2.0!ip cefsubscriber access pppoe pre-authorize nas-port-id mlist_nasportvpdn enable!vpdn-group l2tp_initiatorrequest-dialinprotocol l2tpdomain domain1.cominitiate-to ip 10.1.1.2local name lac!vpdn-group pppoe_terminateaccept-dialinprotocol pppoevirtual-template 1pppoe limit per-mac 10pppoe limit per-vc 10pppoe limit per-vlan 10!vc-class atm pppoeprotocol pppoeubr 155000encapsulation aal5snap!interface ATM2/0no ip addressno ip mroute-cacheno atm ilmi-keepalive!interface ATM2/0.1 point-to-pointclass-int pppoepvc 1/100encapsulation aal5snap!!interface FastEthernet4/0ip address 10.1.1.1 255.255.255.0no ip mroute-cacheduplex full!interface FastEthernet6/0ip address 192.168.1.0 255.255.255.0no ip mroute-cacheduplex full!interface Virtual-Template1ip unnumbered Loopback0no peer default ip addressppp authentication chap mlist_nasport!ip default-gateway 10.3.0.1ip classlessip route 10.0.0.0 10.0.0.0 10.3.0.1!!ip radius source-interface FastEthernet6/0!radius-server host 192.168.1.2 auth-port 1645 acct-port 1646radius-server key ciscoradius-server authorization permit missing Service-Type!Configuring the LAC for per-NAS-Port Session Limits for PPPoE over VLAN: Example
The following example shows how to configure per-NAS-port session limits for PPPoE over VLAN on the LAC:
!username lac password 0 labusername lns password 0 labaaa new-model!!aaa authentication ppp default group radius localaaa authentication ppp mlist_nasport group radiusaaa authorization network mlist_nasport group radiusaaa session-id commonip subnet-zero!!no ip domain lookupip host abrick 192.168.2.223!ip cefsubscriber access pppoe pre-authorize nas-port-id mlist_nasportvpdn enable!vpdn-group l2tp_initiatorrequest-dialinprotocol l2tpdomain nasport.cominitiate-to ip 10.1.1.2local name lac!vpdn-group pppoe_terminateaccept-dialinprotocol pppoevirtual-template 1pppoe limit per-mac 10pppoe limit per-vc 10pppoe limit per-vlan 10!vc-class atm pppoeprotocol pppoeubr 155000encapsulation aal5snap!interface ATM2/0no ip addressno ip mroute-cacheshutdownno atm ilmi-keepalive!interface FastEthernet4/0ip address 10.1.1.1 255.255.255.0no ip mroute-cacheduplex full!interface FastEthernet6/0ip address 192.168.20.3 255.255.255.0no ip mroute-cacheduplex full!interface Virtual-Template1ip unnumbered Loopback0no peer default ip addressppp authentication chap mlist_nasport!ip default-gateway 10.3.0.1ip classlessip route 10.0.0.0 10.0.0.0 10.3.0.1!!ip radius source-interface FastEthernet6/0!!!radius-server host 10.1.1.2 auth-port 1645 acct-port 1646radius-server key ciscoradius-server authorization permit missing Service-Type!Configuring the User Profile for PPPoE Session Limit per NAS Port: Example
The following example shows how to configure the user profile for PPPoE Session Limit per NAS port. In this example, the user has a PVC with a VPI of 1 and a VCI of 100 on ATM interface 4/0/0 of the LAC with an IP address of 10.10.10.10:
Username=nas_port:10.10.10.10:4/0/0/1.100Password = "password1"cisco-avpair= "pppoe:session-limit=<session limit per NAS-port>"Additional References
The following sections provide references related to the Cisco IOS Release: Multiple releases (see the Feature History table) feature.
Related Documents
ATM PVC configuration
"ATM" chapter in the Cisco IOS Wide-Area Networking Configuration Guide
PPPoE and PPPoE over 802.1Q VLAN configuration
"Broadband Access: PPP and Routed Bridge Encapsulation" chapter in the Cisco IOS Wide-Area Networking Configuration Guide, Release 12.2
ATM and PPPoE configuration commands
Cisco IOS Wide-Area Networking Command Reference, Cisco IOS Release 12.3(4)T
Standards
MIBs
None
To locate and download MIBs for selected platforms, Cisco IOS releases, and feature sets, use Cisco MIB Locator found at the following URL:
RFCs
Technical Assistance
Command Reference
This section documents a modified command only.
subscriber access
To configure a network access server (NAS) to enable Subscriber Service Switch (SSS) to preauthorize the NAS port identifier (NAS-Port-ID) string before authorizing the domain name, use the subscriber access command in global configuration mode. To disable SSS preauthorization, use the no form of this command.
subscriber access {pppoe | pppoa} pre-authorize nas-port-id [default | list-name] [send username]
no subscriber access {pppoe | pppoa} pre-authorize nas-port-id
Syntax Description
Defaults
Preauthorization is disabled.
Command Modes
Global configuration
Command History
Usage Guidelines
The NAS-Port-ID string is used to locate the first service record, which may contain one of three attributes, as follows:
•
A restricted set of values for the domain substring of the unauthenticated PPP name.
This filtered service key then locates the final service. See the vpdn authorize domain command for more information.
•
PPPoE session limit.
•
The logical line ID (LLID).
Once NAS port authorization has taken place, normal authorization, which is usually the domain authorization, continues.
Logical Line ID
The LLID is an alphanumeric string of 1 to 253 characters that serves as the logical identification of a subscriber line. The LLID is maintained in a RADIUS server customer profile database and enables users to track their customers on the basis of the physical lines on which customer calls originate. Downloading the LLID is also referred to as "preauthorization" because it occurs before normal virtual private dialup network (VPDN) authorization downloads layer two tunnel protocol (L2TP) information.
This command enables LLID and SSS querying only for PPP over Ethernet over ATM (PPPoEoATM) and PPP over Ethernet over VLAN (PPPoEoVLAN or Dot1Q) calls; all other calls, such as ISDN, are not supported.
Per-NAS-Port Session Limits for PPPoE
Use this command to configure SSS preauthorization on the L2TP Access Concentrator (LAC) so that the PPPoE per-NAS-port session limit can be downloaded from the customer profile database. To use PPPoE per-NAS-port session limits, you must also configure the PPPoE Session-Limit per NAS-Port Cisco attribute-value pair in the user profile.
Examples
The following example signals SSS to preauthorize the NAS-Port-ID string before authorizing the domain name. This policy applies only to sessions that have a PPPoE access type.
aaa new-modelaaa group server radius sg-llidserver 172.20.164.106 auth-port 1645 acct-port 1646aaa group server radius sg-groupserver 172.20.164.106 auth-port 1645 acct-port 1646aaa authentication ppp default group radiusaaa authorization confg-commandsaaa authorization network default group sg-groupaaa authorization network mlist_llid group sg-llidaaa session-id common!username s7200_2 password 0 labusername s5300 password 0 labusername sg-group password 0 labvpdn enable!vpdn-group 2request-dialinprotocol 12tpdomain group.cominitiate-to ip 10.1.1.1local name s7200-2!vpdn-group 3accept dialinprotocol pppoevirtual-template 1!! Signals Subscriber Service Switch to preauthorize the NAS-Port-ID string before! authorizing the domain name.subscriber access pppoe pre-authorize nas-port-id mlist-llid!interface Loopback0ip address 10.1.1.2 255.255.255.0!interface Loopback1ip address 10.1.1.1 255.255.255.0!interface Ethernet1/0ip address 10.2.2.2 255.255.255.0 secondaryip address 10.0.58.111 255.255.255.0no cdp enable!interface ATM4/0no ip addressno atm ilmi-keepalive!interface ATM4/0.1 point-to-pointpvc 1/100encapsulation aa15snapprotocol pppoe!interface virtual-template1no ip unnumbered Loopback0no peer default ip addressppp authentication chap!radius-server host 172.20.164.120 auth-port 1645 acct-port 1646 key rad123radius-server host 172.20.164.106 auth-port 1645 acct-port 1646 key rad123ip radius source-interface Loopback1The following example is identical to the previous example except that it also adds support for sending the PPP authenticating username with the preauthorization in the Connect-Info attribute. This example also includes command-line interface (CLI) suppression on the LLID if the username that is used to authenticate has a domain that includes #184.
aaa new-modelaaa group server radius sg-llidserver 172.31.164.106 auth-port 1645 acct-port 1646aaa group server radius sg-groupserver 172.31.164.106 auth-port 1645 acct-port 1646aaa authentication ppp default group radiusaaa authorization confg-commandsaaa authorization network default group sg-groupaaa authorization network mlist-llid group sg-llidaaa session-id common!username s7200-2 password 0 labusername s5300 password 0 labusername sg-group password 0 labvpdn enable!vpdn-group 2request-dialinprotocol 12tpdomain domain1.comdomain domain1.com#184initiate-to ip 10.1.1.1local name s7200-2l2tp attribute clid mask-method right * 255 match #184!vpdn-group 3accept dialinprocotol pppoevirtual-template 1!subscriber access pppoe pre-authorize nas-port-id mlist-llid send username!Related Commands
Cisco and the Cisco Logo are trademarks of Cisco Systems, Inc. and/or its affiliates in the U.S. and other countries. A listing of Cisco's trademarks can be found at www.cisco.com/go/trademarks. Third party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1005R)
Any Internet Protocol (IP) addresses used in this document are not intended to be actual addresses. Any examples, command display output, and figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses in illustrative content is unintentional and coincidental.
© 2002-2003, 2005-2006 Cisco Systems, Inc. All rights reserved.

 Feedback
Feedback