Introduction
This document describes the steps to perform a basic analysis and how to troubleshoot the SecureX and Insights and Secure Email Appliance integration module.
Prerequisites
Requirements
Cisco recommends that you have knowledge of these topics:
- SecureX
- Security Services Exchange
- Secure Email
Components Used
The information in this document is based on these software and hardware versions:
- Security Services Exchange
- SecureX 1.54
- Secure Email C100V on software version 13.0.0-392
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, ensure that you understand the potential impact of any command.
Background Information
The Cisco Secure Email Appliance (formerly Email Security Appliance) provides advanced threat protection capabilities to detect, block, and remediate threats faster, prevent data loss, and secure important information in transit with end-to-end encryption. Once configured, the Secure Email Appliance module provides details associated with observables. You can:
- View the email reports and message tracks data from multiple appliances in your organization
- Identify, investigate and remediate threats observed in the email reports and message tracks
- Resolve the identified threats rapidly and provide recommended actions to take against the identified threats
- Document the threats to save the investigation, and enable collaboration of information among other devices
The integration of a Secure Email Appliance module requires the use of Security Services Exchange (SSE). SSE allows a Secure Email Appliance to register with the Exchange and you provide explicit permission to access the registered devices.
If you want to know more about the configuration, please review, this article here the integration module details.
Troubleshoot
In order to troubleshoot common issues with the SecureX and Secure Email Appliance integration, you can verify these steps.
Secure Email device is not shown in the SecureX nor Security Services Exchange portal
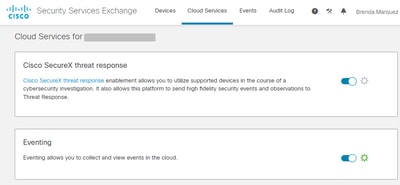
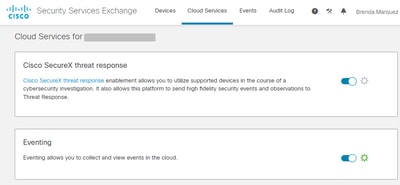
If your device is not shown in the SSE portal, please ensure to have enabled the SecureX Threat Response and Event services in the SSE portal, navigate to Cloud Services, and enable the services, as the image below:
Secure Email does not request for the Registration token
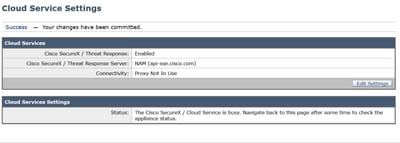
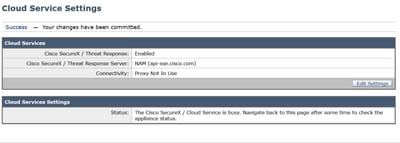
Please ensure to commit the changes, once the Cisco SecureX / Threat Response service has been enabled, otherwise, the changes are not applied to the Cloud Service section in the Secure Email, see the image below.
Registration failed because of an invalid or expired token
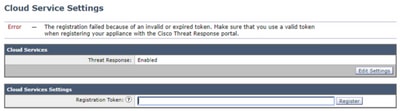
If you see the error message: "The registration failed because of an invalid or expired token. Ensure that you use a valid token for your appliance with the Cisco Threat Response portal" in the Secure Email GUI, as in the image below:
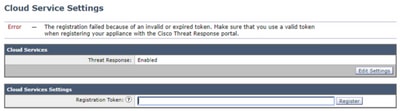
Please ensure that the token is generated from the correct Cloud:
If you use Europe (EU) Cloud for Secure Email, generate the token from https://admin.eu.sse.itd.cisco.com/
If you use Americas (NAM) Cloud for Secure Email, generate the token from https://admin.sse.itd.cisco.com/
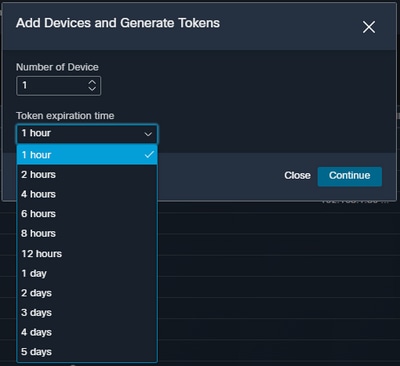
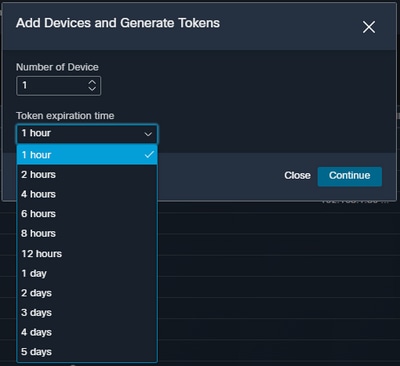
Also, remember that the Registration token has an expiration time (select the most convenient time to complete the Integration in time), as shown in the image.
SecureX Dashboard does not display information of the Secure Email module
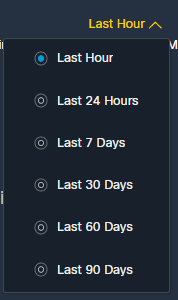
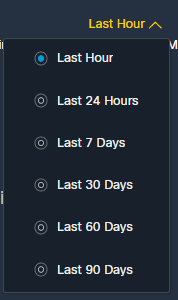
You can select a wider time range in the available tiles, from Last Hour to Last 90 Days, as in the image below.
Other examples could be that we see the message "There was a problem. Try again later." or even the error message "There was a client error in the Secure Email module: E4017: Device is offline [409]". Verify if the device is still shown as registered over the SSE portal, probably the device was des-registered and it is no longer visible. Please try to add a new module to the SecureX portal.
SecureX Secure Email tile module displays error "There was an unexpected Error on the Secure Email module"
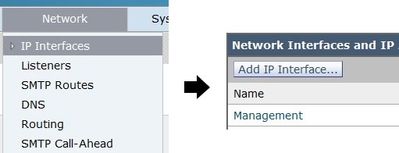
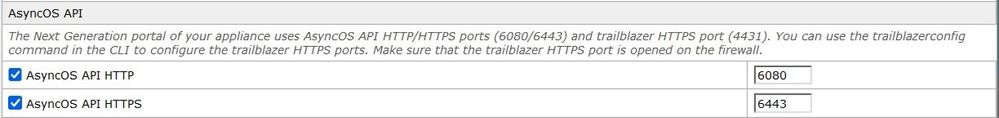
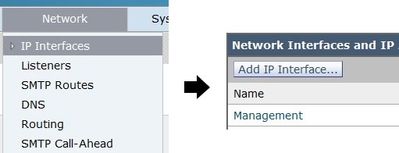
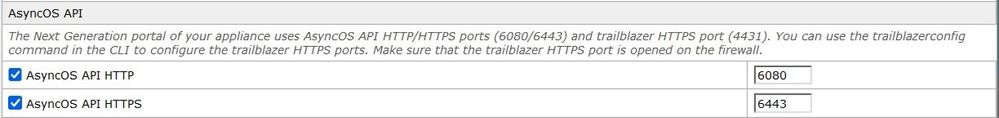
Secure Email requires AsyncOS API HTTP & HTTPS configuration enabled over the management interface to communicate with SecureX/CTR portal. For an on-prem Secure Email configure this feature from the Secure Email portal GUI, navigate to Network > IP Interfaces > Management interface > AsyncOS API, and enable HTTP and HTTPS, as shown in the image.
For a CES (Cloud-Based Secure Email) this configuration needs to be done from the backend by an Secure Email TAC engineer, it requires access to the support tunnel of the impacted CES.
Verify
Once Secure Email is added as a source to Device Insights, you can see a successful REST API connection status.
- You can see the REST API connection with a green status
- Press on SYNC NOW to trigger the initial full sync, as shown in the image
In case the issue persists with the SecureX and Secure Email Appliance integration,please see this article to collect HAR logs from the browser and contact TAC support in order to perform a deeper analysis.
Related Information

 Feedback
Feedback